We may or may not see Apple's long-awaited take on AR smartglasses this year, but the company is more than getting its practice swings in with its current wearables business, which hit record revenue in 2019 according to financial results released this week.
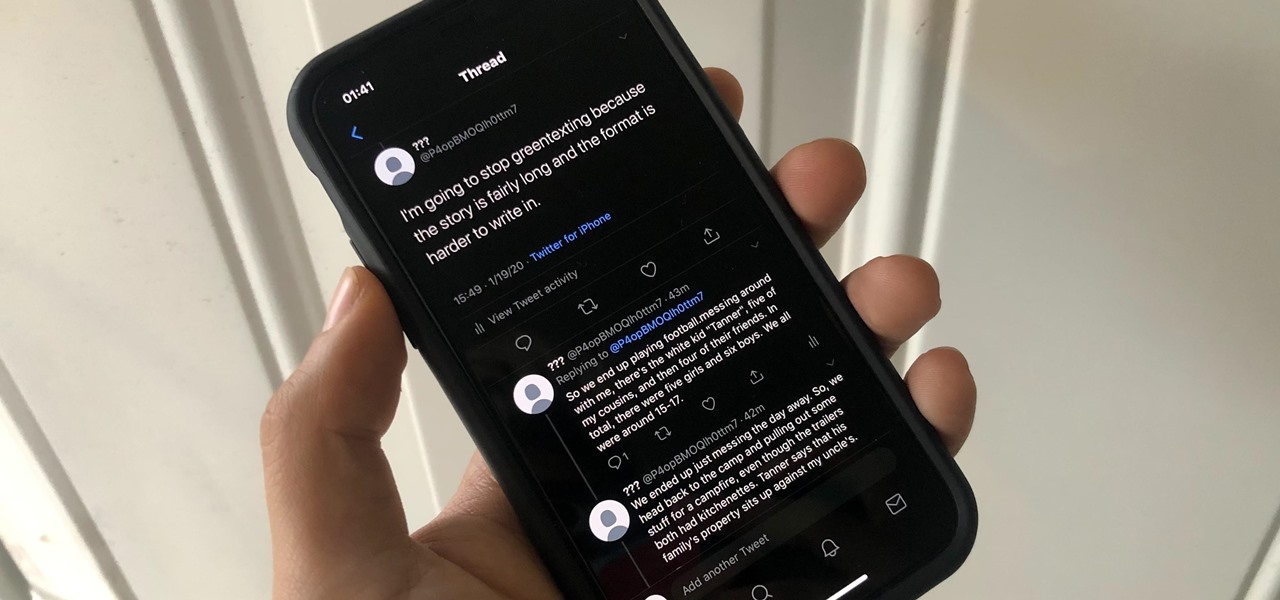
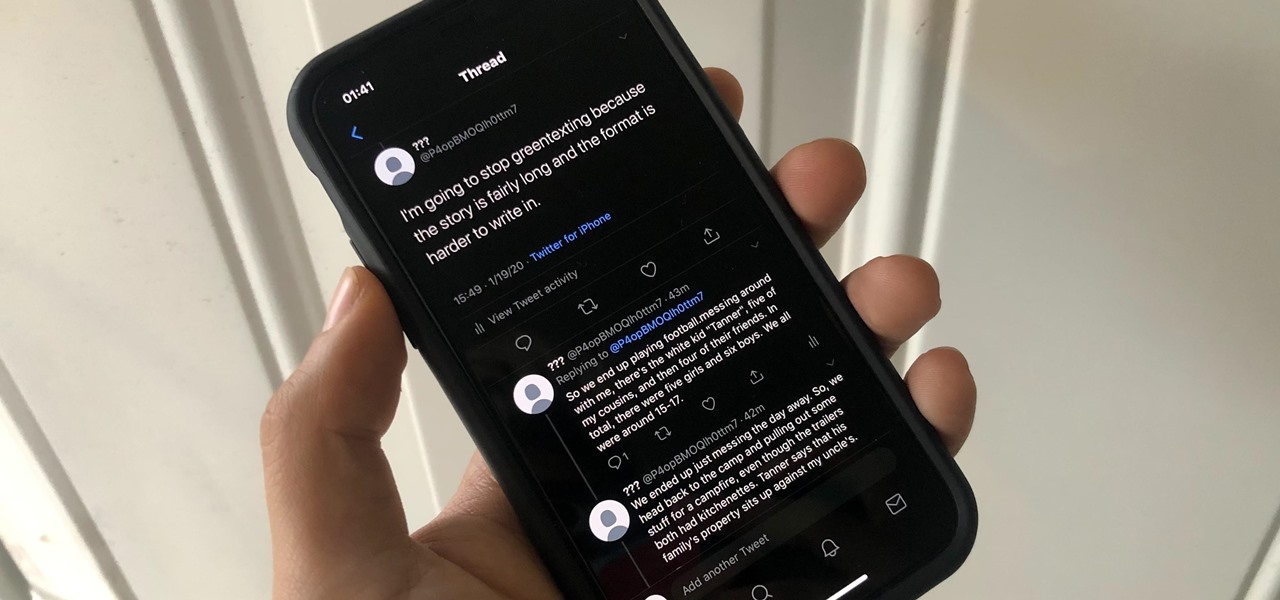
The 280-character limit for tweets on Twitter is double what it used to be back