The idea of remote assistant apps in augmented reality has been taking off in the last couple of years, but Epson is introducing a differing kind of solution for companies that may benefit from a more straightforward dynamic before going full-on immersive with higher-end AR remote assistance tools.

Smartglasses maker Vuzix rushed out of the gate to be the first company to announce hardware powered by the Qualcomm Snapdragon XR1 for augmented reality wearables, but now the company is buying time until the product is ready to ship.

Hot on the heels of all the talk about Google's newest Android Q update, known as Android 10, there's a new beta to check out. OnePlus is one of the many partners that can now offer its users a chance to test the latest version early. That means you can install the newest Android Q beta right this second on your OnePlus 6, 6T, or 7 Pro just like Google's Pixel smartphones.

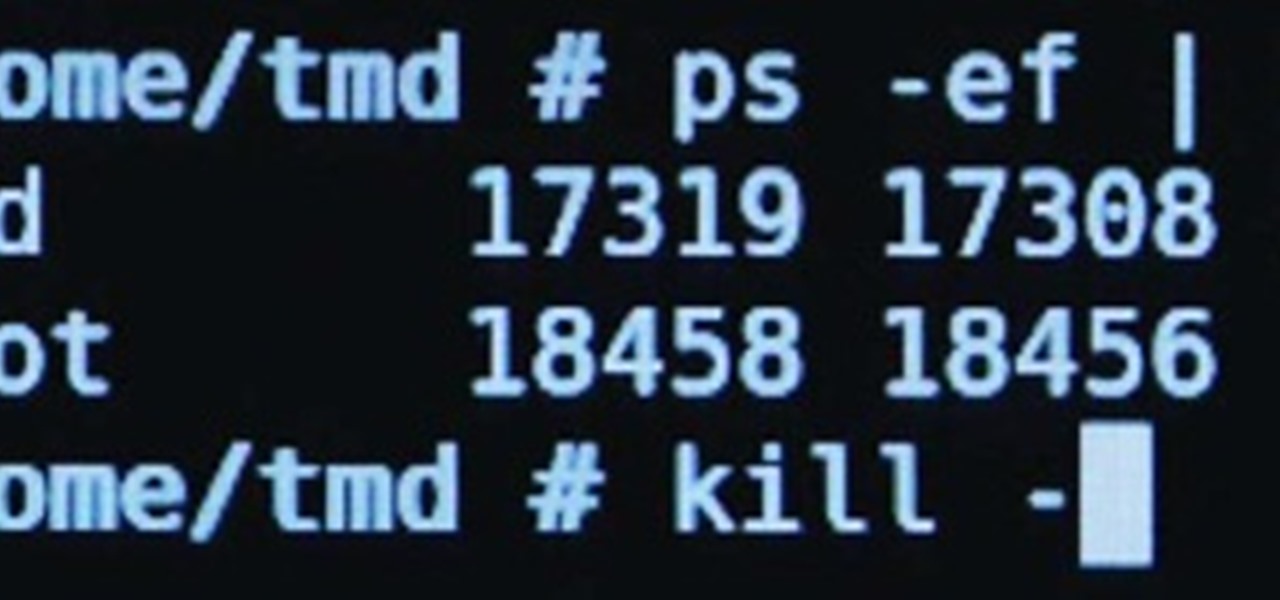
With just a few taps, an Android phone can be weaponized into a covert hacking device capable of running tools such as Nmap, Nikto, and Netcat — all without rooting the device.

