Welcome back, my greenhorn hackers! A few years back, Microsoft implicitly recognized the superiority of the Linux terminal over the GUI-based operating system by developing PowerShell. Since Windows 7, every Windows operating system has had PowerShell installed by default, and they even made PowerShell capable of running Linux commands on Windows!

Welcome back, everyone. In the previous part of this rapid-fire miniseries, we built the attacker portion of the shell. In this article, we'll just be testing it to see if everything works correctly.
I wrote a python script that allows you to easily ask what service runs on a specific port and vice-versa. Now, I am sure that such a program already exists on our lovely linux OS's, but... I didn't think of that before I started, and haven't found it yet. So if you haven't found it yet either, maybe you'll find this of some use. It's just called getport. If I have a port number, and want to know what services run on that port, I do:

Now that we have our vulnerable server, it's time to start up BeEF. Getting Started

Welcome back, my aspiring hackers! Many of you have installed Kali Linux as a virtual machine (VM) using VMware or VirtualBox, while others have installed Kali (or BackTrack) in a dual-boot system. The drawback to installing these hacking systems as a VM is that it then requires an external wireless adapter (your wireless adapter is piped through the VM as a wired device, eth0), but it makes for a great place to test your hacks while honing your skills.

Welcome back, my greenhorn hackers! I recently began a series on scripting and have received such positive feedback that I'm going to keep this series going. As I've said before, to graduate from the script kiddie to the pro hacker, you'll need to have some scripting skills. The better you are at scripting, the more advanced your hacking. Ultimately, we are leading up to developing the skills to build your own zero day exploits.

Welcome back, my hacker novitiates! Finding vulnerabilities in systems can be one of the most time-consuming tasks for a hacker. There will be times, though, when you'll find yourself in a position that you know that a particular port represents a vulnerable application or service.

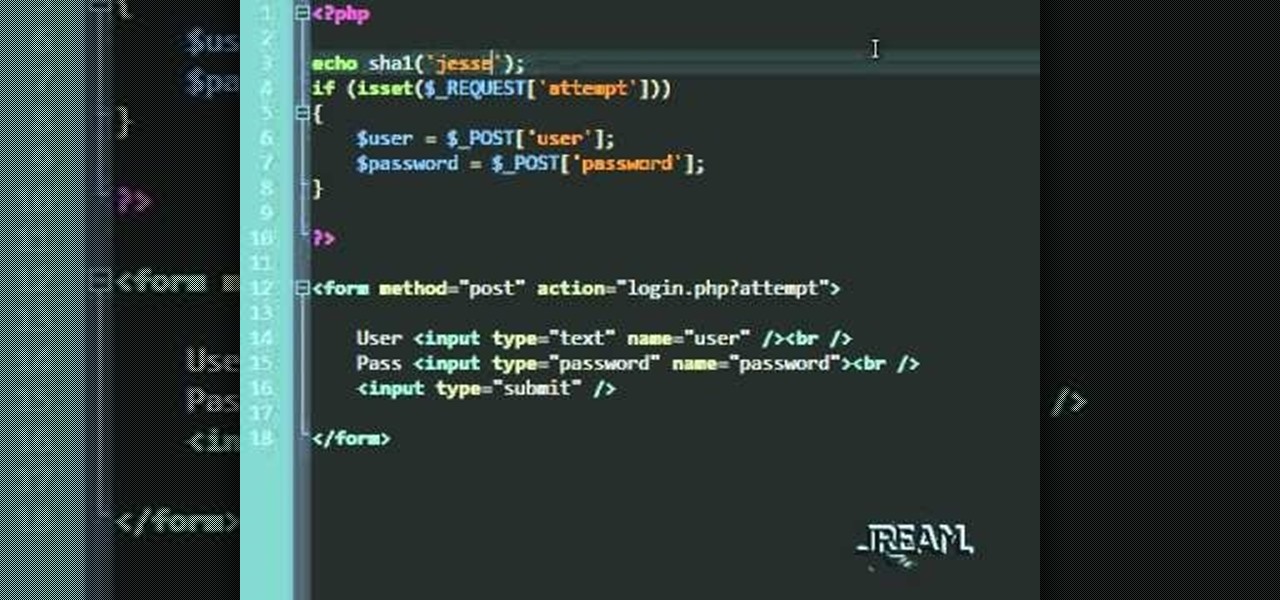
In this tutorial you'll learn about a simple PHP login script that serves to check your MySQL database against a user/password. The code in this video is a quick and dirty procedural code, but it's enough to get you going so you can try it out yourself.

