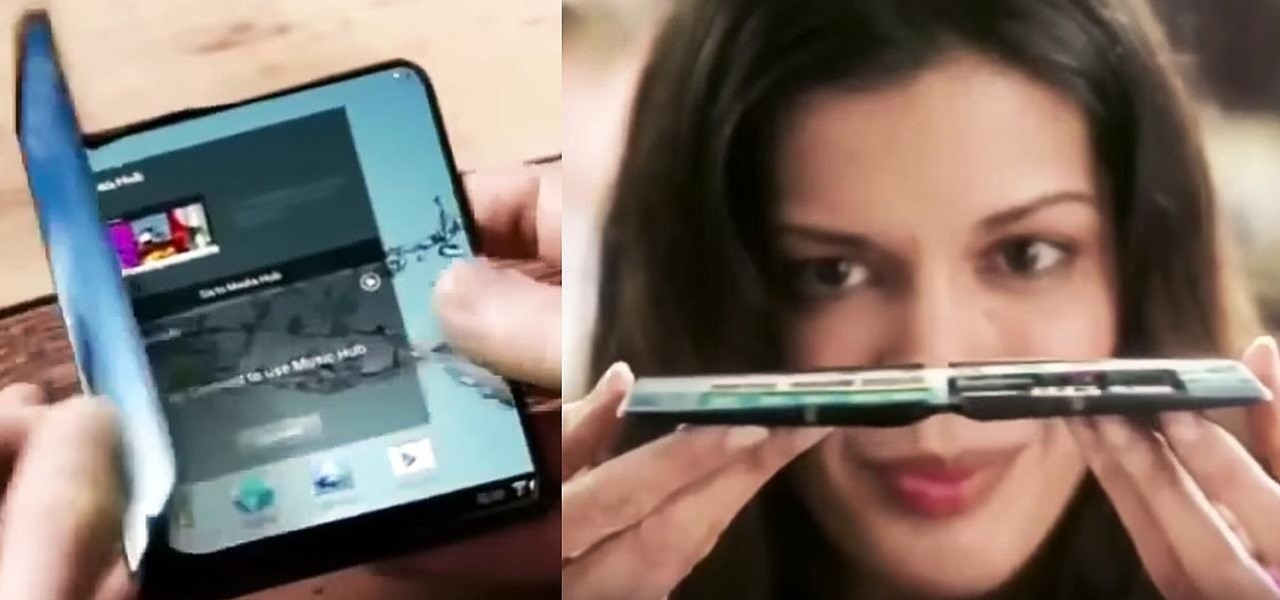
News: Woah. This Report Suggests Samsung's Folding Phablet Is Coming Next Year
If you think phablets are too big to be smartphones, and not big enough to be tablets, then you're going to love what's coming next.

If you think phablets are too big to be smartphones, and not big enough to be tablets, then you're going to love what's coming next.

From day to day, it can be difficult to remember everything that's required of you. I tend to forget exactly where it is I'm supposed to be during my busiest moments, and it's even easier to delete each day's events out of your brain when there's so much else that dominates your mind. Yet taking the time to remember exactly what it is that happens during each of our days can be a vital part of our memory—and with nothing more than 15 minutes, we can strengthen our brains and remember more tha...

When you search for a specific location or business with the Google app, a Knowledge Graph card is usually the top result. This card displays a handy mini-map and offers a quick link for directions to the location of your query, but it has one irksome flaw—these links can only be opened by the Google Maps app.
In the past few weeks, the internet has been abuzz with nightmarish horror stories of Comcast's questionable decision-making and downright terrible customer service. The central theme of many of these disputes with the nation's largest cable provider is that without evidence, the conglomerate will refuse to acknowledge its mistake and place the burden of proof on the customer.
According to a recent survey conducted by Edison Research and Statista, Pandora still has a firm grasp as the most popular music streaming service in the United States. With iHeartRadio, iTunes Radio, and even Spotify trailing behind by a large margin, it doesn't look like Pandora will lose their footing in the near future.
Privacy features have become quite the hot commodity, emerging from the aftermath of the NSA scandals that rocked the United States this past year. While the NSA has the means to gather information on all of us (regardless of any security software we implement), it doesn't mean that they're the only ones looking.