Passwords and data stored in web browsers are extremely valuable to hackers. If not for financial gain, black hat hackers may still leak your passwords and personal information for amusement. Never undervalue what you're worth to a hacker.
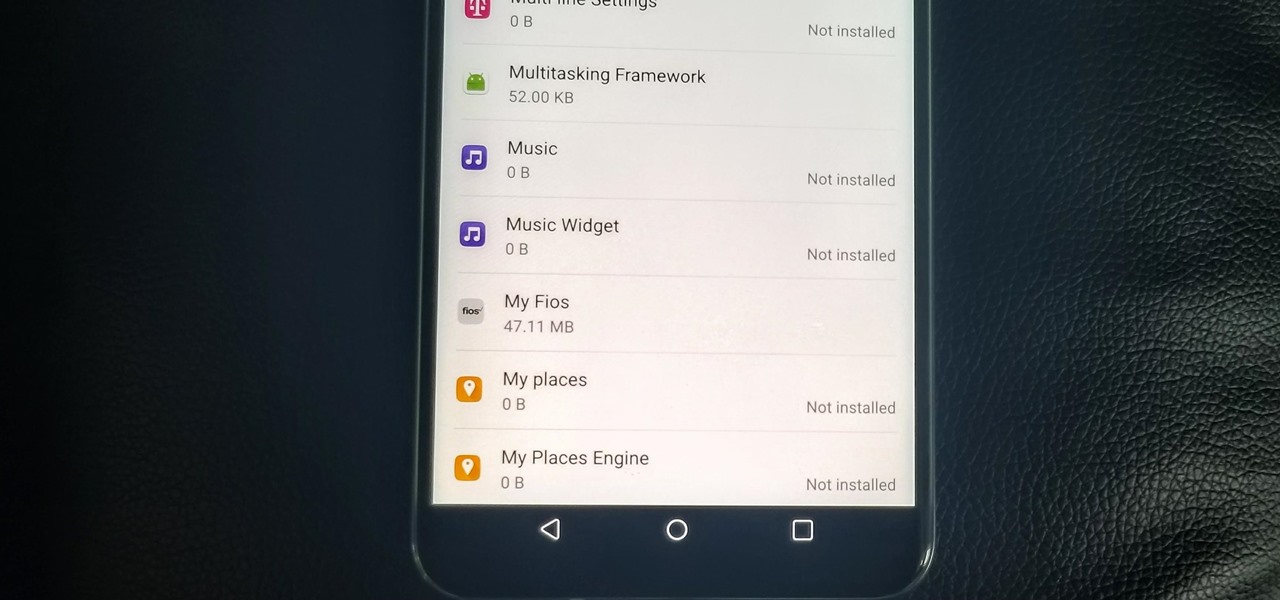
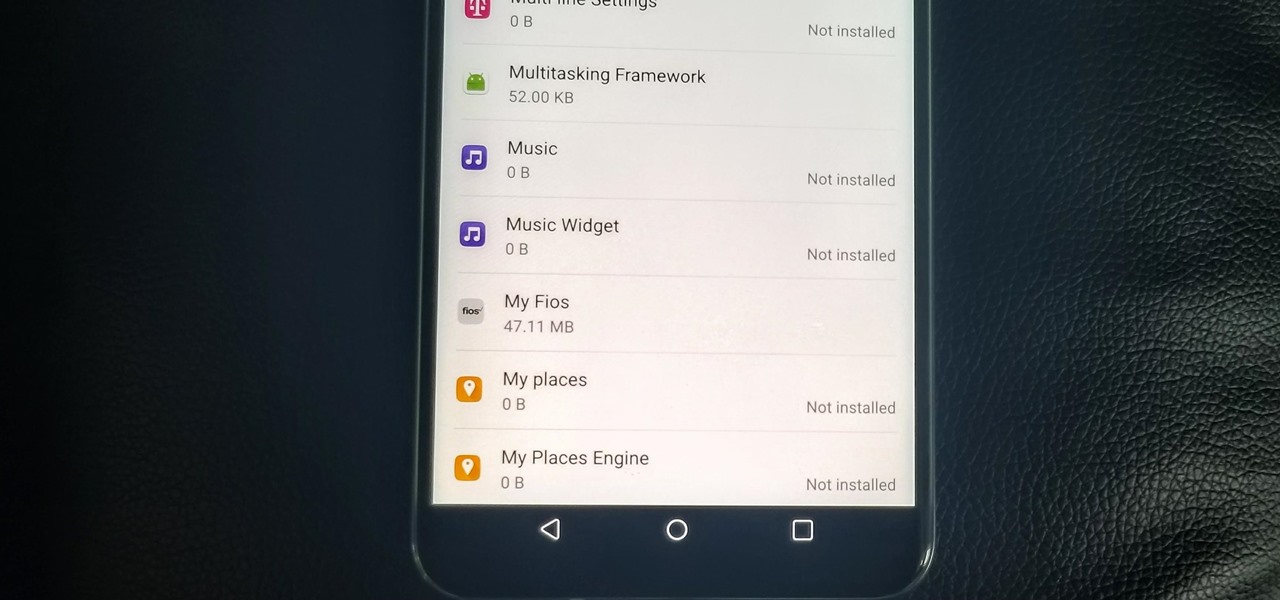
With the V30, LG has really delivered an amazing smartphone that hits all the major features consumers want. Amazing camera, beautiful edge-to-edge display, great battery life, water resistance, and smooth performance — there isn't much not to like about the LG V30. Unfortunately, it does suffer from heavy bloatware thanks to the carriers. The good thing is, unlike in the past, you are not stuck with it.
This is for those using Kali Linux 2.0 that need to edit the CRDA values to get the increase in Txpower