in the day, but it's still not enough to express in-depth thoughts, ideas, commentary, rants, blogs, stories, and the like. These tweetstorms, as they're called, are the reason why Twitter created its threads feature.
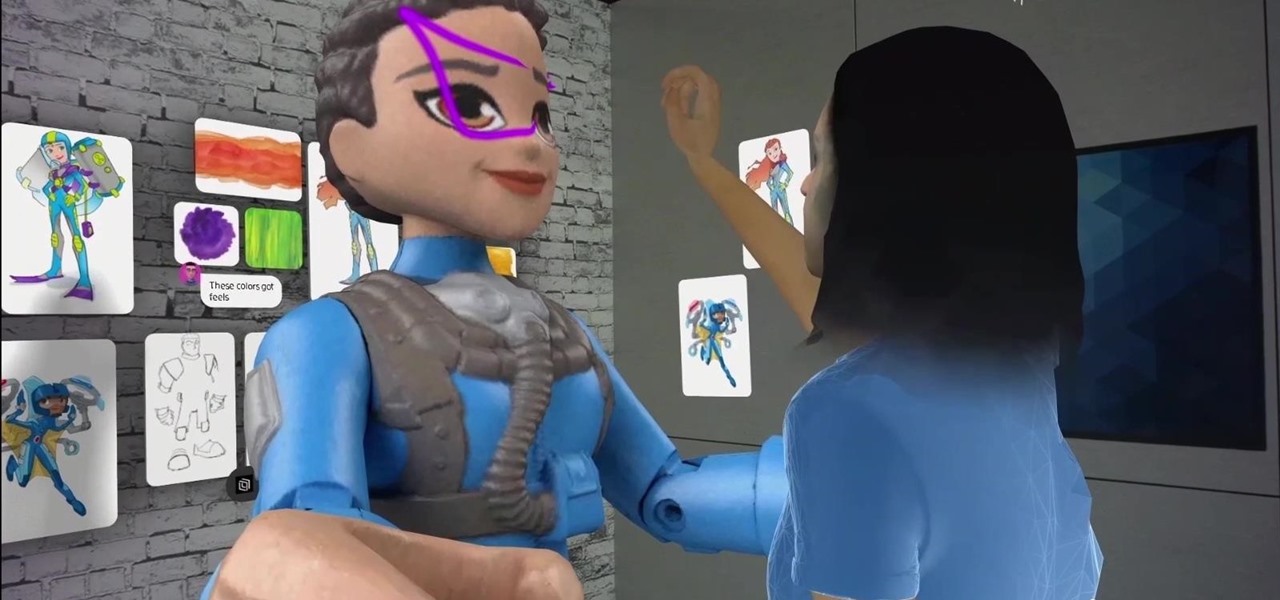
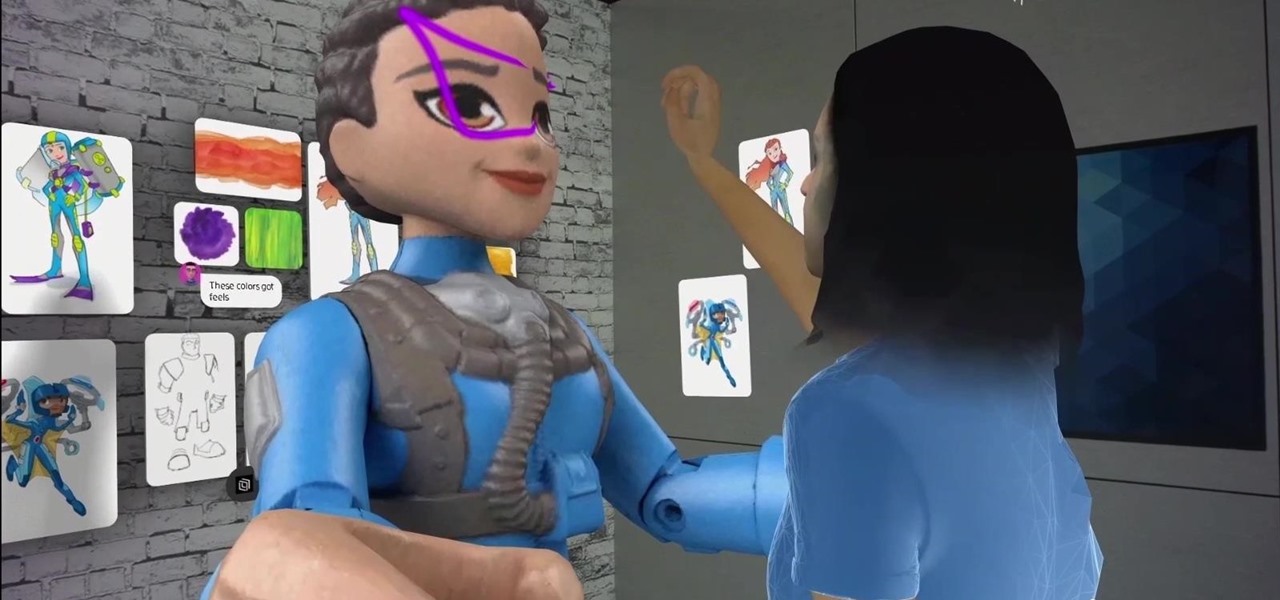
Having emerged as one of the leading augmented reality video conferencing apps, Spatial is ready to improve upon the experience.
