How To: Pronounce the English word "tacit"
Today's word is "tacit". This is an adjective which means implied or conveyed without words.

Today's word is "tacit". This is an adjective which means implied or conveyed without words.
In this AeroCast episode, UND Aerospace discusses the Slow Flight maneuver as performed in the Piper Warrior (PA-28-161), referencing the procedures and standards outlined in the UND Warrior Standardization Manual. All performance tolerances are based on the performance standards set forth by the FAA Private Pilot Practical Test Standards. Since the most critical phases of flight occur at airspeeds less than cruise, a pilot must always be comfortable with his or her airplane’s handling charac...

In this AeroCast episode, Anthony Bottini discusses the Power On Stall maneuver as performed in the Piper Warrior (PA-28-161), referencing the procedures and standards outlined in the UND Aerospace Warrior Standardization Manual. All performance tolerances are based on the performance standards set forth by the FAA Private Pilot Practical Test Standards. Power On Stall practice is vital in increasing a pilot’s proficiency in regards to stall recognition and stall recovery techniques during an...

Unless you have your own private airport (I’m looking in your direction John Travolta) then you will most likely have to coordinate your takeoffs and landings with all the other air traffic using your specific airport. Whether it be a towered or non-towered airport, this latest UND Video Standardization Lesson is designed to help you, the student pilot, become familiar and hopefully more comfortable with Airport Traffic Pattern operations.

Need internet access and you don't have a login? Hack into a private or controlled network with this tutorial. Thefixed.org also shows you how to build a smoke bomb!

Find the biggest files on your computer ordered by size. Learn to order folder by filesize so you can find the ones harboring the most diskspace terrorists. Learn to clear up your private data automatically and wipe it clean from being undeleted.

Technically it's the California Chardonnay vs. the French White Burgundy but since they both use the Chardonnay grape it's still a battle. In this video Gary tastes and compares two against two: 2004 Pessagno Sleepy Hollow Chardonnay and 2004 Beringer Private Reserve Chardonnay vs. 2003 Caves De Colombe Chassagne Montrachet and 2001 Matrot Puligny Montrachet Comb Ottes. See which Gary puts on top.

Isometric exercises are strength training exercises that don't let the joint angle and muscle length contract during the movement. This means that the exercise is done in a static position with the muscular intensity coming from the weights and your own body.

After a long day at work, your back can feel pretty sore. Fortunately, if you don't have enough cash to go to a chiropractor or massage studio regularly, there are some free and easy exercises you can perform at home.

Apple's new iOS 8 has a ton of new features, and so does their revamped Safari app, only some of the features aren't quite as obvious as others. In this guide, I'll show you my 5 favorite Safari secrets in iOS 8 for your iPad, iPhone, or iPod touch.

