Chromecasts can make for some fun nights. Whether you're setting up a collaborative YouTube watch list, letting everyone add to a giant party playlist, or playing games like Cardcast and Big Web Quiz, Google's streaming media stick is a hit by all accounts.

For those of you who have been taking full advantage of the jailbreak for iOS 8 that's available, you can understand and appreciate what this really offers iPhone users—sovereignty.
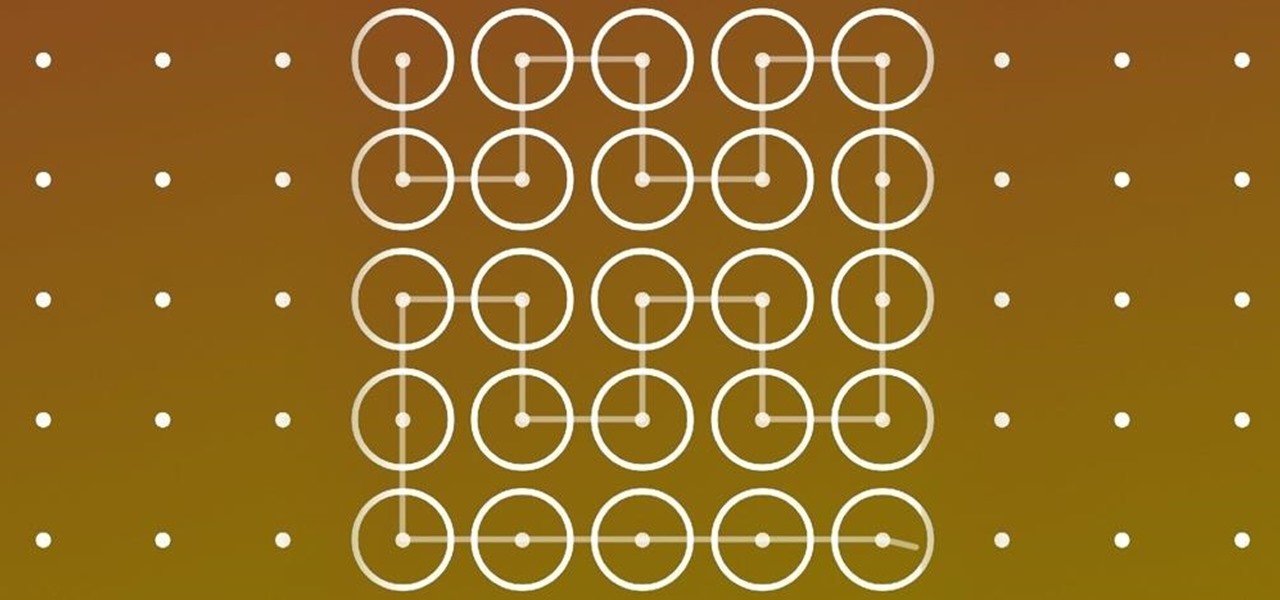
I think it's safe to assume that most of us appreciate a little privacy and security when it comes to our mobile devices, which is exactly why we have lock screens that require unique passwords, patterns, or PINs. Although someone can discretely peer over your shoulder to see what your password is, it's much more difficult for them to duplicate your face to unlock the device.

