The most used and most washed articles of clothing are undergarments. Underwear, specifically bras and panties, are in desperate need of attention after each and every use. They're not like a pair of jeans, wearing them twice in a row is not a good idea, nor clean. Shabby’s not chic when it comes to lingerie. Use a little extra care to keep your lace and silk bras and panties looking good.

Follow this video which provides a good simple explanation on how to do a great hairstyle in a few minutes. When wearing a dress which has a lot of ornaments and details around the neckline it is a good idea to avoid having your hair in the way. Thus by applying a half up half down hairstyle you can be elegant in your hairstyle while also showing off your dress. Apply a heat protectant to your hair in order to retain a better look especially if the event is going to be held outdoors. The next...

Xteeener wants to show you how to make the cool easy Updo Bun. Materials required:

Automation has been a buzz word for quite some time now, but the principles behind it are as strong as ever. For a hacker or pentester, Bash scripting is one form of automation that cannot be ignored. Virtually any command that can be run from the terminal can be scripted — and should be, in many cases — to save valuable time and effort. And a Bash script just happens to be great for recon.

Many popular IoT devices have terrible security. For instance, a hacker who's on the same Wi-Fi network as a Sonos speaker can assume direct control over the device's behavior. If an IoT device doesn't secure the messages used to control it over a network, it's easy for somebody to write a few Python scripts to make it do whatever they want.

A powered-off MacBook can be compromised in less than three minutes. With just a few commands, it's possible for a hacker to extract a target's password hash and crack it without their knowledge.

It's not uncommon for hackers to attempt to move laterally between devices in proximity of a compromised device to maintain a prolonged presence in the network. Malware utilizing USB flash sticks to self-replicate and compromise air-gapped machines isn't a new concept.

With an ordinary birthday card, we can introduce a physical device which contains malicious files into someone's home and deceive them into inserting the device into a computer.

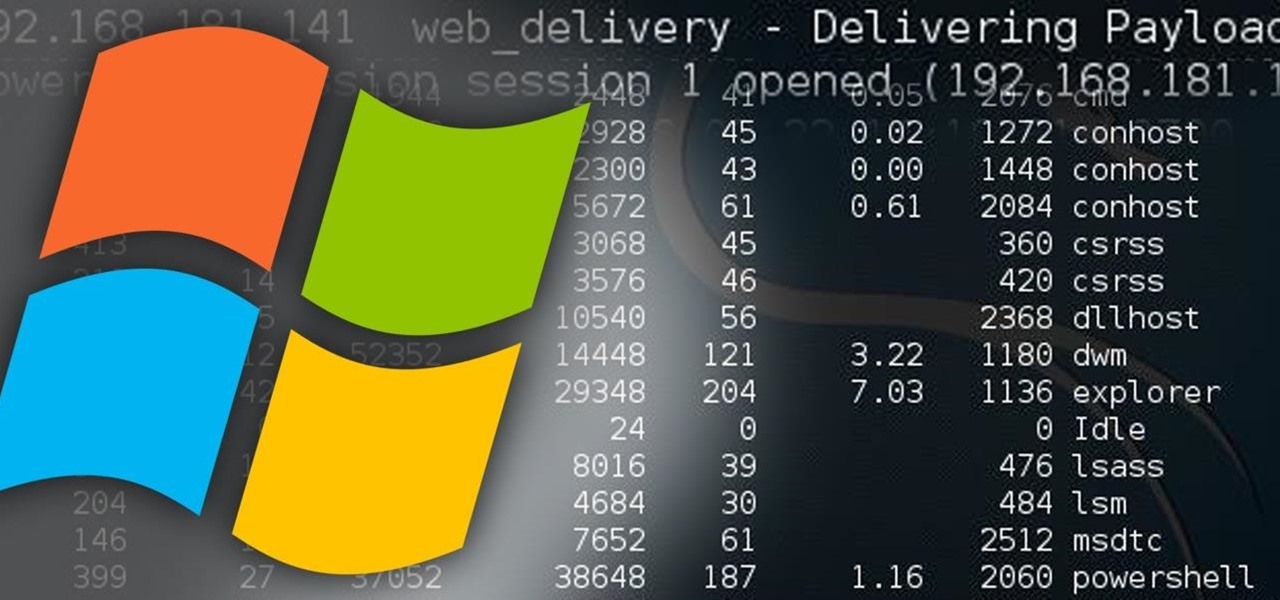
PowerShell Empire is an amazing framework that is widely used by penetration testers for exploiting Microsoft Windows hosts. In our previous guide, we discussed why and when it's important to use, as well as some general info on listeners, stagers, agents, and modules. Now, we will actually explore setting up listeners and generating a stager.

