Most of the images in your iPhone's Photos app contain exchangeable image file format data known as Exif or EXIF data, which has several helpful uses. You can use countless apps capable of reading Exif data, many of which are paid or limited. But you already have an app on your iPhone that can give you important details about each image — and I'm not talking about the Photos app.

This holiday season, give yourself a gift that will keep on giving: a new web development skill. Whether it's to secure lucrative freelance work in the new year, bolster your résumé, or have fun with some frankly outrageous discounts on online course bundles right now (up to 99% off), there's nothing better you can do with your free time. Your future (pro coder) self will thank you.
It's Black Friday time, and in 2020, that means a lot of online deals to make up for more stores closing on Thanksgiving, as well as everyone avoiding in-person shopping because of the coronavirus. But while you may wish to grab a better 65-inch 4K TV, the new PlayStation 5, or some hacker hardware on sale, Black Friday is also the best time to invest in your programming and cybersecurity education.
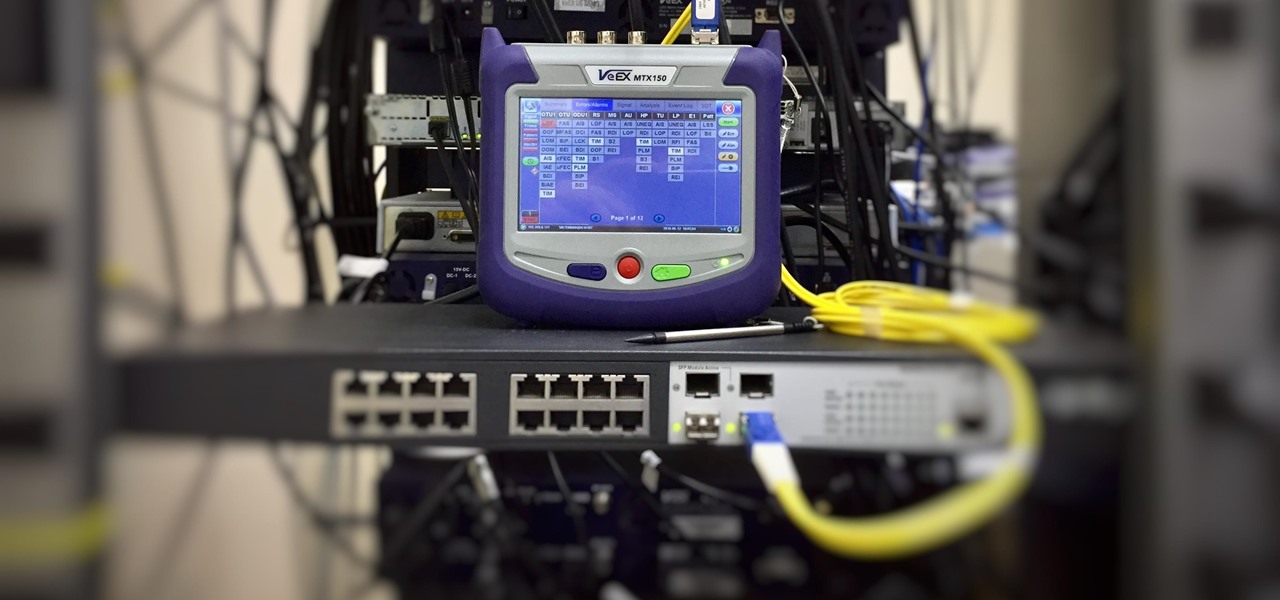
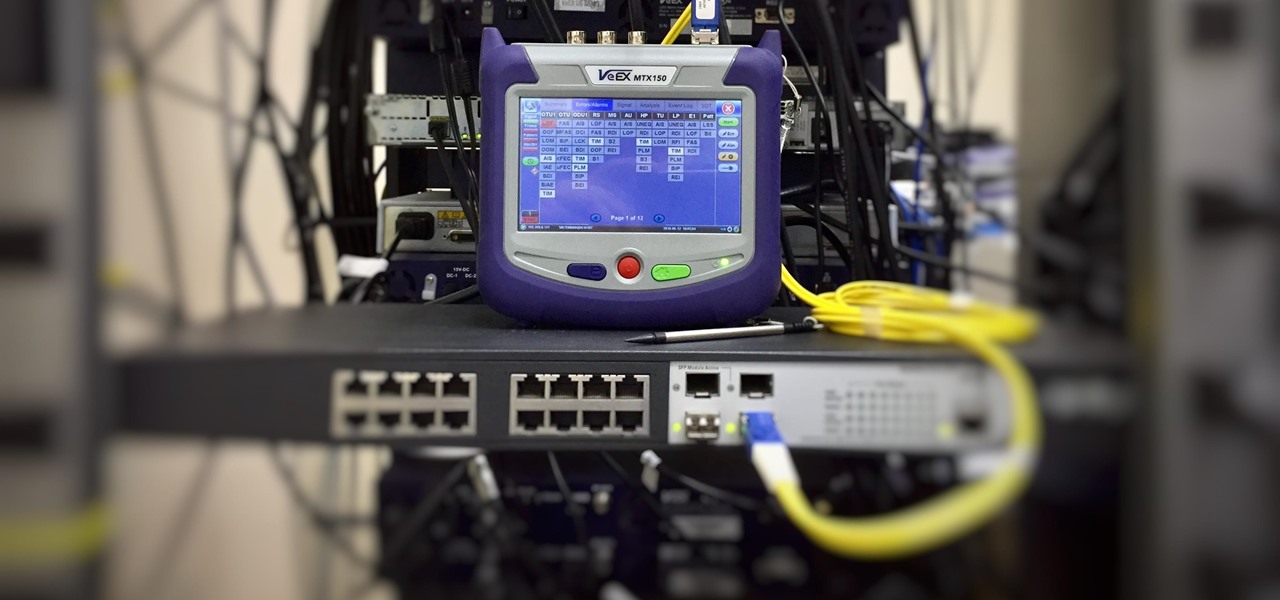
As we've seen with other tools and utilities, administrators typically use certain things to do their job more efficiently, and those things are often abused by attackers for exploitation. After all, hacking is just the process of getting a computer to do things in unexpected ways. Today, we will be covering various methods to perform banner grabbing to learn more about the target system.
Millions of people use YouTube every day, whether it's for trailers, new music, or gameplay walkthroughs. But according to Pew Research Center, over half of U.S. adults use YouTube to figure out how to do things. If you fall into that crowd, adult or not, sometimes it's good to have written instructions to follow along with the video or in lieu of it completely.