Welcome back, my fledgling hackers! The database is the hacker's "pot-of-gold," as it contains information that is very valuable to both the business and the hacker. In this, the second of my series on hacking databases, we're on the "hunt" for Microsoft's SQL Server. Although far from the most commonly used database (Oracle hold's that title), Microsoft's SQL Server is very often found in small-to-medium sized businesses. Even a few big businesses use it.

How much privacy are you getting as an AT&T customer? With the recent leaks confirming the National Security Agency's surveillance on AT&T users, and the ongoing trial of Jewel v. NSA, it seems not much at all.

UPDATE: The whitehouse petition has received enough signatures to require a response from the government. Your voices have been heard! Now we wait...

Do you own an HP printer? If so, it may be vulnerable to malware attacks. Researchers at Columbia University discovered that 25% of Hewlett-Packard printers have significant vulnerabilities that put your printer in danger from hackers—even your home. With a budget of just $2,000, researchers Salvatore Stolfo and Ang Cui were able to hack into the printers using remote firmware to install malware, and in some cases even cause the printer to catch on fire. The main issue is with the printer's c...

Don't want to shell out the big bucks for some fancy, expensive budgeting software? Well, if you have Excel 2008 for Mac installed, you can manage your budget right there. Personal financing doesn't get easier than this— even business finances are easy to keep track of. The Microsoft Office for Mac team shows you just how to manage your finances with pre-formatted Ledger Sheets in this how-to video.

The COVID-19 pandemic forced many businesses into remote work models, whether they were ready or not, making Zoom a household (or home office) name for its video conferencing service.
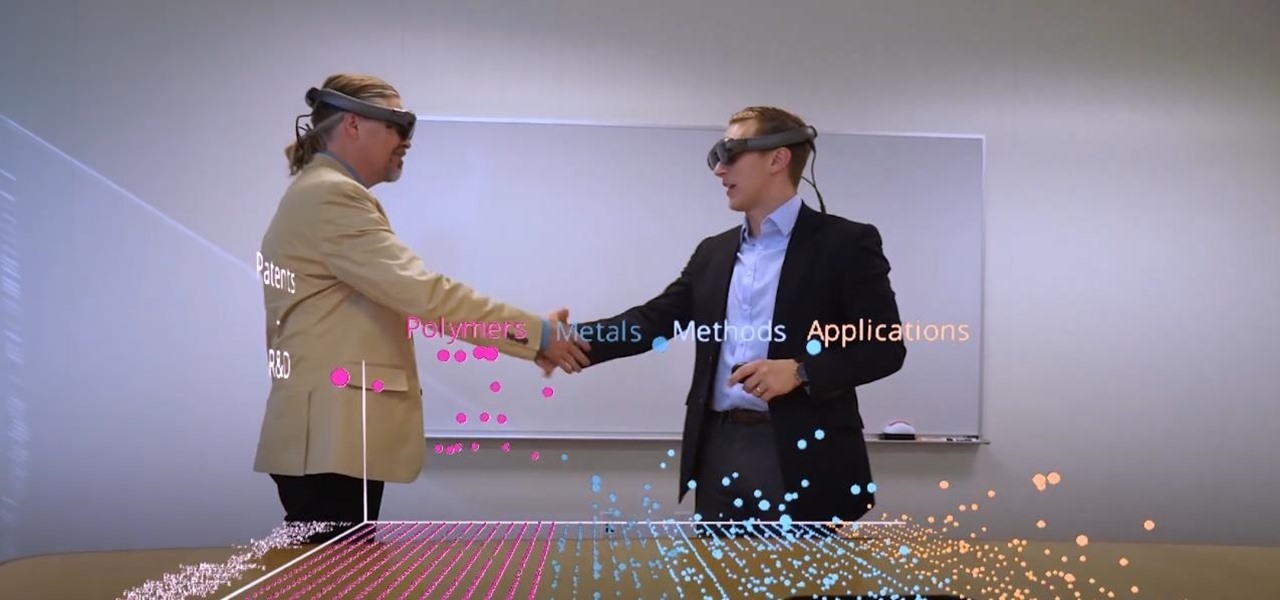
Thanks to the expanding universe of augmented reality tools being made available, increasingly, anybody can liven up sleepy office meetings with immersive computing.

