MouseJack vulnerabilities were disclosed over three years ago. Some wireless keyboard manufacturers have since issued firmware updates, but millions (if not billions) of keyboards remain unpatched worldwide, either because they can't be updated or because the manufacturer never bothered to issue one.

NetBIOS is a service that allows for communication over a network and is often used to join a domain and legacy applications. It is an older technology but still used in some environments today. Since it is an unsecured protocol, it can often be a good starting point when attacking a network. Scanning for NetBIOS shares with NBTScan and the Nmap Scripting Engine is a good way to begin.

Popping a shell is often the main goal of a hacker, and it can be exciting when executed properly, but sometimes they do have their limitations. Metasploit's Meterpreter probably needs no introduction, but this powerful, dynamic payload can offer a leg up over normal shells. To prove it, we'll show how to take a normal command shell and elevate it to a Meterpreter session.
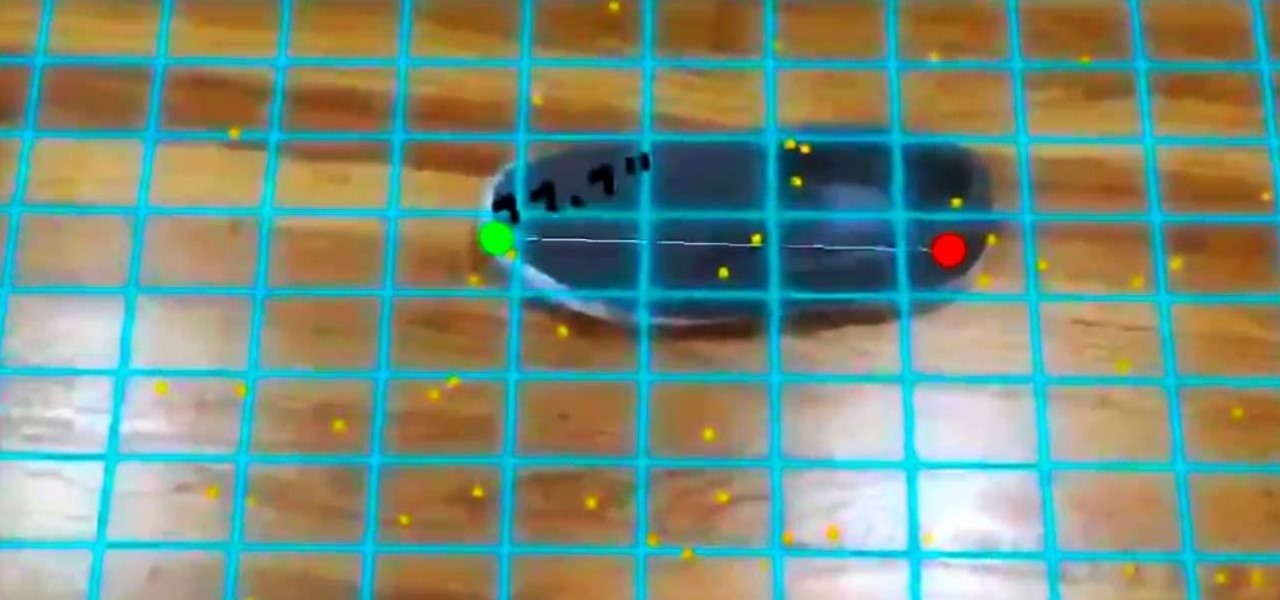
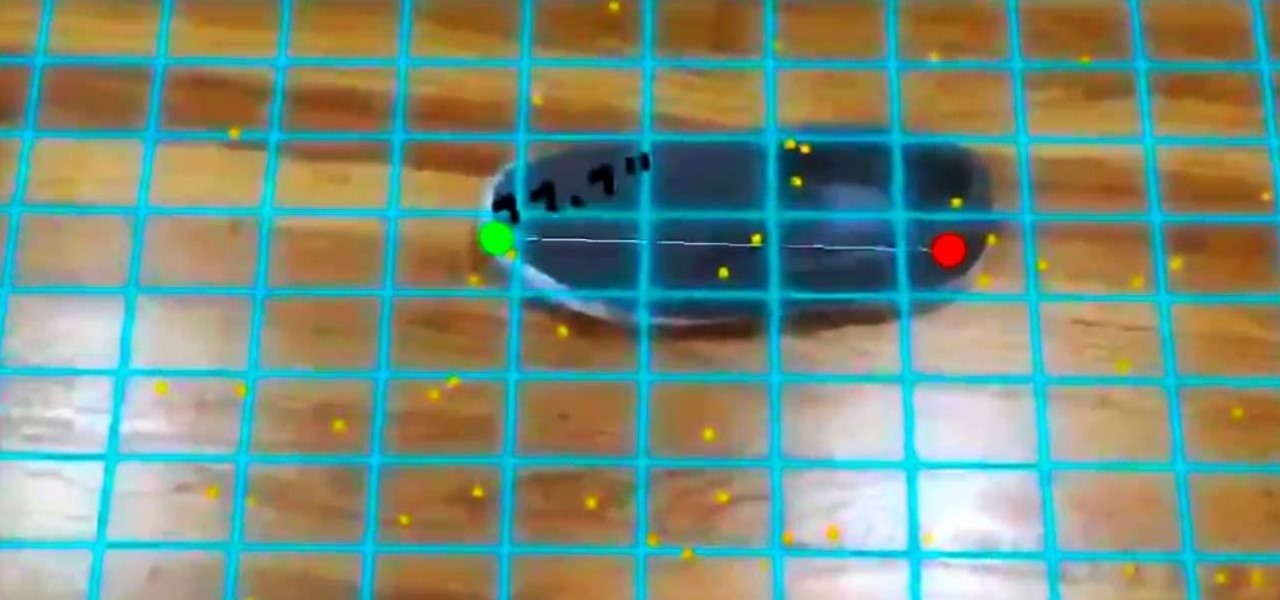
In our last ARKit tutorial, we learned how to measure the sizes of horizontal planes. It was a helpful entryway into the arena of determining spatial relationships with real world spaces versus virtual objects and experiences.