It's pretty much a given at this point that Facebook has a lot of data on us. While you might be conscious of the data you share with Facebook when you post, upload photos, or chat with friends on Messenger, you might not be thinking about all the data it receives from websites and apps you use outside the social media giant. Now, you can actually do something about it.

Traveling abroad can be a hassle. Between the flight, hotels, food, and the languages barriers, it can be a lot to manage. There's one tool you have that can help with all of this — your smartphone. Fortunately, nowadays, you don't have to change your carrier to continue using your phone.

It's easier than you might think to hack into Wi-Fi routers using just one unrooted Android phone. This method doesn't require brute-forcing the password, a Windows OS for converting PowerShell scripts into EXE format, a reliable VPS for intercepting hacked Wi-Fi passwords, or Metasploit for post-exploitation tricks.

Whether you're in high school or college, you no doubt will have your iPhone in your pocket all day long. To make your iPhone last the whole time and even help you out with your studies, these are the accessories you'll want to get your hands on.

Hackers often rely on lazy system admins and unpatched vulnerabilities to get access to a host. Keeping intruders off of our machines requires us to update daily, only run the services we need, and read the code, among other things, but we can still make mistakes. Luckily for us, we can limit the damage caused by those mistakes by running SELinux.

Still on the fence about Apple's native Notes app? The latest Notes update for iPhone, iPad, and Mac is about to change your mind. With some fantastic new features and plenty of valuable tools from previous software versions, Notes is becoming a clear winner when it comes to saving important information from your personal and professional life.

When you take a screenshot on your iPhone, it's automatically saved to your Photos app. You can ignore the screenshot thumbnail or swipe it away, but you shouldn't. If you open the screenshot editor instead, you'll gain access to your iPhone's most useful screen capture tool: full-page screenshots.

The last iOS software update was a modest one, but iOS 17.4 has a lot more for your iPhone, including changes to emoji, Podcasts, security, Safari, widgets, Apple Cash, CarPlay, and more.

Apple has a few exciting surprises for you in its latest iOS 16 and iPadOS 16 software updates. Released on Thursday, May 18, version 16.5 includes new features, bug fixes, and security patches, and there are even hints of some big things coming in future software updates for iPhone and iPad.