Some investors play the short game, placing their bets on industries that show the quickest return on their investment, and, in the augmented reality space, that means the enterprise sector.

In about 27% of all car crashes, someone was using their cell phone. You may think texting is the big problem here, but many fail to realize that even the smallest smartphone interaction could spell disaster. Thankfully, Google Maps has rolled out an overdue feature that'll help ensure a safer drive.

Throwaway phones aren't just for seedy criminals and spies—they can be useful for many everyday situations.
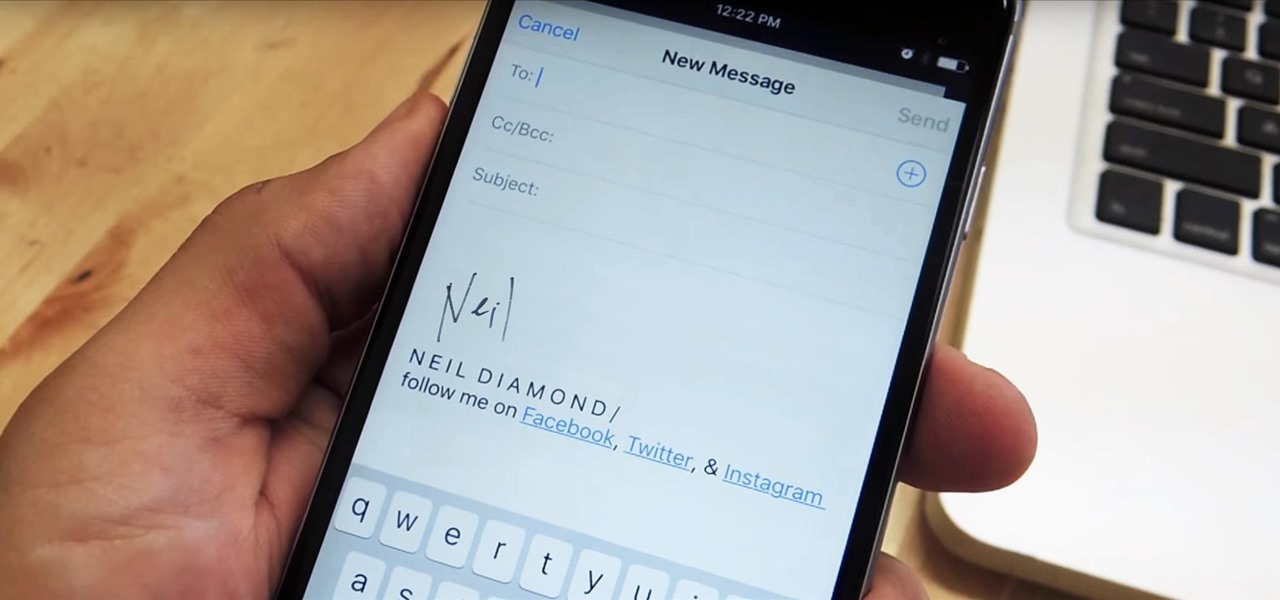
Emails sent from an iPhone, by default, are signed "Sent from my iPhone," which almost seems like a disclaimer in case the email has spelling or formatting errors. If your goal is to look professional while corresponding with coworkers or potential employers, then you're better off removing the signature completely and just typing your name out.
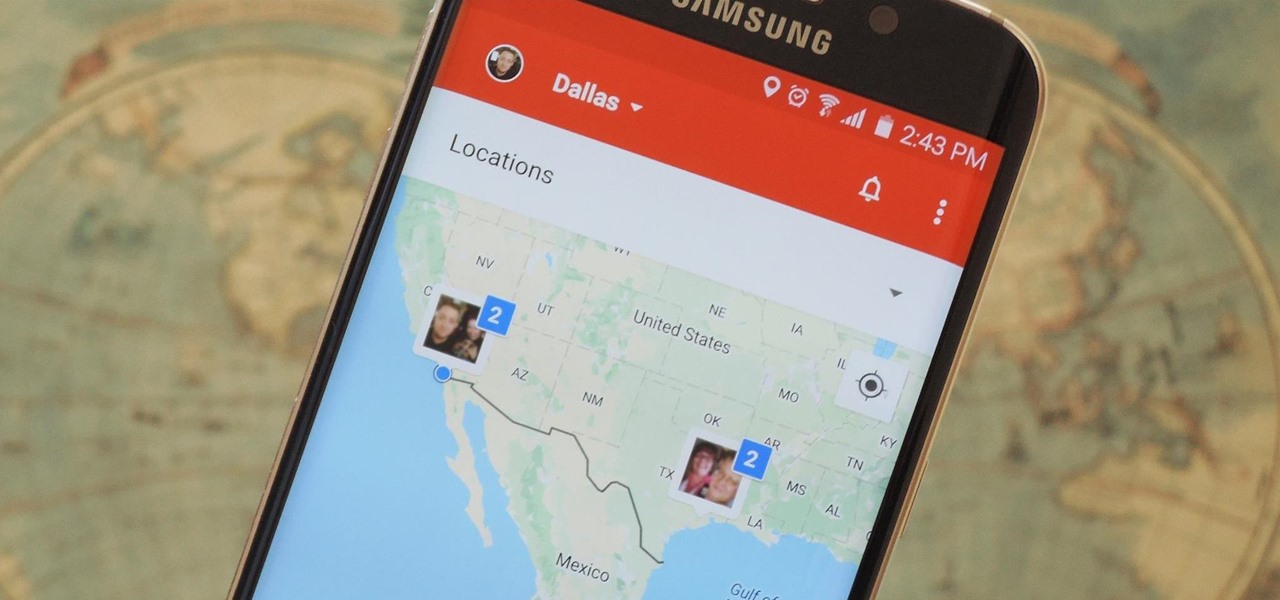
Instead of wasting time asking where your friends and family are at a given moment, then having them waste time by describing their location, there are several Android apps you can use that will automate this whole process. To top it off, it doesn't have to be about invading privacy or spying on someone, since most of these apps are offer two-way location sharing, or at least let you share locations only when you feel comfortable with it.

