In many programs on Linux, you'll come across programs which allow you to specify additional arguments instead of just simply running the program by itself. If you've used the Kali distribution, I'm more than certain you'll have come across these with the command line tools, else if you have been following these tutorials, we have already come across three tools which also use the same technique, i.e. gcc, gdb and wc. How do we do this with C? Let's find out.

Hello, everyone! Many of you don't even know about my existence here on Null Byte, so I thought of contributing something rather interesting. Recently, someone asked how to make your own "Bad USB," and I promised to make a how-to on this topic. In addition, it would be nice to have something related on our WonderHowTo world. So here it is!

It sounded great on the surface when Microsoft announced that existing Windows 7 or 8 users would be able to upgrade to Windows 10 for free, but the execution so far has left a lot to be desired. Upgrading from an existing installation is relatively easy, but when you start with a clean install of Windows 10, you run into some problems.
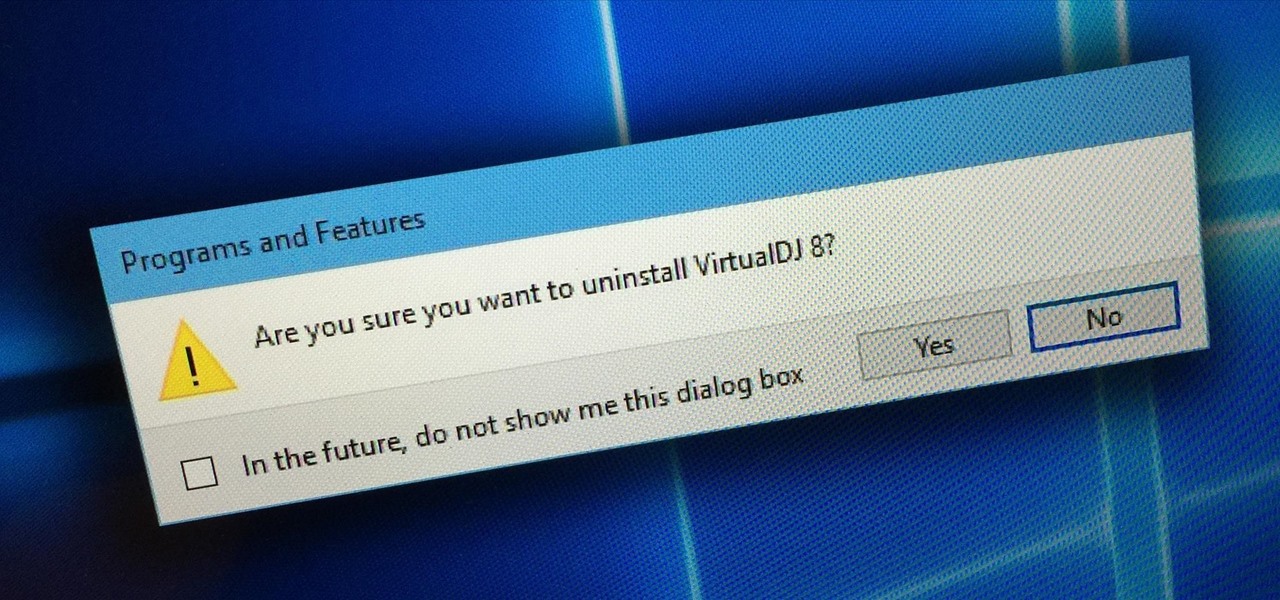
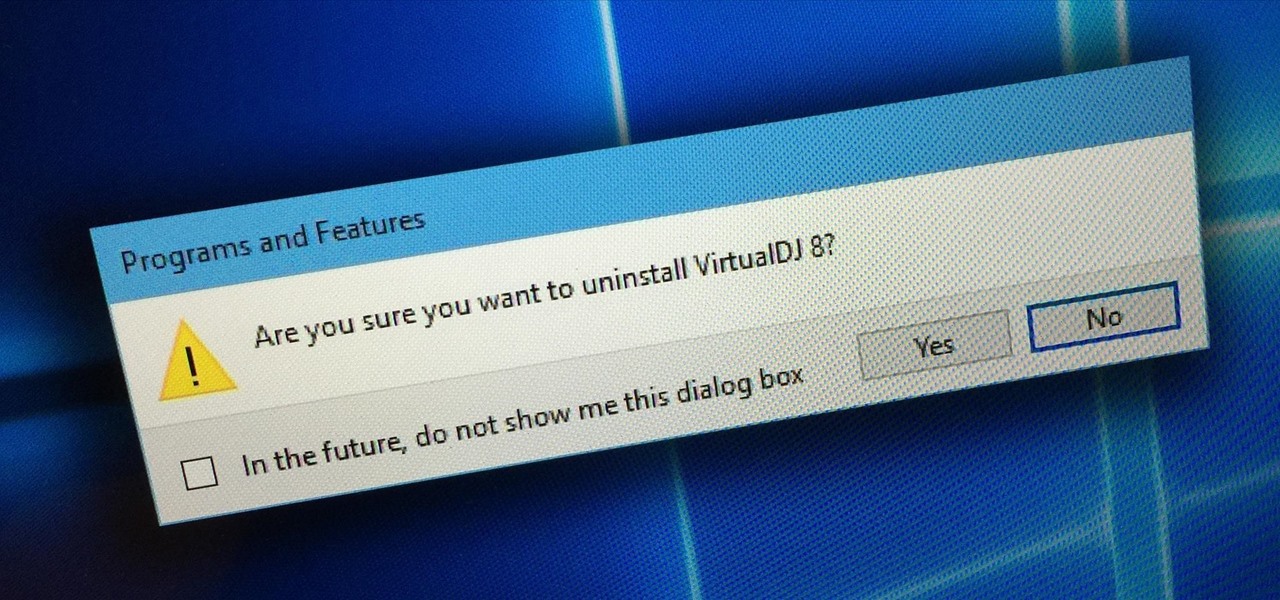
Uninstalling programs in Windows is not the nicest procedure. Some programs bundle a nice uninstaller with them which helps to ease the process. Other programs, mainly those that utilize the Windows Installer technology, begin the uninstall process right away. This can potentially be problematic for users who are trigger-happy with the mouse.