This year's biggest film certainly didn't come as a surprise: with another incredible comic book creation, Marvel's Guardians of the Galaxy wowed audiences more than any other movie. With its unique team of heroes, Guardians provided a set of ready-made Halloween costumes.
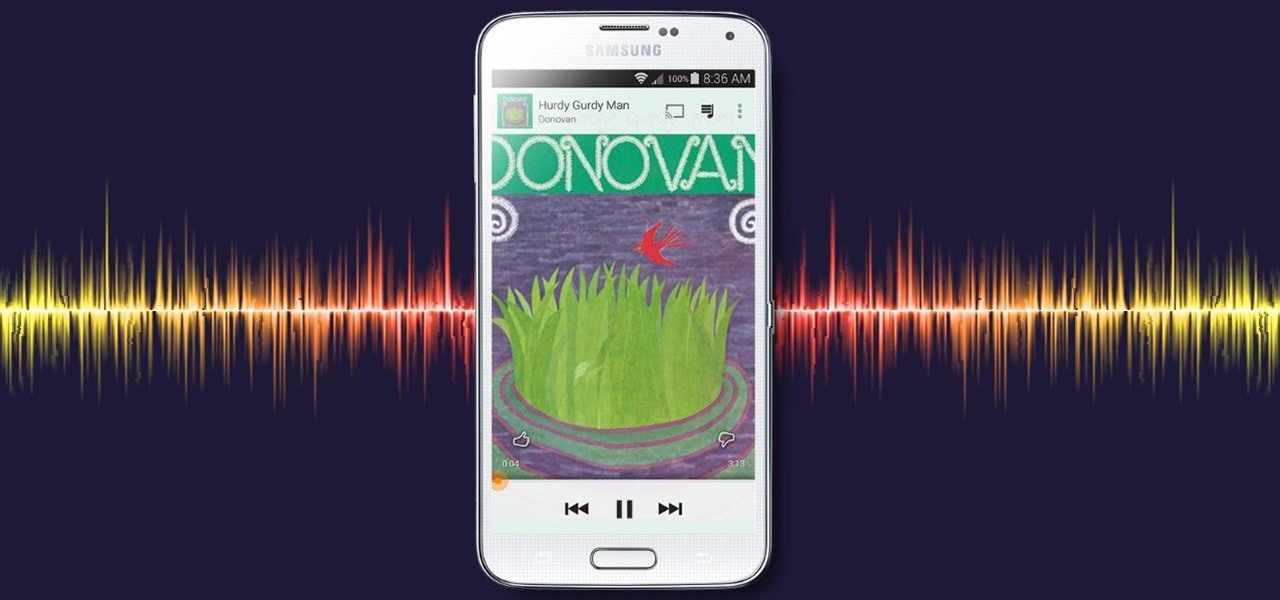
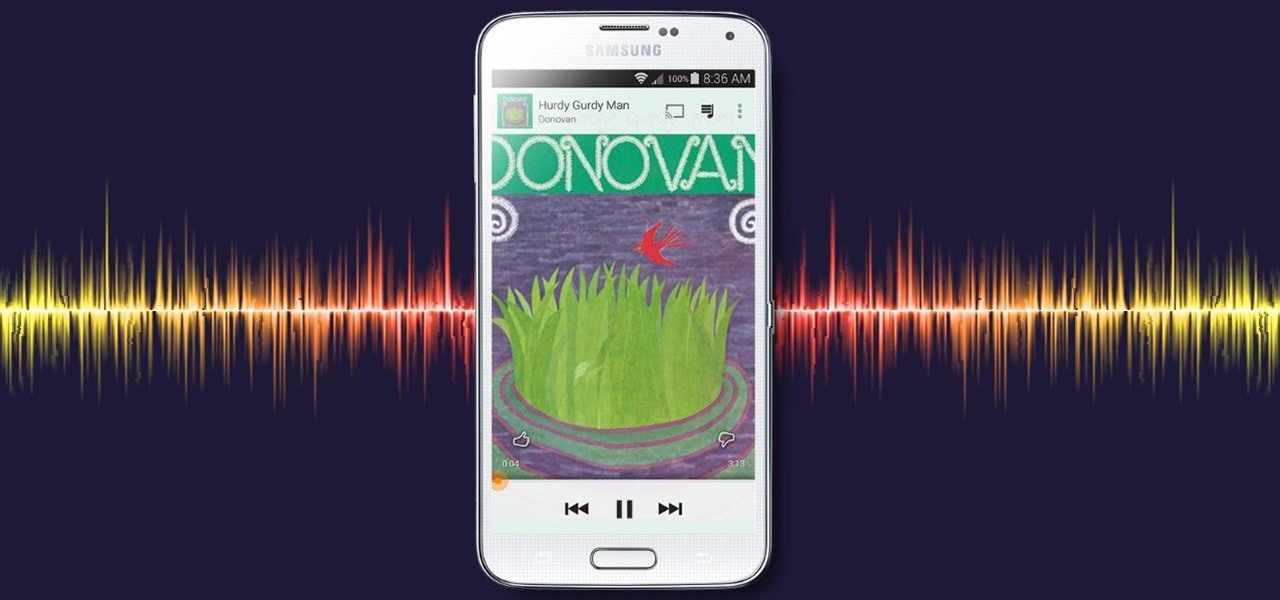
With all of the top-notch specs that the Galaxy S5 sports, the only minor quibble users have had with its hardware is the speaker situation. A front-facing earpiece is used for phone calls, but all other media is restricted to a single rear-firing speaker.

The Galaxy S5's camera is amongst the most capable smartphone shooters on the market. With a 16-megapixel sensor that is capable of recording 1080p video at 120 frames per second, the stat sheet was officially stuffed when Samsung brought this device to market.