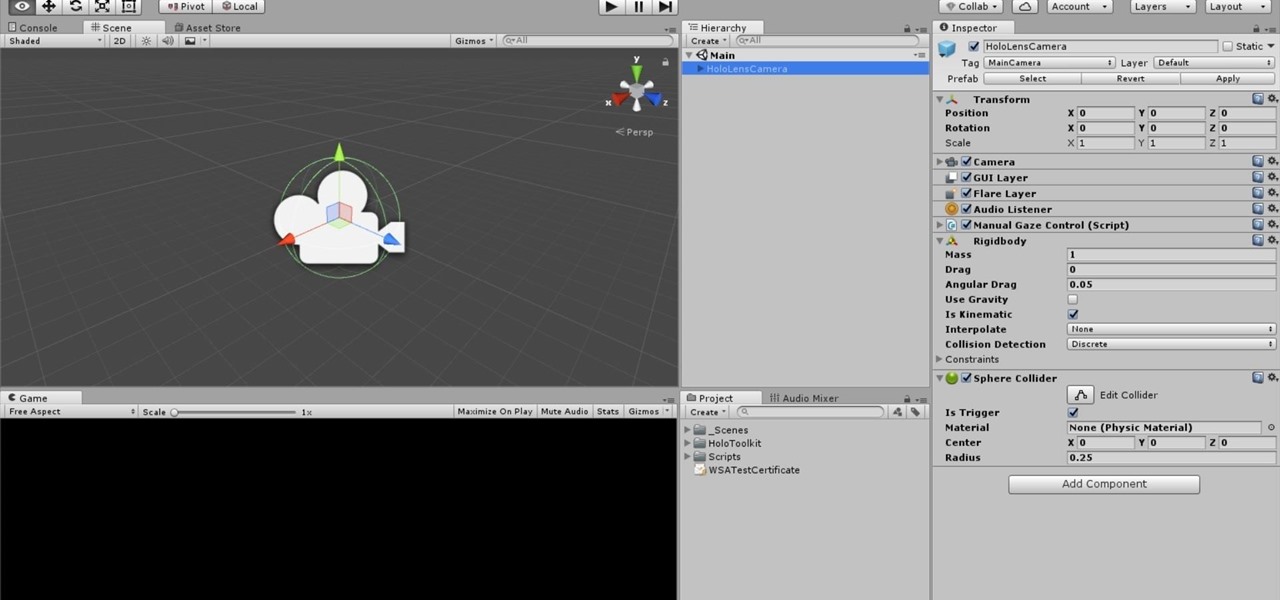
One of the truly beautiful things about the HoloLens is its completely untethered, the-world-is-your-oyster freedom. This, paired with the ability to view your real surroundings while wearing the device, allows for some incredibly interesting uses. One particular use is triggering events when a user enters a specific location in a physical space. Think of it as a futuristic automatic door.

It's the bane of many a tech geek's existence that the customizability of Android software cannot be combined with the sleek design of the iPhone. A new Kickstarter project titled Eye, however, is looking to change that with a new iPhone case that allows you to combine the two.

Welcome back, my hacker novitiates! In the previous part of this series, we looked at how to use Metasploit's web delivery exploit to create a script to connect to a UNIX, Linux, or OS X machine using Python. Many members of the Null Byte community have asked me, "Can we do the same for a Windows systems?" The answer is YES!

Hi I am a new member of null byte(although I am reading this website from the beginning) and this is going to be my first post.

In the second part of this tutorial, we are going to crack the hashes that we've captured previously. I'm going to explain how to do it with the powerful John the Ripper. It comes with Kali by default, so no need to install!

Recently, I've been learning Ruby as a second scripting language. But one topic I never covered with the many lessons online were sockets. So I did some research and came up with a very simple client/server connection that sends a string over the socket.

If you're a big fan of home improvement, then you've you've probably painted a wall or item in your day. Not only can it get expensive, it's also time consuming, and very often just plain boring. Waiting for paint to dry so that you can add another coat is, well…like waiting for paint to dry.

I still have a nexus one. This little phone 196 Mb of storage space (and most of that is taken by the system). But I have somehow managed to live off it for 2 years. This is for anyone with a small amount of memory. We will be using Link2SD. MUST HAVE CWR AND A ROOTED PHONE.

I can't say that my handwriting skills are the best, and my cursive is even worse. I mean, I still don't know how to write a capital L in cursive, but who really cares when I do all my everyday writing with a keyboard now. I've gotten pretty fast at typing on my computer, but those tiny buttons on the Samsung Galaxy S3's keyboard is a totally different thing.

Are you thinking of a ponytail or a simple bun? If you can make a ponytail, you can make a bun, and in this guide, we'll show you how to make a bow bun—for beginners. It's a very easy, but very cute and chic, way of tying up that short hair.