While hackers have taken advantage of numerous vulnerabilities in Adobe's products to deliver payloads to Windows users via PDF files, a malicious PDF file can also wreak havoc on a Mac that's using the default Preview app. So think twice before double-clicking a PDF open on your MacBook — it might just be a Trojan with a rootkit inside.

Know thy enemy — wise words that can be applied to many different situations, including database hacking. It is essential to performing adequate reconnaissance on a system before even thinking about launching an attack — any type of attack — and this is no different for SQL injection.

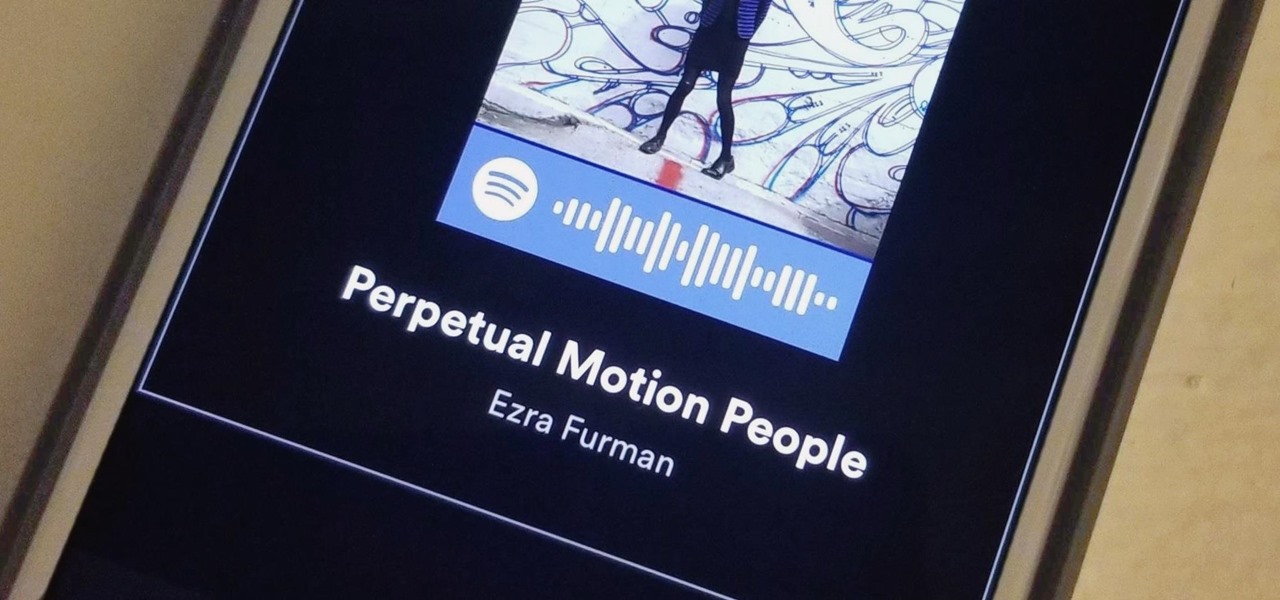
If you're anything like me, when you first find a good song, album, or playlist on Spotify, your initial reaction may be to share it with your family and friends. While there are the usual share methods available in Spotify that are available in other streaming music services such as Apple Music and Google Play Music, Spotify goes one step further with QR-like codes users can easily scan.