It takes a lot of time, effort, and cash to create a unique Halloween costume that will likely never see the light of day after the 31st. Not to worry: you can do it on the cheap and feel savvy and creative while everybody compliments your ingenuity.

Welcome back, my hacker novitiates! Every so often, a MAJOR vulnerability appears that makes millions of systems vulnerable to attack. The most recent, named Shellshock, basically leaves every Mac OS X, Linux, and UNIX system on the planet vulnerable. As nearly two-thirds of all web servers on planet Earth run one of these operating systems (primarily Linux), that's a whole lot of systems out there waiting to be harvested.

Reddit is home to tons of fun and unique content. A starting point for the various memes and videos that eventually make it into your Facebook feed, you could seriously spend all day just browsing different subreddits and not get bored.

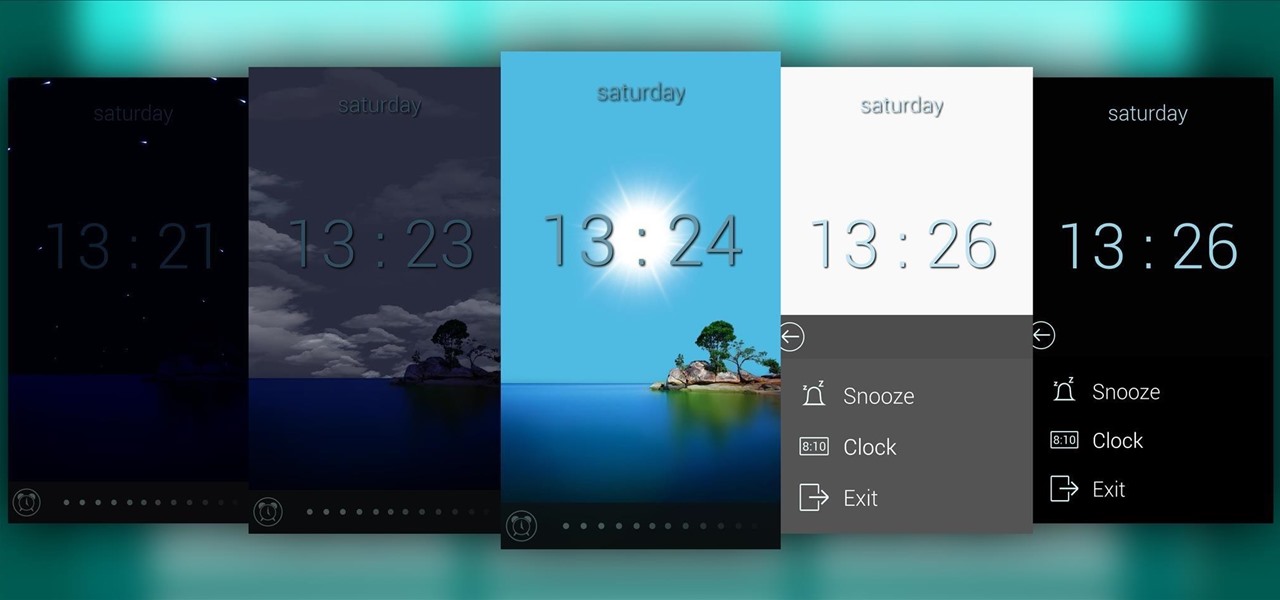
Most alarms just make noise to wake you up, and it can be a bit jarring coming off of a deep sleep to suddenly being woken up by a blaring sound. On the flip side, if you're a heavy sleeper, this might not even be enough stimuli to snap you out of your 8-hour coma.