These cinnamon buns baked in orange peels are one of the easiest, cutest, and tastiest treats you can make for breakfast, a sweet snack, or dessert. Whether you bake them in the oven or grill them over a campfire, the orange peels infuse the cinnamon rolls with a fragrant, citrus-y flavor.

Apple released the new Mac OS X 10.10 Yosemite in the Mac App Store for everyone to download and install for free on October 16th, 2014, but downloading a 5+ GB file for each of your computers will take some serious time. The best thing to do is download it once and create a bootable install USB drive from the file for all of your Macs.

How can you tell if the pair of Ray-Ban Wayfarer sunglasses that you are about to buy online are not a fake? Follow these 9 simple steps to verify the authenticity of your purchase. Always ask the seller to use the youVerify app prior to purchase. It's Smarter Selling & Safer Shopping.

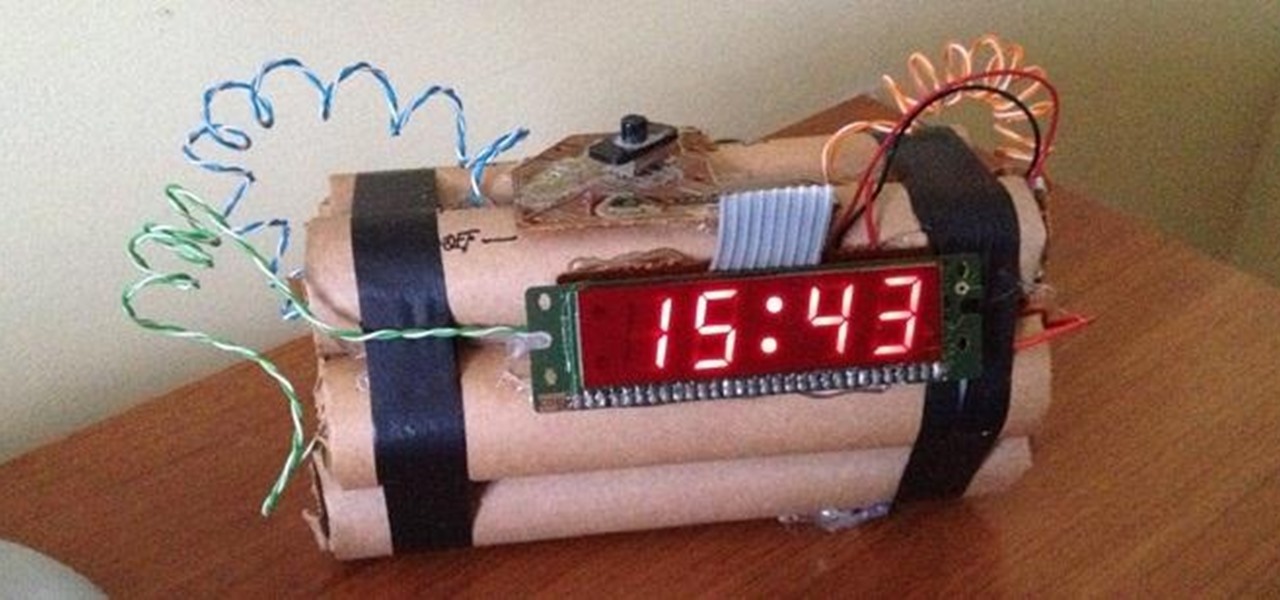
The first alarm clock in recorded history can be traced back to ancient Greek philosopher Plato, known for laying the foundations of Western philosophy and science. Plato was said to possess a very large water clock with an alarm signal similar to that of a water organ.

