While a release date for Harry Potter: Wizards Unite has not yet materialized, co-developers Niantic and WB Games have finally released gameplay footage and an in-depth game description to whet the appetites of eager Harry Potter fans.

It looks like Facebook really likes Google's augmented reality leadership talent, as the social media giant has hired away another employee from the AR and VR team at Mountain View to lead its team for a product that brings Facebook's AR platform into homes.
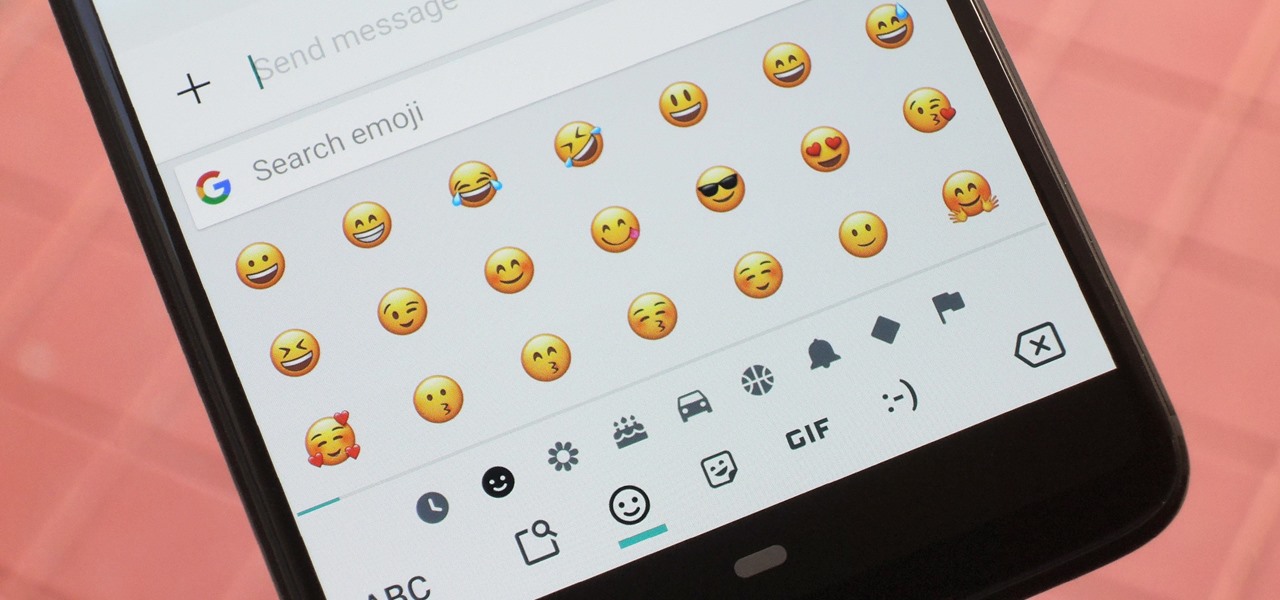
There's been a lot of fanfare as iOS 12 rolls out, and as an Android owner, you might be feeling left out. There's no need to feel that way, though. You don't have to choose between running out to get a new iPhone or being stuck with only your Android's features — at least when it comes to emojis. This is one of those rare times in life when you can have it all.

Apple's macOS operating system is just as vulnerable to attacks as any Windows 10 computer or Android smartphone. Hacker's can embed backdoors, evade antivirus with simple commands, and utilize USB flash drives to completely compromise a MacBook. In this always-updated guide, we'll outline dozens of macOS-specific attacks penetration testers should know about.