If you want to convince your friends that money is not an issue, then you can just burn it for real like Walter White. But if you don't really want to destroy your hard-earned cash, this burn trick is perfect for you. It just takes some basic chemistry and a few materials, such as salt, water, alcohol, tongs, and a source of fire. And of course—money.
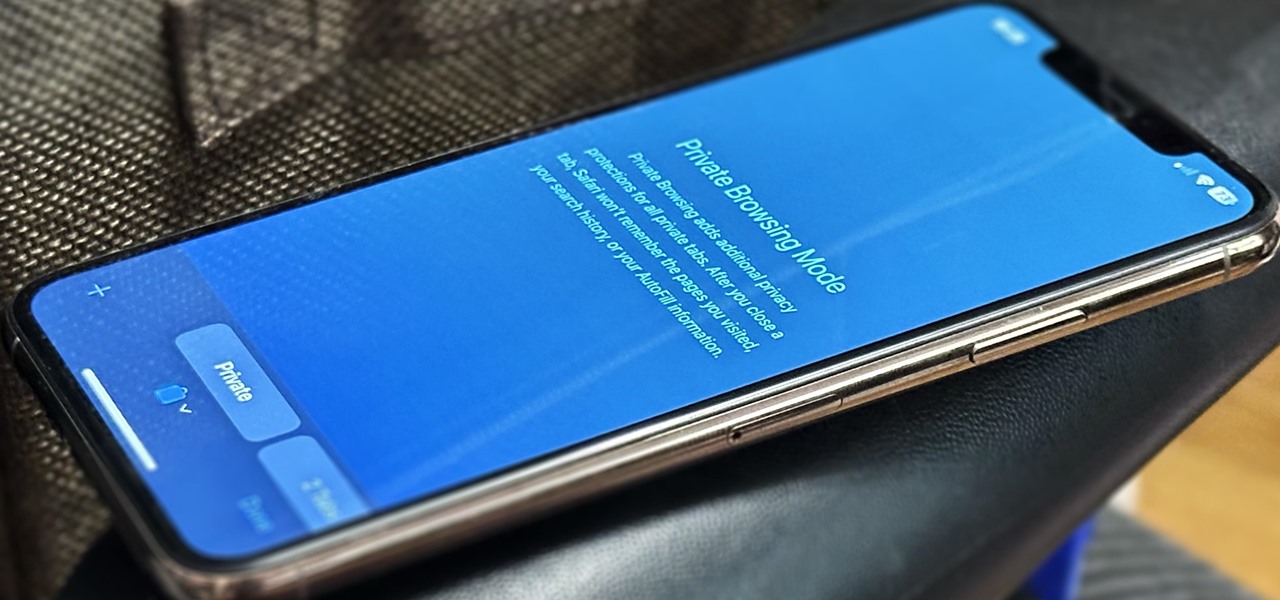
Private Browsing mode finally lives up to its name in Apple's huge Safari 17 update for iPhone, iPad, and Mac. So whether you search for things you don't want anybody to know about or want to ensure websites and trackers aren't eavesdropping on your activity, you'll want to update your devices pronto.
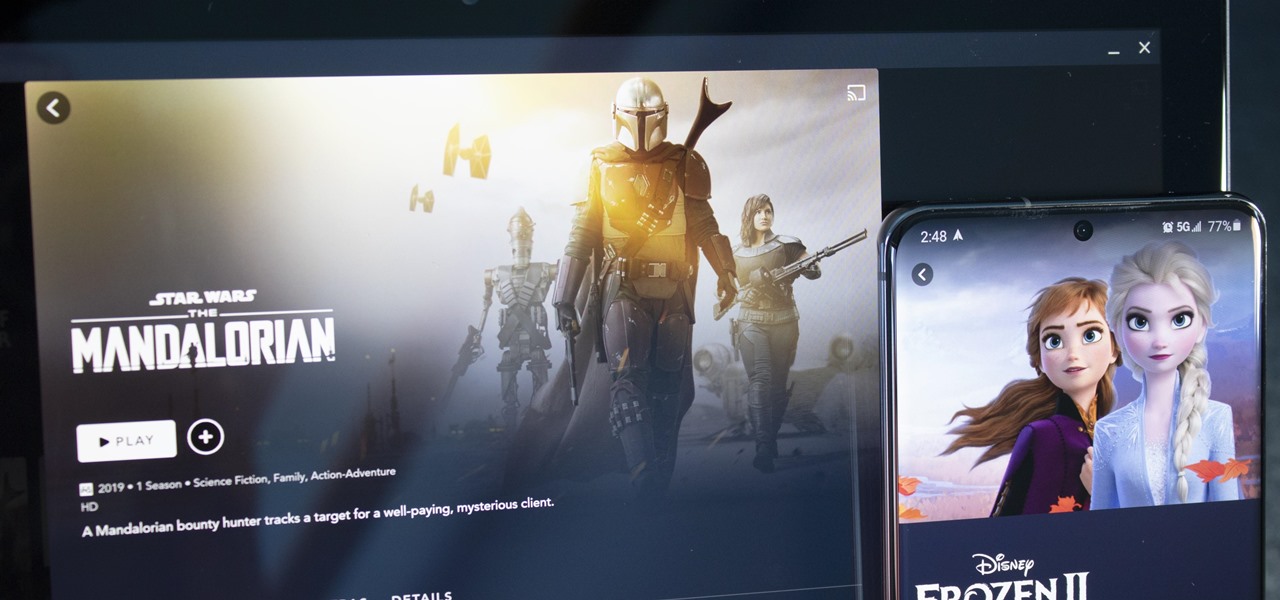
With shows like "The Mandalorian" and movies like "Frozen 2," Disney+ has quickly become a must-have streaming service. However, with Netflix, Amazon Prime Video, and Hulu, adding another subscription-based service can become expensive — but there are ways to trim down the cost.

