We're maniacs for mustard: we put it on our sausages, our salmon, our turkey club sandwiches... you name the dish, we find an excuse to spread mustard on it. So it's not surprising that it's a common item on our grocery list.
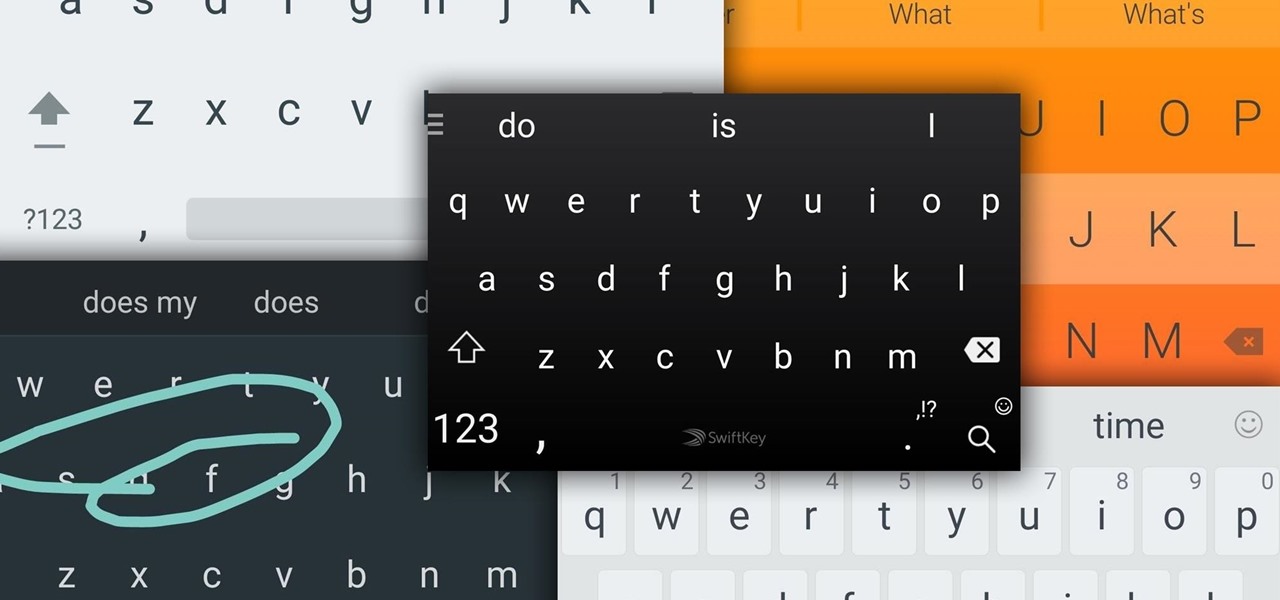
Google Now, Siri, and Cortana aside, the main way you interact with your smartphone is through the keyboard. Every app you use, every search you perform, every message you send—the most fundamental interface between you and your device is that handful of characters and those 26 letters on the bottom half of your screen.

New technologies in current-generations smartphones allow for much faster charging—Qualcomm Quick Charge 3.0, VOOC Flash Charge, and USB Type-C, for instance, can charge a phone up to 4 times faster than traditional methods. However, the majority of phones on the market still don't support these standards. So for the rest of us, I'll go over an easy tip that can charge any smartphone as much as 25% faster.

Welcome back, my greenhorn hackers! Throughout this series on Metasploit, and in most of my hacking tutorials here on Null Byte that use Metasploit (there are many; type "metasploit" into the search bar and you will find dozens), I have focused primarily on just two types of modules: exploits and payloads. Remember, Metasploit has six types of modules:

Hello Everyone! I wanted to share a free and open source note taking tool that I've been using for quite some time now.

Hello everybody Joe here. Today I will be demonstrating how you can find XSS vulnerabilities in a website and what you can do with them

One of my favorite things to do when I visit my parents is cook. Aside from the fact that I adore cooking with my mom, there's something comforting about returning to the kitchen that I first started playing in 20 years ago. Nearly all of the tools and appliances are the same ones that I used as a kid, and the familiarity is palpable.

In my opinion (and I suspect in the opinion of the masses), there is no greater snack food than potato chips. They're crunchy, they're salty, they're fried, and they're bite size; what's not to love? But I believe that, like almost all foods, potato chips can get even better. Especially if they're the most basic garden variety type of chip: sea salt.