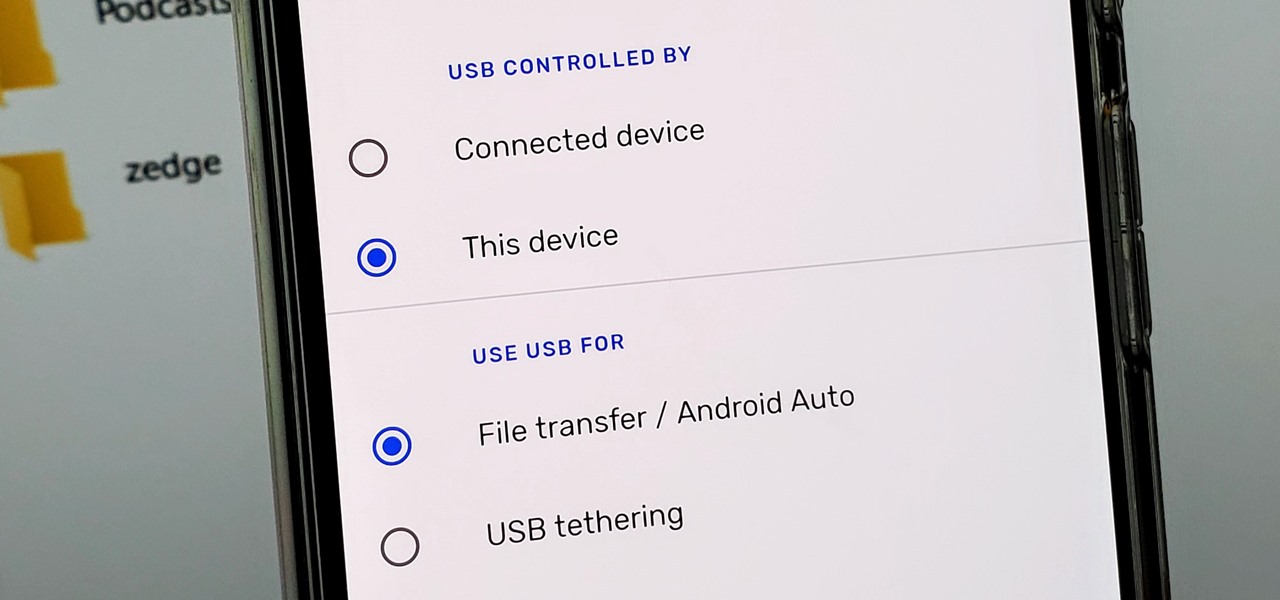
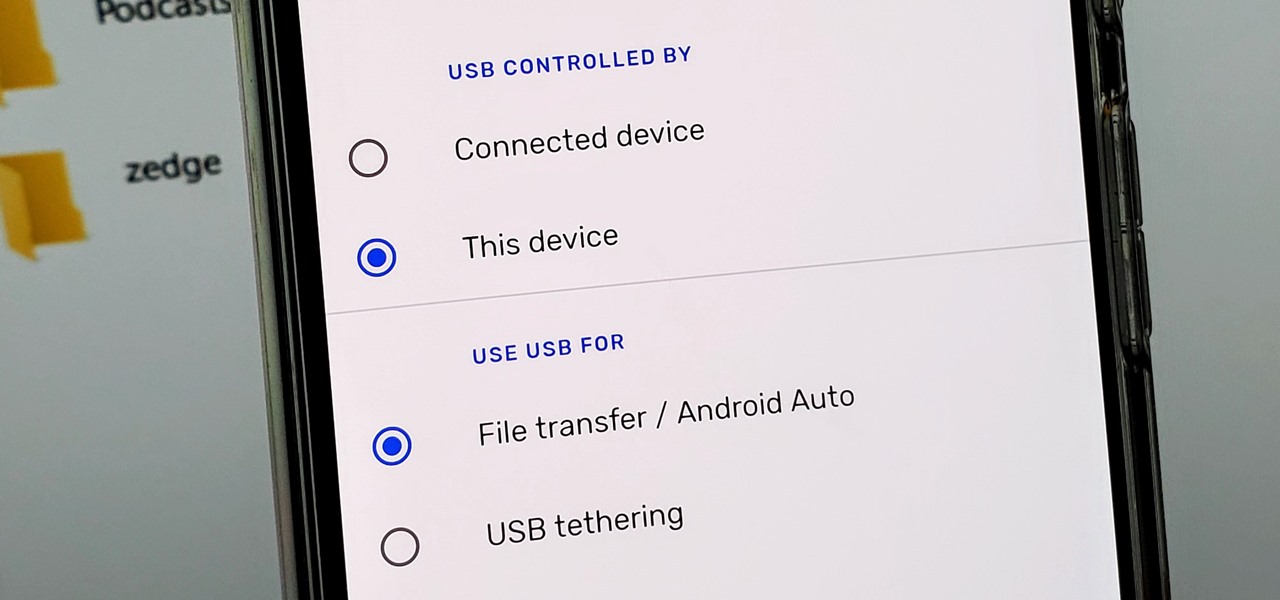
Back in the earlier days of Android, you were able to connect your phone to a computer, and it would mount automatically. This meant once the USB connection was made, your internal storage would pop up on the computer and you could go about your business. But recent versions of Android changed that to help increase security.