If you have friends who aren't privacy-conscious, you've surely heard the old "What do I have to hide?" excuse. Despite the fact that billions of people are using the internet each day, many of them don't know the dangers that can find them. And many don't know the tools to combat them.
Many apps, including Facebook, Twitter, and Facebook, do not let you download videos, even if they are living on your own account. Saving these videos usually requires a third-party app or screen recorder, which is inconvenient and can result in loss of quality. However, TikTok, the newish popular short-form video platform, makes it easy to download videos — even if they're not yours.
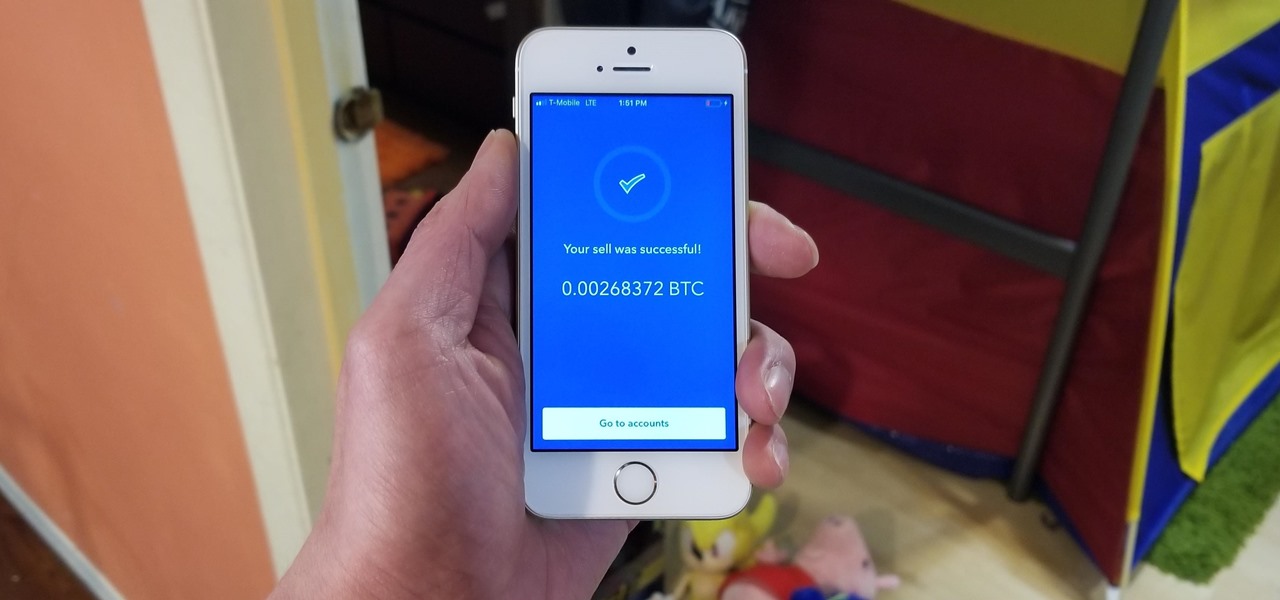
Coinbase has become the most popular mobile wallet app due in large part to its user-friendliness. The app takes the hassle out of buying and selling Bitcoin (BTC), Bitcoin Cash (BCH), Ethereum (ETH), and Litecoin (LTC), letting Android and iPhone users alike trade their favorite cryptocurrency in a few easy steps.

For $0.25 per transaction, PayPal will soon be allowing you to transfer money through their app that will get delivered within seconds rather than days.