Among all the new Magic Leap app announcements made at the recent L.E.A.P. conference, an update to one of the company's major in-house apps went mostly unnoticed: Create 1.1.
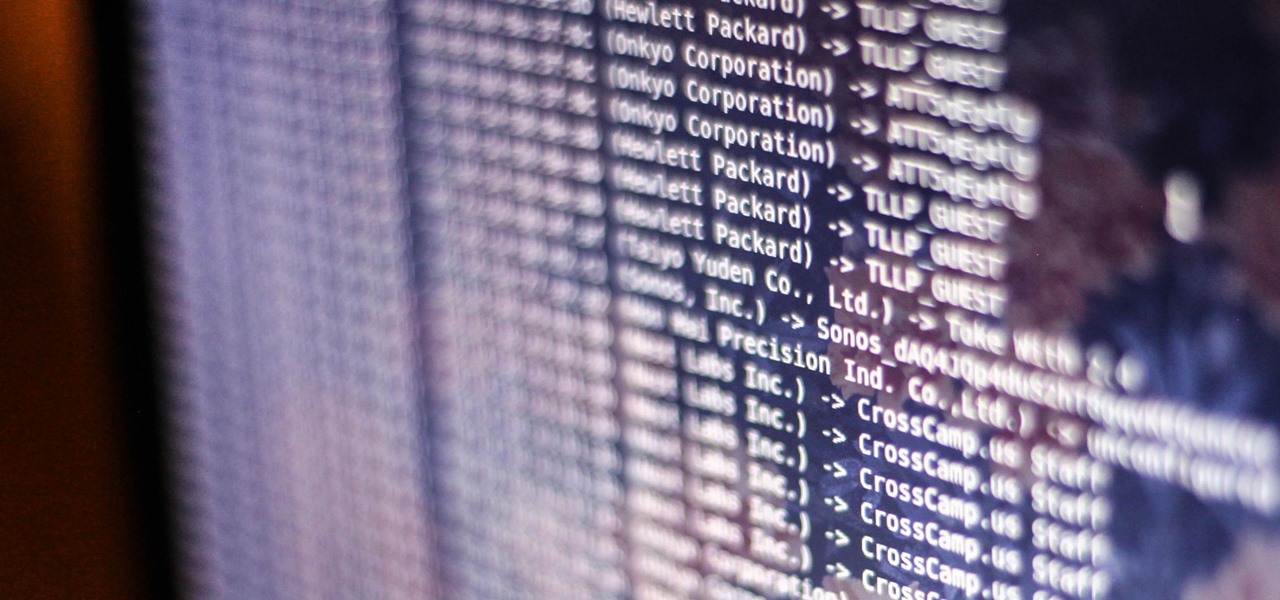
Smartphones and laptops are constantly sending Wi-Fi radio signals, and many of these signals can be used to track us. In this guide, we'll program a cheap IoT device in Arduino to create hundreds of fake networks with common names; This will cause nearby devices to reveal their real trackable MAC address, and it can even let an attacker take over the phone's data connection with no warning.

Venom, the latest in a long list of comic book characters to headline its own movie, is known by comic book fans by his catchphrase, "We are Venom."

The famous Flappy Bird (technically Flappy Droid) game is still around in Android 9.0 Pie. First introduced in 5.0 Lollipop, the game was originally the version number easter egg for the new Android update. But after Android Marshmallow, Google began to hide it from its usual location, and Pie continues this tradition.