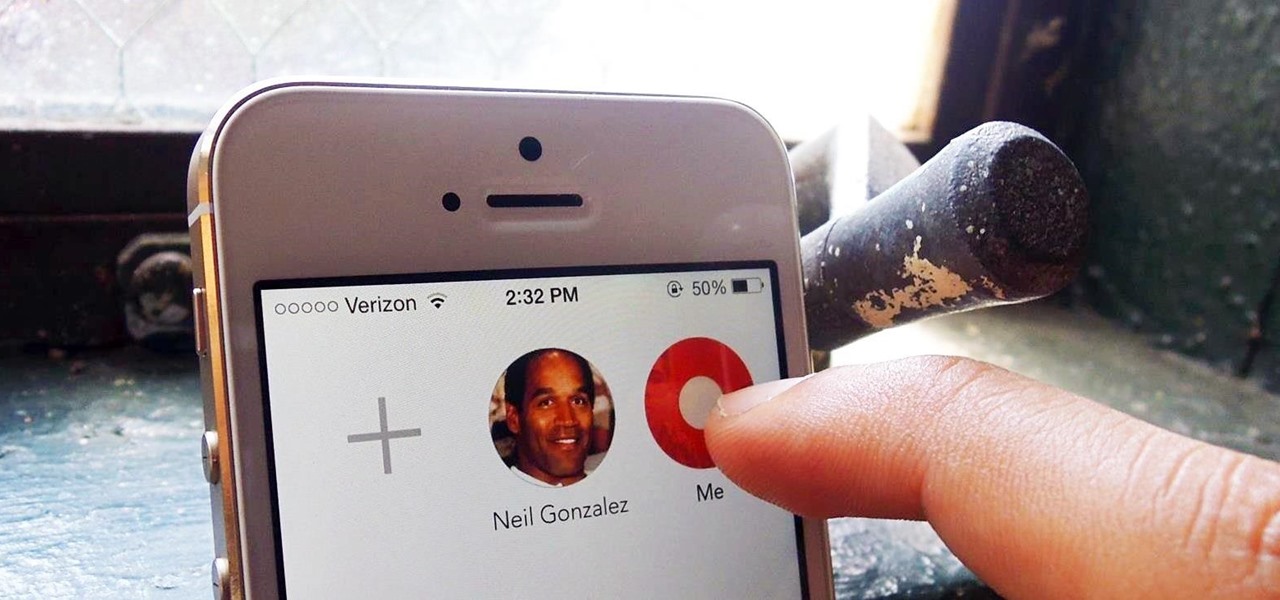
Apple is bringing one of the biggest updates ever to its Messages app, including a feature that will allow users to send audio messages back and forth with the press of a button. Goodbye, voicemail.

Welcome back, my tenderfoot hackers! I have written many tutorials on hacking using Metasploit, including leaving no evidence behind and exploring the inner architecture. Also, there are my Metasploit cheat sheets for commands and hacking scripts.

Android has had predictive text for a while now, both with stock and third-party keyboards such as Fleksy, SwiftKey, TouchPal, et al. Apple is even getting on board, with stock predictive text and third-party keyboards for iOS 8, slated for public release later this year.

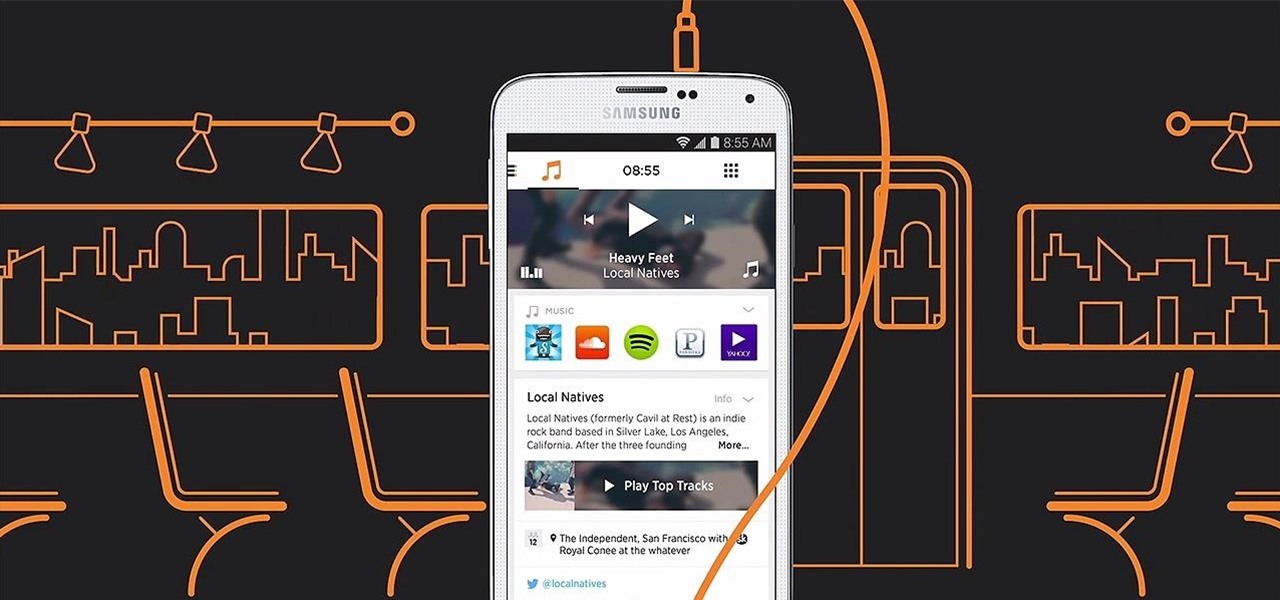
When Yahoo! purchased the home screen replacement app Aviate back in January, many were wondering if the internet giant intended to continue development of the launcher or if the transaction was just another acqui-hire.