After Android 10 added a system-wide dark mode, hordes of app developers rushed to add support for the feature. This even helped users on Android 9 and below since most apps could be manually set to a dark theme now. Emphasis on most — WhatsApp was conspicuously absent, for one. That changes today.
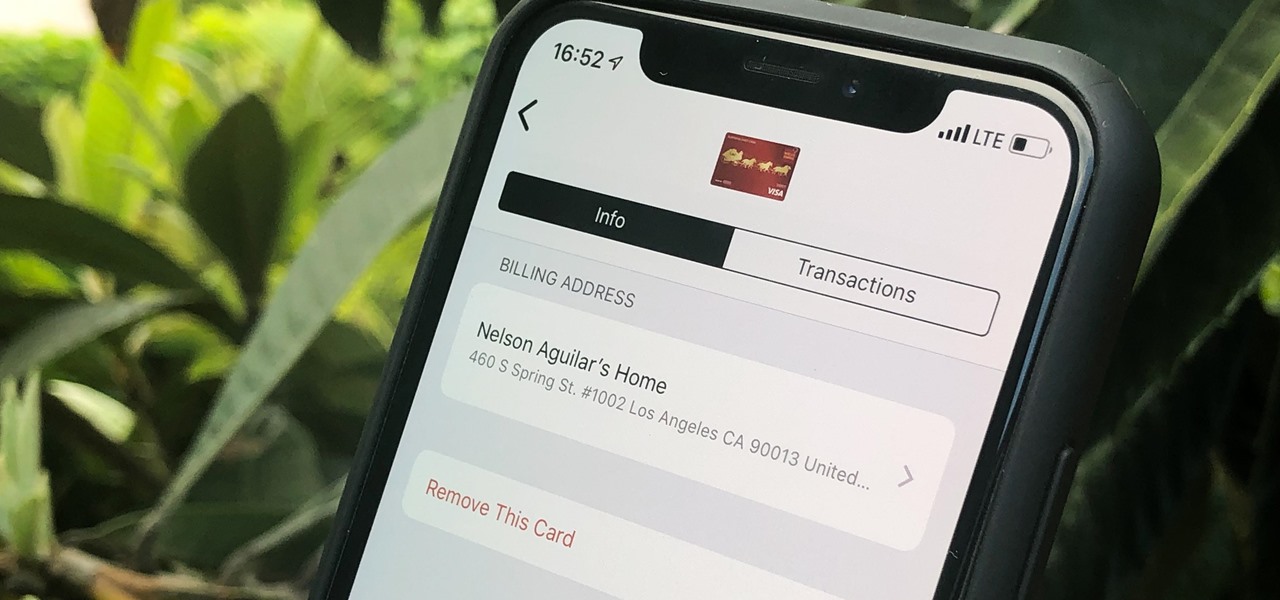
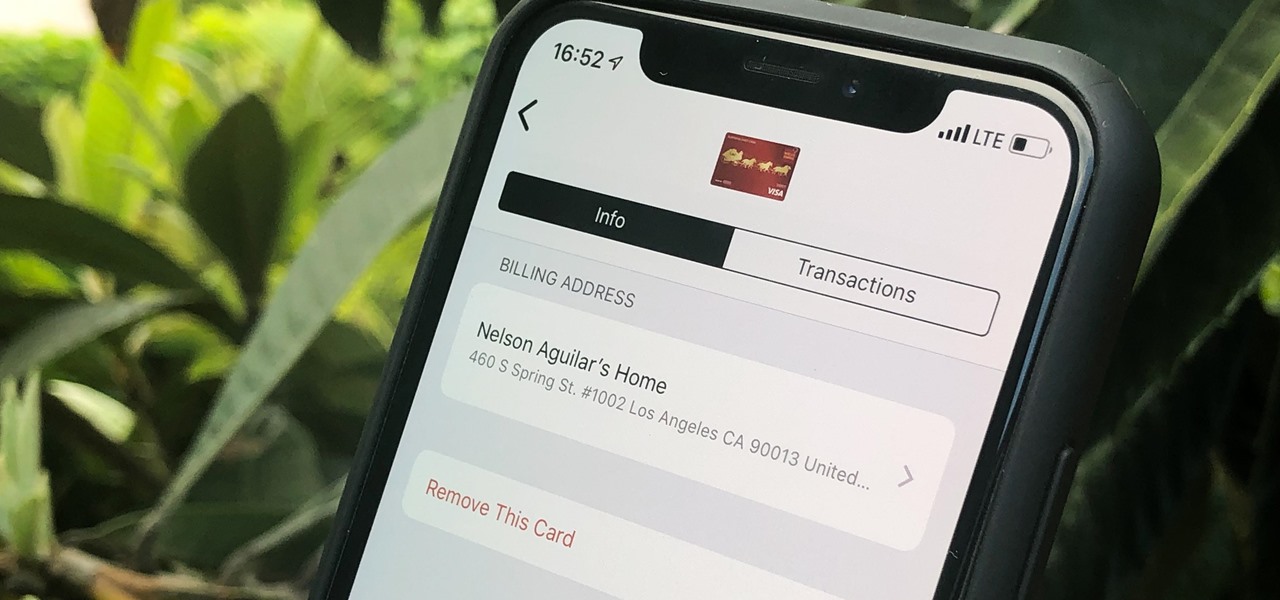
Apple Pay can be used at retail stores, restaurants, markets, and millions of other locations in the US and abroad. It's used to buy everything from clothing to groceries and vending machine snacks, so it's important to ensure that the cards in your Wallet are always up to date with the correct billing and shipping addresses.

