Welcome back, my fledgling hackers! Sometimes, for a variety of reasons, we can only get a command shell on our target system. For instance, with Metasploit, it's not always possible to get the all powerful Meterpreter on our target system. In other cases, we may be able to connect to a command shell via Netcat or Cryptcat.

Welcome back, my budding hackers! We've spent a lot of time learning to compromise Windows systems, and we've successfully compromised them with Metasploit, cracked their passwords, and hacked their Wi-Fi. However, very little time was spent developing ways to extract the information from the system once inside.

Ever since the much-lauded effects of the Mediterranean diet became widely known, people have been buying olive oil by the gallon. A diet that prevents heart disease, is based on fresh, seasonal foods, and includes a tasty as hell fat like olive oil? Duh—that's a no-brainer.

Welcome back, my budding hackers! One of the keys to becoming a professional and successful hacker is to think creatively. There is always a way to get into any network or system, if you think creatively. In previous tutorials, I have demonstrated ways to crack passwords on both Linux and Windows systems, but in this case, I will show you a way to get the sysadmin password by intercepting it from a Remote Desktop session.
The Lamborghini Gallardo is a sports car that most auto enthusiasts can only dream about, and with its cost at over $200,000, it's literally a "dream car". But you can get one step closer to reality with this realistic and artistic drawing of the Gallardo sports car. Maybe you can sell your masterpiece sketch for $200K and finally get behind the wheels of this 2-doored beast. Follow along with Merrill K to replicate this Lamborghini model on paper. Pause the video when needed.

Sloppy Joes are a great dinner when you don't have all night to cook. They're messy, so kids love them, and they pack in a whole bunch of 'secret' veggies, too! Use lean beef and make these healthy and delicious Joes along with Betty! Everyone will love them!
When stories are told about people in need, the ones with happy endings include the details of someone that produced an action that caused the people in need to be better off than before. Do we have to wait for the identification of a need? Could we on purpose just plan to present products and services that cause our customers and client to see an improvement in their circumstances just because of the business interchange with an owner manager of purpose? The fair exchange of products or serv...

Tattoo lady and reality TV star Kat Von D is obviously extremely talented with the tattoo needle. Creating interesting designs for clients that include celebrities, Kat Von D exudes a distinctive style that includes looking like a tougher version of a classic pin up.

In this video, we learn how to give a professional hand massage. First, spread oil onto the hand with your hands, which will prevent you from sticking together. After this, open the hand up and interlock your fingers with theirs and start to massage the inside of the hand. Open the hand up and work your fingers into the sensitive muscle areas. Go slowly, but apply enough pressure around the hands to make a difference. After this, work the tendons on the front and work your hands around each o...

This instructional video Nehal Kazim from Site shows you how to make a complete Facebook fan page. Before creating a fan page evaluate the reasons of making a fan page. A fan page lets you connect with your future clients and fans and keeps them updated and gives them a platform to talk about your organization. To create a fan page go to the bottom of any page and click 'Advertising', select pages and click create a page. Select a suitable category and a suitable name make sure to select it c...

For a mom, there is always so much to do that your own personal care routine may take a back seat. But in this video, top hair stylist Gary France offers tips on how to style very short hair for the busy mom. France shows us his process on a busy working mom. The client receives a lighter color to brighten up her look, a trim to texturize her hair and styles the hair without using a blow dryer, which is great for saving time. France shows us that just because you have kids to take care of doe...

Instead of using Photoshop, why not give Apple's Aperture a try? Aperture is designed more for post-production work for professional photographers, letting you cull through shoots, enhance images, manage massive libraries, and deliver stunning photos.

Instead of using Photoshop, why not give Apple's Aperture a try? Aperture is designed more for post-production work for professional photographers, letting you cull through shoots, enhance images, manage massive libraries, and deliver stunning photos.

In this episode of Full Disclosure we are explaining the website attack known as Cross-Site Scripting (XSS). Cross-Site Scripting is a type of security vulnerability that affects web applications that do not sanitize user input properly. This kind of vulnerability allows an "attacker" to inject HTML or client side script like JavaScript into the website. Cross-Site Scripting is most commonly used to steal cookies. Cookies are used for authenticating, tracking, and maintaining specific informa...

Taking one-handed pictures with your phone can quickly devolve into a juggling act. You have to secure the phone in landscape mode (if you're doing it right), tap to focus, and then somehow hit the shutter button without shaking the device too much. Fortunately, Samsung has a nifty feature that'll help you keep a more secure grip on your Galaxy S9 or S9+ as you take photos with one hand.

