
How To: Download and Install the Minecraft 1.8 Pre-Release
Update 2: 1.9 Version3 is currently out. Click here to download and install 1.9 Version 3. Update: 1.8 is now officially out! It'll prompt you to update the next time you launch.


Update 2: 1.9 Version3 is currently out. Click here to download and install 1.9 Version 3. Update: 1.8 is now officially out! It'll prompt you to update the next time you launch.

Hey now! Brazil, Paraguay, Chile, Argentina and Uruguay are doing very well in their respective groups. The are all expected to qualify to the final 16. In fact, they are doing better than any other continent. Europe's top flight teams are disappointing, as are the host African nations.

In this Adobe Acrobat video tutorial you will learn how to use the Rubber Stamp Tool. You use the Stamp tool in Acrobat 5 to apply a stamp to an Adobe PDF document in much the same way you would use a rubber stamp on a paper document. In addition to the standard stamps offered, dynamic stamps obtain information from your system and from the Identity panel of the Preferences dialog box, allowing you to indicate name, date, and time information on the stamp. Make sure to hit "play tutorial" in ...

Any talk about privacy is a complicated (usually) and touchy subject. In today's world, privacy is an ever eroding pleasure to be had. Numerous cases, like the monumental Kat'z vs United States, have been fought to hold on to this right.

Pranks are fun, but finding a way to maximize the affect of a prank can be tricky. Toilet papering the whole campus or repainting all of the parking spaces slightly smaller can take a long time and a lot of resources. A better plan of attack is to booby trap the choke points where your victims are forced to pass through. Think like a guerrilla. A dorm doorway is a good idea.

In my recent Darknet series, I attempted to connect the dots on the Deep Web. I covered the two largest anonymity networks on the Internet today, Tor and I2P. While my initial four articles were meant as an introduction, I ended up receiving a lot of interesting comments and messages asking the technical differences between the two. I'd like to thank all of you for letting me know what was on your minds, as you should always!

We had a blast during last week's social engineering calls. One of our attending social engineers was so clever that she convinced several people on Craigslist that lost items were hers, even if it seemed she couldn't be trusted. But females are better social engineers, naturally. Some say that females have a special knack for manipulating men, but I think that's preposterous. I can't see why that would be true in a million years (note my sarcasm).

I'm sure we've all heard about MSN and Yahoo! Messenger, right? They can be useful, but the setup can be quite time consuming for those who need to use it just once or twice—and the privacy statements are a real bother. For example, we must provide our real details. You could use Fake Name Generator, but if you get caught, you will have your account suspended. I don't have a law degree, but to my understanding the United States recently passed legislation that gives the authorities the power ...

Increasingly, I'm turning to Google+ as a source of news, and it looks like I'm not the only one. On Thursday, news of a small earthquake broke on both Twitter and Google+. One curious user, +Keith Barrett, decided to try and find out which social network was faster with the news. Turns out it was a tie. As Google integrates Google+ more closely with the rest of its services, and more users post relevant stories, I think we'll start to see Google+ as a place that can create and break stories,...

Four years ago Mind Candy was a pretty small game company. They were best known for their revolutionary but short lived ARG Perplex City, and had no other successful franchises to fall back on when that ended. Their plan to save it? Start a free online social game for children ages 7-12 called Moshi Monsters, where kids can create monster pets, raise them, and socialize with one another in a controlled, safe environment.

Video games were blamed in the death of Chris Staniforth last May, but now things have gotten worse as video games take the blame for a more recent tragedy...

Some cops already have the ability to extract data from your cell phone using handheld forensic devices, but soon police officers will have a new mobile data collection toy to play with—an Apple iPhone. Actually, it's an iPhone-based device that connects directly to the back of an iPhone, which is designed to give law enforcement an accurate and immediate identification of a suspect based on their facial features, fingerprints and even their eyes.

Last week, we discussed whether Google should require you to use your real name for Google+ profiles. Google is working on eliminating fake profiles, and in the process, they've booted some real people, including actor +William Shatner. If you find out that your Google+ account has been suspended, you can appeal the suspension and get your profile reinstated.

The debate over whether video games can be considered art or not has intensified in recent years as games like Braid and Flow have taken the digital aesthetic experience to new heights. These new games are great examples, but there are much older ones that present compelling arguments as well. The best is a 1986 ZX Spectrum/Commodore 64/Amstrad CPC game called Frankie Goes To Hollywood.

