In the last article, we left off with the Tor network and its hidden services. As I mentioned, Tor is not the only option in the game, and I want to offer a general introduction to I2P.

Bitcoin is a new currency built off "Satoshi Nakamoto's" (alias) 2008 Bitcoin white-paper. Bitcoin provides its users with a way to make peer-to-peer (P2P) transactions without having to use a bank as a mediator. There is no middle man, no corporation backing it, and no one has access to your money, except you. It's decentralized from government, run by the people, for the people.

One of the most important marketing tools we should always be developing to help reinforce our brand is our references. Just like many companies use their client list and client references to build credibility and confidence for their products and services, we should also leverage our references to build credibility and confidence in our capabilities and brand. Sometimes reference checks are just a formality, but in most cases potential employers (i.e., potential clients) use reference checks...

Whether it's the new iPad Killer or not, one thing's for sure—the Motorola XOOM is hackable. Just hours after its release last week, Verizon's new Android-based tablet (running Honeycomb) was rooted by hacker Koushik Dutta, which seems easy enough.

From the people who brought you the Dummies instructional book series, brings you the same non-intimidating guides in video form. This is Mac for Dummies. Just watch this video tutorial to learn how to send email on your Mac computer, For Dummies.

When your computer first connects to a nework, it sends out a request on the network to lease an IP from the router. The router then leases your computer an unused IP address, which is used as a unique routing address for sending traffic that is meant for you, to you. As everything tends to, this method has its flaws.

OpenVPN is the open-source VPN (Virtual Private Network) client, used over the PPTP (Point to Point Tunneling Protocol). It allows you to connect to a remote network over a secure, encrypted connection and mask your IP addresses over all ports. Since there is only one "hop," the network speeds are barely effected and are far more secure.

SSH is what is referred to as the Secure SHell protocol. SSH allows you to do a plethora of great things over a network, all while being heavily encrypted. You can make a remote accessible shell on your home computer that gives you access to all your files at home, and you can even tunnel all of your traffic to keep you anonymous and protected on public Wi-Fi. It has many great uses and is a must have tool for your arsenal. It was designed to replace the insecure Telnet protocol, which sends ...

This laminate flooring is very impressive as far as the surface is concerned. My client actually used a sharp screw and tried to scratch it, and we could not see anything. It is rated as a AC3 which is mid grade as the grading system is from AC1 to AC 5, 5 being the best.

Creating fake wounds on the human body is one of the most fun parts of being an amateur or professional makeup artist, and whether your clients are you friends on Halloween or Brad Pitt. This video will teach you very quickly how to make a fake wound on your hand out of latex and other basic makeup costume makeup materials. Make others think that you need to be hospitalized! Make a fake wound for Halloween or film.

This video demonstrates how to send email on your Mac. From the people who brought you the Dummies instructional book series, brings you the same non-intimidating guides in video form. Watch this video tutorial to learn how to send email on your Mac, For Dummies.

This article is all about creating content and using it to build links to your website. Content, meaning articles, videos, and even podcasts is now really the new advertising. That’s because people go to the internet to look for information, not look at advertising. So you need to create compelling content about your business, your industry in general and any topics connected to your entire field that people will want to read, listen to or watch.

This article is all about creating content. This is a very important concept to grasp because the content that you create for a website is going to be the basis for how you will advertise and promote that website. Content, meaning articles, videos, and even podcasts is now really the new advertising. Instead of traditional types of advertising and instead of the traditional separation between editorial content and advertising, that has gone the way of the dinosaur.

My palace for a city that has no fewer than 7 100k block structures (will have 15-20 when the central blvds are finished - map link : http://www.minecraftworldmap.com/worlds/_IgOQ ). Today's tip - at the start of the video - how did I put in the lighting for players to navigate the palace hedgemaze (at the start and end of the video).

Welcome to the 10th Community Byte session for coding in Python and completing the challenges presented to us by HackThisSite. These sessions are created to bring our community together, to learn from each other, and grow together. Everyone is welcome, from novice programmers to aspiring hackers.

Welcome to the eighth Community Byte for coding in Python and completing the challenges presented to us by HackThisSite. These sessions are created to bring our community together, to learn from each other, and grow together. Everyone is welcome, from novice programmers to aspiring hackers.

Welcome to the seventh Community Byte for coding in Python and completing the challenges presented to us by HackThisSite. These sessions are created to bring our community together, to learn from each other, and grow together. Everyone is welcome, from novice programmers to aspiring hackers.