After finding and monitoring nearby wireless access points and devices connected to them, hackers can use this information to bypass some types of security, like the kind used for Wi-Fi hotspots in coffee shops, hotels, and in flights high above the ground. By swapping their MAC address for that of someone already connected, a hacker can bypass the MAC filter and connect freely.

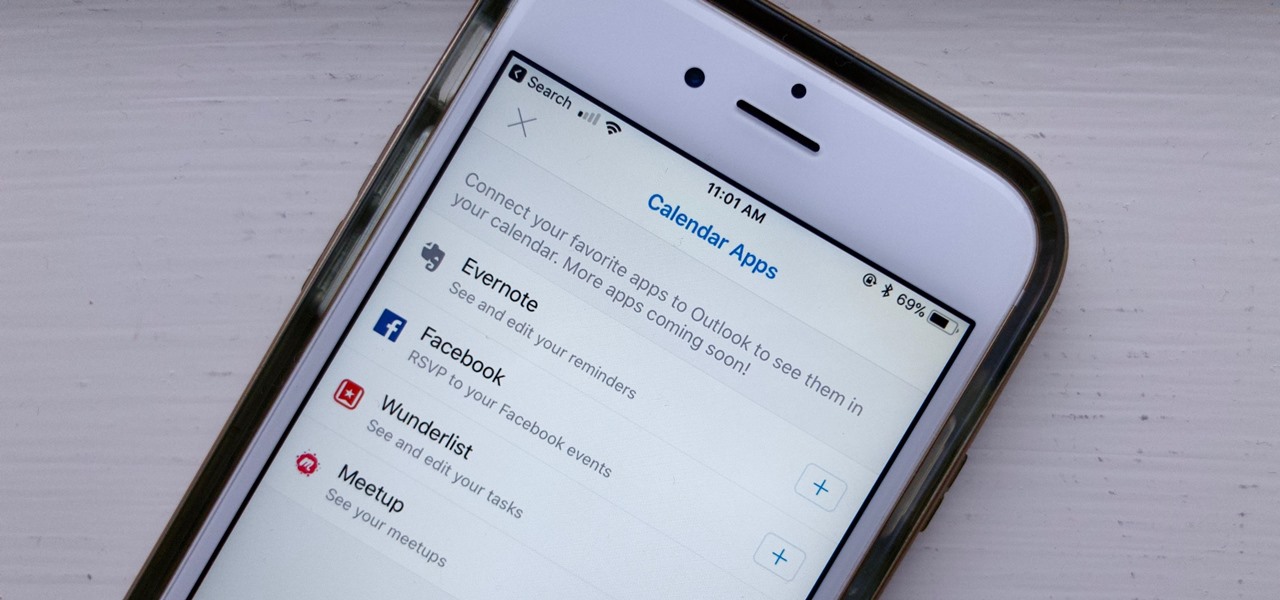
If you've read our list of the best email clients for iOS, you'll know Apple's Mail app doesn't cut it when it comes to third-party integration. If you want to use some of your favorite apps directly in your mail client's calendar, go with Outlook.

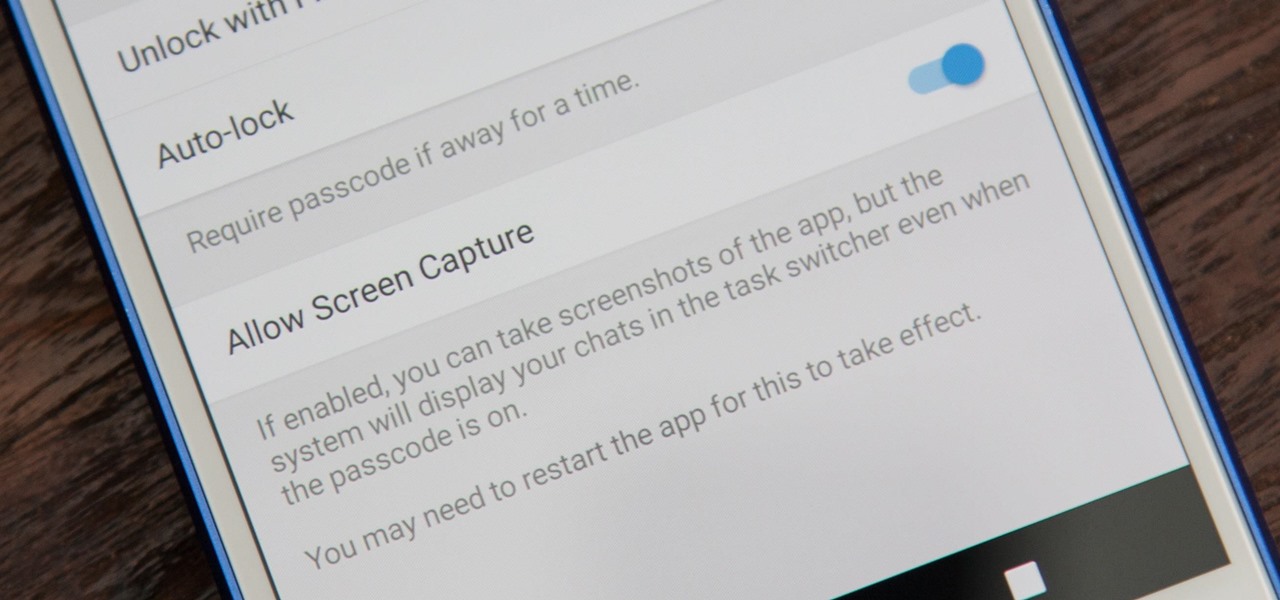
While it's easy enough to take a screenshot of an end-to-end encrypted Telegram chat thread using an iPhone, it's an entirely different story on Android phones. Telegram disables screenshots for Secret Chats by default on Android, and not everyone can turn it on.