From laptops to tablets, technology is taking over classrooms. Elementary schools offer kids tablets, and college students are bringing laptops into lecture halls, leaving their notebooks behind. Today, many students prefer putting their fingers to a keyboard rather than pen to paper, but are these helpful devices truly beneficial?

Welcome back, my neophyte hackers! In previous tutorials, we learned how to steal system tokens that we could use to access resources, how to use hashdump to pull password hashes from a local system, and how to grab password hashes from a local system and crack them.

What Is IPython? IPython is a richly featured replacement for the standard python interpreter. It offers a wider range of functionality, that the standard

The Nexus 6 is one of the few devices on the market that sports a 1440p "QHD" display. This means that the amount of pixels displayed is higher than almost any other smartphone, which sounds great on the surface, but is not without its drawbacks.

I know people who hate mayonnaise. I know people who detest ketchup. But I know almost no one that hates mustard, and that's because mustard has a complexity and depth that bland mayo and ketchup do not. Mustard runs the gamut from smooth and subtle to sharp and spicy, especially when you know how to make your own.

This is the best how-to's website that I've ever seen, and I wanted to join it. It taught me a lot, but, because I'm here to learn too, please correct me if I'm wrong.

Welcome back, my greenhorn hackers! Continuing with my series on how to crack passwords, I now want to introduce you to one of the newest and best designed password crackers out there—hashcat. The beauty of hashcat is in its design, which focuses on speed and versatility. It enables us to crack multiple types of hashes, in multiple ways, very fast.

Welcome back, my hacker novitiates! In previous guides, we have used one of the most powerful hacking platforms on the planet, Metasploit, to perform numerous hacks. They ranged from exploiting Windows XP and Windows 7/8 vulnerabilities, to installing a keylogger and turning on a webcam remotely. We have even been able to save the world from nuclear annihilation, see if our girlfriend is cheating, spy on suspicious neighbors, evade antivirus detection, and more.

There are a lot of instances where we find ourselves typing virtually the same phrase that we've typed many times before. Whether it's the standard spousal reply of "I'll be home in a few", or a work-related phrase like "I'll have that to you by the end of the day", typing phrases like these can feel very redundant at times.

Remember those horrible, soul-crushing studies from a few years back linking grilled meats with cancer? Unfortunately, they're still true, but scientists have recently found that an unexpected ingredient can curb some of the harmful effects of high-temperature cooking.

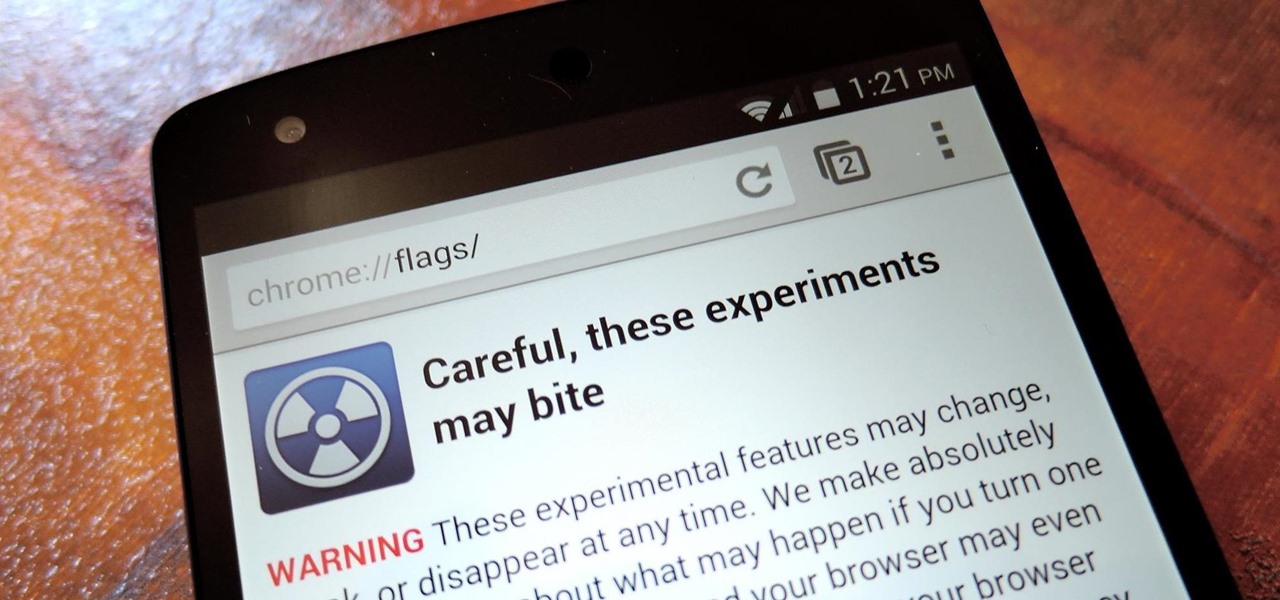
With the release of Jelly Bean, Chrome became the default web browser on Android. The wildly successful desktop browser was now fully entrenched in the world's largest mobile operating system.