A massive leak appeared the web today, and it's got some huge security implications for every iPhone on the market. On the plus side, it also has some potential for enabling deep-level modifications and jailbreak tweaks.

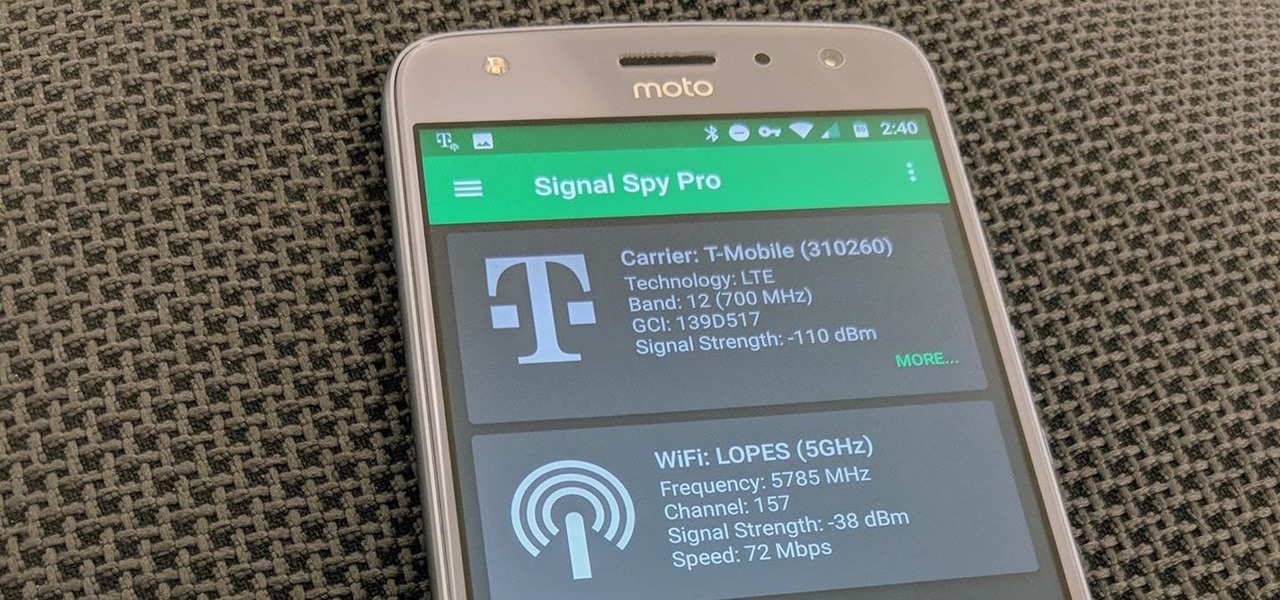
If you own a Pixel or Nexus device, Project Fi is a great alternative for cellular service outside of the four major US carriers. Project Fi is a Google-managed MVNO, providing service primarily through the T-Mobile and Sprint networks. One of the biggest mysteries on Fi is which network you're connected to at any given time, but there's a simple solution.

Open your Spotify app, search for an artist, view its "Spotify Code," and display it to that friend lurking over your shoulder. Sound familiar? Probably not ... yet.