Time is money, and if your job requires sending out hundreds of generic emails—think "Thank You" notes and sales pitches—you could save days of work by creating templates stored within your Gmail called "canned responses."

Prying into people's lives without them putting up their guard can be difficult, unless you can convince them that you already know them very well. Most people don't have many friends they can be honest with, and this can be exploited. Once they're convinced you already know their secrets, they'll start to fill you in on the little details.

Most of you probably spread ketchup all over hamburgers and fries. Some of you may even drink it straight. But did you know that tame (and slightly addictive) condiment in your fridge is also a powerful cleaning agent?

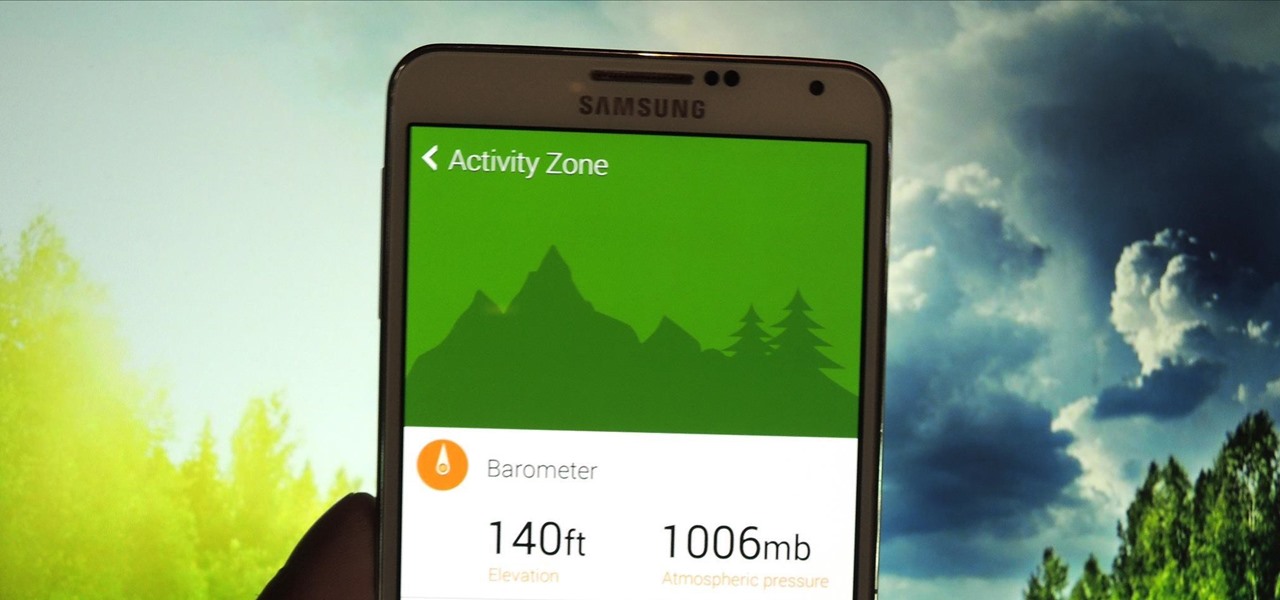
Last week, I showed you a peek at the not-yet-released Galaxy S5 Active, the more rugged version of Samsung's current flagship. The man behind those leaks, TK Tech News, has now brought another goodie from the device, and it's one we can have on the Galaxy Note 3.

These days, our smartphones carry some very sensitive data. From banking app passwords to personal photos, there are many things on your Nexus 5 that you might not want other people to have access to.

A few days ago I finally finished my 2 week journey into trying to get OpenVas to work properly. You all may have noticed that you can't just click the setup openvas in kali and have it working properly.

Included in Spotify's new darker, slimmed down redesign is a much needed My Music section, which consolidates all of your starred music, local files, and playlists into a personal collection of songs, albums, and artists, similar to how iTunes organizes your music. This makes me wonder...

With popular remote desktop app LogMeIn recently ending its free service, lots of Android users have begun looking for alternatives. There are some good ones out there like TeamViewer and Microsoft Remote Desktop, but today, Google released an app that makes a pretty good contender.