Apple's bringing big changes to your iPhone's lock screen in iOS 16, and one of those changes lets you pick an always-updating wallpaper for your local weather conditions. If you don't want to wait until the fall for the stable iOS 16 version and don't want to install any iOS 16 betas, you can still get an always-updating weather wallpaper for your lock screen on iOS 15.

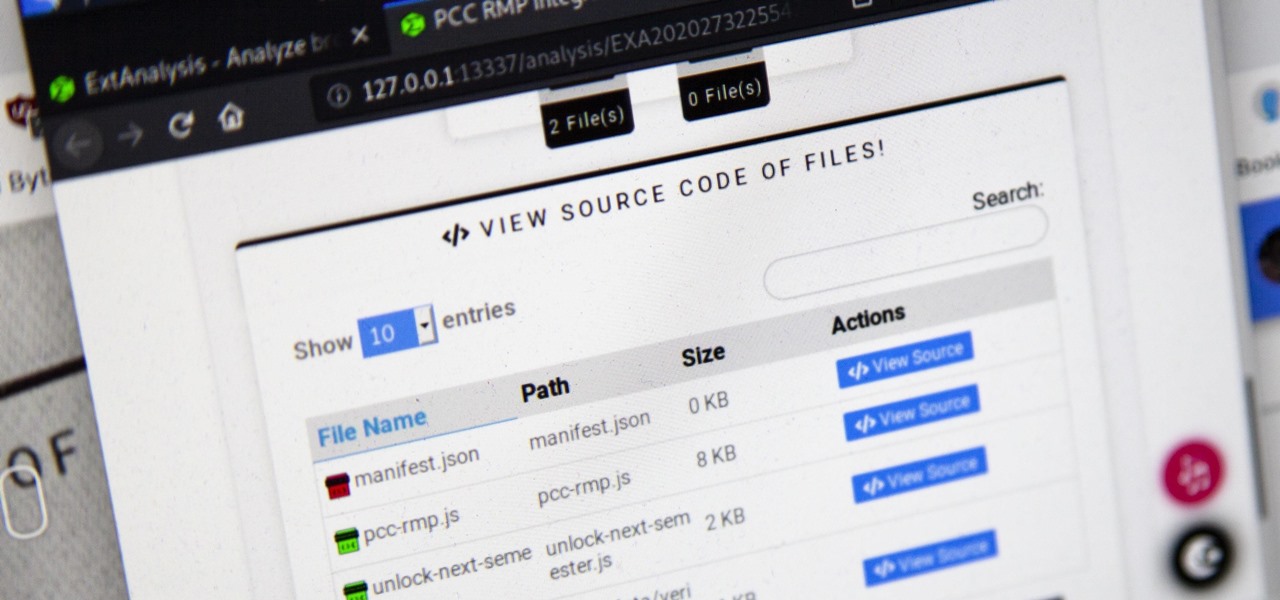
Browser extensions are extremely useful since they can expand web browsers like Google Chrome and Mozilla Firefox beyond their built-in features. However, we don't always know who's behind a browser add-on or what it's doing beyond what's advertised. That's where ExtAnalysis comes into play.

The art of fuzzing is a vital skill for any penetration tester or hacker to possess. The faster you fuzz, and the more efficiently you are at doing it, the closer you come to achieving your goal, whether that means finding a valid bug or discovering an initial attack vector. A tool called ffuf comes in handy to help speed things along and fuzz for parameters, directors, and more.

The internet has undoubtedly changed the way we work and communicate. With technological advances, more and more people can collaborate on the web from anywhere in the world. But this remote-friendly environment inherently brings security risks, and hackers are always finding ways to exploit systems for other uses.

You've protected your Ubuntu system from physical attacks, annoyed network hackers, and sandboxed potentially malicious applications. Great! Now, the next logical steps to locking down your OS include thoroughly auditing Ubuntu for weak points, using antivirus software that respects your privacy, and monitoring system logs like a boss.

A mention of the deep web can bring to mind images of drugs, hackers, and other criminal activity. Despite the presence of these elements, the Tor network is a valuable tool for preserving privacy and anonymity. And browsing the deep web and any hidden services can be as simple as downloading the Tor Browser.

Watch this video to learn how to create an image gallery in html. Create an image gallery in HTML.

Watch the video to learn how to let the user choose the background of the site. This is a cool feature that makes your site more user friendly. Let the user choose the background in HTML.

Learn how to change the HTML ExpressShow template for single output, non-SCORM productions. The HTML template appears as the background around the video. ExpressShow is a video branding option within Camtasia Studio 5. Customize the HTML template for ExpressShow production.