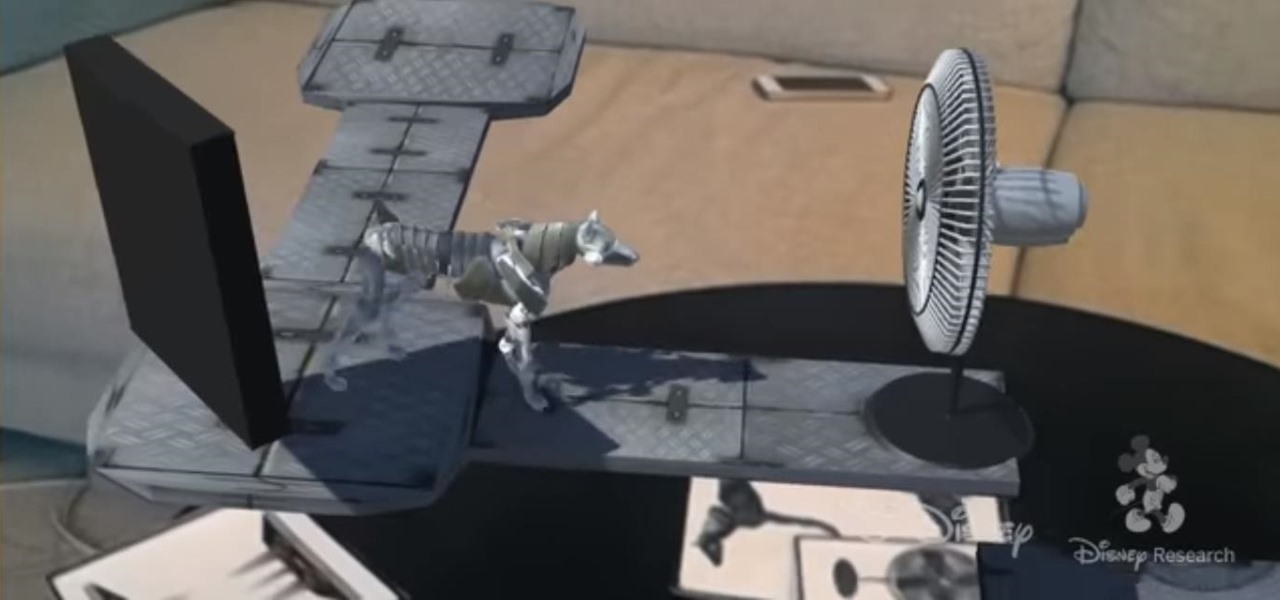
A new augmented reality framework from Disney Research could make it possible for fans to take selfies with an augmented reality Mickey Mouse, Darth Vader, or Iron Man that mimic the user's poses.

Developers creating login systems know better than to store passwords in plain text, usually storing hashes of a password to prevent storing the credentials in a way a hacker could steal. Due to the way hashes work, not all are created equal. Some are more vulnerable than others, and a little Python could be used to brute-force any weak hashes to get the passwords they were created from.

