Big name individual hackers and hacker groups everywhere in the news are getting caught and thrown in jail. Everytime I see something like this happen, I won't lie, I get a little sad. Then I wonder, how are these guys getting caught? If a group like LulzSec, with all the fame and "1337-ness" can get caught, I think my hacker comrades are doing something wrong.

With so many wireless iOS networking apps for the iPhone, iPad, and iPod touch available, there’s very little reason to connect any of these devices to iTunes, except to update the software. Besides, importing and exporting photos using iTunes has never been one of the best features of Apple‘s mobile device process. Let me introduce you to 5 useful apps for importing and exporting photos to and from your iOS device(s).

So our GUY has traded wallets with a gangster, met a beautiful Grocery Store cashier, and used the Gangsters credit card.

SSH is amazing, and we praise its existence on Null Byte for many reasons. Notably, it allows us to reroute our traffic through encrypted ports on our local host to be sent to its destination when on the go. You can even control your home computers remotely over a secure and encrypted connection. This is handy for a multitude of reasons.

A proxy is a server that lets a client to connect to it and forward its traffic. This enables a certain "layer" of protection by masking your IP. An IP address can be used to learn your location and track you on the Internet, thus eliminating any form of anonymity that you may have.

Warning Don't torrent things that you do not have the rights to torrent. Everything I torrent, I have a physical copy of, and just want a copy on my computer without causing wear-and-tear on my DVD drive's laser. Piracy is naughty.

The challenge of creating garments with unconventional materials has become an all too familiar gimmick for most first year students at fashion schools. The end result is more often than not a catwalk of garbage bags, zip ties, plastic bottles and cans, assembled into a menagerie of mediocrity. Enter Jum Nakao. But while the Japanese-Brasilian artist/fashion designer does use an unconventional and impractical material (paper) for his collection "A Costura do Invisivel"(translation: "Sewing th...
Warnings this only for educational use i dont take responsiblety for any use of this article if you want to use this for use at a school plz contact me at sebzy4@hotmail.com hi im a computer enginer/programmer (NOT games) but i am good at hacking and i want to help. notise that this is just a help site not hacking site but this will help firstimers
So precisely what is an affiliate marketer? Essentially, an affiliate marketer has an online site and also refers guests to some other sites, called 'merchants'. When these site visitors buy things, the other websites pay the particular online affiliate marketer a payment, which depends upon online monitoring softwares which monitors web customers purchases.

A man going by the pseudonym of Ed Dante has written an illuminating account on his life as a career cheater. His clients include ESL students, hopeless dummies, and spoiled, lazy rich kids:

The first marriage to be officiated by a robot took place in Japan this past Sunday. A humanoid robot named I-Fairy stood in as witness at the ceremony between Tomohiro Shibata and Satoko Inoue of Tokyo.

You may not always want to, but there will probably be a time when you'll want to know if an email you send — like a job application or a support request — is opened by the recipient. It's actually easy to implement, and you may be using an email client on your device right now that supports email tracking.

Since its release back in 1988, Microsoft Office has been the top client and server software suite for businesses around the world. Office's domination is thanks to both Microsoft's extraordinary foresight and their continual updates and innovations to ensure that companies always get what they need.