This is a little c++ program that I thought would be handy in the future. Although, I apologize in advance for any errors in the code since I haven't had the chance to compile it yet. Anyway, please if you are a script kiddie please do me a favor and at least read this article fully. :)

In this article, we will explore the basics of radare2, a powerful package that comes with Kali. We are going to write a simple program, and then disassemble it, to see what is really doing in the processor.

April Fools may be over, but any day is a good day to prank someone, and the best time to do it is when everyone's eyes are glued to the television.

For over 20 years, a tiny but mighty tool has been used by hackers for a wide range of activities. Although well known in hacking circles, Netcat is virtually unknown outside. It's so simple, powerful, and useful that many people within the IT community refer to it as the "Swiss Army knife of hacking tools." We'll look at the capabilities of Netcat and how the aspiring hacker can use it.

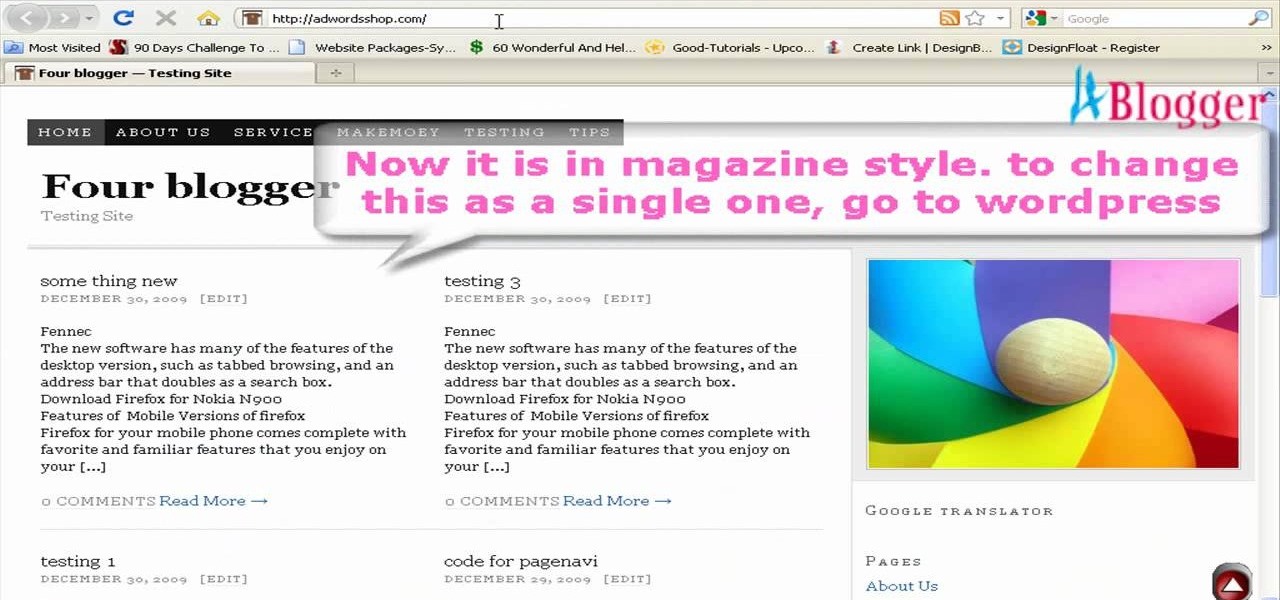
First go to your Wordpress admin and click the "custom file editor" in thesis options. Now copy that code which is showing in the video and paste it in the custom.css file and click on the big green save button. Now select

Unlock cheat codes on Guitar Hero III (3).

No downloads or extra programs needed! This video is pure cheat codes, all for playing on Poptropica! You can do fun things like change your skin color, change your hair color and even get the elusive pumpkin hat to wear!

This tutorial for PHP beginners introduces the viewer to the concept of class inheritance. As your coding career takes off, you'll need to know as many ways to work efficently and code with speed to save time and money. Check it!