If you want to learn patterns drafting/making in different sizes (EXTRA SMALL, SMALL, MEDIUM, MEDIUM-LARGE, LARGE, EXTRA LARGE), now it becomes easy with these great videos that make patterns drafting easier and clearer.

Welcome back, my tenderfoot hackers! In some of my past articles, I've shown numerous ways of embedding a listener/rootkit on a remote system, including buffer overflows of the operating system, getting the victim to click on a link to our malicious website, and sending a malicious Microsoft Office and Adobe Acrobat file.

There's a lot going for the Samsung Galaxy Note 2—smart screen rotation, huge HD display, great rear camera—which makes it an awesome device for reading, watching videos, and taking pics. But all of those luxuries will end up hogging up your internal memory, which is one of the few things the Note 2 could use some help in. The device comes with 16 to 64 GB of internal storage, depending on your model, with the option of adding a microSD card for more space. Only problem is, everything automat...

There is nothing more irritating than having a nice jam session interrupted by an ad selling B vitamins, and that's exactly what Spotify does to you if you don't pay up.

Hello! My latest interest is screenwriting. I would like to share a few hints I find quite useful. I am a newbie, so the following post will not be taken from the treasury of many years of experience. Just plain facts,.. Thanks for reading! Step 1: In the Beginning

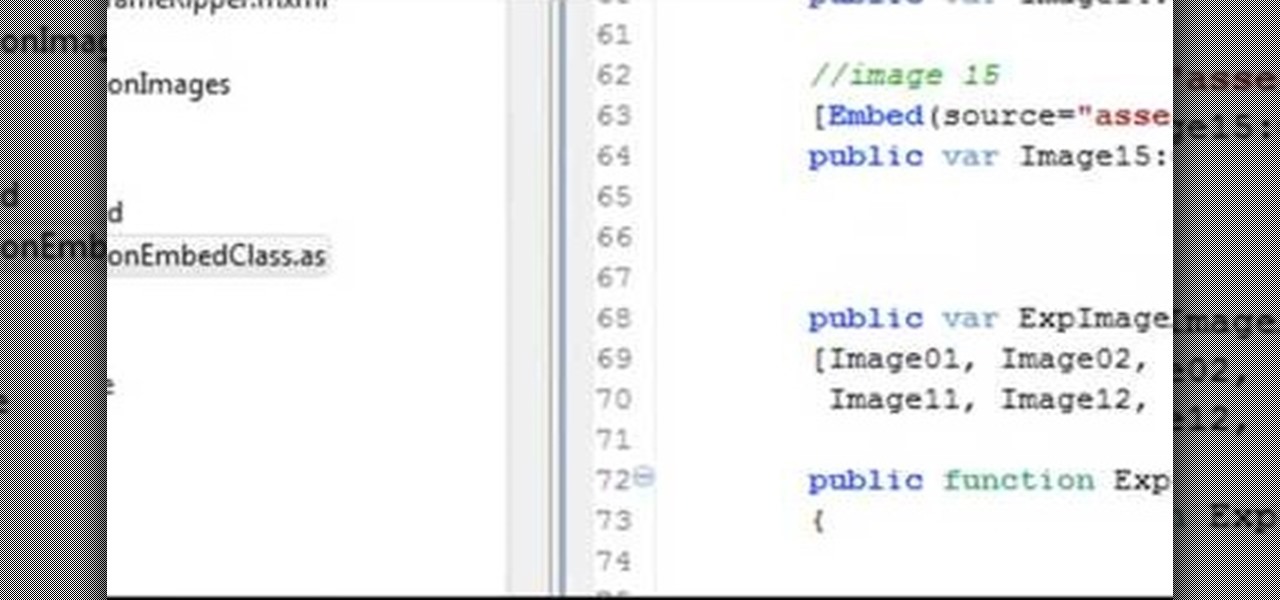
Make a Spark frame ripper

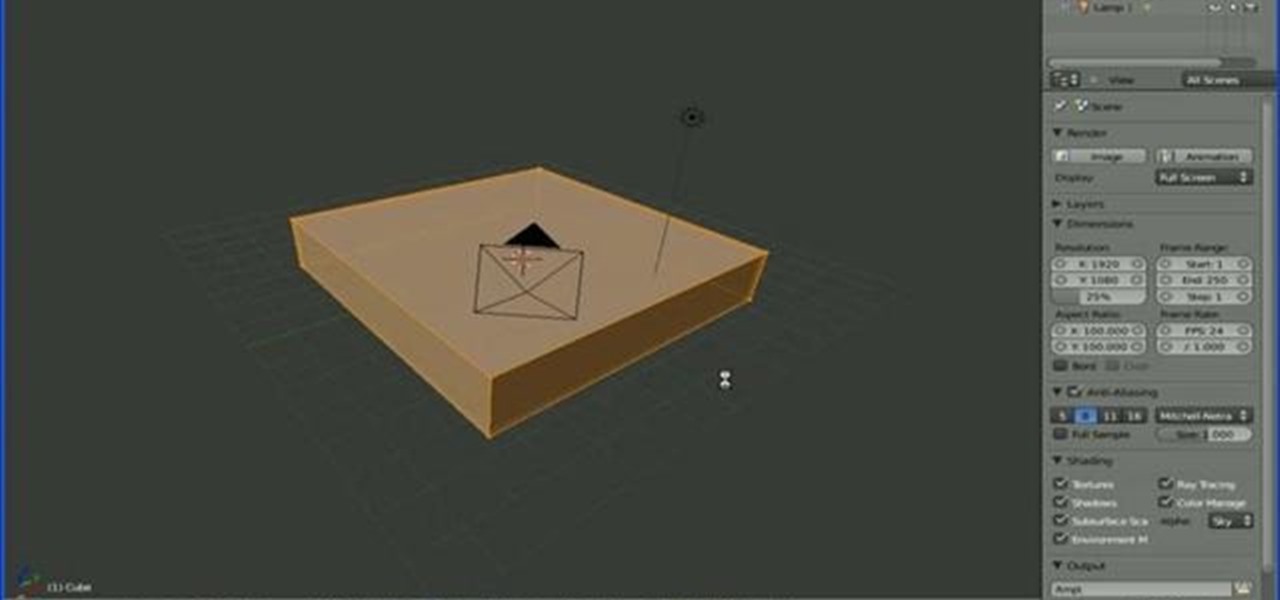
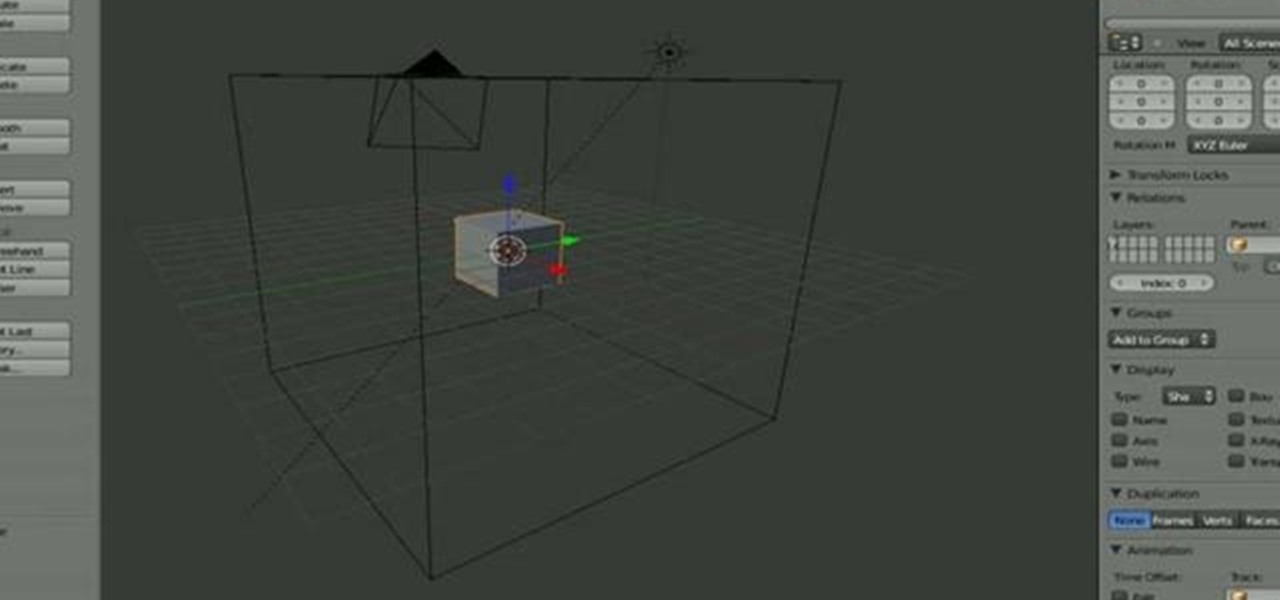
This is a quick tutorial on setting up a nodes-based texture for 3D volumes in Blender 2.5. Were you aware Blender 2.5 includes a cloud generation script? See how to use it with this video guide. Whether you're new to the Blender Foundation's popular open-source 3D computer graphics application or are a seasoned digital artist merely on the lookout for new tips and tricks, you're sure to be well served by this free video software tutorial. For more information, including step-by-step instruct...

This clip offers a quick guide on how to work with point density volumetrics within Blender 2.5. This same technique can be used to make tornados, drifting fog, dry ice and a great number of other things. Were you aware Blender 2.5 includes a cloud generation script? See how to use it with this video guide. Whether you're new to the Blender Foundation's popular open-source 3D computer graphics application or are a seasoned digital artist merely on the lookout for new tips and tricks, you're s...