Imagine for a moment that a VPN is like putting on a disguise for your computer. This disguise works to change your IP address, secure your traffic with encryption, and mask your location to bypass regional restrictions. This makes it a helpful tool for both whistleblowers and journalists. VPNs are also built into the well-known Tor Browser.

A couple days back we told you about the 30-day free trial for people interested in YouTube Red, and now Google is running a concurrent promotion that really sweetens the deal, especially if you're a first-time subscriber and own or plan to buy a Chromecast.

First of all, Merry Christmas and Happy New Year to all Null-Byters that learn and teach in this wonderful site. In this article we will explore the basics of the meterpreter's IRB (Interactive Ruby Shell).

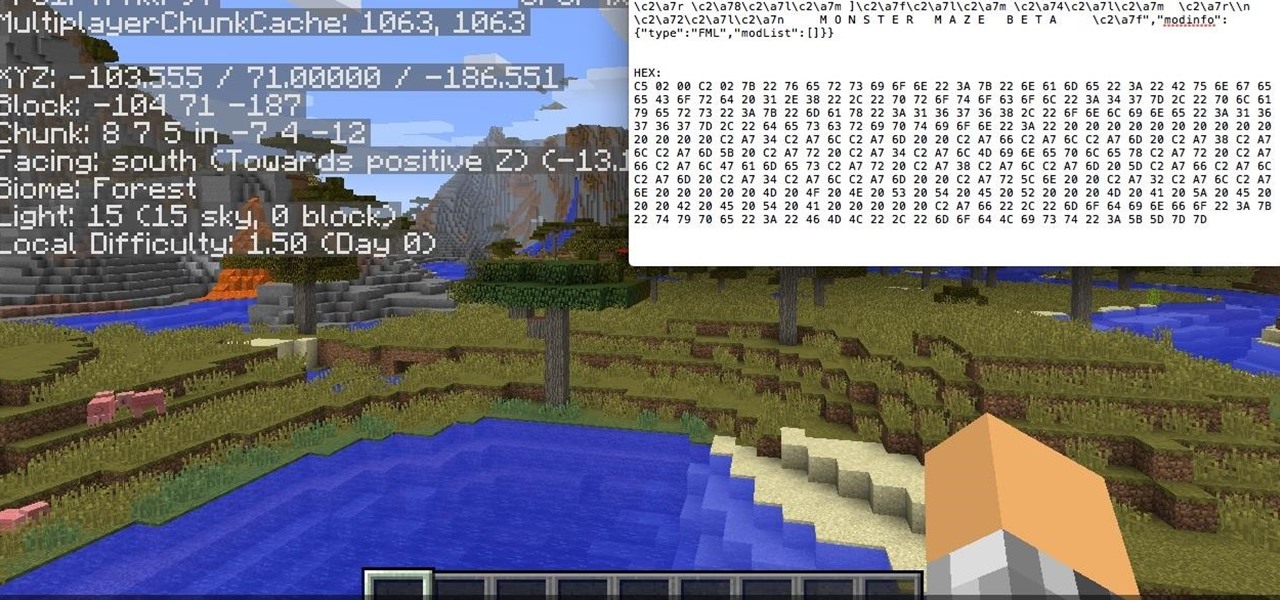
Hello, fellow hackers. I'm sure we've all seen it somewhere: the undying question of "How do I hack the game so-and-so?" And the answer usually is, "Come back when you actually know how to hack!" But how does one even go about "hacking" a game? What could that even mean?

Welcome back, my budding hackers! With this article, I am initiating a new series that so many of you have been asking for: Hacking Web Applications.