With Instagram's archive feature, we have the pleasure of hiding all our stupid photos of #gettingcrunk from back in the day. This wonderful new IG feature will still allow us all to cherish those embarrassing moments in our life, yet hide them from those people we hope would never scroll so far down.

It's become a routine for many of us to ring in the New Year with pledges to finally get our budgets and finances under control. Unfortunately, it's also quite difficult to to keep those promises. Some of us will just dive into our resolutions and wing it as we move forward, which usually ends in failure. But even for those of us who plan carefully, obstacles along the way can spell doom for New Year's resolutions.

Whether you're a secret spy or just a regular person with a few secrets, you may want to keep certain information on your smartphone private, and it's totally possible on Android to do so.

Apple is set to unveil the iPhone 6 on September 9th, and shortly thereafter carriers like AT&T and Verizon Wireless will begin selling them online and in stores. So, if it's time in your contract for a device upgrade, it's time to start thinking about trading your current iPhone in for up to $400 in value.

In the wake of the NSA controversy and its subsequent fallout, many dashed towards finding means of secure communication—using private internet browsing and encrypted text messaging applications—out of fear of being spied on.

Craigslist is probably the greatest site ever created, and I'm just talking about it's classified section, both awesome and amazingly creepy. Seriously, spend 20 minutes scrolling through the personals and you'll never want to take your eyes off the screen. But I digress—Craigslist is also one of the most convenient places to buy and sell pretty much anything you can think of. I've used it to buy my bed, my old bike (which was stolen!), and my couch. And while Craigslist is great in many ways...

Do you find yourself getting rocked by your friends and relatives whenever you play Wild Ones on Facebook? A little more money would help right? This video will teach you how to use an easy cheat to acquire a theoretically infinite amount of money and coins. All you need are two Facebook accounts and two different web browsers and you can do this easily. Now get in there and buy yourself a better pet!

In this video, you'll use Scope and create a simple calculator while learning a little about private, public and protected properties in OOP programming. If you're looking to bone up your PHP coding skills you'll want to check this video out.

If you're Apple computer needs a little cleaning, not the hardware, but the software, then MacKeeper is the way to go. This application will help protect your hard drive from junk and other useless data, freeing up much needed space on your Mac. Also, you can recover files, hide private files, clean up your login items, apps and plugins, and more! Watch this video to see how to use MacKeeper.