Most of you already know that a zero-day exploit is an exploit that has not yet been revealed to the software vendor or the public. As a result, the vulnerability that enables the exploit hasn't been patched. This means that someone with a zero-day exploit can hack into any system that has that particular configuration or software, giving them free reign to steal information, identities, credit card info, and spy on victims.

Welcome back, my novice hackers! In my series on cracking passwords, I began by showing off some basic password-cracking principles; developed an efficient password-cracking strategy; demonstrated how to use Hashcat, one of the most powerful password-cracking programs; and showed how to create a custom wordlist using Crunch. In this tutorial, I will show you how to create a custom wordlist based upon the industry or business of the targets using CeWL.

Electro pop has been big business since The Postal Service made their era-defining record in 2005, and few artists since have captured that magic as well as Owl City. If you fancy producing some electro pop yourself and have Reason 4, watch this video to learn how producing a good electro-pop song works using Owl City's "Cave In" as an example.

Looking for a fast way to thaw your meat without using the microwave? Thawing meat can be unhealthy if you do it without the proper care. Be safe! Here are two techniques that will give you great thawed meat that will be ready for dinner.
There's nothing more tedious, yet exciting, than watching surveillance cameras at work. They prey on the innocent and the unknowing. They protect businesses, workplaces, and homes. They catch criminals in the act, find hilarious anomalies, and are just darn cool when you're not the one that's supposed to be eavesdropping with them.

Right out of the box, iPhone is incredibly easy to use. If you want to get the most out of every feature, you’ve come to the right place. This video tutorial straight from Apple will teach you how to shop the App Store on the Apple iPhone 3G. The iPhone redefines what a mobile phone can do.

With the unemployment rate hovering at around 9.8% in California, many of us are still unfortunately without a job. Ergo, you must treat every meeting as an opportunity to network and find job leads. Which is why carrying business cards around is an absolute necessity. But given that purchasing cards cost money (and sometimes a LOT of money depending how nicely you want them done), why not save yourself cash by making your own business cards?

Benny from askbenny.cn teaches you some Mandarin Chinese words and phrases for use when making a formal business call.
Benny teaches you some Mandarin Chinese words and phrases for use during a business meeting.

Benny teaches you some Mandarin Chinese phrases to convey business etiquette.