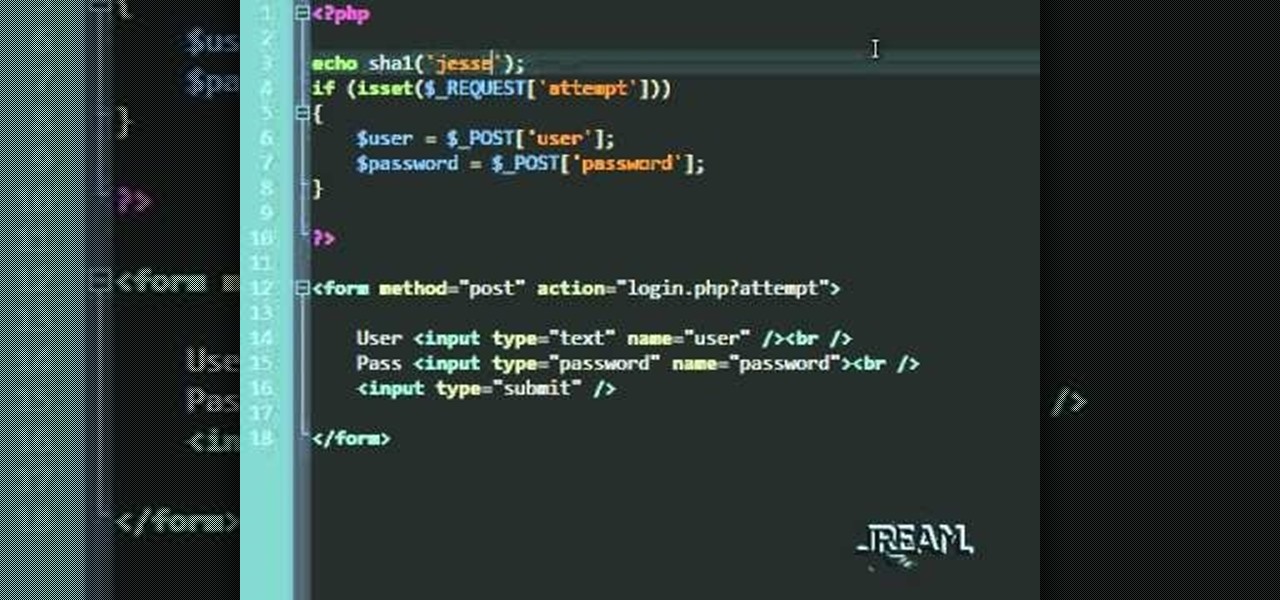
In this tutorial you'll learn about a simple PHP login script that serves to check your MySQL database against a user/password. The code in this video is a quick and dirty procedural code, but it's enough to get you going so you can try it out yourself.

A snippet is a piece of code which you may want to repeatedly use (like a login code). Snippets can also be global, which you can apply to every website you have. This tutorial shows you how to store and use snippets in Dreamweaver.

After running a diagnostics test on a 2002 Jeep Liberty, if you get the code P0442, that means you have an Evaporative Emission Control System (EVAP) leak detected, which is just a small leak, but a leak nonetheless. This video will show you how to smoke test the EVAP leak to find the problem spot inside the vehicle.

If you didn't find the solution to your misfire problem in this video, then the 1999 Mercury Villager 3.3L might have a code P0305 (Cylinder #5 Misfire). This is great troubleshooting advice from a professional mechanic to help you diagnose the problem. The vehicle is a '99 Mercury Village, 3.3L, with 150,000 miles on it. The chief complaint is the CEL (check engine light) comes on and it runs like it has a misfire. It feels like a steady consistent misfire, which is code P0305. Watch the vid...

In this tutorial, we learn how to fix error code 86420 and change your NAT type to open. First, go to the website to change the settings for your Linksys router. Next, go to the applications tab that says "applications and gaming". After this, go to port range forwarding, then write in a name next to where it says "application name". Under "start" write the number 1 and under "end" write 6553, then keep "both" marked under protocol. Next, enter in the last 3 digits of your console's IP addres...

Are you a big fan of Japanese anime series, Code Geass? Learn how to draw the main character, Lelouch, from the series with help from Drawing Now. Search WonderHowTo for more videos from Drawing Now to learn how to draw a variety of characters and cartoons!

Google G1 users, want to switch your phone network? In this video, learn how to unlock the Google G1 HTC Dream Phone. All you need to complete this tutorial is your phone and a SIM network unlock pin code.