In the previous article, we learned how to set up our VPS, configure our PHP server, and developed an in-depth understanding of how the payload works. With all that taken care of, we can get into disguising our payload to appear as an image and crafting the note in the greeting card being delivered to our intended target.

Several years ago, I moved to Brooklyn, New York, just outside a Spanish neighborhood. It was here that I was introduced to chayote. Fast-forward to present day: I live in Los Angeles and buy several chayote squash a week to cook with—yes, I said several. It's so versatile and healthy! For the uninitiated, chayote (chai-YOH-tee) is a light green squash shaped like a pear originating from central Mexico. Although it's considered a fruit, chayote is a member of the Cucurbitaceous (gourd) family...

Tired of cleaning the stove and oven every time you cook? (It always gets so messy, doesn't it?) Well, there's one solution to keep the cleanup to a minimum, albeit a little unconventional, and that is to use your dishwasher!

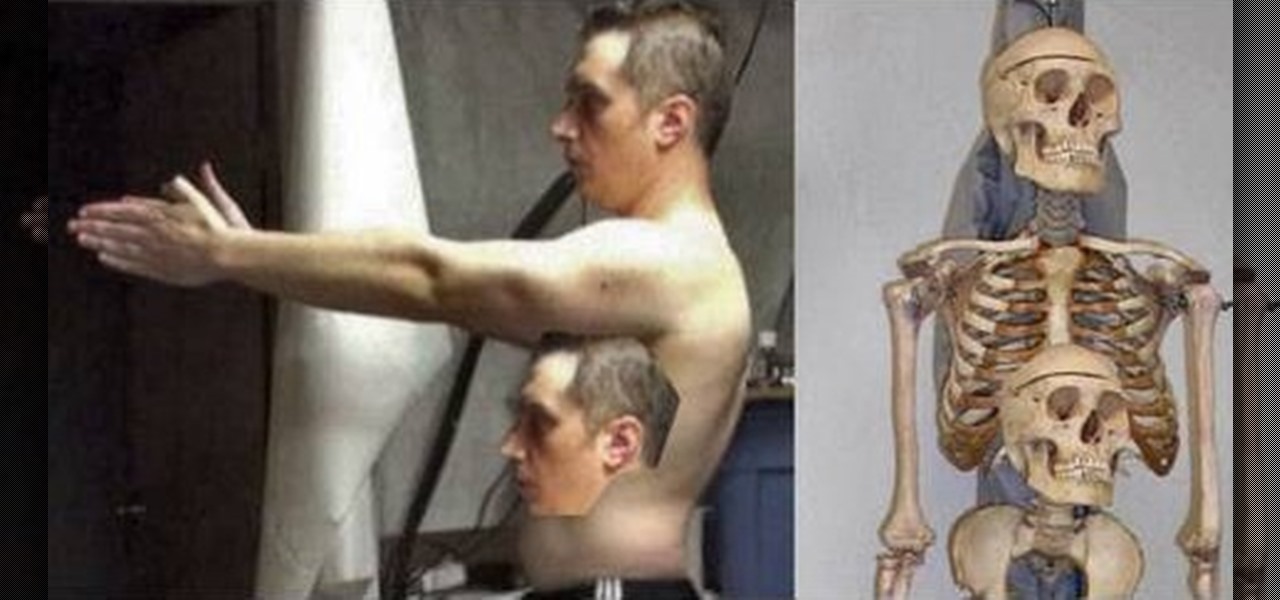
This is the ultimate guide to drawing correct human proportions. If you've always had trouble with it in high school art class or in art school, this video condenses all the information into a tight package that's fun and easy to understand. This will uncover all the tricks to human proportions for figure drawings.

Surprise your sweetheart this Valentines Day or any night, with a delicious Indian version of tiramisu. Tiramisu is traditionally an Italian dessert, and this is a similar recipe with an Indian twist. Why not give it a try? No one can resist the creamy deliciousness of fresh Tiramisu.

Tie dying a spider design on a t-shirt starts by folding the t-shirt in half vertically. Between one quarter and one half of the way down the shirt grab a piece of the shirt and spin around the table to create a coil of the shirt. Tie a string around the outside of the coil to make sure it stays in a disk. Set a rack on top of some type of basin that can catch liquid to work on the dyeing. Set the t-shirt coil on the clean rack. Take dye that has already been prepared in squirt tubes or syrin...