Not all body shapes are created equal, just as not all jacket cuts are created equal. A trapeze jacket, which flares out at the bottom like a bell, can look phenomenol on your size 0, petite friend, but on your feminien curves it can just make you look pregnant.

Cold readings are the toughest parts of many acting auditions. Having to act a script you've never seen before convincingly is key to you getting the part. This video will give you some tips for nailing your next cold reading and wowing the casting directors.

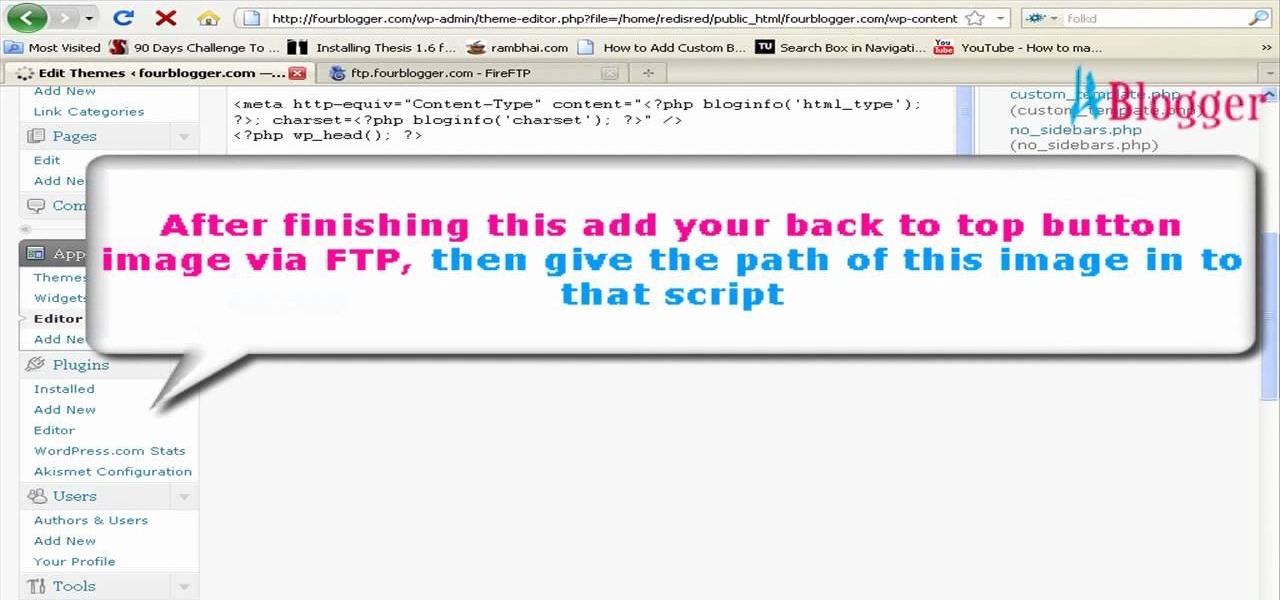
If you would like to add a "back" button to the top of your Wordpress blog, then you will need to go to Wordpress admin. When you get there, you will need to find "Thesis Options". Then, click on it. Next, find "Header Scripts" and click on it. Copy and paste the script into the box. Next, save it by clicking on the green button that reads "big ass save button".