One thing the whole Internet can agree with is that cats are cute and (sometimes) cuddly. But what those endless cat videos you find yourself watching for hours on YouTube don't tell you is that cats stink. While cats aren't the source of the smell, owning a cat means a stinky litter box.

Both the Galaxy S6 and S6 Edge have had root methods available to them before the phones were even released, but the problem with these existing root methods is that they would trip the KNOX counter on your device.

bObsweep robotic vacuums automatically clean whenever instructed to do so by an owner or because of a pre-programmed schedule.

Samsung is known for its added features, but occasionally, these can cross the line between functionality and bloat. For many users, this is the case with the "S Finder" and "Quick connect" buttons that are hard-coded into the notification tray on most Galaxy S6 and S6 Edge variants.

In this simple tutorial you will be shown step-by-step how to write local shellcode for use on 64-Bit Linux systems. Shellcode is simple code, usually written in assembly that is used as payload in exploits such as buffer overflow attacks. Payloads are the arrow head of an exploit: though the rest of the arrow is important for the delivery of the attack, the arrow head deals the killing blow. In reality, payloads are slightly less exciting yet far more interesting and intelligent than medieva...

Auto manufacturers are slowly starting to debut models with Google's new Android Auto software baked into the dashboard console. Starting with the 2016 model year, we should see vehicles from Honda, Ford, Chevrolet, and many others sporting the new software.

Heartbleed, move over. There's a new bug in town, and this time it's also affecting Mac and Linux computers. It's called Shellshock (its original official title is CVE-2014-6271), and it's currently got a 10 out of 10 severity rating over at the National Cyber Awareness System. While some updates have been issued to fix this bug, they were incomplete, and your system is probably still vulnerable, as it has been for the last probably 20 years.