Google recently updated their TOS to reflect the email scanning practices they use in Gmail, which are used to display more relevant ads, among other things.

Figuring out someone's password, pattern, or PIN isn't very difficult—simply watching over their shoulder or following the oil marks left across their screen is enough to figure them out and bypass whatever lock screen security they have.

Whether you've been fully converted or just want a little Apple with your Android, adding your iCloud email to your Galaxy Note 3 is a fairly simple task. Usually, Apple and Android don't play nice, but your iCloud address can be added to your stock email app just like any other email account.

Muzei Live Wallpaper is a popular Android app that refreshes your home screen background at set intervals, turning it into blurred pieces of artwork or photography while keeping your icons and widgets in the spotlight.

Fresh off the heels of their latest agreement, Google and Samsung may soon be further aligned in their mobile technology outlook. The two tech giants signed a cross-licensing patent agreement, but that doesn't mean that Samsung was just going to start putting out stock Android devices. Quite the opposite really, as we saw from leaks of its new Magazine UX. The new user interface was shown during Samsung's presentation of it's latest Galaxy tablet at this years CES, and as reported to Re/code,...

Introducing a unique way to share photos and videos among friends and family, Snapchat was the big hit of 2013 (despite its many flaws). Thanks to its ephemeral nature and lack of third-party sign-in integration, it quickly grew into a multibillion-dollar company in the span of just 12 months.

As precious as we like to think that all of the photographs on our smartphones are, they're really not. Every time I rummage through my extensive index of pictures, I quickly realize how many one-off pictures I have, which served their purpose a long time ago and are no longer important.

Initially introduced as an Easter egg deep within Android's operating system, the Daydream screensaver feature turned official in the release of 4.2.2 Jelly Bean. Now, it's been out for a few months, which means developers have already figured out how to take advantage of it in their own ways.

With only a day left until Halloween, a full and detailed costume is too much to throw together for most people. But you still have to dress up as something, right? No one will give you candy or let you into a Halloween party if you don't even put in some effort.

Android gets a lot of love for its immeasurable amount of customization, and for the most part, you don't even have to do any heinous hacking to swag out your Samsung Galaxy S3 or other Android device.

The majority of our documents and music are digital, which is great for convenience, but it presents a problem for those with a lot of stuff—where do you store it all? There are tons of sites that offer cloud storage, like Dropbox, SkyDrive, and even Flickr, but most of them have limits unless you want to pay, and no way to connect them all.

Search Engine Optimization is important for every successful SEO or blogging campaign. Therefore it is required to be implemented in the correct manner. Google consider many factors while ranking a webpage and it keeps on changing. Some of the common SEO mistakes which you must avoid are as follows:

These days, we increasingly have more and more devices in our everyday possession. While a notebook computer, a tablet, and a smartphone may seem like overkill, they do work to make our lives easier and even help reduce clutter in certain ways.

While the pope himself may not be Steampunk, you might be amazed at what is: the coronation stove. For those who don't know, it's been a tradition for a very long time to signal the election of a new pope (or the lack of a new pope) via colored smoke. More specifically, once the cardinals have all voted for the new pope during the conclave, the ballots are burned in a special stove in the Sistine Chapel, and the smoke is visible in St. Peter's square.

Just about anyone who's been gaming for a long time occasionally feels nostalgic for the simpler consoles of yesteryear. I don't play much anymore, but my grandmother (yes, grandmother) got me started on NES when I was about three years old, and most days I'd still take that over the 360 or PS3.

So many times, you turn on your computer, you open your front door, or you sit down on the couch to watch some well-earned TV, when you think -- Gosh! If only I could do this or this, life could be so much easier! And then, if you were a boring person, you would slouch even further down on the couch and continue to watch those reruns of The Sopranos.

I am a man who enjoys a good cup of crap. Not just any crap, but the kind that makes the Seattle coffee-snob inside of me feel all warm and happy as if the sun were out (which of course it isn't.) It's the kind of crap that has traveled through the intestinal tracts of a nocturnal marsupial, cutely called a Civet. It's the kind of fermented brew that everyone should lay their lips on at least once.

Want the convenience of a throwaway email address without all the hassle? How about anonymous text messaging so you can get to know someone before giving them your real information? Gliph has you covered. Gliph is a service that lets you create an identity around a set of three to five symbols called "artifacts" instead of your name, phone number, or email address. You choose how much information you reveal, and anytime you communicate with someone else who has Gliph, the data is protected us...