There's definitely some malware-ridden apps on the Play Store. When it comes to the third-party apps you've connected to your Google Fit account, some have a crazy amount of permissions they have no business accessing. For example, you probably don't want a heart monitor app having access to your personal location data.

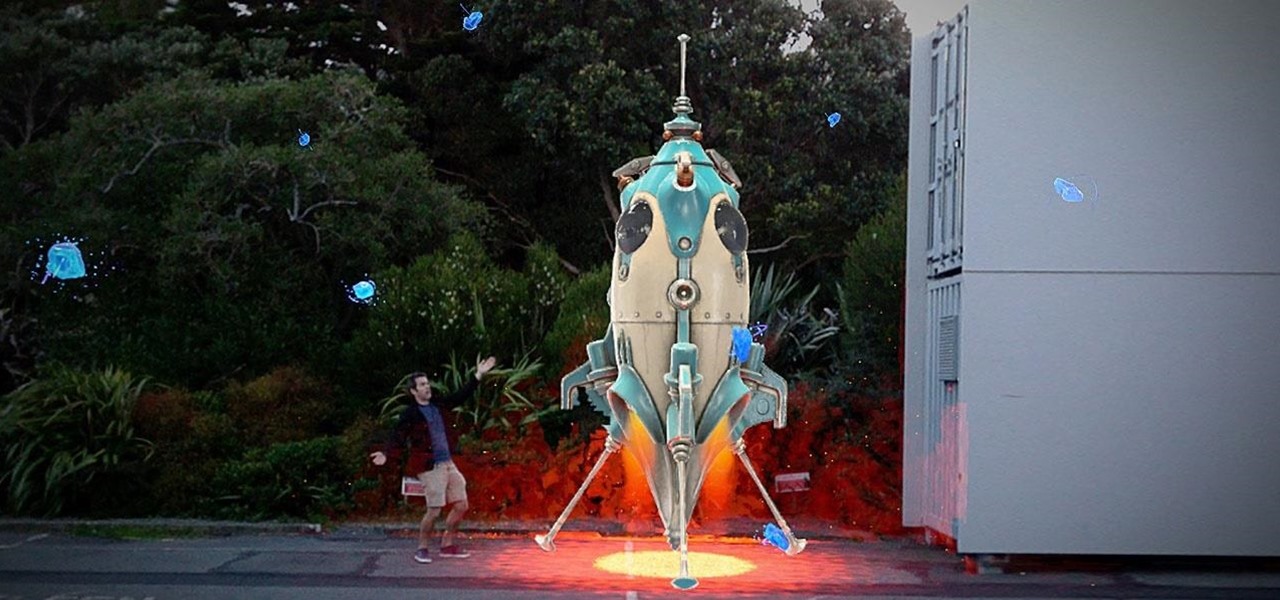
As the year comes to a close, we've invited some of the leaders of the AR industry to take the time to look back at the progress the AR industry has made while looking forward to what's ahead in 2020. A report on the top apps of 2019 — and the decade — also offers some insights on the progress and direction of mobile AR.