In this episode of Gopher Haul you'll learn you can use an autodialer to market your business. This is a device that makes outgoing calls from a computer while you are out working. Then when you get back you can listen to the messages of people who want an estimate.

The year 2019 was filled with all the normal peaks and valleys of the tech business cycle, but this year was particularly important in a space as relatively young as the augmented reality industry.

The natural marriage between fashion and augmented reality is charging onward, but not just from the major brands we already know about.
In the wake of Apple and Google pitching augmented reality to schools, McGraw-Hill is stepping up its own augmented reality efforts for education.
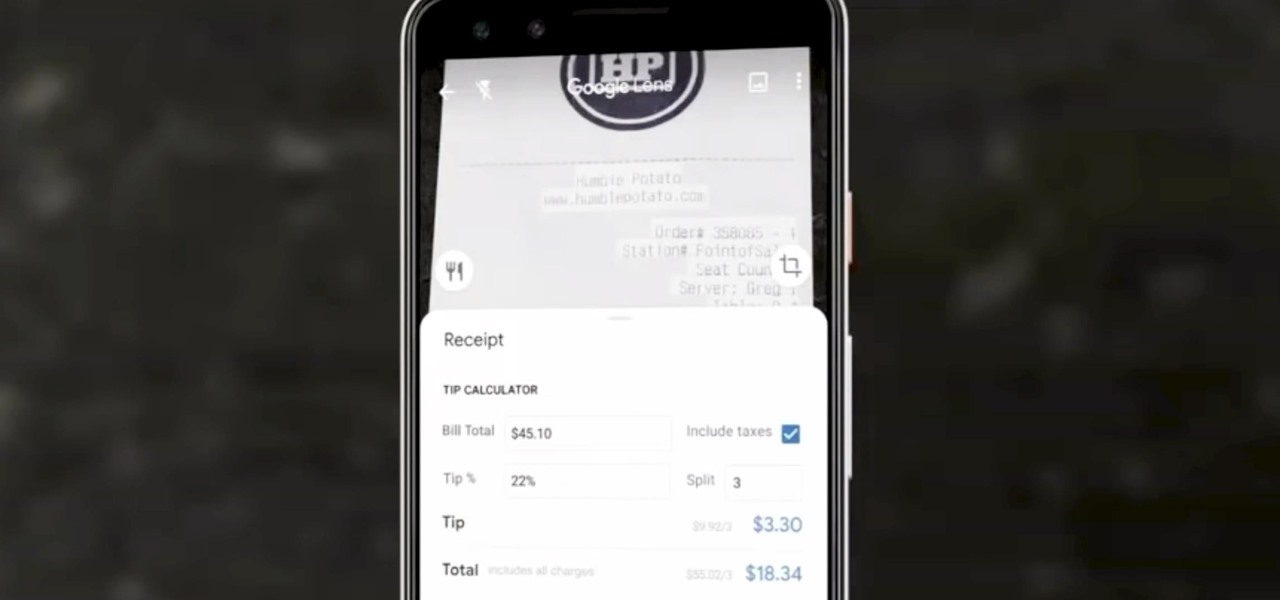
Google Lens can perform many different tasks with your smartphone's camera thanks to advanced machine learning, such as foreign text translations, landmark identification, and business cards to contacts conversion, to name a few. With this year's Google I/O conference, we have another cool Lens feature to look forward to — receipt calculations.

Months ago, we showed you some of the powers of Spatial, the HoloLens app that allows groups of workers to collaborate in augmented reality using 3D avatars.

Magic Leap's business strategy for bringing augmented reality to the mainstream has become even clearer via its latest funding round.

Spring is here across the US, but, through the lens of Snapchat and augmented reality, winter is coming to New York.

Just weeks after revealing plans to port one of its most vital augmented reality products from HoloLens to the smartphone world, Microsoft has finally opened the mobile software floodgates to the public.

While the tech industries giants and eager startups chase the dream of widespread consumer augmented reality, enterprise AR is living the dream today.

The Apple rumor mill is getting its first real workout of 2019, and this time the whispers are more exciting than usual.

Now that we've officially seen the HoloLens 2 and Microsoft has shown off the improvements and new superpowers of the augmented reality headset, what about the specs?