In this tutorial, we learn how to sound like a biological woman while speaking. There are many different techniques to help you speak like a woman, including going into falsetto. This isn't about getting the sound, it's about learning how to not speak with resonance. You want to focus your voice up in your throat instead of deep down. You probably haven't used the muscles for this voice, so using falsetto is a great way to practice. You may be able to speak a few minutes and feel yourself fal...
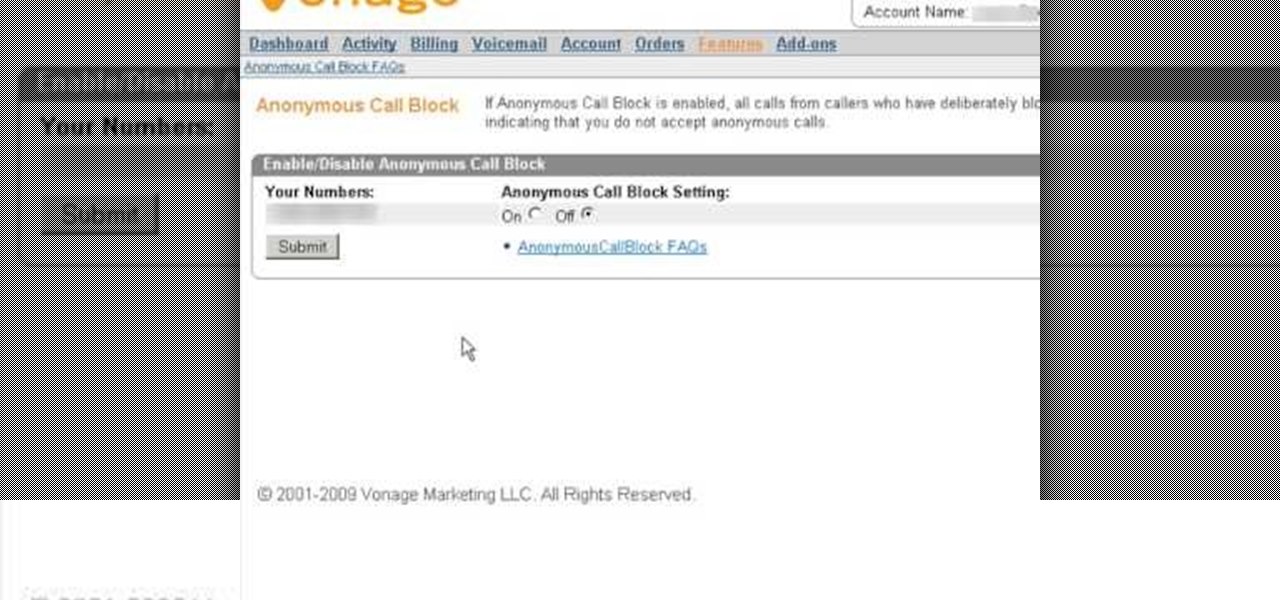
If you are looking for a way to prevent telemarketers and nothing else is working, consider signing up for Vonage's call blocking feature. In this tutorial, brought to you straight from the professionals at Vonage, learn how to set your phone to block any incoming call without a number attached to it.
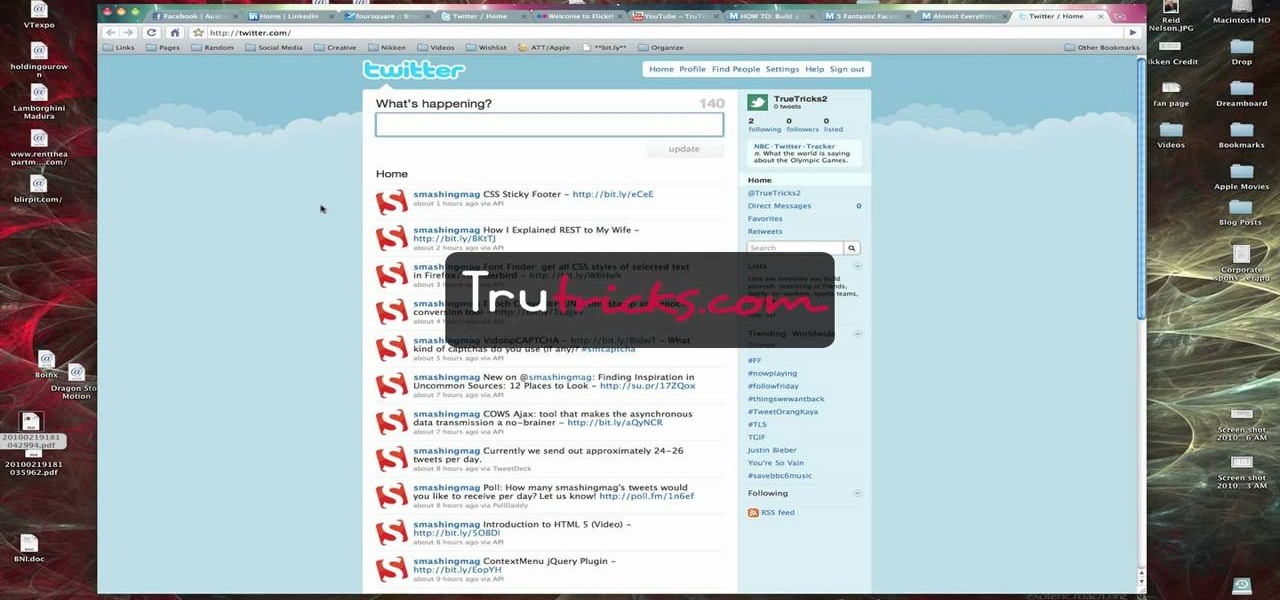
Brian explains us how to use Twitter, one of the best social media networks out there. One thing to notice is that Twitter allows you to send text messages up to 140 characters. In the right corner you can see you account name and your avatar which can be changed from the settings menu. Twitter allows you to follow people and be followed by people. Basically when you follow people you will be able to see messages they post and when people follow you, they will see what you post. Twitter is a ...