Graffiti maestro Wizard performs one of his trademark user-requested graffiti demonstrations. In this video creates an even more compact design than usual, creating the word UZI in fairly standard graffiti-script and elaborating it with some splatter patterns and a hatted figure popping out from the corner. His speed and technique, especially working without a pre-drawing, are simply remarkable.

In this video, we learn how to dress chic like a geek! Dressing like a geek is becoming one of the hottest ways to dress! Some of the modern geek fashions are shirts with binary on them, old school video game shirts, geek shirts and many others. You can visit websites including ThinkGeek, which has a section dedicated to geek clothing. They also have shirts that relate to computer geek information and talk. Zeestuff is an apparel site that has game wear apparel for gaming geeks. There are als...

Set a table that’s tres chic by folding your napkins French style. Learn the art of napkin folding, perfect for entertaining guests!

Learn how you can read the Arabic language with this how to video. Follow this language tutorial and you will be able to read modern standard Arabic script in no time at all.

This video is a basic calligraphy instructional video that shows you how to script in the copperplate style of the uppercase letters I and J.

This video is a basic calligraphy instructional video that shows you how to script in the copperplate style of the uppercase letters V and W.

This video is a basic calligraphy instructional video that shows you how to script in the copperplate style of the uppercase letters H and K.

This video is a basic calligraphy instructional video that shows you how to script in the copperplate style of the uppercase G, L, and S.

This video is a basic calligraphy instructional video that shows you how to script in the copperplate style of the uppercase letter C.

This video is a basic calligraphy instructional video that shows you how to script in the copperplate style of the uppercase letter E.

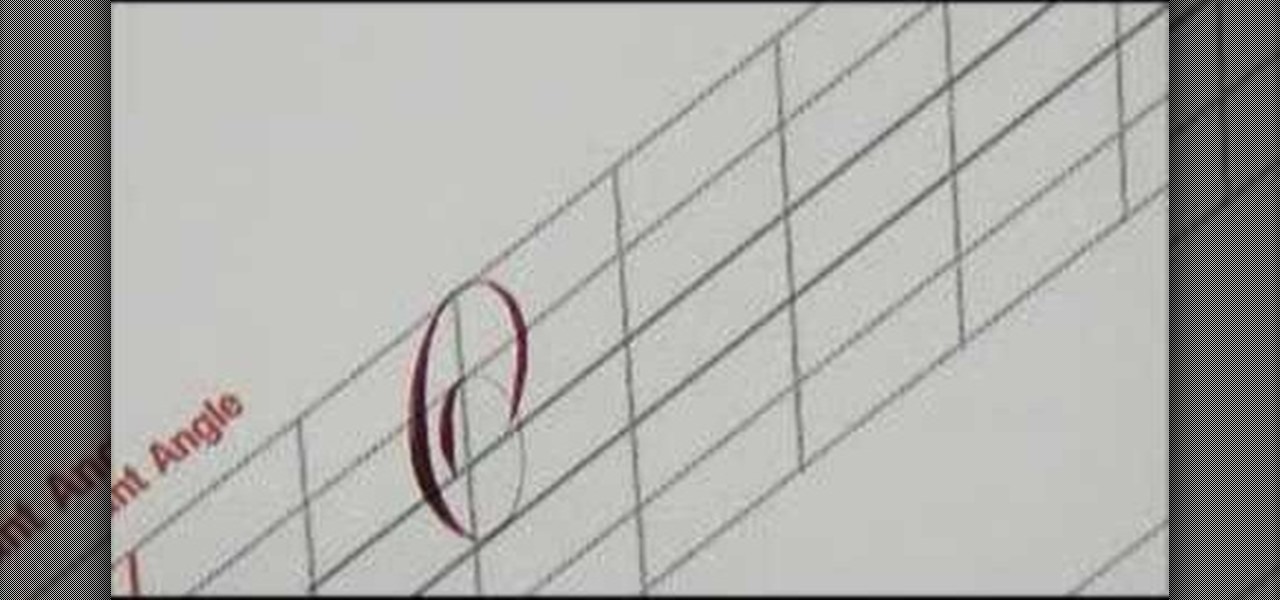
This video is a basic calligraphy instructional video that shows you how to script in the copperplate style of the uppercase O and Q.