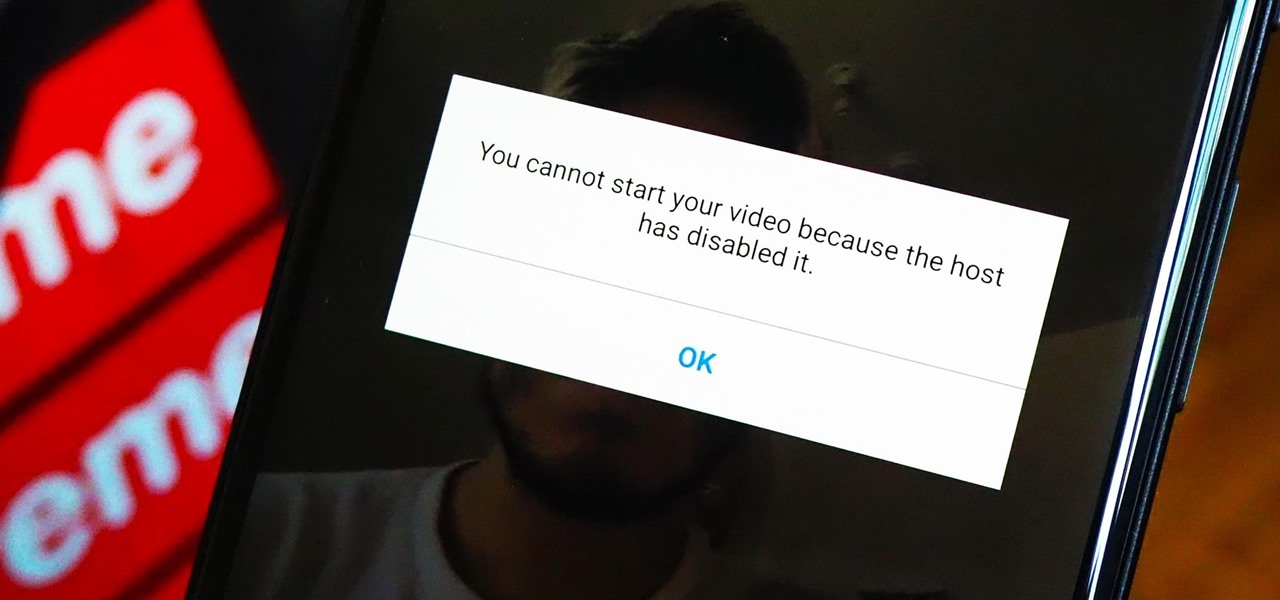
As a meeting host on Zoom, you can't control what a participant does during your live video call, but you do have the power to turn off their camera so that other people aren't subjected to distractions. So if you catch someone in your call purposely making obscene gestures or accidentally exposing themselves while using the bathroom, you can block their camera, as long as you know how.

If you're tired of the so-called "top" tweets appearing first in your Twitter timeline instead of only the latest from the people, companies, and bots you follow, there's a way to get rid of them.

For Snapchat users wondering if that selfie is ready to send to their crush, independent Lens Studio creator Andrew Mendez created a handy tool called the Smile Rater.

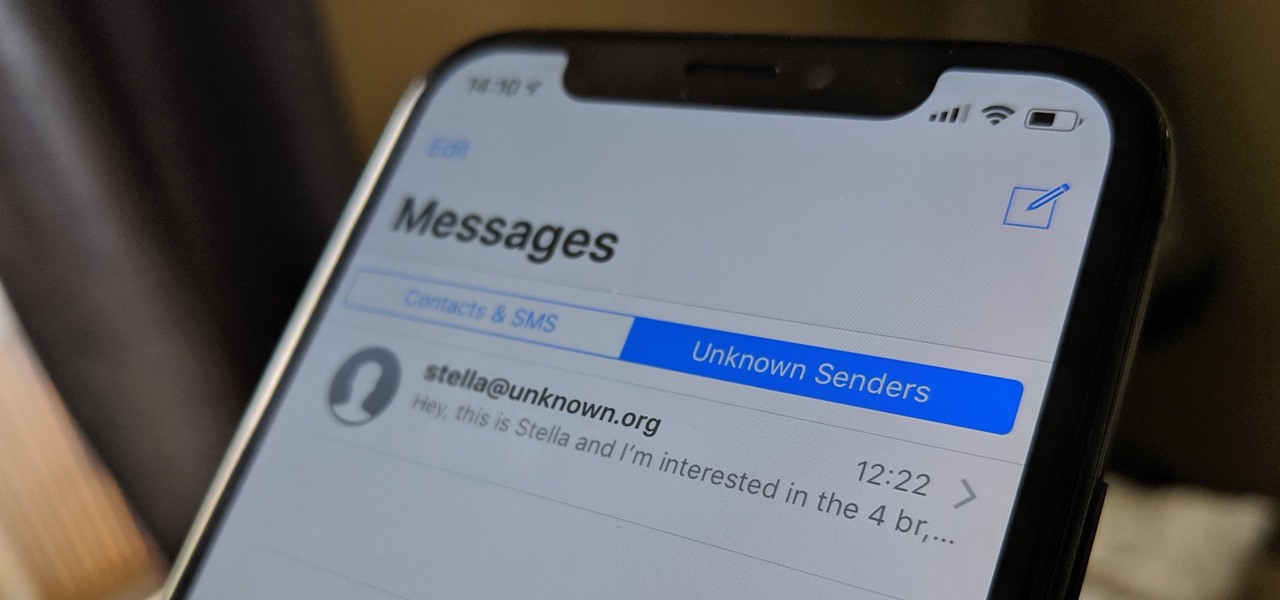
If your job revolves around prospective clients and customers, you may frequently receive iMessages from unknown numbers. Although this isn't necessarily a bad thing, being bombarded with messages from strangers can create disarray in your inbox if you're not careful. Luckily, Apple makes it easier to organize your conversations by allowing you to filter unknown numbers in the Messages app.