The Xposed Framework offers many great customization options for your Galaxy S5. S Health, with its ability to read your heart rate through a built-in monitor, is one of the main selling points of the GS5. Trouble is, the two don't seem to play nice together.

While the majority of photos taken on phones are used for personal reasons, mediums like Instagram and Flickr offer a means to show them off to the world. But those pictures of your brunch or beach day can actually go beyond that to make you some money.

T-Mobile continues to make waves in the U.S. wireless market behind CEO John Legere's UnCarrier program. At the latest installment in a series of industry-challenging announcements, Uncarrier 5.0 unveiled Test Drive. The new program is set to allow would-be customers to try out the "latest generation" iPhone for seven days on T-Mobile's network without any financial commitments.

The desktop layout in Mac OS X Yosemite is undeniably beautiful—it's sleek, simple, and easy to admire. Thing is, I do too much on my Mac to install a developer preview as my main OS (even though I can make a bootable install drive and dual-boot it), but I do want the aesthetics of the new build.

There are plenty of times when we need to charge our phones but don't have access to electricity. Whether the power is out do to storms, you're camping and run out of juice, or you're in a Tom-Hanks-like Castaway situation, it's important to have a charged phone in case of an emergency.

Pallets, Pallets, Pallets. You have to love them! How to build an outdoor play kitchen for the kids using old pallets and recycled / reclaimed wood. I came up with the idea after seeing how my young son loved playing with the one at childcare. Pallet projects and Pallet Ideas are never far from my mind so l couldn't wait to get stuck into building my play kitchen.

How to build a set of strong, stackable sturdy sawhorses. Let's face it, one of the most useful pieces of carpentry equipment would have to be a set of sawhorses. Every worksite, garage or workshop needs a set of sawhorses. They have numerous uses from stacking timber on, using as painting racks, to using as a temporary workbench by laying a door or some ply across two sawhorses. You can even use them as trestles for a dining table!

Transparent status bars and new lock screens weren't the only new additions that came with the Galaxy S3 KitKat update. Along with better battery life and a smoother user experience, we got a new toggles design and recent apps menu. Of course, Samsung's infinite wisdom left these two aesthetic features hidden away. Luckily, with root, you can easily enable them with just a few quick edits.

Hello, freakje118 here, it is a while ago, but here are the winners of the easter builds! First place is this week for: Fedganac88

Veering from common practice, XDA commenter, "the_commenter", discovered a changelog for the upcoming version of Android 4.4.3 tucked away on Google's servers.

You can easily level picture frames on your wall using your iPhone, but leveling the photos you actually take is a whole 'nother story. There are no built-in leveling tools in your stock Camera app, or in most camera apps for that matter.

Yesterday, the Free Software Foundation published an article written by Paul Kocialkowski. A software developer for the the Android fork system Replicant, Paul stated that his organization discovered, and later patched, a "backdoor" vulnerability that existed in older Samsung Galaxy devices, including our beloved Galaxy S3s. Only problem is, it's kind of bullshit—but we'll get to that later.

Presentational video for our DIY Camera Crane project. Video: .

Well, that was quick. A little over a week after releasing the third beta for iOS 7.1, Apple presented a fourth build to developers.

I have shown here to install Java development kit. It also contains the settings of path and classpath to prepare for java programming.

How to make a wooden bench from reclaimed wood. Recycled wood projects, whether it's from pallet wood or old fence palings, the end result can be fantastic! In this video l am using reclaimed hardwood fence palings to build a rustic wooden bench seat. Rustic wood furniture has to be one of my favourites.

How much privacy are you getting as an AT&T customer? With the recent leaks confirming the National Security Agency's surveillance on AT&T users, and the ongoing trial of Jewel v. NSA, it seems not much at all.