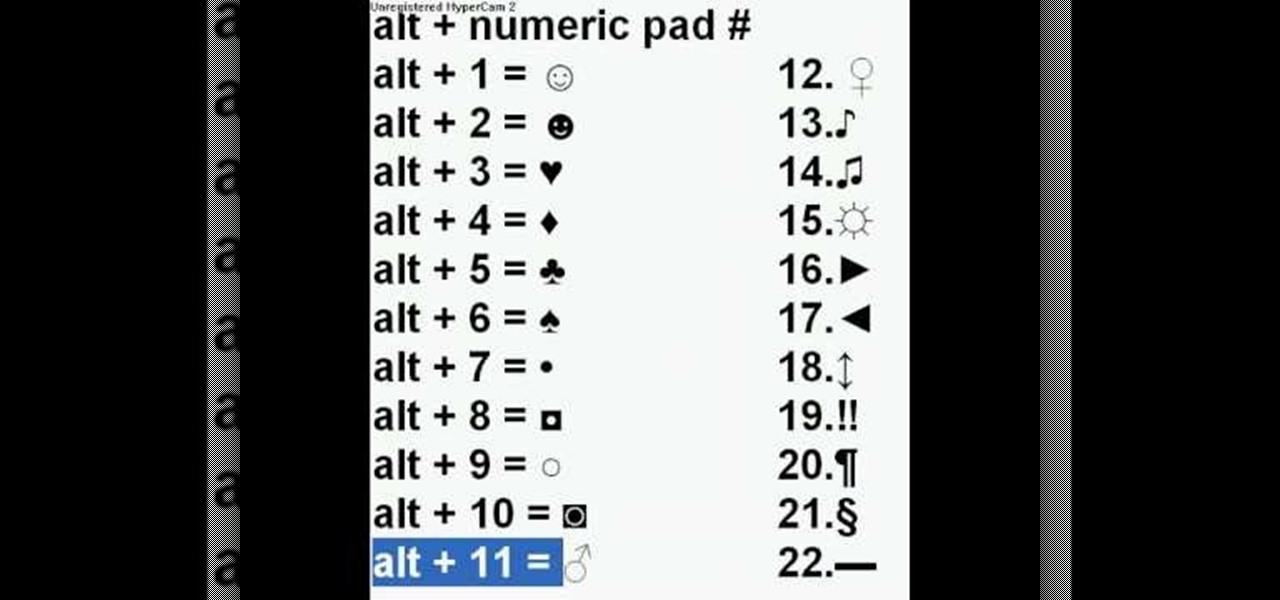
It is possible to add a little extra personality and ting to your facebook, myspace, or most any messaging system online by adding characters such as hearts, smiley faces and many more. With this video you will see the simple alt codes you can use to personalize your messages by pressing alt + a number.

In this how-to video, you will learn how to embed a social or fund raising widget on to your Facebook page. Look for static fbml on the Facebook search function. Click on it and add to page. Next, press add static fbml. Now you are finished. Go to edit page and click edit on the application. Now you can embed whichever code you need to paste into your Facebook page. Do not worry about what the code does, as you do not need to know it in order for it to work. Save the changes and go back to th...

Please permit us, dear player, to expand your dim view. See how Bakersburg suffered thanks to P.B. (and you)! Get the solution to the "Busted Cretin" puzzle in The Misadventures of PB Winterbottom.

If you're a Visual [blank] programmer heretofore intimidated by the thought of programming for the Linux operating system, take heart: this video tutorial will teach you how to visually code GUI applications with Ruby and Glade.

Before SOAP and REST, there were Remote Procedure Calls. Ruby on Rails ships with native RPC support and this screencast programming tutorial will show you how to build powerful remote API queries with 3 lines of Ruby on Rails code!

In this video tutorial, Keith Code walks you through how to set the sag on your motorcycle's suspension. If your sag is too loose or too tight, you can damage your bike and potentially damage yourself. Watch this video to become a pro at setting up your motorcycle.