After one of Britain's "Brothers Bling" bought Blippar out of bankruptcy, the mobile augmented reality company is getting back to business with the addition of web-based AR capabilities to its platform.

For the release of John Wick: Chapter 3 - Parabellum, Snapchat and Lionsgate aren't just creating AR experiences to promote the movie, they are giving fans the opportunity to create and share their own AR experiences.

Augmented reality platform maker Zappar and its marker-based augmented reality technology have been around well before Apple and Google brought markerless AR to mobile apps.

When it comes to web-based augmented reality, 8th Wall has emerged as one of the leading platform providers, and the company just cranked up its capabilities another notch for AR marketers.

Just weeks after revealing plans to port one of its most vital augmented reality products from HoloLens to the smartphone world, Microsoft has finally opened the mobile software floodgates to the public.

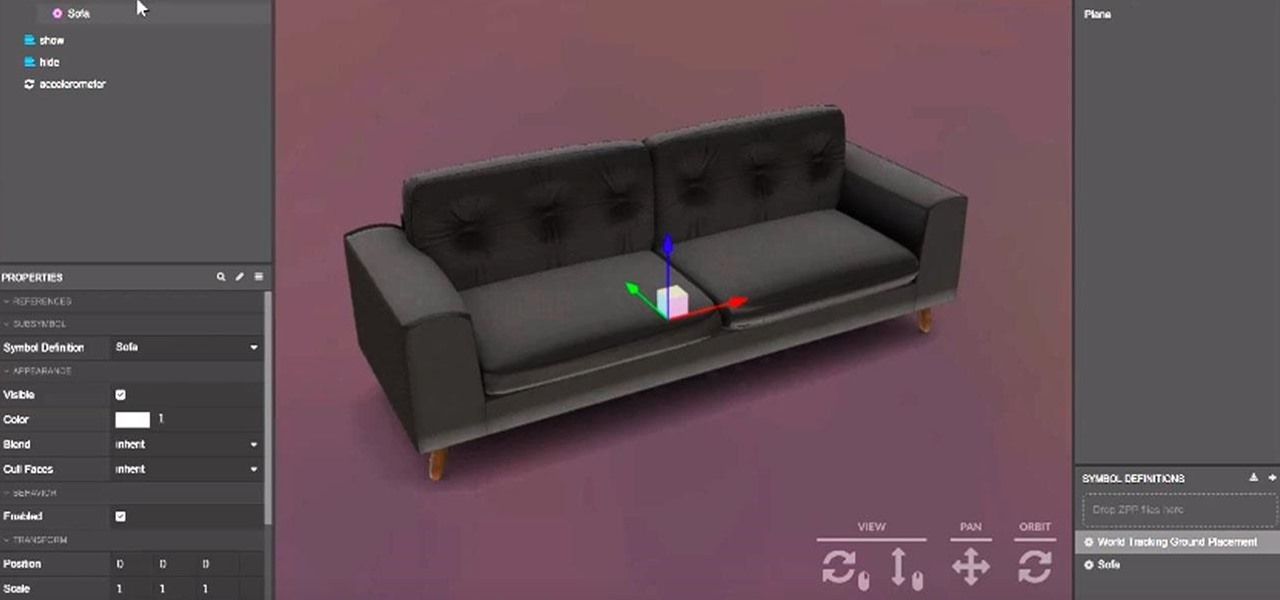
Mobile app publishers are using augmented reality to solve everyday measurement problems from measuring the length or height of items to previewing furniture in the home.