When it comes to text documents and spreadsheets, Microsoft Office is the be-all and end-all office suite—but it's not cheap. Paying anywhere from $140 to $400 puts a big dent in your bank account, especially if you're a broke college student eating ramen for breakfast, lunch, and dinner. Something that I wish I would've known about during college is Microsoft's HUP (Home Use Program). With HUP, any employee or student of an organization that has a Microsoft volume license is eligible to purc...

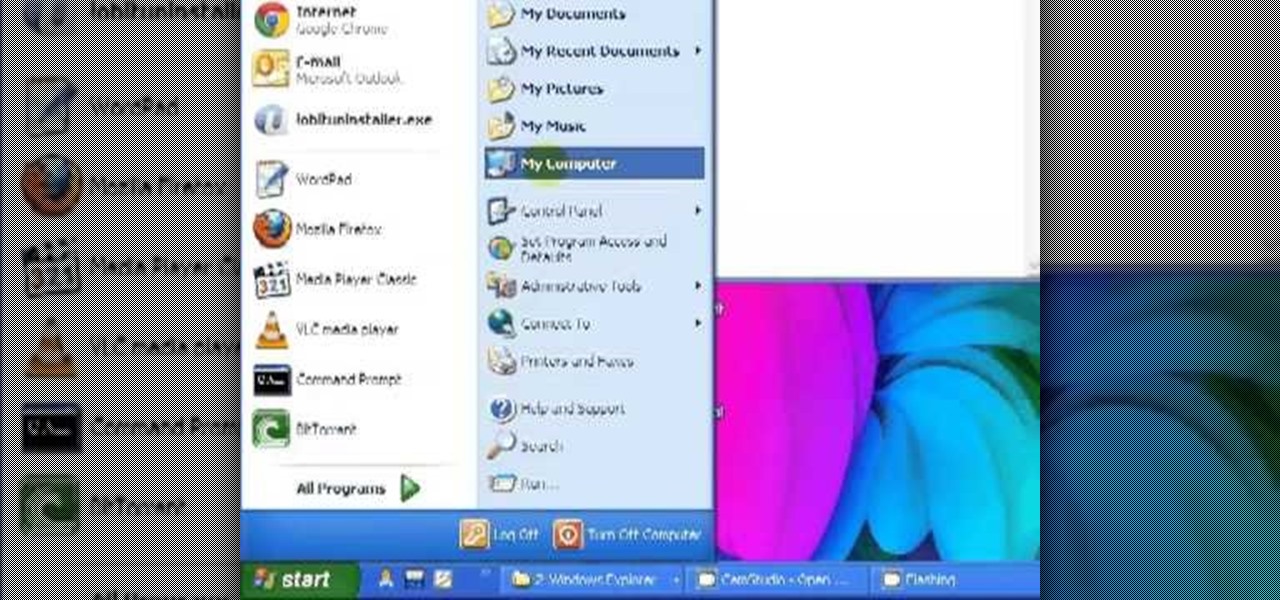
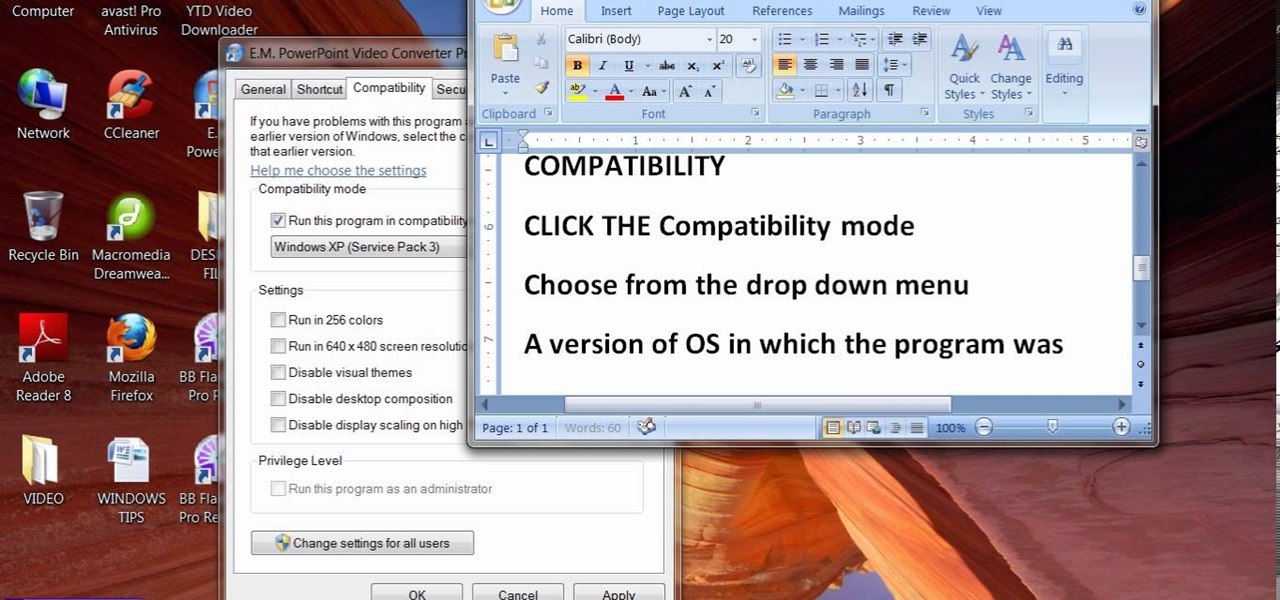
When people upgrade their windows few software don't run on new OS. How to fix the problem? Setting program compatibility solves the issue. Watch the video we made and submitted earlier in You tube.