It looks like Pokémon GO players may get a surprise gift from the game's developer, Niantic, this holiday season.

There may be questions from some about the future of Magic Leap, but in Japan, The Force is with the augmented reality startup.

Friends and family receiving new Portal devices for Christmas will have some extra stocking stuffers in the form of new AR features.

Apple's ARKit has built a considerable lead in terms of features over Google's ARCore, but Google's latest update to ARCore adds a capability that makes the platform a bit more competitive with ARKit.

YouTube Music has been around since late 2015, but it only started becoming a viable music service in 2019. It makes sense for Google to utilize YouTube's existing library of music videos, remixes, and cover songs to create one massive music platform. But one downside is you get a lot of the music video versions of songs instead of the album versions. Thankfully, you can change this.

After entering into settlement talks with Epic Games over the gaming giant's trademark challenge, Nreal is now ready to open up the floodgates to potential early adopters in the augmented reality space.

After talking up the Magicverse for the past year and adding new capabilities to Lumin OS to accommodate it, Magic Leap appears to be inching ever closer to actually launching its cross-platform flavor of the AR cloud while introducing a new tool for its development community.

Homemade Halloween costumes that exhibit the maker's creativity are always better than off-the-shelf versions. It turns out that the same is true with virtual costumers.

Just as Apple, Snapchat, and other tech giants are working on augmented reality wearables in the race to replace smartphones for the future of mobile computing, so is Samsung.

Reminders may have received the biggest update out of all the native Apple apps on iOS 13. Among other things, the new Reminders app now comes packed with smart lists to make it easier find things, and a flagging feature to help you better manage your most important reminders.

Your Pixel has a few hidden features you probably don't know about, like the ability to clean up your funky contacts list. Since I'm sure you haven't manually organized your contacts since the inception of Android, there are likely some incomplete and duplicate contacts. Thankfully, your phone can fix this automatically.

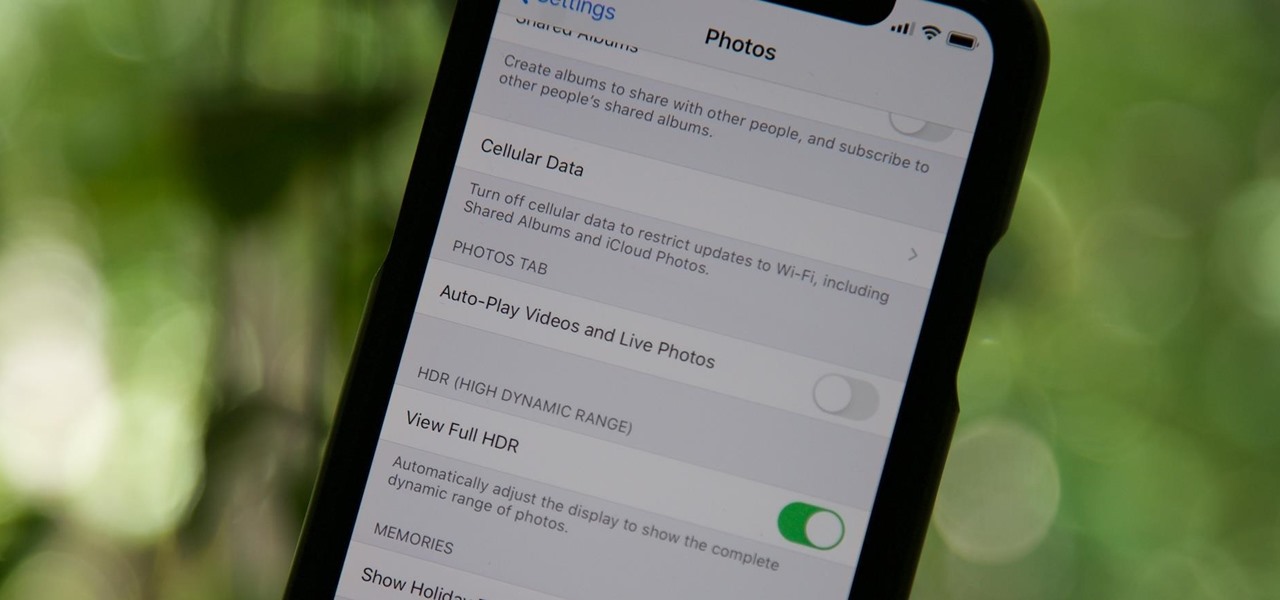
By default, videos in the Photos app auto-play in several instances on iOS 13, making it a great way to get a quick, extended glimpse when you're browsing. But this isn't always ideal — especially when you're flipping through private or embarrassing videos and other eyes are on your screen. Fortunately, Apple has an easy way to disable this feature.