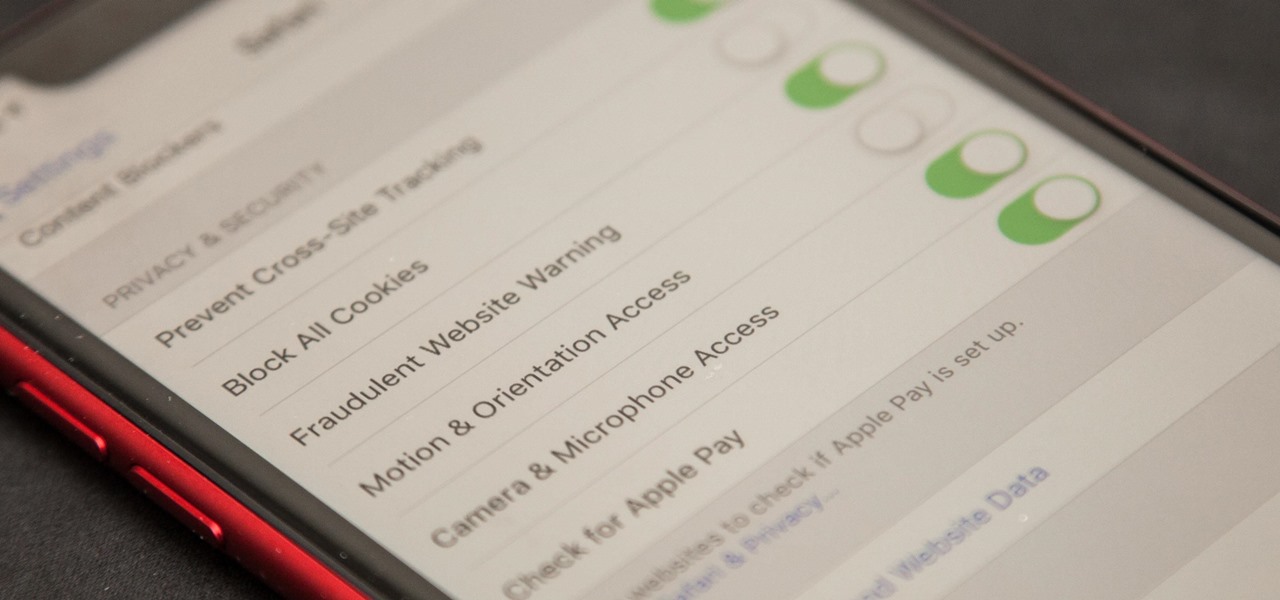
Apple first added the "Do Not Track" option to Safari in iOS 7, which sent a request to site owners and advertisers to not track your browsing activity. By tracking your activity, those third-parties could tailor content to you that you're more likely to interact with. While the feature was always opt-in, it's no longer a feature at all in iOS 12.2 on your iPhone.

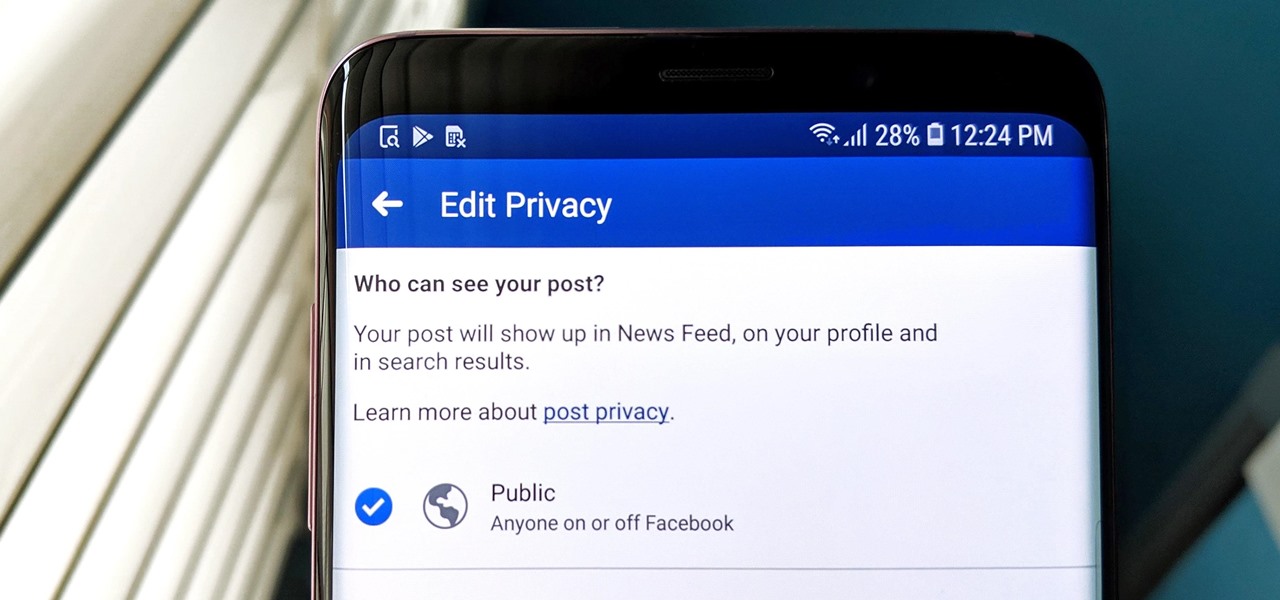
Facebook has grown into one of the central hubs of the internet where ideas are shared with others. But with the rise of brand development, individuals and companies need to get their messages out beyond their group of Facebook friends so it can be seen by more of the world.