Antique car collecting and restoration is a very popular hobby practiced by many around the world. A quick drive through my town turns up with a handful of classic cars parked in their respective driveways, some in pristine condition, and others not-so-much. While some people end up eventually fixing up their classics, many also do not. Some cars end up rotting away, left to be either salvaged or sold off in pieces—mostly due to time consumption and excessive costs.

There are plenty of ways to create decent looking special effects on a budget. You can use basic, inexpensive materials to make ground explosions or realistic looking alien landscapes. But nothing says Hollywood quite like your own green screen.

Time-lapse videos are a recent phenomenon to the mainstream audience—in movies, on television shows, and even in commercial ads. These sped-up and blurred images are a microcosm of many of our lives in which we're constantly in a hurry to get somewhere. We like everything fast: our work, our coffee, and our news.

LEGO has not attempted a blimp, zeppelin, or similar airship since 1999, the 5956 Expedition Balloon which used highly specialized parts. This is unfortunate as these vessels are well and truly part of the pulpy adventure and steampunk scene.

You can do a lot with water guns. Have trouble waking up? Make a water gun alarm clock that (almost) no one could sleep through. Prefer real ammo? Turn your water gun into an airsoft BB gun. And if you don't have one, you can even make your own.

Christopher Nolan's Batman trilogy has been one of the most successful film series of all time, so it comes as no surprise that everyone wants their own real-life versions of the Dark Knight's gadgets and vehicles.

Back in 2008, media artist Kyle McDonald created a 3D interface that could track movement, which he turned into a virtual Tic-tac-toe game.

RFID chips are everywhere. They're in passports, credit cards, and tons of items you've bought in the last 5 years or so. Big retailers like Walmart started using tracking products with RFID as early as 2004, and today, they're used in everything from mobile payments to hospital record systems. Chances are, unless you're a hermit (in which case you wouldn't be reading this anyway), there's an RFID tag within a few feet of you. Photo by sridgway

No one likes to think about the possibility of natural disasters, but we all know they could happen at any time. Some of us are a little more paranoid than others, but wouldn't it be nice to know that you'd be protected if anything really crazy ever happened? Like the zombie apocalypse?

Hello! I would like to share some data about the nests that rabbits and dwarf rabbits build. They represent good shelters for them and their babies.