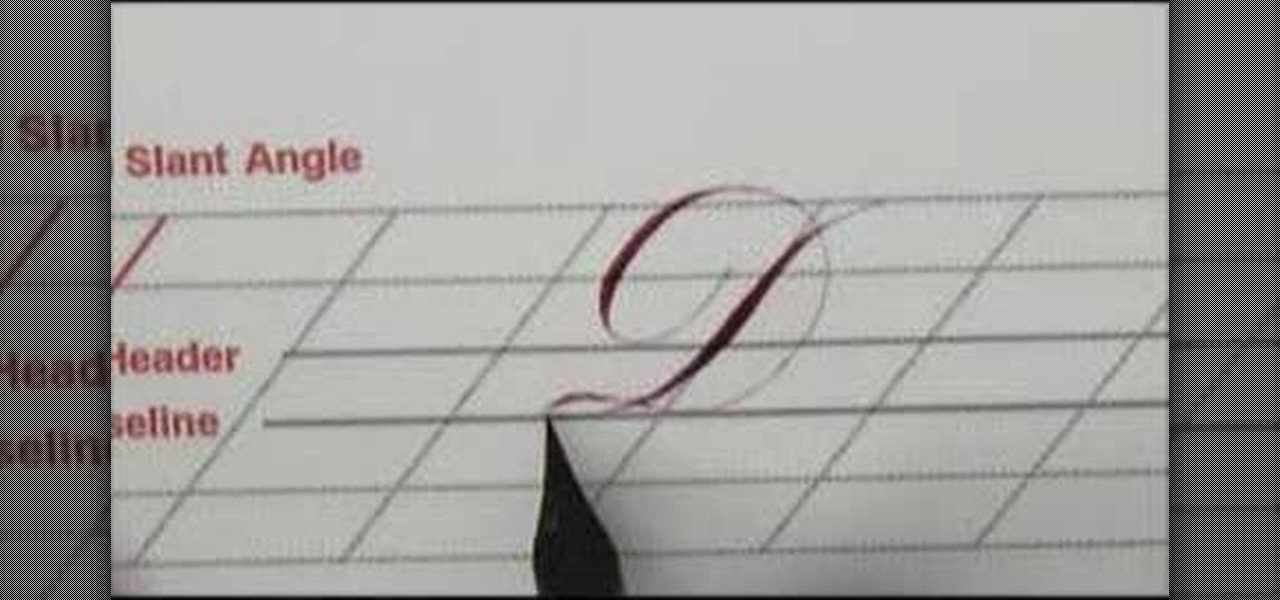
This video is a basic calligraphy instructional video that shows you how to script in the copperplate style of the uppercase letter D.

This video is a basic calligraphy instructional video that shows you how to script in the copperplate style of the uppercase F and T.

This video is a basic calligraphy instructional video that shows you how to script in the copperplate style of the lower case r, m, and n.

This video is a basic calligraphy instructional video that shows you how to script in the copperplate style of the lower case i, u, and w.

Computer pranks are some of the most insidious because computer are so expensive, necessary, and misunderstood by the general public. This video will show you how to take advantage of all of that by writing a quick script that will cause a computer's disc drive to open and close apparently of it's own free will. Great for messing with friends and coworkers at the office.

If you want to use Greasemonkey and Stylish to edit javascript you can go to Userstyles.org and you can change and edit your mainpage/homepage such as Google. On greasemonkey, you can apply extra functionality to sites and web pages. Using javascript you can post a code and animate the images or web results. The images will fly and dance around the screen using this particular javascript. Also, go to userscripts.org to get various Greasemonkey scripts to customize various sites. Such as, you ...