The wildfires that spread across Northern California for two weeks in November were among the deadliest and most destructive in the state's history. Ultimately, the incident claimed 85 lives, and hundreds of people are still missing in the wake of the disaster, which impacted over 154,000 acres of land.

In their first head-to-head major contract clash, Microsoft has emerged victorious over Magic Leap, as the US Army has awarded a $480 million contract to the HoloLens maker.

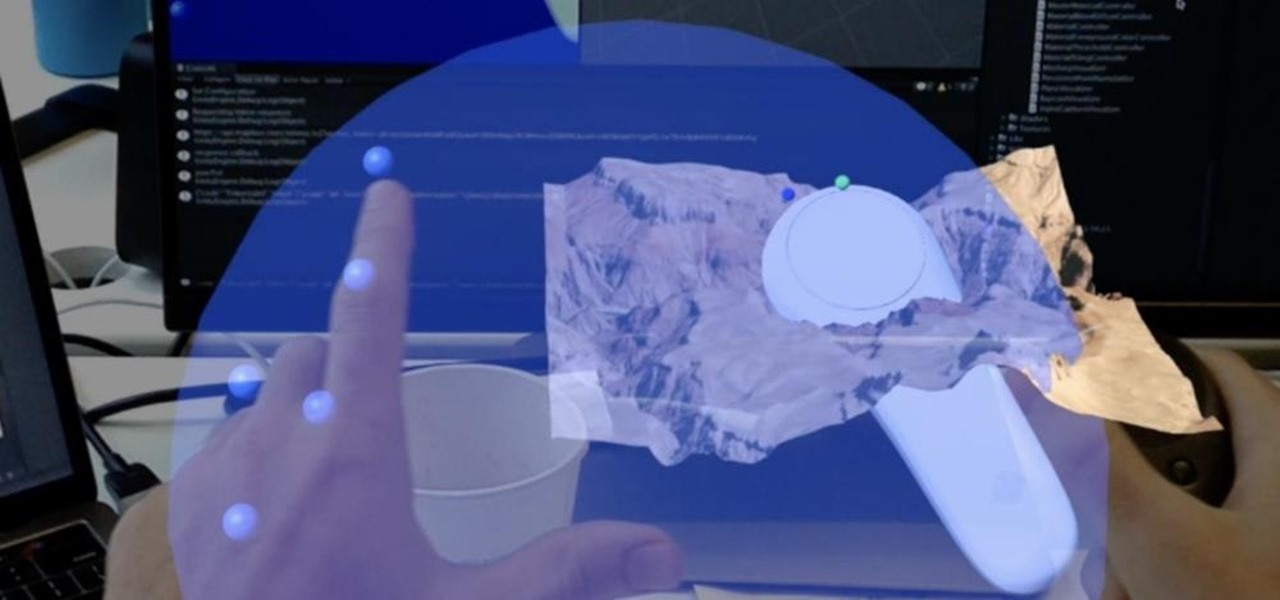
Less than 20 days after the launch of Magic Leap One, Mapbox has jumped at the chance to provide its map services to Magic Leap developers through its Maps SDK for Unity.

On Thursday, at the Augmented World Expo, Stockholm, Sweden-based eye tracking company Tobii announced that the augmented reality display company Lumus will integrate its eye tracking technology into the Lumus DK50 AR development kit.

Fast-casual burger restaurant Bareburger expects to soon replace all of its paper menus with 3D models of its burgers and other items rendered in augmented reality, but for now, the company is preparing some rather interesting limited AR interactions.

The augmented reality and VR arm of Verizon, Envrmnt, wants to make it really easy for anyone to create AR apps.

On Tuesday, at the Geneva International Motor Show, Volkswagen gave the world an early peek at a futuristic autonomous concept car that includes a virtual AI host embodied in an augmented reality interface.