This tool in Dreamweaver allows users to redefine an existing component of HTML. For more Adobe software tutorials from Layers Magazine, search Layers Magazine on WonderHowTo. WonderHowTo indexes all Layers Magazine tutorials for Illustrator, InDesign, Photoshop, Acrobat, After Effects, Premiere Pro, Dreamweaver and Flash.

Adobe Fireworks CS4 software is used to rapidly prototype websites and application interfaces and to create and optimize images for the web more quickly and accurately. It is ideal for web designers, web developers, and visual designers. Simply having the software isn't enough, however; you'll need to know how to use it. In this CS4 video tutorial, you'll learn how to create HTML clickthroughs in Adobe Fireworks. Create HTML clickthroughs in Fireworks CS4.

It is not that they do crazy things they do not know how to deal with stress. It is more likely for a teen to make a “bad” decision when they are under stress. Teens' brains are not yet developed; your brain is fully develop around the age of 25. That is why an adult will response better under stress than a teen.

It takes practice but helps anyone create a personal web page from scratch. Code paragraphs, text, tables and lists on an HTML website with a professional designer in this free web design video. Add text on a website with HTML - Part 1 of 65.

This tutorial shows you how to edit a Dynamic Flash Template just by moving files around in folders and doing a little HTML writing. Edit a dynamic flash template.

http://www.nationalgeographic.com/adventure/0505/photo_index.html

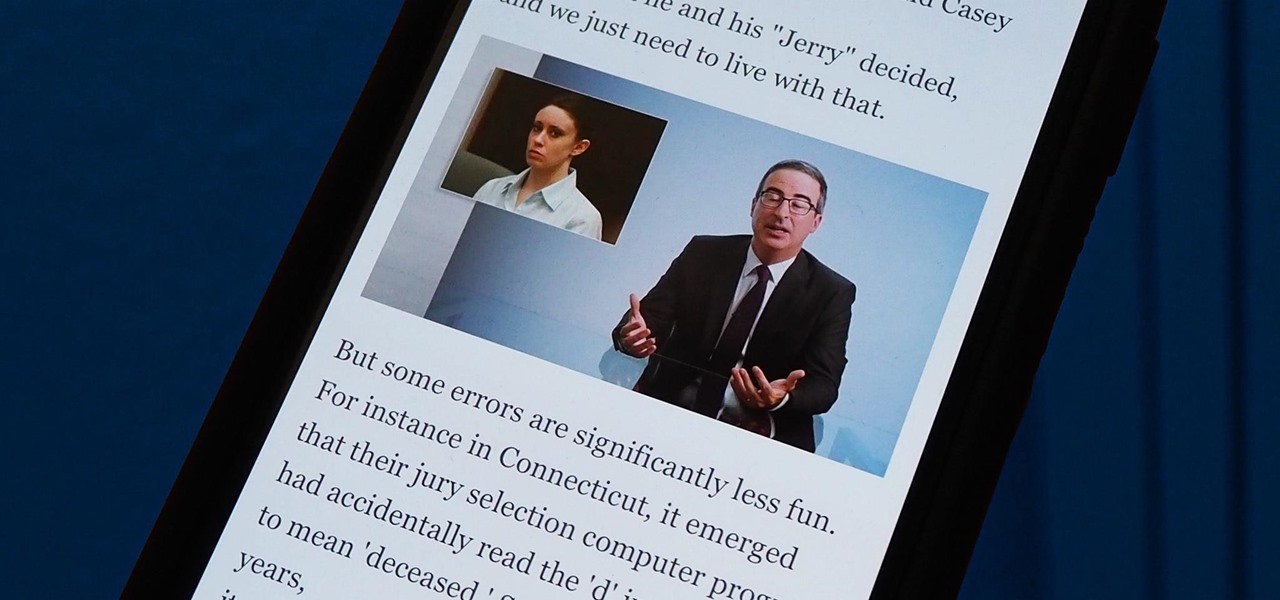
Welcome to the Goodnight Byte for HackThisSite, Basic Mission 4. In Friday's session, we tackled some coding in Gobby. Nothing special, just a few modifications to the NullBot script we made a few session ago, and some education on regular expressions. Apart from coding, we did our scheduled HackThisSite mission. We had to take on some JavaScript, which was a new thing for Null Byte. This mission taught us about client-side HTML manipulation through JavaScript injections. This just means that...