Dark mode themes for mobile apps are all the rage these days, but YouTube is taking that a bit literally with its latest augmented reality experience.

Augmented reality enthusiasts who expected an AR hardware unveiling at Apple's annual iPhone launch event might not have to wait much longer.

There is power in the detail. Sending an email at a specific time can give you an edge. Depending on what you are doing, it can help your email get read or it can put you at the top of someone's inbox. With the Gmail app for Android and iOS, you can now schedule your messages to maximize the efficiency of your email.

This time last year, Snap CEO Evan Spiegel and his company were faced with an erosion of its user base that cratered its stock price. This year, on the strength of Snapchat's AR camera effects, the company has reversed course. And that's why Spiegel tops the NR30, our annual list of the leaders in the AR industry.

Apple Maps has had a rocky history since its introduction, which included limited features and questionable data, earning it a reputation as a lesser alternative to Google Maps. Since then, Apple has worked to close the gap, and in iOS 13, they're introducing Collections, which allow you to create groups of locations on your iPhone that you can then quickly access and share with others.

The growing stock of augmented reality apps filling up the Magic Leap store seems to be picking up pace in recent months.

Less than a month after launching its augmented reality Swim Goggles, wearables startup Form is preparing to add a major new feature for aquatic athletes.

Although styluses and smartphones have existed together for years, the iPhone has always ignored the pairing. After all, "Who wants a stylus?" But ever since the Apple Pencil made its debut on iPad, the rumor mill has churned out the idea that an iPhone could one day see stylus support. That day will probably come with the release of iPhone 11, and there's a good indicator to make its case.

Before smartglasses makers can dream of taking smartglasses to mainstream consumers, they must first determine the right mix of form, function, and price that will drive customers to buy into what they're hoping to sell.

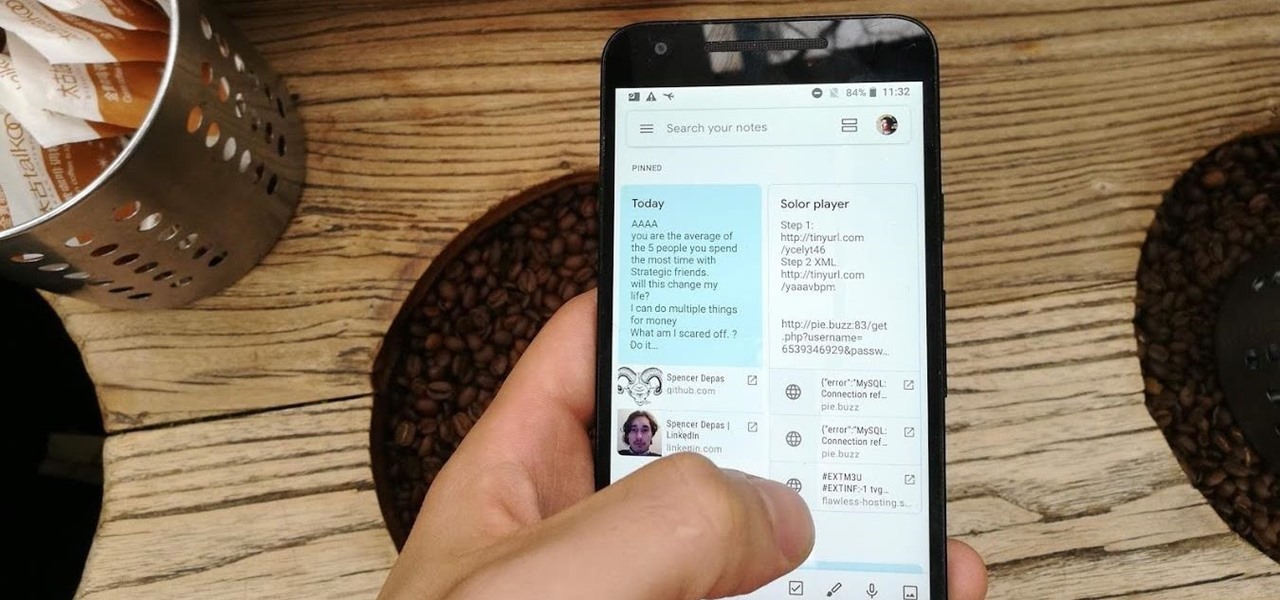
Disabling clunky, revealing link previews on Google Keep can serve multiple purposes. You know, those expanded versions of the same URL you pasted into your note, except duplicated, tacked onto the bottom of your note, and showing a preview picture. Removing these can help optimize your productivity formula.