Update 2: 1.9 Version3 is currently out. Click here to download and install 1.9 Version 3. Update: 1.8 is now officially out! It'll prompt you to update the next time you launch.

I have had a lot of people ask me, "How does my neighbor keep getting into my wireless?!". Chances are, these people are all using WEP, a deprecated wireless encryption protocol. Either that, or you are using one weak WPA passphrase.

Sitting in the dentist’s waiting room, I found I couldn’t browse the internet on my smartphone anymore. My eyes were tired from reading and there were no headphones to listen to music. There are no magazines at this dentist’s office, just an old TV playing Russian music videos ad nauseam. Mostly female Russian singers, and curiously enough they all shared similar traits: they can’t dance. They look gorgeous, but the best they could do is small movements and two slow moves at best- a huge diff...

Nobody could predict the success of Microsoft's Kinect, not even Microsoft themselves. So, it was quite a surprise when it ended up earning a Guinness World Record for fastest-selling consumer electronics device, and an even bigger surprise to see people buying one that didn't even own an Xbox 360.

You have two choices for keeping your living room looking fresh: A. constantly update the decor by tripping out on acid—NOT recommended—or B. paint your living room white and get two video projectors. Created by Mr. Beam:

Surfing Magazine staff photographer Nathan Lawrence and Balaram Stack, Oliver Kurtz and Michael Dunphy descend upon Bocas Del Toro and Red Frog Bungalows for a surf trip of a lifetime. Nathan Lawrence is one of the best surf photographers in the world and he summed up the conditions over the week as ,"the best beach breaks I have ever seen in my life". This is saying a lot for someone who is payed to travel the world and snap photos of the best professional surfers in the world. look for the ...

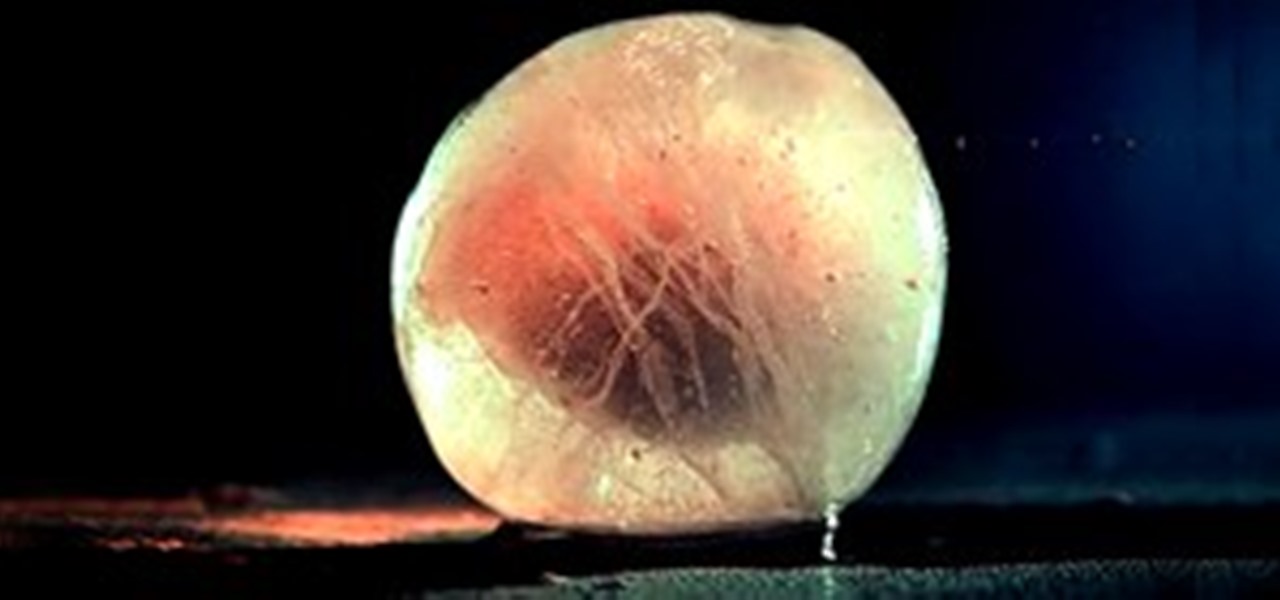
"Freezing Moments" is a great piece of video of different liquids dramatically reaching freezing point, directed by Andrey Muratov. It's cryptically described as "Components of the space. Between existence and 'No!'. Alive - Absorbs." Hmm. Client is also cryptic: GTLK (Gosudarstvennaya Transportnaya Lizingovaya Kompaniya). Appears to be Russian, which would translate to the "State Transport Leasing Company".