Google is a great research tool, but sometimes the results can be overwhelming. In this tutorial from the experts at Revision 3 learn how to highlight text in your search results and be more efficient while you surf.

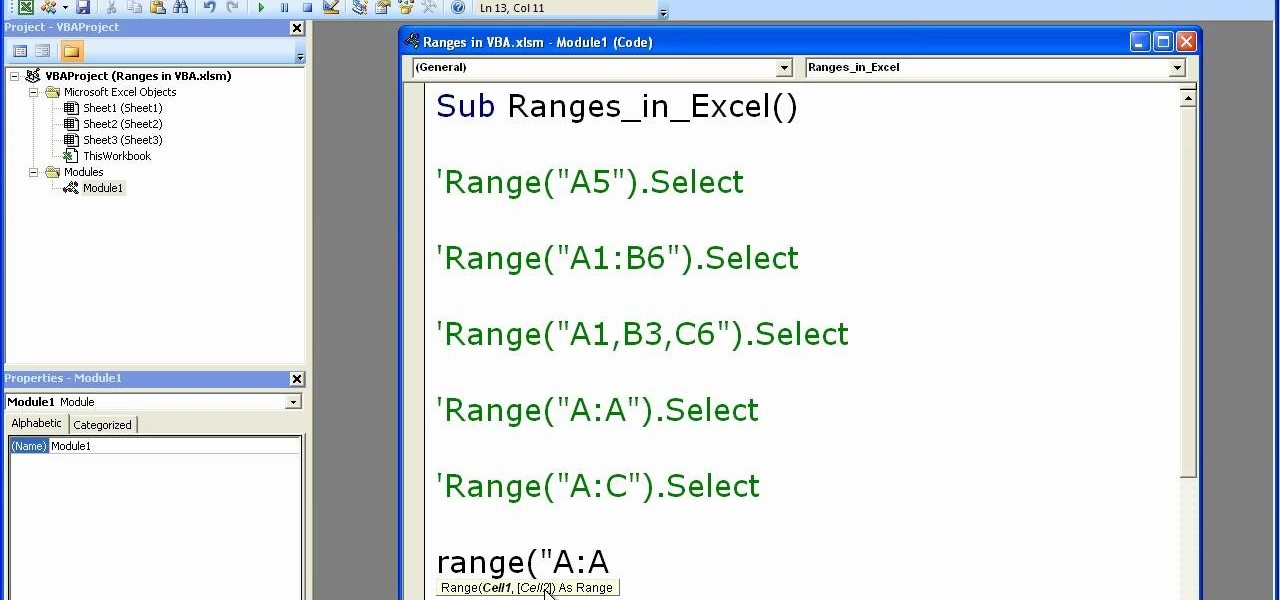
Microsoft excel is a powerful tool used to work with numbers and data by filling them down in rows and columns of a table. Excels also supports macros, which are small scripts to automate certain functions. In Microsoft Excel you can select entire rows and columns using the range property. You can also use macros to select individual rows and columns as well as multiple variations of rows, columns, and individual cells all at once. In Excel a horizontal line of data is called as row and a ver...

The video shows us how to use a proxy to bypass the Internet Filters. Most of the times in our schools and colleges most of the websites including the social networking ones will be blocked for security reasons and makes us unable to log into those websites. In such cases even the ones from the YouTube, several videos will be blocked. So in this video, we will be shown how to bypass those filters and log into those sites. Firstly go to the website Proxapp and over there you will be asked the ...

When shooting a movie, a director creates a storyboard. A comic book artist must do the same thing for drawing a comic book. Thumbnails are small blocks that represent the pages in a comic book. There is no finished work, but sketches. When following the script, the artist needs to be aware how many words are in each frame. The publisher will not be shy about putting the words on top of the drawing, or yelling at the artist. The thumbnails allow the artist to pay close attention drawing varie...