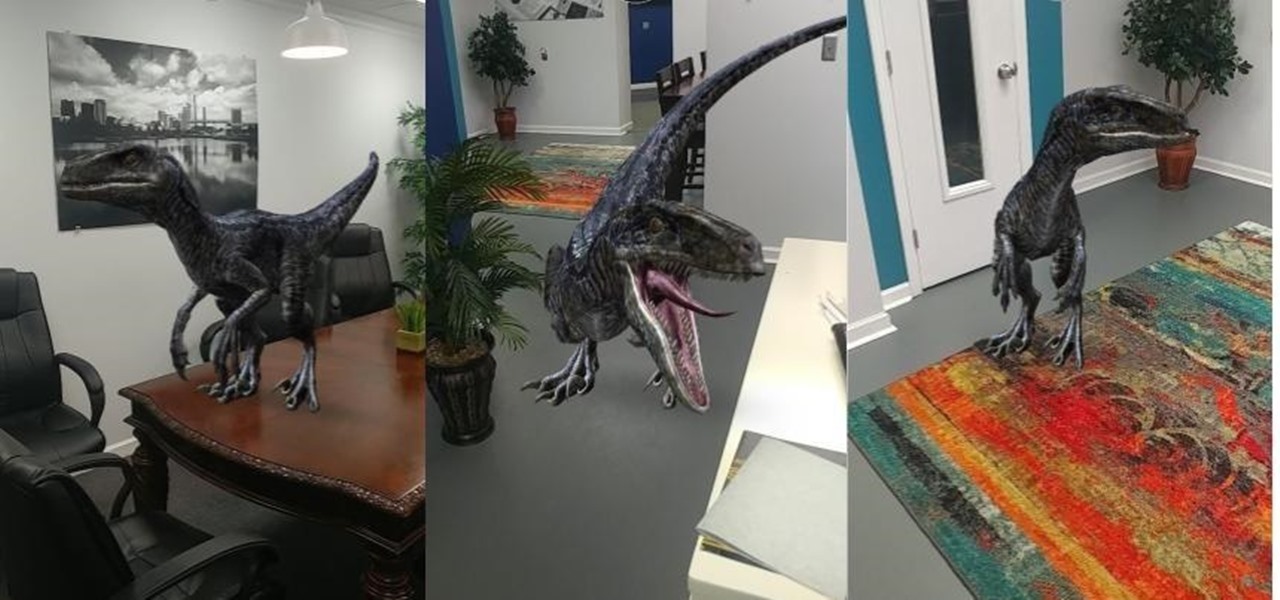
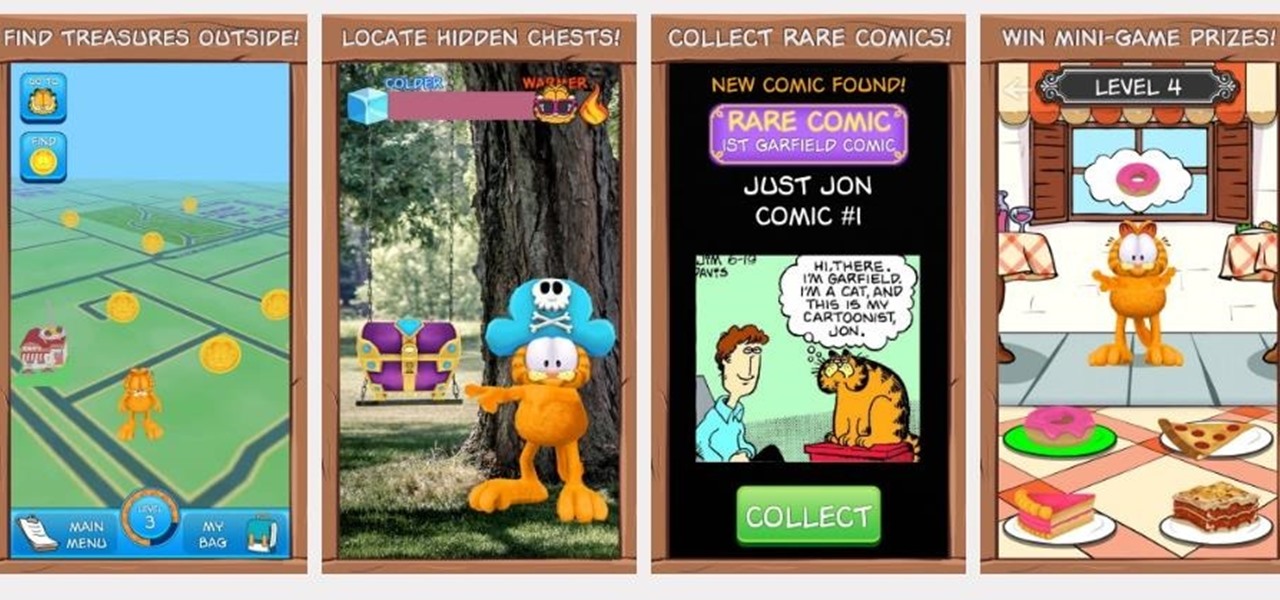
While mobile gaming, in the 10 years since the App Store launched, has matured to console-level quality, premium augmented reality games built with ARKit (or ARCore) have been scarce.

Augmented reality avatars that mimic facial expressions are no longer the exclusive province of Animojis on the iPhone X or AR Emojis from Samsung. Camera app Snow has added its own alternative to Apple and Samsung's features, which it also calls AR Emoji, for iOS and Android.

Kitten Planet, a spin-off company that grew up in Samsung's C-Lab incubator, has developed a connected toothbrush that teaches and motivates children to brush their teeth better via augmented reality while tracking their performance.

With the heavily anticipated installment of the God of War game series arriving on April 20, PlayStation has taken the opportunity to make its first foray into mobile augmented reality with a companion app.

Mobile gamers who grew up on J.K. Rowling's fantasy epic have yet another reason to rejoice, as Jam City's Harry Potter: Hogwart Mystery is slated to touch down on both iOS and Android on April 25. But if you can't bear the wait, there's a little hack you can do to give the game a try right now.