THIS IS IN THE PALTALK PC TECH ROOM..

Though only just released, the official Skype client for Android has already been unlocked. Thanks to xeudoxus of DroidForums.net, American Android users may now do what their European counterparts have been able to do all along: make free Skype-to-Skype voice calls over 3G.

In this tutorial, we learn how to track work in progress while using QuickBooks. Start by enter in an estimate and then click on the button to create an invoice. The progress invoice will now appear to track what you want to do with the estimate. You can then choose what you want to fill out, and show either quantity and rate or you can show percentages. You can now change the numbers and figures onto the page, and then click "ok". When finished, you will be brought back to your original page...

When i went to class today, a good friend asked me a question. He wanted to know what the best hacking software was to basically do everything. What i told him was this: Well there isn't an "Ultimate" tool boot there are a number of tools which deserve a "Medal." So what i'm trying to say here... What are some of the best hacking tools available right now? For starters i created a list with some of the tools.

Reverse shells are useful for issuing commands to a remote client when the client is behind something such as a NAT. You might say, "But can't a normal shell or simple SSH tunnel do the same thing?". No, it can't. All over the internet I see a lot of confusion regarding the difference between a normal shell and a reverse shell. Let's clear this up before we get started.

Often times when staying at a hotel or anywhere for that matter, you'll whip out your laptop and check the local area for Wi-Fi. I know you've all been in my shoes when you find an unsecured network that appears to be public Wi-Fi belonging to the hotel or airport, and you connect to it. You connect fast and perfectly, only to find that when you open your browser, it says you don't have an account, and are filtered from accessing the web. This is because the owners of the network want to keep...

Indie developers and their games have enjoyed massive success distributing through Steam, notably Zeboyd Games and Carpe Fulgar. While that bodes well for the future of indies on the platform, Steam has to devote a lot of front-page real estate to AAA games and thus can't promote small indies as well as a dedicated indie game distribution service could. IndieCity out of the UK seems like it could be that, but today a consortium of three German game companies launched their attempt at beating ...

Through Thursday, January 20th, Borders is offering the Kobo Wireless eReader for $99 with coupon—that's $40 off its typical retail price of $139! Though the Kobo comes preloaded with 100 out-of-copyright classics, new users will nevertheless be interested in filling their new eReaders with their own books.

Some people are what is labeled a power user. I am one of these people. No matter how fast I get my system, or how quick of programs I have, it is never good enough. There is always at least one program that I could swap out for a more advanced, text-based counterpart that increases performance just a bit. Luckily, you don't have to use text-based programs without graphical user interfaces to get blazing fast speeds on Linux. There are tons of open source alternatives to the mainstream progra...

Business owners and marketeers are diverting from traditional marketing techniques, including billboards, radio and TV advertising, brochures, and any other outdoor promotions, to cheaper but effective Internet marketing strategies. Under the new arrangement, business owners reach out to the final consumers through advertising on the World Wide Web.

Installing the Software Download the PC/Mac client from Dropbox for your computer. When installing the software you will also be prompted to create an account. Please do so at this point. This account gives you free access to 2 gigabytes (gb) of cloud storage that can be accessed from any PC/Mac or Dropbox Enabled Device.

As a web developer, I often read articles about hackers (from the lowly to the knowledgeable) infiltrating websites via the dreaded 'SQL Injection' method and completely taking control, changing, gaining access, or destroying the owner's data. As a fellow web developer, I'm sure you want to know how to protect against it. Well, here it is! In this article, you will find out what SQL Injection is, what you can do to protect against it, and additional recommendations that are easy to do and onl...

For a professional photographer in the market for good business management software, Canon offers the Studio solutions package. This tutorial series outlines all the various functions and features of Studio Solutions, such as order processing, client files and managing your various photos for each product. Manage your professional photography business using Canon Studio Solutions - Part 1 of 8.

Follow these few step by step instructions to learn how to activate the junk mail filter in Entourage for Mac.

Welcome to Minecraft World! Check out our tutorials, post to the community corkboard, and come play on our free server!

This article is all about creating content. This is a very important concept to grasp because the content that you will learn how to create is going to be the basis for how you will advertise and promote your website. Content, meaning articles, videos, and even podcasts. Content is now really the new advertising. Instead of traditional types of advertising and instead of the traditional separation between editorial content and advertising, that has gone the way of the dinosaur.