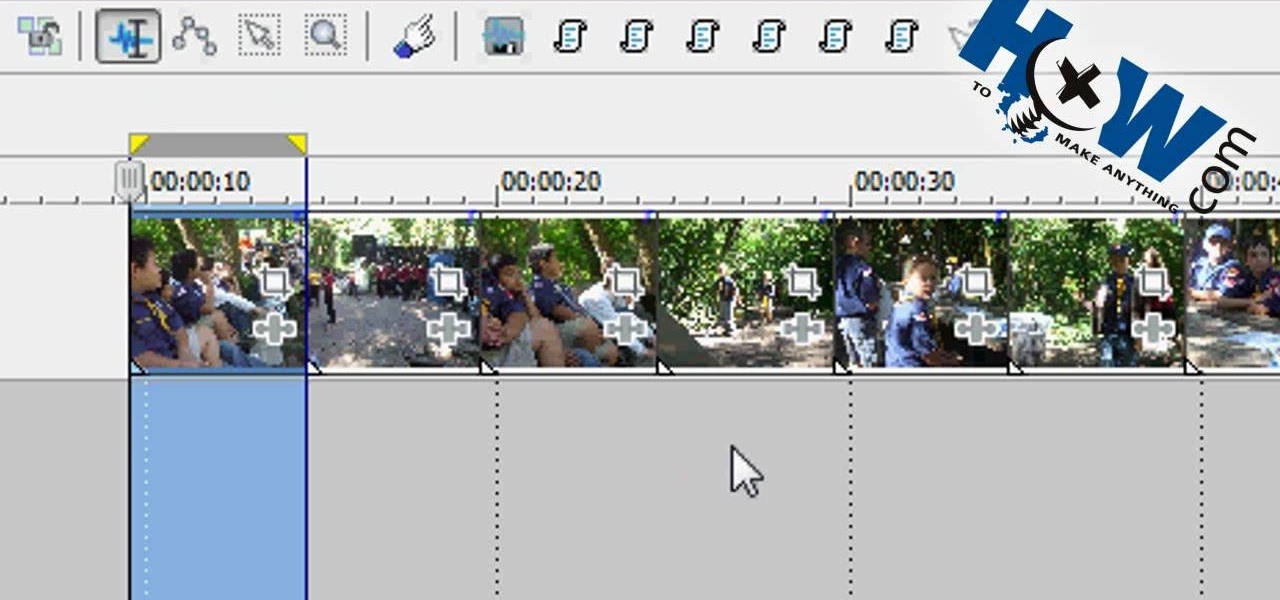
In this video tutorial, viewers learn how to make a batch render in Sony Vegas. Sony Vegas is a professional non-linear editing system. Viewers will learn how to use the batch render. At default, it is located on the toolbar. Begin by importing your clips or images into the time line. One of the batch render's features is to render regions. Begin putting regions around the clips by highlighting the clip, press R and press Enter. The add the Add Regions To Event script to automatically set reg...

Are you interested in 2D animation in Flash? First import a image in flash. Then create a new layer and choose oval tool and take a radial gradient. In the middle of the shape, we need to have zero alpha value and pick the colors from the background of the image. Create the shape over the image and take another frame at no.10 and increase alpha. Then create another keyframe and convert it to movie clip. Then create shape and motion tween. On the new layer, write a stop command in action scrip...

Gus Russel explains how storyboarding can be used to illustrate what a movie might be like. He has been given the task of drawing a frame for each page of a 130 page movie script. Story boarding gives the author a general idea of how the movie will come together, how the characters will look, etc. Russel shows the audience how to quickly draw a quality sketch, and how to shade it properly. The sketches do not function to show exactly what will happen in each scene, but rather what "might" hap...

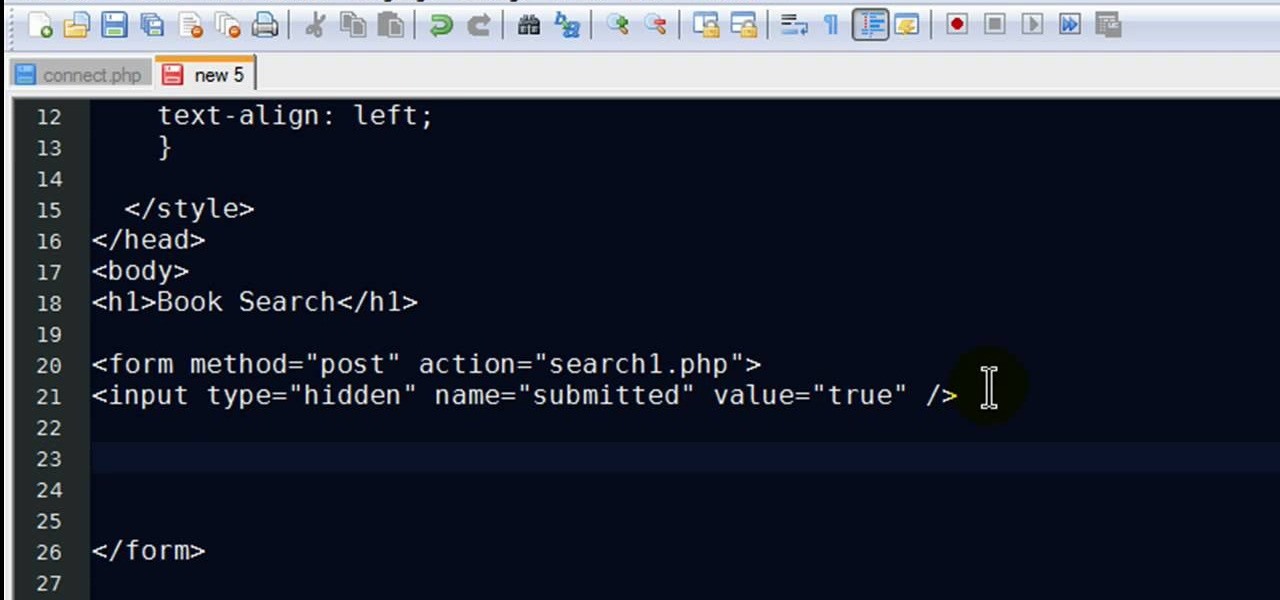
New to PHP? There's no better way to learn a scripting language than to code with it. And this two-part video guide, which demonstrates how to use a web form to retrieve data from a database with PHP, will get you started on your way.