Yes, "Safer Internet Day" is a real thing, and it's actually been around for 12 years. This year, Google again will be commemorating the event by giving away a 2-gigabyte storage bump for their Google Drive cloud service if you simply run through a security checkup.

When Google Play Music launched a few years ago, I ditched iTunes and began using the service as my one and only source for listening to my personal music library. While All Access is great, I still prefer the radio feature on Spotify, so I still use that to discover new music.

Before Continuity and Handoff were even announced, Pushbullet was already allowing users to quickly send notes, links, and photos between their devices with a few clicks.

We've all been there. Rushing to find an outlet because your smartphone's battery is about to die and you're in the middle of uploading a picture on Instagram or something else of dire importance. Android's operating system shuts down automatically when ever there is 1% left in order to allow for a proper shut down, and so as not to mess with the calibration of the battery, extending its overall life.

It's fairly easy to switch between running apps on the Nexus 7 by hitting the Recent apps key in the Navigation bar at the bottom of your screen, but for me—it's just not good enough. I don't particularly like leaving the app I'm currently in to see this menu, and the menu itself is kind of clunky, and overall, not as fast as I'd like it to be.
In any project management career, there is no such thing as a person who knows everything for each project. Many times, those who got too much confident with their jobs fail because they were not able to make things clear before and during the project implementation.

In my first few articles, we focused on operating system hacks. These hacks have been primarily on older operating systems such as Windows XP, Windows Vista, and Windows Server 2003.

Everything is documented these days, thanks to the Internet and mobile devices. Most people who own a smartphone use it to take lots of pictures. If you're one of those people, an app called Scoopshot can help you turn some of those photos into extra cash. Scoopshots lets you post your pics so that news organizations can pay you to use them. Companies can also post tasks, so if someone is looking for a particular photo in your area, you can accept the task, go take the photo, and earn money f...
I've noticed that a few people using the crypto-currency, Bitcoin are having issues importing private keys to their Bitcoin wallet. This is easy to do and doesn't require anything other than your Bitcoin client/daemon (as of ver0.6.0 ) and the command line.

To become a bounty hunter, you will want to first check your state's laws to see if you need to be a licensed private investigator. If you live in Florida, South Carolina, Oregon, Wisconsin, or Kentucky, don't even try it--bounty hunting is not allowed! Otherwise, your first step is to find a client who needs a target to be caught. Bail bond agents employ bounty hunters to track down people who have refused to show up to court. Find out who your target is. Assemble a file, look into any recor...

In this video tutorial, viewers learn how to create a FTP from a local computer to a website. In this video, viewers are shown (once you've chosen a web host) how to perform FTP file transfers from your local computer to your website. FTP (File Transfer Protocol) is a process that you can use to transfer files from your local computer to a remote computer (your website). Once you've set up a hosting account, your hosting company will provide you with FTP login credentials. Using an FTP softwa...

Enabling Telnet in Windows Vista is a little bit more difficult than its predecessors but it still can be done. This video will demonstrate exactly how to enable Telnet in Windows 7 and Vista.

The video shows us how to use a proxy to bypass the Internet Filters. Most of the times in our schools and colleges most of the websites including the social networking ones will be blocked for security reasons and makes us unable to log into those websites. In such cases even the ones from the YouTube, several videos will be blocked. So in this video, we will be shown how to bypass those filters and log into those sites. Firstly go to the website Proxapp and over there you will be asked the ...

When conducting covert mobile surveillance with video it is vital to have a good bag that will contain and allow you to get footage in an inconspicuous manner. Always take into consideration the lighting and distance you’ll be at.

Do your presentation skills need a little work? Being in front of a crowd or some potential clients may be one of the hardest things you will ever do, but staying confident makes all the difference. Losing any bit of confidence will result in your presentation falling flat and killing your self-esteem, and perhaps even risking your job. So, being confident is a must.

Microsoft Windows Vista Tips - Finding Information with Instant Search in Microsoft Office Outlook 2007 - Somewhere in the hundreds, or perhaps thousands of messages in your Microsoft Office Outlook 2003 mailbox is the one that has the information you need about that client meeting on Thursday. So how do you find it without reading through every one of your messages? The new Instant Search feature in Microsoft Office Outlook 2007 allows you to find the information you need instantly. For more...

Work out the pelvis with pelvic tilts. Learn about exercises for strength and flexibility in this training video. Take action: keep your back flat, this is a high repetition exercise, and keep feet flat on floor. Michelle, the instructor in this how-to video, is a personal trainer at a gym in NC and has been a personal trainer for several years. She is certified through ACE and is a certified aerobics instructor as well. Her Specialty is weight lifting and she enjoys training aspiring female ...