Throwing a block party is a great way to meet your neighbours! Block parties are perfect for hot summer nights when no one wants to be stuck indoors. These parties are fun and easy to throw, even on a budget. Check out this video for information on how to throw a rockin' party for your neighborhood without spending much money.

Email is one of the least private and least secure forms of communication, although few people realize this. MixMaster is one way to allow secure, anonymous communication even over the very public medium of email. This tutorial will get you started with MixMaster quickly and easily.
If you're using the Private Browsing feature in Safari, you'll still need to do more to keep your surfing history secret. This helpful software video tutorial shows you how to cover your tracks in the Apple application Safari.

This is a very basic introductory video that teaches you how to successfully install Quartz Composer on your MAC OSX 10.5 Leopard. Quartz Composer is a node-based graphical data software that uses visual programming language. Built exclusively for use on the MAC OSX, it's a handy software for graphic designers.

Ever a hacker can have their own business that goes beyond cashing in on profitable bug bounties. With the right skill set and certifications, an ethical hacker could build a cybersecurity firm, become a penetration testing for hire, or even just consult on preventive measures to defend against black hats. But learning how to start and grow a business is rarely easy.
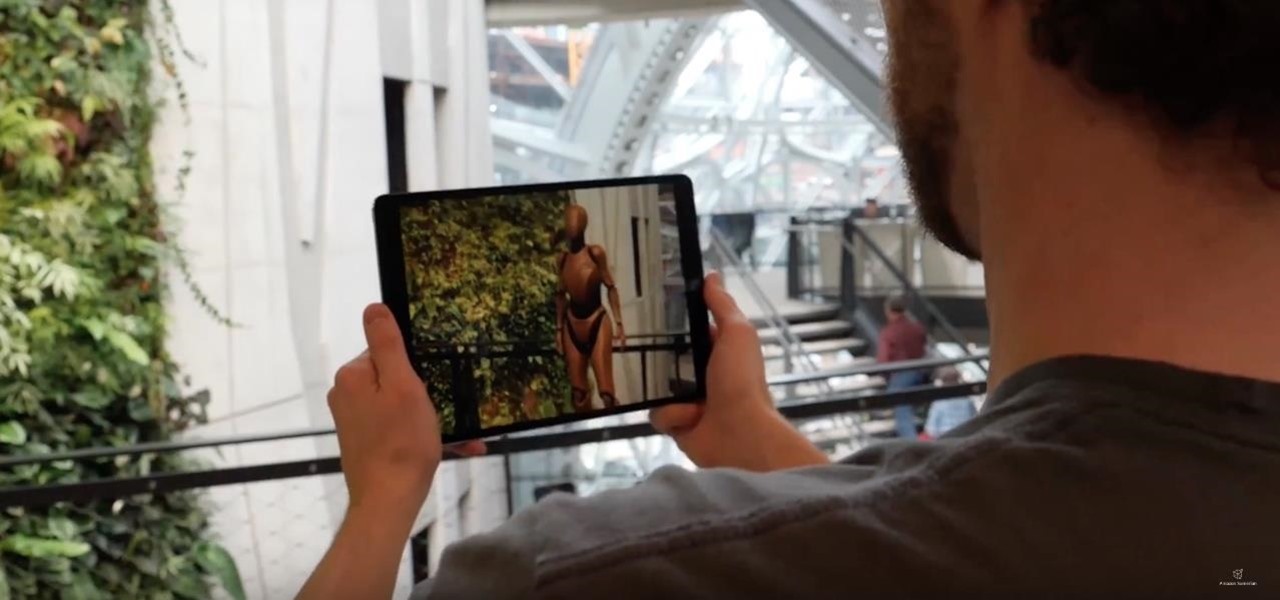
Amazon Web Services is calling up an age-old tactic of the tech industry — the hackathon — to drum up excitement and encourage the development of apps built on the Amazon Sumerian AR/VR platform.