Whether you use shadow puppets or marionettes, put on a fanciful puppet show with these tips. Step 1: Decide on script

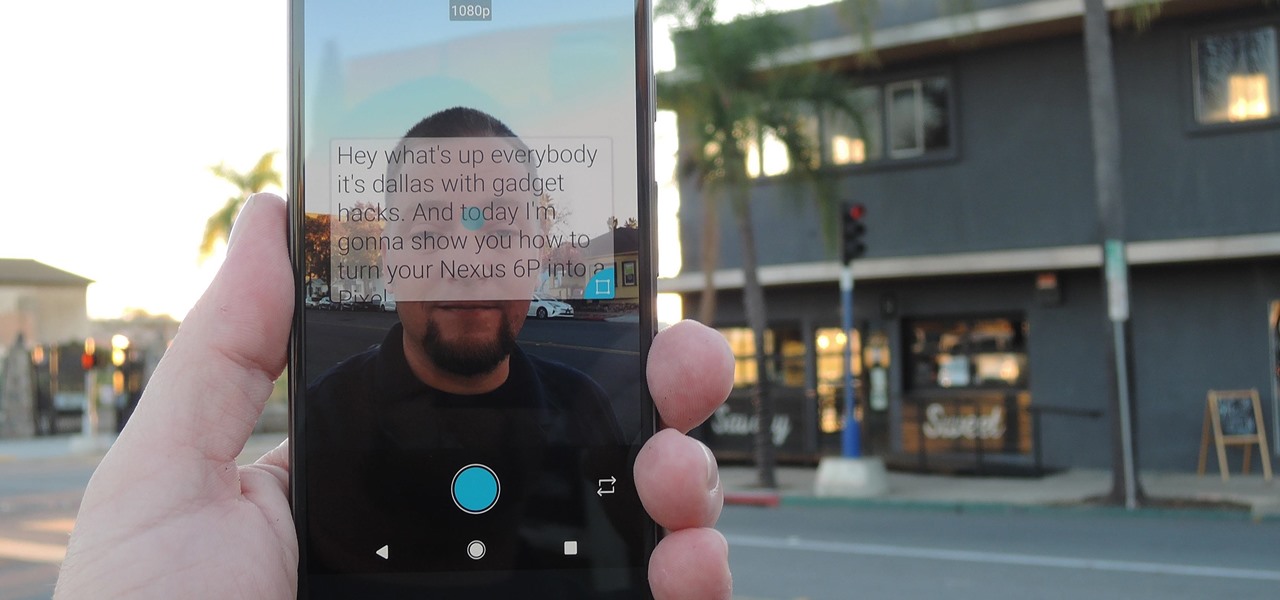
Thanks to live-streaming video and social media apps like Facebook, Instagram, and Snapchat, we're all on camera nowadays. Unfortunately, though, we don't have a script to work with when we're shooting selfie videos, so it's hard to come off as perfectly eloquent when you're just freestyling off the top of your head.

In my last how-to, we built a man-in-the-middle tool. The aforementioned script only established a man-in-the-middle. Today we'll be building a tool to utilize it. We'll be building a DNS packet sniffer. In a nutshell, this listens for DNS queries from the victim and shows them to us. This allows us to track the victims activity and perform some useful recon.

Welcome back, my fledgling hackers! Scripting skills are essential is ascending to the upper echelons of the hacker clique. Without scripting skills, you are dependent upon others to develop your tools. When others develop your tools, you will always be behind the curve in the battle against security admins.

TouchDevelop is a browser-based programming tool that allows anyone to build your own Windows 8 apps directly from any touchscreen device, including iPad, iPhone, Windows Phone, Android, PC and Macs. Once the script is created and the app proves to work, it can be placed in the Windows Store for free or purchase.

AppleScript is quite an easy scripting language to use. In this guide, I will be showing you several commands. Near the end, I will show how these can be used to create a fake virus that actually does no harm.