Chinese food is delicious, but it isn't very healthy and can be quite expensive. In this video, Betty adds a Southern touch to a traditional Asian dish and makes vegetables with a soy sauce gravy. The veggies are good for you and filling, and the gravy gives them a nice, hearty texture. Enjoy this dish anytime, and if veggies aren't enough for you - toss in some chicken or seafood, or even noodles and create your own delicious meal!

Coleslaw is always a nice sidedish, whether you are having a BBQ or a traditional dinner. In this video, Betty shows us a new variation on the traditional salad. This coleslaw recipe is fruity and sweet, instead of tangy and salty. You and your family will love this interesting new twist!

Pigs in a blanket are the perfect appetizer for any occasion. They are great snacks at Super Bowl parties, family functions or birthdays. They are easy to eat finger foods and with only 3 ingredients, require very little work or clean up! In this tutorial, Betty shows us how to make inexpensive pigs in a blanket with Vienna sausages. Enjoy!

Make spring rolls like a professional! Use pre-packaged purchased wrappers. Have some egg yolk ready. Apply some egg yolk on the edges of the wrapper, so that it can act like glue. Paint it on all 4 edges. You can use a brush for that. The filling is pre-prepared. It is a mixture of vegetables , cooked pork, and cooked shrimp. We will then add ginger and soy sauce to the filling. Take a small amount of filling, so that the spring rolls are thin, because that is how they are meant to be. Fold ...

Bake a red velvet cake whenever you want to serve a dessert that’s as beautiful as it is delicious. You Will Need:

Watch this video tutorial from the Polish Guy to see how to polish silverware using Cape Cod polishing cloths. In this polishing tip we polish silverware using Cap Cod Metal Polishing Cloths. The cloths are individually packaged in an attractive tin that includes a pair of reusable gloves and a buffing cloth.

Anytime you purchase a game for the Xbox 360, you know there's going to be achievements that need to be collected. That's true as well for one of their Xbox Live Arcade games, Hydro Thunder Hurricane. This racing game features explosions, boosts, and a whole lot of water.

It's been done for ages, but for most of us, "regift" entered our vocabulary after the 98th episode of Seinfeld—"The Label Maker." In this episode, Elaine calls Dr. Whatley (played by Bryan Cranston) a "regifter" after he gives Jerry a label maker—the same label maker that Elaine gave Whatley.

I may be a bit weird, but I enjoy listening to music at night as I fall asleep. Sure, you could create a playlist of songs so that it stopped after all the songs finished playing, but I have a rather extensive database of music and I enjoy listening to them randomly. Also, I like to ensure it terminates after a specific amount of time (I don't want it playing all night). Or sometimes I use it when I am cooking so that when the music stops, I know I need to check on my food, etc.

The competition to secure the top slot in the smartglasses space is now in full swing, with Facebook challenging Snap's Spectacles and Amazon's Echo Frames with its own collaboration with Ray-Ban called Stories.

Most packages sent to you via delivery services include a tracking number that allows you to track it from the creation of the shipping label all the way to your doorstep. The U.S. Postal Service includes tracking information with many of its mailing services, but not for first-class mail or periodicals. Luckily, there's a workaround to that limitation that you can set up pretty quickly.

Bloatware is a problem on Android, and it's not just a Samsung thing. Removing apps that have the Uninstall or Disable button grayed out in Settings has always involved sending ADB commands to your phone from a computer, which itself was always such a pain to set up. Thankfully, that has finally changed.

It's a common misconception that iPhones are impervious to cyberattacks and "more secure" than Android. And when an iPhone does get hacked, it's nearly impossible to tell that it happened.

Sniffing packets over a network is an easy way for hackers to gather information on a target without needing to do much work. But doing so can be risky if sniffing packets on an untrusted network because a payload within the packets being captured could be executed on your system. To prevent that, Sniffglue sandboxes packet sniffing to provide an extra layer of security.

Although the Magic Leap One: Creators Edition is currently officially available in only six US cities, those living outside of Magic Leap's designed US cities now have a roundabout way to order the device.