Flavored extracts may seem like they'd be complicated to make, but there's a lot less to them than you'd think, and will cost you less in the long run.

Valentine's Day is a day for love, but it also just happens to be the time when every flower shop in town hikes up their prices. Chocolates are still relatively cheap, but I never understood why you have to give the gift of bigger love handles when something more creative gets the job done at a much cheaper price.

Apple's just released a new beta of iOS 7.1 for developers, Beta 5, which fixes some small bugs and adds some minor feature enhancements. With previous reports stating that the final version of 7.1 was slated for a public release in March, these early leaks are indications that the final will be released in the following weeks, shortly after the Golden Master version hits developers.

Welcome back, my rookie hackers! Many newbie hackers focus upon the technical aspects of hacking and fail to give enough attention to social engineering. In fact, I would say that technical hacks should ONLY be attempted if social engineering attacks fail. Why bother spending hours or days trying to hack a password if someone will simply give it to you?

In my first tutorial on Linux basics, I discussed the importance of hackers using Linux and the structure of the directory system. We also looked briefly at the cd command. In this second Linux guide, I'll spend a bit more time with changing directories, listing directories, creating files and directories, and finally, getting help. Let's open up BackTrack and getting started learning more Linux for the aspiring hacker.

Love or hate 'em, you've got to admit that cupcakes really had their moment. They started rising in popularity back in 2003 with the opening of Crumbs Bake Shop in Manhattan, and quickly became one of the most annoyingly ubiquitous food trends to date. Seriously. Type "cupcake" into Google. While I wouldn't turn it down if you put one in front of me (red velvet, please), I can't say that I was particularly disappointed to hear that the cupcake trend is coming to an end. I'm more of a cheeseca...

Who doesn't hate Auto Correct? There's nothing worse than hitting 'Send' only to realize that your phone betrayed you by changing a word so that your message doesn't even mean the same thing anymore—especially when it's going to someone like your boss or parents.

With the use of Terminal, anyone can run multiple instances of the same application on a Mac. When you have multiple windows open in a web browser, the windows are all running under the same Process ID (PID). But, with multiple instances, each has its own unique PID. So why would you want to run multiple instances of the same app? There are several reasons a person may run clones of the same application, but the most popular would be so that the user could multitask. Some applications, like t...

When I left off on our last hack, we had hacked into the ubiquitous Windows Server 2003 server by adding ourselves as a user to that system so that we can return undetected at any time. The problem with this approach is that a sysadmin who is on their toes will note that a new user has been added and will begin to take preventative action.

RFID chips are everywhere. They're in passports, credit cards, and tons of items you've bought in the last 5 years or so. Big retailers like Walmart started using tracking products with RFID as early as 2004, and today, they're used in everything from mobile payments to hospital record systems. Chances are, unless you're a hermit (in which case you wouldn't be reading this anyway), there's an RFID tag within a few feet of you. Photo by sridgway

It's already August, which means school will be back in just a few short weeks. If you're getting ready to start or go back to college, that means you'll probably be dropping a few hundred bucks on textbooks. Here are some of the best places online to buy, sell and rent textbooks so that you can get back to more important things, like making your papers look longer than they really are and getting around your school's website blockers. Plus you can spend your money on more exciting things, li...