Uber drivers do a lot for us. They sit through traffic, make conversation, put on our favorite tunes, drive us however far we need to go, and they work long hours. Some even have to deal with people who may have had too much to drink, which we all know can be obnoxious. So yeah, we'd say that it's about time for Uber to include a tipping feature in their app.

Welcome back, my greenhorn hackers! As expected with Null Byte's dramatic growth over the last year, we have added many new aspiring hackers who are still lacking in the basics of networking. In addition, with the new "White Hat" certifications coming out shortly, the exam will require some basic networking skills and knowledge to pass.
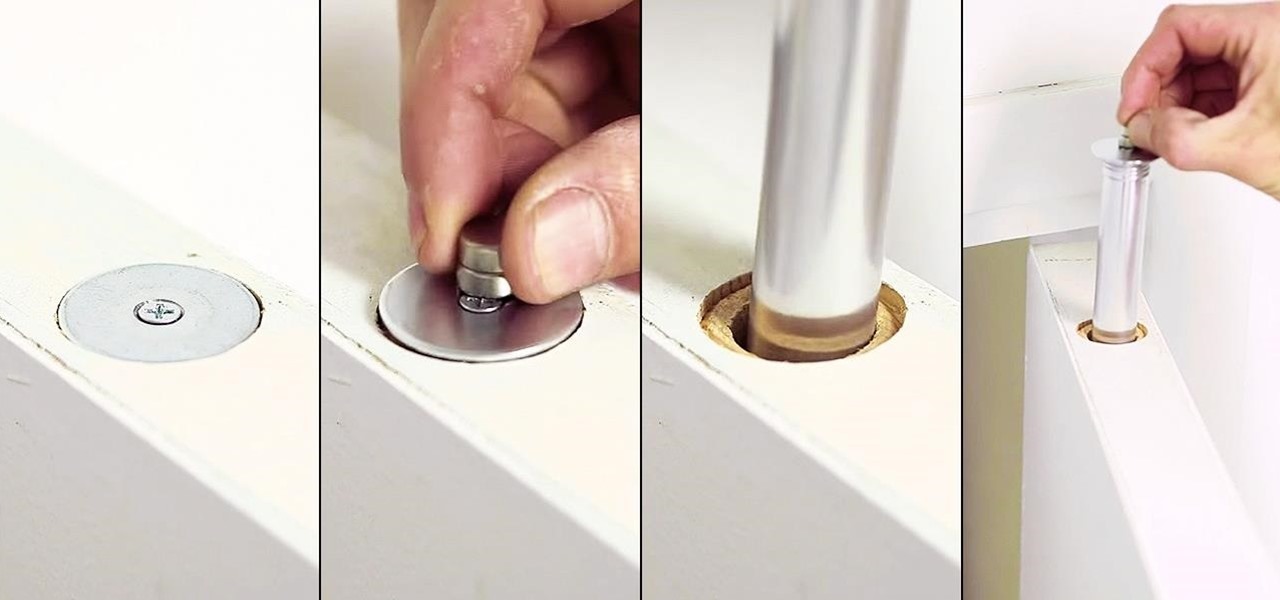
Thanks to the internet and its increasingly lack of privacy, secrets don't even seem safe in our own homes anymore. So how do you hide your secrets, stash your cash, or keep your valuable jewelry out of sight where no one can find it? Well, the answer might be right above you... if you're standing under the threshold of a door, that is.

Welcome back, my novice hackers! In a recent tutorial, I showed how the SNMP protocol can be a gold mine of information for reconnaissance on a potential target. If you haven't already, I strongly suggest that you read it before progressing here, as little of this will make much sense without that background.
Make sure your private documents are completely secure. This episode by Tinkernut deals with not only encrypting your files, but also hiding them in a hidden volume.