Your email is just that — yours. You shouldn't have to worry about other people gaining access to it on your iPhone. Fortunately, Outlook agrees, and has included a way for you to protect your messages with one of two keys no one possesses but you — your face or fingerprint.

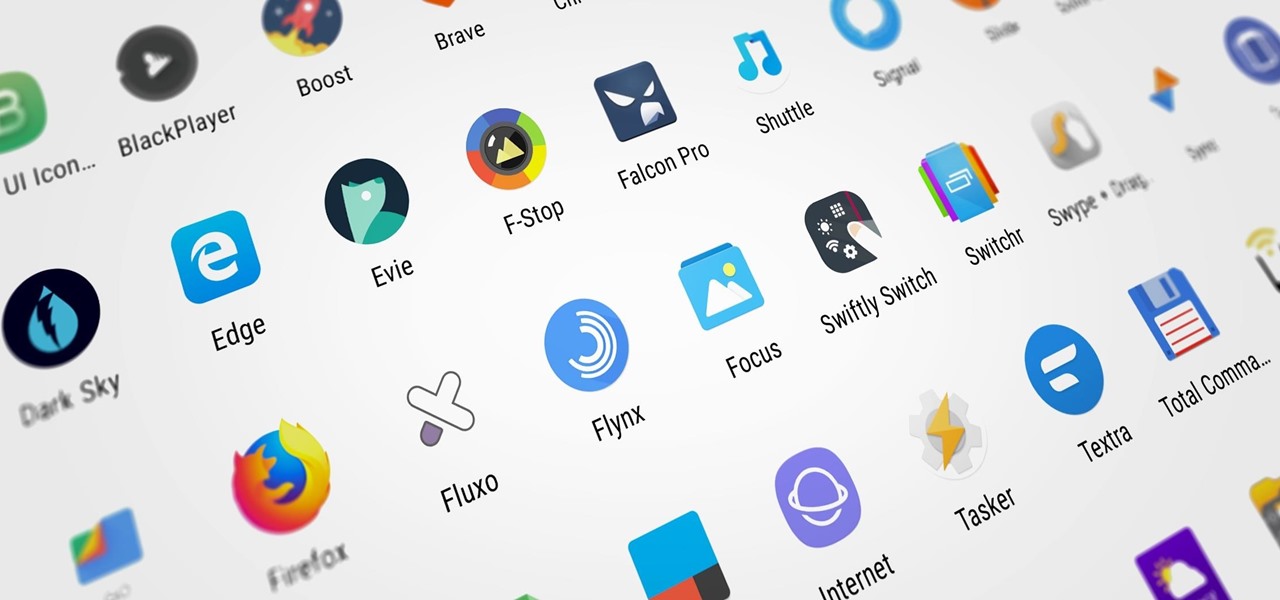
Whether you're new to Android or you just haven't kept up on the app scene lately, we hand-picked over one hundred essential apps that are all designed to improve your experience. From custom launchers and icon packs to weather apps and file explorers, there's something for everyone in this list.

From media insiders to the halls of politics, news travels fast on Twitter, making it one of the most powerful social media channels for disseminating or collecting information. Now, for better or for worse, you can immerse yourself in the data firehose of Twitter in augmented reality.

While AR apps by Modiface and Perfect Corp. have made it easier for people to shop for makeup without setting foot in a store, MAC Cosmetics wants to give its brick-and-mortar customers the same experience.

While millions eagerly await the stable Android 8.0 release for the Galaxy S8, the beta is already in the wild and readily available. Notable improvements include notification channels and the revamped Samsung keyboard. One aspect often overlooked are new customization options, a huge part of Android. Let's take a look at what's new for customization on the S8's home screen in Oreo.

With a pair of new APIs and low-latency media servers, Twilio's Programmable Video platform could soon help ARKit and ARCore app developers build shared AR experiences between multiple users.

Virtual private networks, or VPNs, are popular for helping you stay anonymous online by changing your IP address, encrypting traffic, and hiding your location. However, common IoT devices, media players, and smart TVs are hard to connect to a VPN, but we have a solution: Turn a Raspberry Pi into a router running through PIA VPN, which will ensure every connected device gets the VPN treatment.

As augmented reality gains popularity, the demand for delivering related services and generating content increases. This is demonstrated by a pair of investments from the past week, one in the expansion of a technology lab and another in the form of seed funding for a content studio.