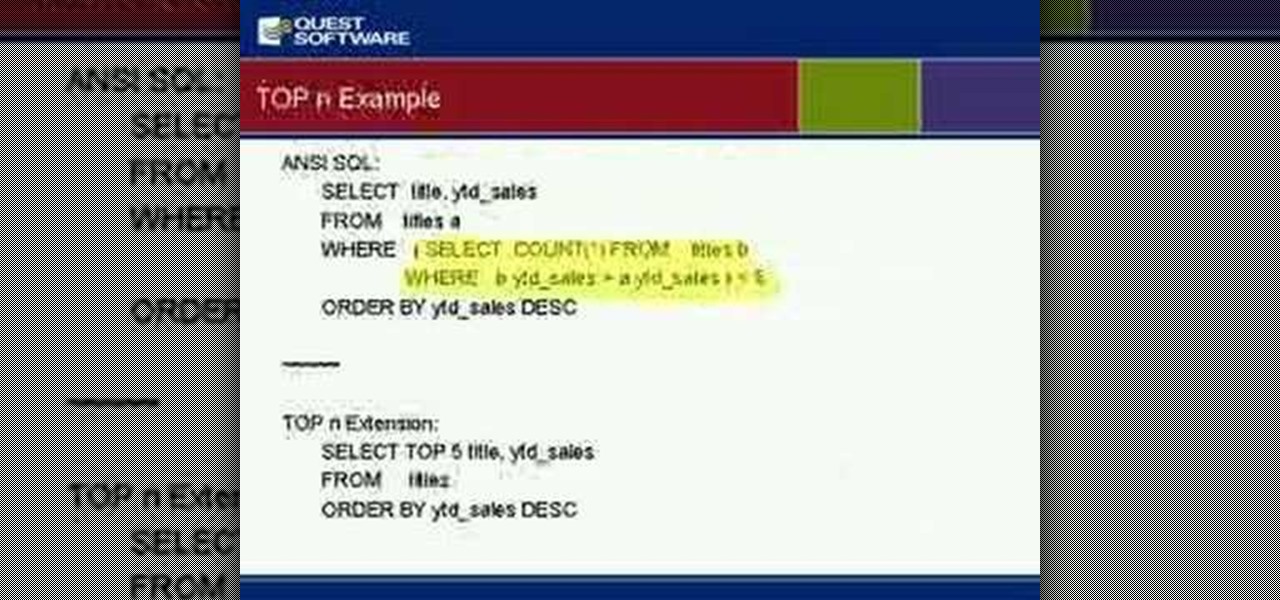
Gain insight into best practices for SQL Server optimization and ways to alleviate many root causes that can impact performance of your SQL Server database. Kevin also will discuss how to manage for planned and unplanned changes, speed time to implementation of your applications and ensure that your databases are running as they should.

Post-exploitation is often not quite as exciting as popping the initial shell, but it's a crucial phase for gathering data and further privilege escalation. Once a target is compromised, there's a lot of information to find and sift through. Luckily, there are tools available that can make the process easy. One such tool is Postenum.

Whether you miss the good old days of Telnet or you want to know what hacking was like when security was nothing but an afterthought, Telehack is the game for you. The text-based hacking game is a simulation of a stylized combination of ARPANET and Usenet, circa 1985 to 1990, with a full multi-user universe and player interactions, including 26,600 hosts.

With the Wigle WiFi app running on an Android phone, a hacker can discover and map any nearby network, including those created by printers and other insecure devices. The default tools to analyze the resulting data can fall short of what a hacker needs, but by importing wardriving data into Jupyter Notebook, we can map all Wi-Fi devices we encounter and slice through the data with ease.

Determining the antivirus and firewall software installed on a Windows computer is crucial to an attacker preparing to create a targeted stager or payload. With covert deep packet inspection, that information is easily identified.

Samba can be configured to allow any user with write access the ability to create a link to the root filesystem. Once an attacker has this level of access, it's only a matter of time before the system gets owned. Although this configuration isn't that common in the wild, it does happen, and Metasploit has a module to easily exploit this security flaw.

SMB (Server Message Block) is a protocol that allows resources on the same network to share files, browse the network, and print over the network. It was initially used on Windows, but Unix systems can use SMB through Samba. Today, we will be using a tool called Enum4linux to extract information from a target, as well as smbclient to connect to an SMB share and transfer files.

KeePassX, 1Password, and LastPass are effective against keyloggers, phishing, and database breaches, but passwords managers rely on the operating system's clipboard to securely move credentials from the password vault to the web browser. It's within these few seconds that an attacker can dump the clipboard contents and exfiltrate passwords.

Apple's Gatekeeper security software for macOS (Mac OS X) is vulnerable to remote attacks up to version 10.14.5. An attacker that's anywhere in the world can exploit MacBooks and other Mac computers by sharing a single ZIP file.