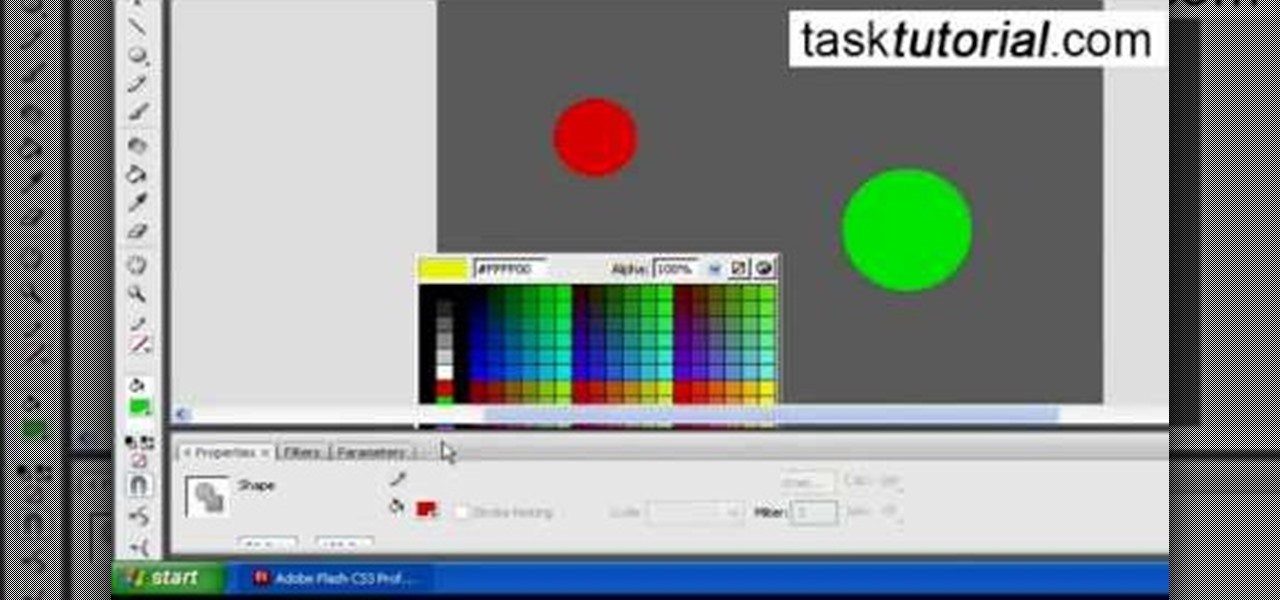
Tasktutorial.com shows us how to create drag and drop functionality into a flash program. Start off by making a few shapes in flash and then add color to each of them, a different one for each shape in order to differentiate between them. After doing this select all the shapes by dragging the cursor over them, once done distribute the shapes into layers by going into the 'modify' drop-down button at the top, then timeline and there will be the option to distribute. Now we have to turn the sha...

This video tutorial will show you how to start animating using the basics in Adobe Flash CS4. This is basically just an introduction to Adobe Flash CS4. You will learn about the Welcome Screen, Defaults, Properties, Layouts, and Tools.