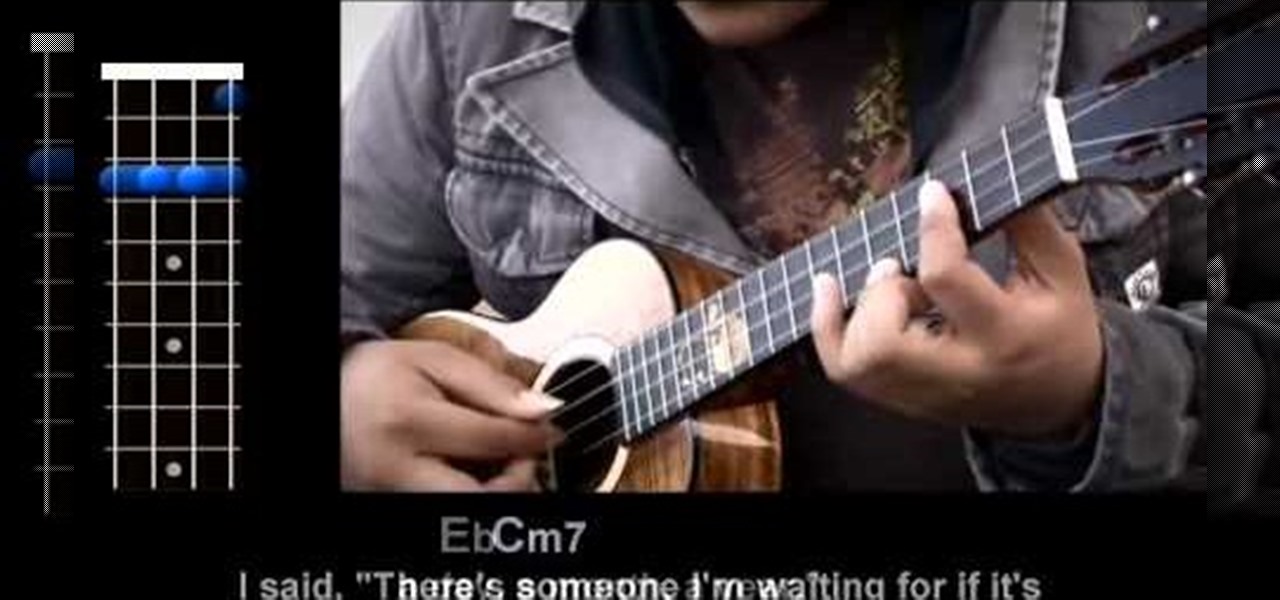
Want to play "The Man Who Can't Be Moved" by the Script on the ukulele? Learn how with this free video ukulele lesson from Ukulele Underground. Whether you play the ukulele or bass kazoo, there is no better way to improve your chops than by learning to play your favorite songs. Not only is it more fun and much easier than running drills or memorizing a chord book by wrote, it's obviously also a wonderful way to build your repertory of songs. For more information, and to get started playing "T...

This is a video that explains to a person how to write their name in Japanese. The woman shows two ways as to how to translate your name in Japanese. The first is how the name is pronounced, and the second way is to translate your name based on the meaning. Usually the name is translated based on pronunciation in the native language. The name is pronounced similarly but not exactly the same. For example Rachel is pronounced "Reicheru". She also shows a website where more information can be fo...

The Wedge ROP is a render output driver, which can be used to change variables on the fly while rendering. This can be very useful when simulating, in that you can test out different parameters to see the different results. It's a relatively new feature in Houdini 9.5.

File permissions can get tricky on Linux and can be a valuable avenue of attack during privilege escalation if things aren't configured correctly. SUID binaries can often be an easy path to root, but sifting through all of the defaults can be a massive waste of time. Luckily, there's a simple script that can sort things out for us.

An attacker can repurpose public MyBB forums to act as command-and-control servers. It only takes a few lines of code to configure a MacBook to fetch commands and send responses to any website the attacker desires.

Privilege escalation is one of the essential skills a hacker can have and often separates the newbies from the pros. With a continually changing landscape and a plethora of exploits out there, it can be a problematic aspect of any attack. Luckily, some tools can help expedite the process. Linux Exploit Suggester is just one of many to help you get root.