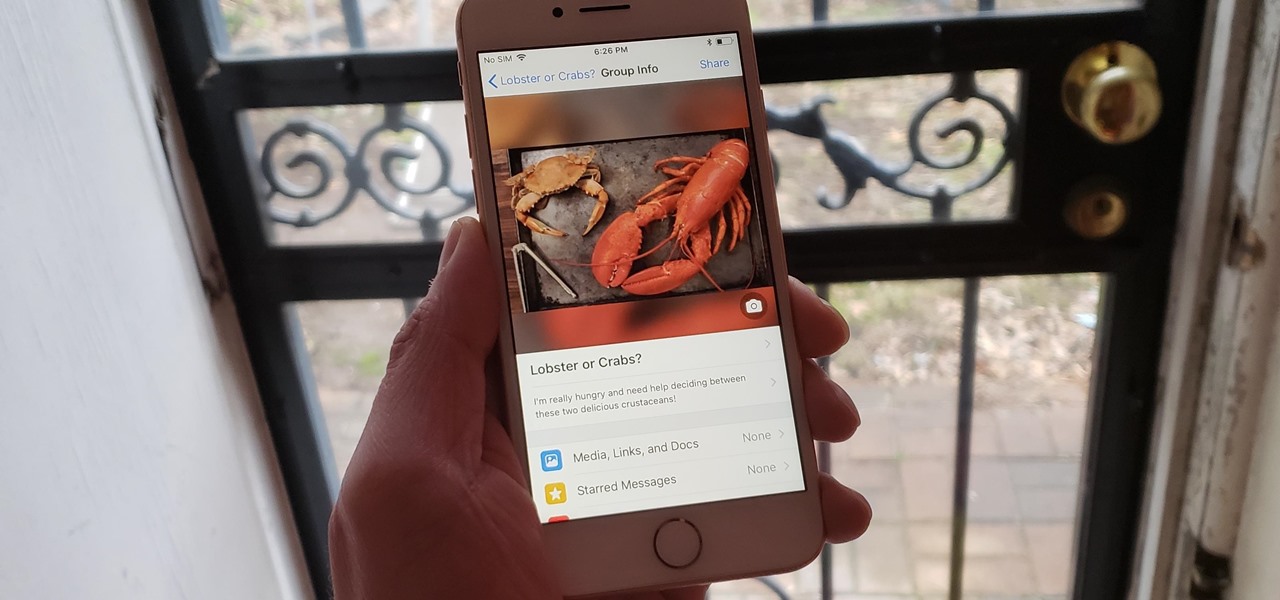
There's a fine line between order and chaos in group chats. With all the cross-talk, threads can easily devolve into a random mess that has nothing to do with the original discussion topic. WhatsApp group chats certainly aren't immune to this problem, but they've recently taken a step in the right direction.

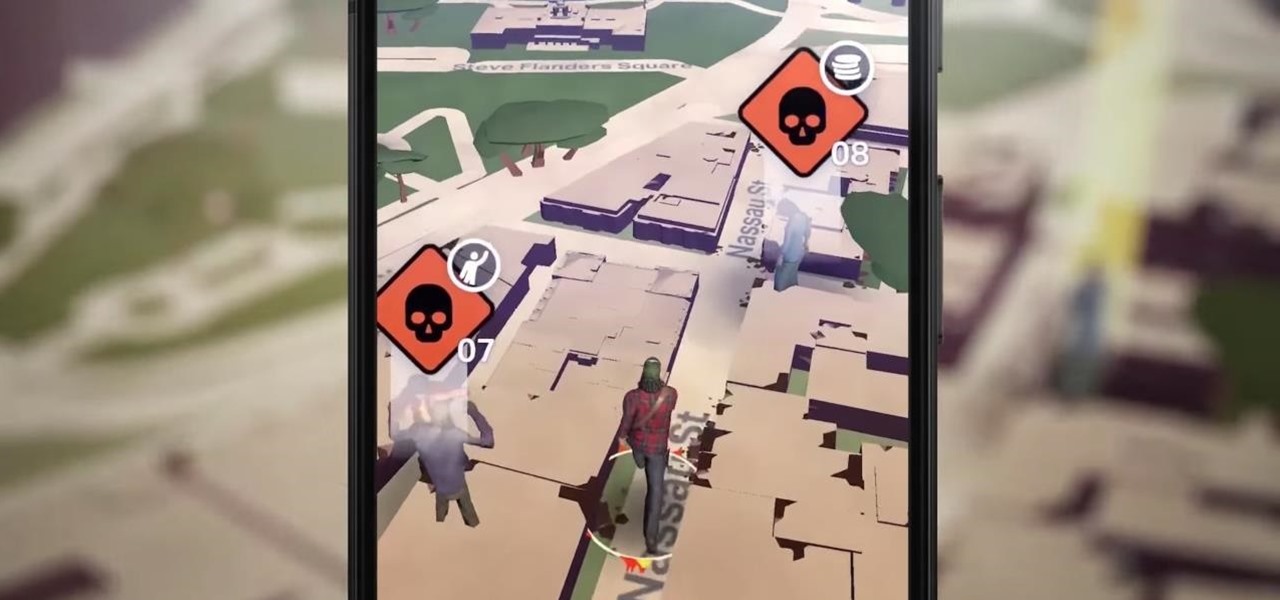
Ever since the announcement of The Walking Dead: Our World game last fall, publisher AMC and developer Next Games have been quiet about the title. Almost too quiet.