Thanks to a new update to Amazon Sumerian, developers will now be able to not only create more realistic 3D content, but also build AR experiences more easily.

Already among the first game makers to add augmented reality content to an existing game upon the launch of ARKit, Zynga is breaking new ground with mobile AR once again.

Remember Photo Booth on Mac and iOS? It still exists, but there was a of time where everyone was using it. And why not? It was so cool to take photos with any background imaginable. Underwater? Check. On the moon? Of course. Now, Instagram wants to bring back the fun by introducing AR backgrounds for stories.

For developers and makers getting started with augmented reality, Intel is lowering the barrier to entry for its RealSense line of sensors.

With the latest version of ARKit and a new set augmented reality development tools set to arrive this Fall with iOS 13, Apple has taken an unprecedented step in recruiting Chinese developers to fill the App Store with mobile AR apps now, likely with an eye to the future.

If you've ever traveled to a country where you do not speak the language, you know there are times you need to translate text. Or maybe you just ordered a foreign good that requires text translation. Google Translate can easily solve this with its camera translation feature. It will translate any text you see in the real world into your desired language.

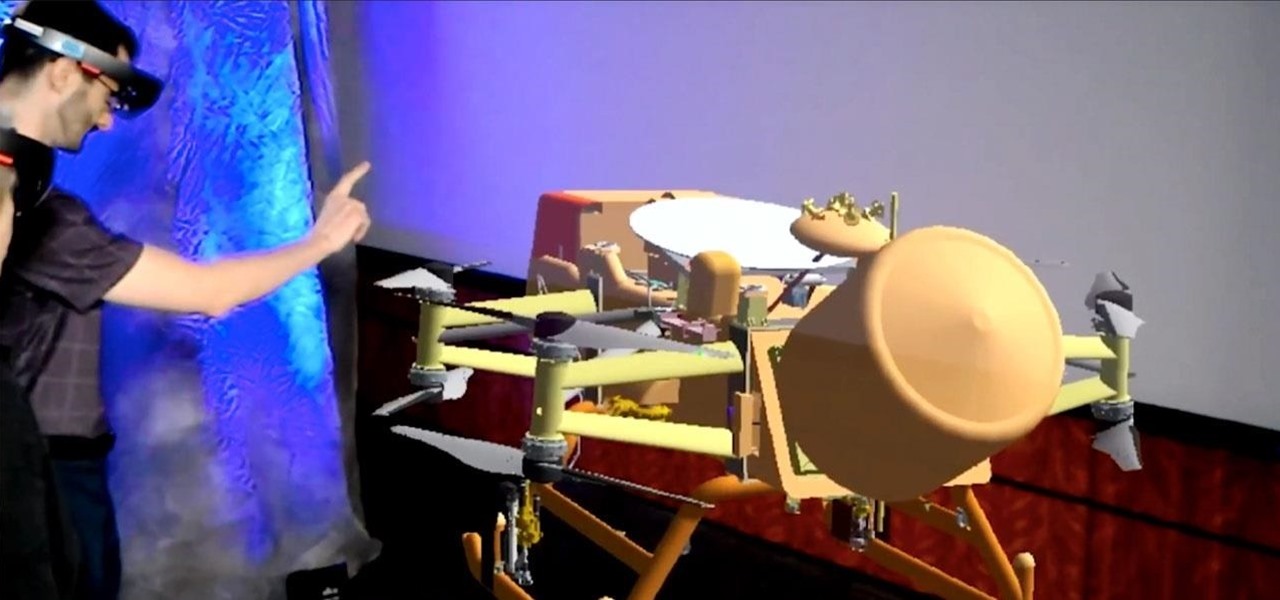
NASA is going going to Saturn's moon Titan, and the space organization is using augmented reality help them do it.

It is said that the best way to avoid detection when hacking is to leave no trace, and often that means not touching the filesystem at all. But realistically, in most cases, it's impossible not to interact with the filesystem in one way or another. The next best thing to do to throw off any investigators is to change the file attributes to hide activity. We can do this with Metasploit's Timestomp.

A company whose sole product line is smartphones might be worried about early proclamations that the smartphone is dead with the advent of augmented reality wearables.

After one of Britain's "Brothers Bling" bought Blippar out of bankruptcy, the mobile augmented reality company is getting back to business with the addition of web-based AR capabilities to its platform.