Web application vulnerabilities are one of the most crucial points of consideration in any penetration test or security evaluation. While some security areas require a home network or computer for testing, creating a test website to learn web app security requires a slightly different approach. For a safe environment to learn about web app hacking, the OWASP Juice Shop can help.

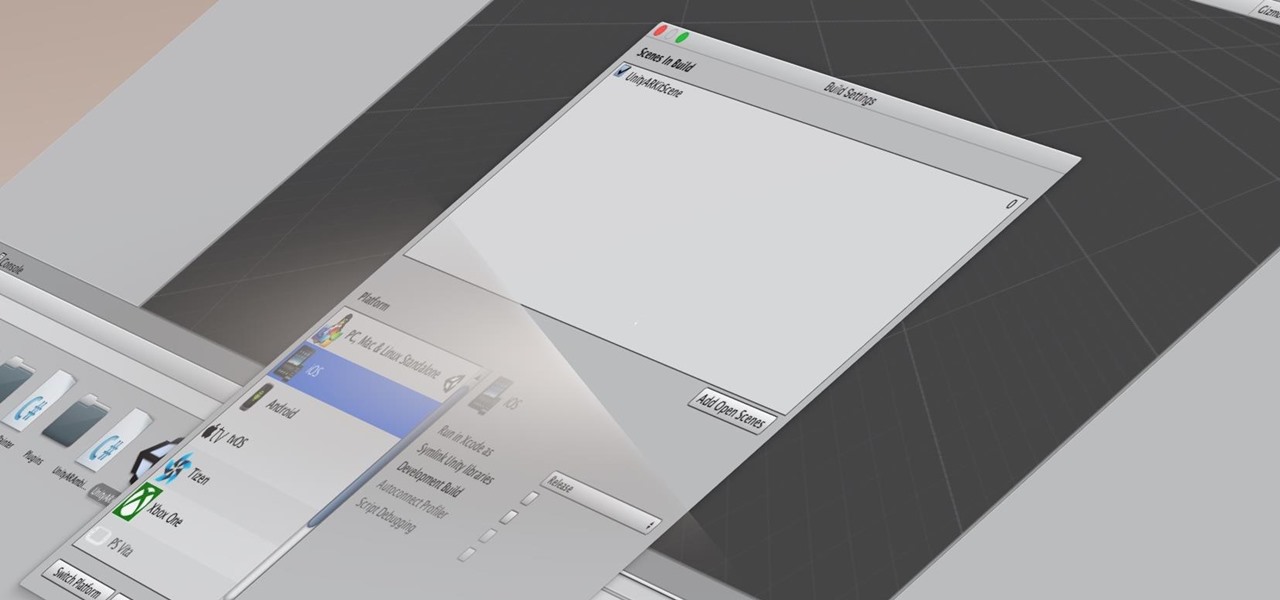
Whether you're a veteran augmented reality developer looking for a quick access point to add a new platform to your arsenal or just getting started with your first AR head-mounted display, get ready to start developing for the Meta 2.

In 2013, Offensive Security released Kali Linux, a rebuild of BackTrack Linux derived from Debian. Since then, Kali has gone on to become somewhat of a standard for penetration testing. It comes preconfigured with a collection of tools accessible by a menu system, tied together with the Gnome desktop environment. However, Kali Linux isn't the only penetration-testing distribution available.

Many developers, myself included, use Unity for 3D application development as well as making games. There are many that mistakenly believe Unity to be a game engine. And that, of course, is how it started. But we now live in a world where our applications have a new level of depth.

In this tutorial I am going to show you how to create an undetectable Meterpreter Trojan using a Domain name. I have taken a few guides/tutorials and built it into one. The first part is creating the DNS Payload. The second part is creating the Executable file. Part 3 is using both in Shellter to create your undetectable Trojan. Part 4 is setting up your listener using Armitage.

When to throw meat away is a common question, and one I often ask when faced with meat sitting in the fridge after a few days. With vegetables, you can usually tell on sight (or with this guide) when they're past due, but meat is not as simple.

The buttery scent of crescent rolls bring me back to my childhood, but those tubes that open with such a satisfying pop are more than just retro reminders. Crescent rolls can morph and serve as the base for hundreds of creative and cool dishes.
This how-to is for everybody who faced the problem of intercepting personal data sending through the Internet and is looking for fast and secure method to protect his activity in the global network.