Snap Inc.'s dedication to augmented reality has expanded the world lenses in Snapchat to our own Bitmojis. While it's great to see our characters interacting with real environments, we haven't seen them connect to other Bitmoji in AR space. That all changes with "3D Friendmojis," a lens from Snapchat that lets you stage scenes between your Bitmoji and a friend's.

A recent update to Facebook's News Feed could significantly broaden its reach when it comes to delivering augmented reality content.

If you're an Android user, you're very likely jealous of your iPhone friends who have access to the wide, wonderful world of augmented reality thanks to ARKit.

Facebook just ratcheted up its ongoing augmented reality war against the competition by stealing away Google's director of product for AR, Nikhil Chandhok. In his new role, the executive will serve as Facebook's director of product on the company's Camera/AR team.

During our last adventure into the realm of format string exploitation, we learned how we can manipulate format specifiers to rewrite a program's memory with an arbitrary value. While that's all well and good, arbitrary values are boring. We want to gain full control over the values we write, and today we are going to learn how to do just that.

On Wednesday, Apple released a new batch of Animoji characters that gives iPhone X users more virtual masks to play around with, but what many have been waiting for is an app that lets you put on a virtual mask of another person, not an animated emoji. Well, that day has finally arrived.

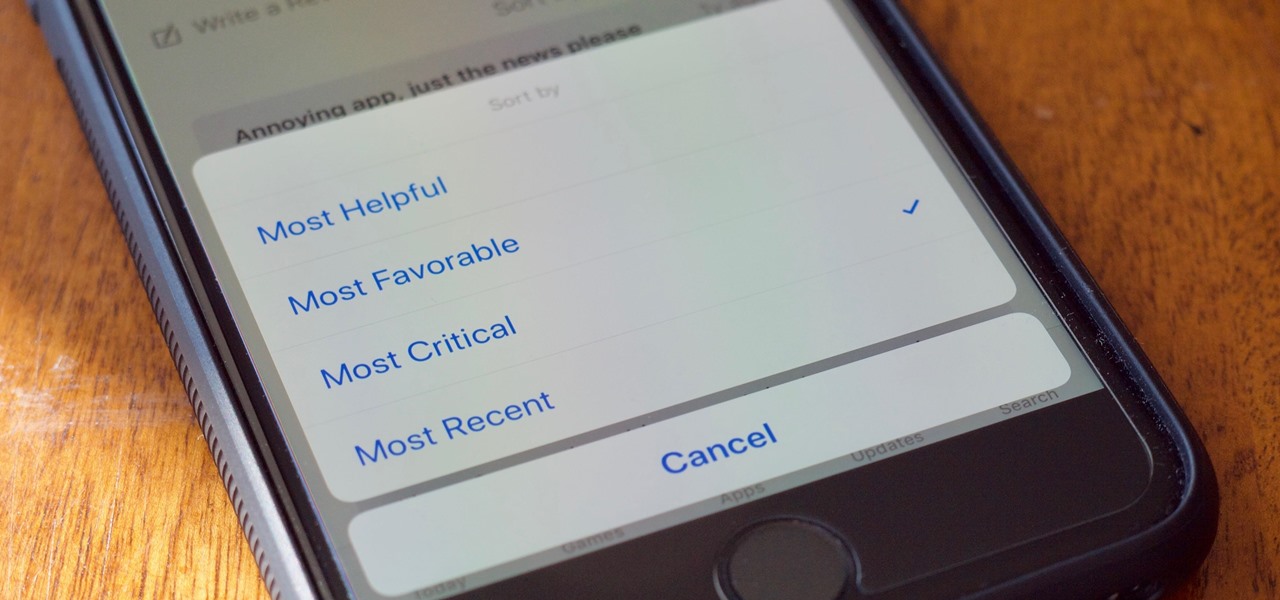
With the release of the iOS 11.3, iPhone users have new features to both sift through and look forward to, such as increased battery health information and control, new Animoji on iPhone X, and Health Records in the Health app. A smaller change with the update, however, is also a useful one — a new way to sort App Store reviews.