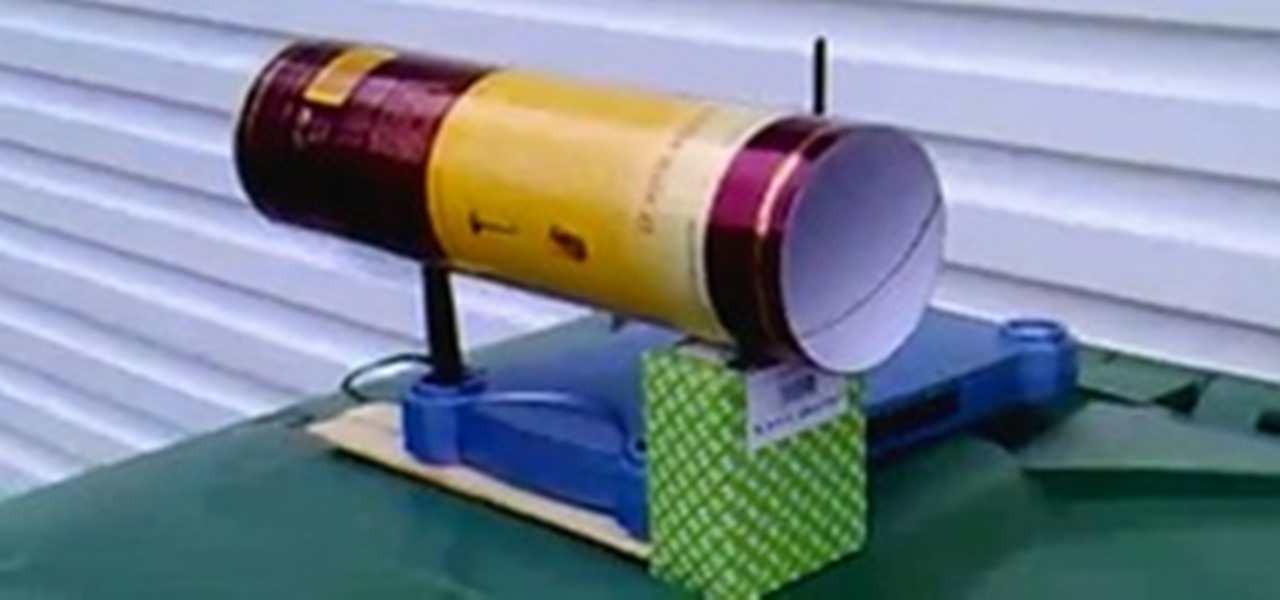
Wish your home wireless network was faster? You can always buy a signal booster, but if you'd rather not spend the money, here are a few tips and tricks to speed up your wireless connection, including how to make a homemade signal booster with things you probably already have lying around.

A minigame we built with redstone! Video: .

If you're tired of replacing the batteries on your remote control and you would rather have the TV remote charge by itself, grab a few solar cells, rechargable batteries, and a few extra odds and ends. With this mod to your remote, you can let light charge your remote and never buy another battery for it again!

Buy a DSLR just for the video? You're not alone. In this video tutorial from renowned DSLR cinematographer Philip Bloom and the staff of Vimeo, we receive some tips on how to set up a DSLR like the Canon 7D, T2i (550D) or 5D Mark II for shooting video.

Well, you've got your friends & family email account, your email account for buying junk and that little secret email you keep for all other reasons. If you've been looking for a way to get them all onto your AT&T BlackBerry, here's a clear & concise tutorial teaching you how to do just that.

So you've bought your fist sewing pattern and unfolded it - but now there all these lines and triangles and dots! What does it all mean? Where do you cut? Here are a few hints - don't forget to iron your pattern, it really does help.

Battlefield Bad Company 2: Vietnam might have the convoluted title of any map pack released in the history of gaming, but it is a great one and must-buy for all your BBC2 players out there. This video will teach you how to jump into three obscure hidden sniper spots scattered across the maps, allowing you to rack up kills while confusing and infuriating your opponents. Perfect.

If you want to engage in macro photography and can't afford a close-up lens, you may be in luck. By using a "G" lens (that is, a lens that does not have a built-in aperture ring) it is possible to reverse the lens and take close-up shots with your camera, without having to buy any additional equipment.

Dead or hot pixels are one of those annoying camera problems that won't make you buy a new camera but will piss you off for years. There's a free solution that may work for you though if you have a Canon 5D or 7D, and this video will show you how to do it with the sensor cleaning function.

Are you the kind of person who's always looking for a new way to scam people into buying them beer with one-sided bets? Then this is right in your wheelhouse. Watch this video to learn why it is impossible to blow a folded bottle cap into a bottle from it's rim and how you can use this to trick bar patrons and partygoers.