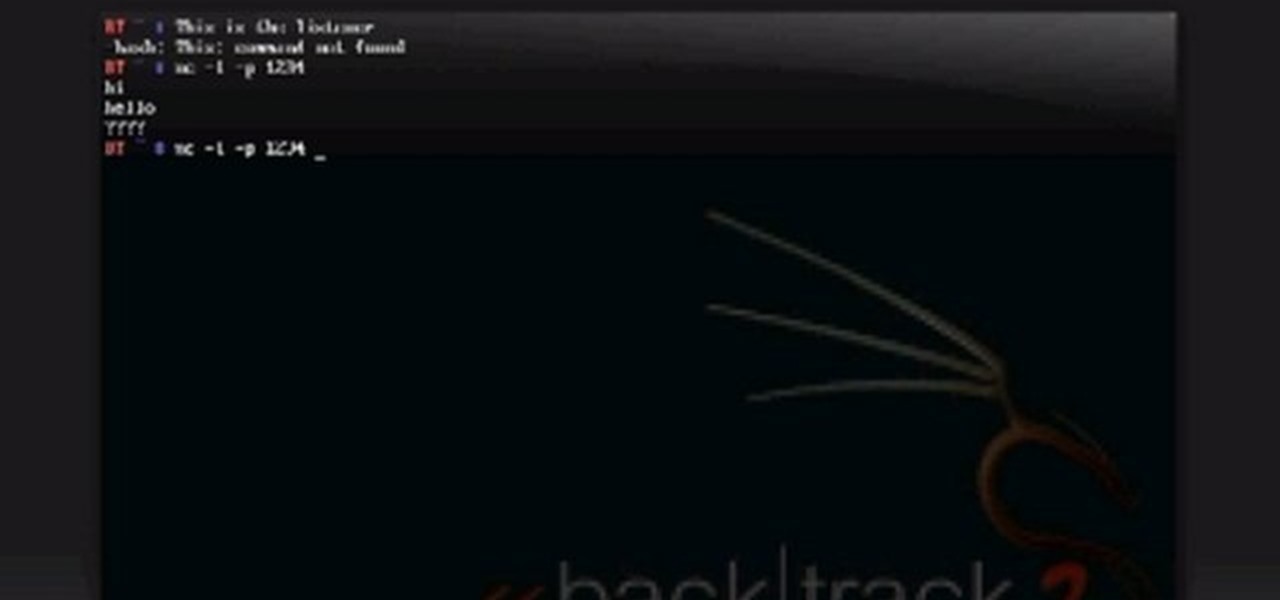
Netcat is a featured networking utility which reads and writes data across network connections, using the TCP/IP protocol.

In this tutorial, Mike Lively of Northern Kentucky University gets you started in getting the Adobe Air Content Management System up and going.

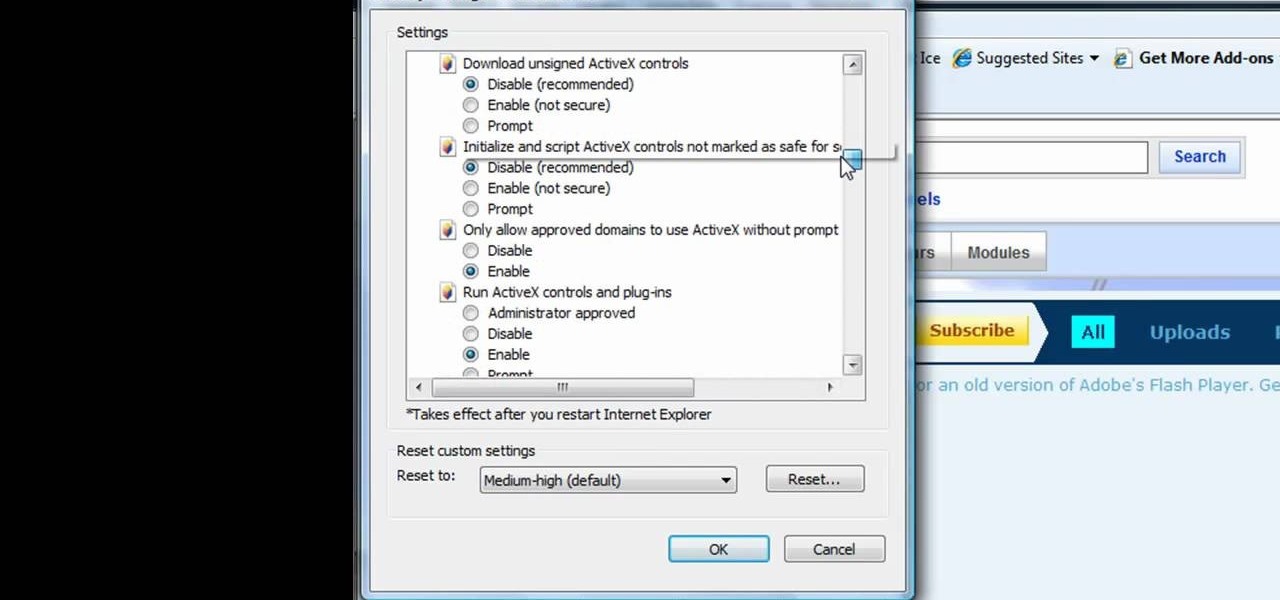
This tutorial shows us how to enable JavaScript in Internet Explorer. First, go to the top right of IE and click "tools". Then, click "internet options" and then go to the security tab. From here, select your security level that you want by clicking "custom level". Scroll down to the bottom and find the tab that says "active scripting" and make sure it's enabled. Click on "ok", then refresh the page that you are on. Now you should be able to watch videos and use anything that uses JavaScript ...