Over the years, the internet has become a dangerous place. As its popularity has increased, it has attracted more hackers looking to make a quick buck. However, as our dependency on the web grows, it becomes increasingly difficult to sever all ties. This means we have to protect one of our weakest points, the password.

If you want your own lightsaber, you don't need to be a Jedi or have kyber crystals in your possession; now, thanks to augmented reality, all you need is an iPhone and a rolled up piece of paper.

If you ever thought the Snorlax in Pokémon Go should be taller, and you have an iPhone compatible with ARKit, get ready to look up.

Researchers at Disney have demonstrated the ability to render virtual characters in augmented reality that are able interact autonomously with its surrounding physical environment.

The first teaser for Jurassic World: Fallen Kingdom just hit computer screens on Sunday, but now plans for an augmented reality book for the film have also emerged.

Death Road to Canada has finally arrived for Android, and it quickly took over our roundup for the best paid action games. Widely regarded as a top contender for the best video game of 2017, it came as no surprise when it easily surpassed all the other games in our list to grab the top spot for both Android and iPhone.

Google just unveiled it's biggest search product in recent memory, except this time the search giant is looking to take over the world of virtual objects.

The first big update to iOS 11 since its release in mid-September just came out, so check your iPhone for a software update to iOS 11.1, because there are a few things you'll want from it. While there's no sight of Apple Pay Cash or Messages in iCloud, there are some significant improvements you'll need to know about.

Until Star Wars Jedi Challenges arrives in November, a forthcoming ARKit revision of HoloGrid: Monster Battle from Tippett Studios and Happy Giant, might be the closest most Star Wars fans can get to playing the HoloChess game from the movie.

One of the byproducts of the success of Pokémon Go was the viral images that made the rounds on social media of people putting Pikachus, Charmanders, and their brethren in compromising positions. Snapchat has a similar claim to fame, most recently with the inexplicable popularity of the dancing hotdog.

Zenko Games makes no apologies for its influences. In fact, they cite them explicitly in their own promotional materials for Diamonst AR.

Another day brings another Apple ARKit demo, this time for a first-person role playing game that inserts villagers, vendors, and villains into real world locations.

If imitation is the sincerest form of flattery, then Niantic must be blushing constantly, as numerous copies of Pokémon GO have spawned over the past year or so, seeking to capture the same success, often adding the lure of tangible prizes from brand partnerships.

The Sharknado franchise is, somehow, releasing a fifth movie "Sharknado 5: Global Swarming" (groan) next month. In anticipation of the film's release, the company has decided to create an augmented reality mobile game called, prepare yourself, "Sharknado: ShARkmented Reality".

A patent from Universal was filed today looking to improve the visual experience at Universal Studios Parks.

The way we tell stories is about to change. Imagine you're hearing a story when suddenly characters and images from the tale start to appear in your world. This immersive way of storytelling is in the not-so-distant future thanks to the Microsoft HoloLens and Rémy Martin.