I already had a mishap shooting my Canon 5d MII tethered....I broke my circuit board because of the stress that a USB cable causes the camera. I wish Canon went with their 1ds route and made a positive locking device, but alas they have not. So the best alternative I could find was a left-angle cable that will reduce the stress and make it quite easy to gaffers tape to my vertical grip for some added safety. Check them all out here, I just purchased the "15' Left Angle" will let you know how ...
What Is a Rational Number? A rational number is a number that can be written as a ratio and a/b.

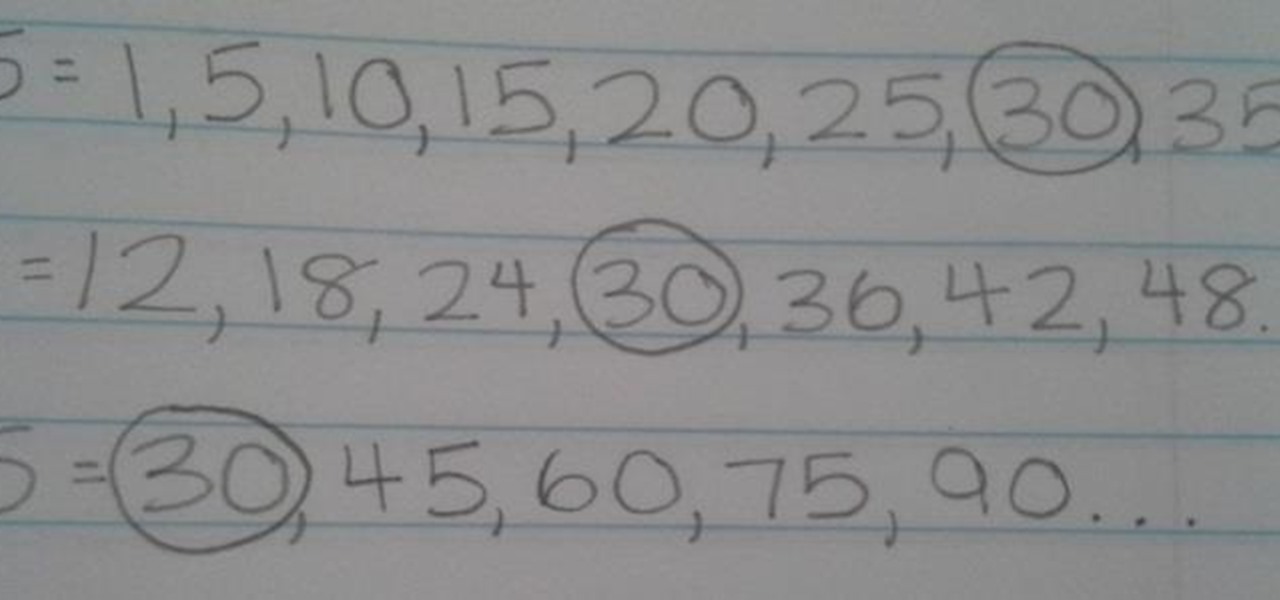
What Is LCM? LCM is an acronym for "Least Common Multiple." LCM is the smallest number that is a multiple of two or more numbers.

In this Adobe Bridge CS4 tutorial you will learn how to create a web photo gallery. Learn how to use built-in HTML and Flash templates within Bridge CS4 to customize, preview and upload a photo gallery directly to an FTP server. Create a web photo gallery in Bridge CS4.

Last Friday's mission was to accomplish solving HackThisSite, realistic 3. The third mission in a series of realistic simulation missions was designed to be exactly like situations you may encounter in the real world, requesting we help a friend restore a defaced website about posting peaceful poetry.
Hello guys, This is a brief introduction about what you are going to learn in this series. What Are You Going to Learn?

How to tie an Alpine Butterfly Loop. Instructions on how to tie an Alpine Butterfly Loop by http://videofishingknots.com - More info at http://videofishingknots.com/poachers-noose.html Tie a poacher's noose knot for fishing.

To avoid waiting a long time to stream an mp3 file, just use an html editor to right click the link and download the file. Ron Hutton demonstrates. Download an mp3 off of a streaming link.

Cross-Site Request Forgery (CSRF, pronounce "sea-surf") is a common web exploit. However, for unknown reasons it's not used very often. It plays on a given website's trust in a web browser by executing another website's form action, for example, sending money to another person. It's usually placed in abnormal places like HTML image tags.
http://web.mac.com/scifione/orig/BOOKS/HEX/hex-def.htm