Artist Austin Houldsworth of the UK has come up with a device that drastically speeds up the process of fossilisation. Entitled Two Million & 1AD, Houldsworth is capable of creating a fossil in a few months (which otherwise might require thousands of years). Houldsworth is currently experimenting with objects such as a pineapple and phesant, but ultimately hopes to fossilize a human. Houldsworth proposes:

Now that I am jumping full swing into WonderHowTo Worlds here... I can see why this is platform is much better for socializing... With Facebook, you might as well flash your naked self for all to see, because there isn't much left to know about you.

Over the past couple of weeks, there have been a series of high-profile hacks and leaks. From the rooting of CombinedSystems, to a secret FBI conference call leak, all the way to the distributed denial-of-service (DDoS) attacks on U.S. government sites—with a lot in-between. As governments move to close their long fingers around the free speech that exposes their secrets, this shadowy collective of loose-knit, but like-minded individuals are hell bent on preventing them. Or are they?

We've talked about the deep web before, but we never really covered the details of what's out there. It occurred to me that a nice list of resources would be very helpful to all of you anons out there. Think of this like a helpful brochure to the hidden web.

Previously, we talked about how to secure Firefox. Today, we will talk about securing a Chromium based Browser. Why? Because Chrome recently beat Firefox in holding more customers.

This Null Byte is the first part in a mini-series on the art of Social Engineering. I will be teaching you how to effectively defend yourself against it.

After the launch of Google+ and its ensuing attendant fanfare and rave reviews, Facebook seemed to undergo an identity crisis. On July 6th, Facebook failed to make waves with its "awesome" announcement - the new group chat and video chat features felt lame in comparison to the Google+ hangout and huddle features. Facebook also faced ongoing criticism for its perceived lack of privacy controls. Over on Quora, workers confirmed a lockdown of sorts at Facebook, for employees to work harder on fe...

I've decided to write this post so some of the fledgling street artists who may or may not follow this world in the future are informed about two things in the urban art world that are either not discussed at all, or distorted (intentionally or otherwise) to the point of misinformation. Those two things are, as the title says, the dangers of street art, and the morals of street art.

Choosing a nanny or au pair for your children is a process that should be organized and performed carefully, to ensure you find someone who can be trusted, will contribute significantly to the development of your child and integrate well into your family.

With FarmVille being one of the hottest Facebook games on the market, it's no wonder it's the primary target for scams and virus downloads. Anyone playing FarmVille is at risk, but the primary targets are those looking to improve their gameplay and build their farms and neighbors up. These "farmers" are the ones seeking quick hacks and cheats.
Minecraft is not just a game. It is a creative tool. Over the past year and a half countless epic builds, servers, and community projects have been undertaken. I'm sure some of you have seen the one-to-one scale recreation of the Starship Enterprise from Star Trek or the epic server Godcraft. Countless projects such as these are being worked on as we speak, and they serve to inspire us all.

Culinary collective Studiofeast is known for thinking outside the box, especially when it comes to food. They've hosted inventive and spectacular events like the L Train Lunch, where a high-end meal was served to guests on a moving train, and the Datalicious Last Supper, where results from a survey of people's desired "last meals" informed the menu.

If you follow the Anonymous, Occupy, and IT security scenes, you have no doubt heard about a dox release. What is it? How can it hurt you? And most importantly, how can you protect yourself from it? Some of these steps might seem common sense, while others will be an ah-ha! moment. Your private info is both your biggest weakness and your biggest weapon in your battle to remain anonymous. You must learn how to use it as both.

Anonymity is something that doesn't exist today. Everything you do in the world is tracked, from the purchases you make to surfing the internet—even taking pictures on your iPhone. Everything you have ever said and done on the internet is still there—somewhere. This is called caching. For example, when a site is down, you can view its cached page on Google.

I have had a lot of people ask me, "How does my neighbor keep getting into my wireless?!". Chances are, these people are all using WEP, a deprecated wireless encryption protocol. Either that, or you are using one weak WPA passphrase.
Night People: A Bad Vibes Label Profile

After the media outcry of Google Buzz's privacy issues, Google has set its goals on making the privacy parameters of Google+ simple to learn and as explicitly manageable as possible. No small feat.
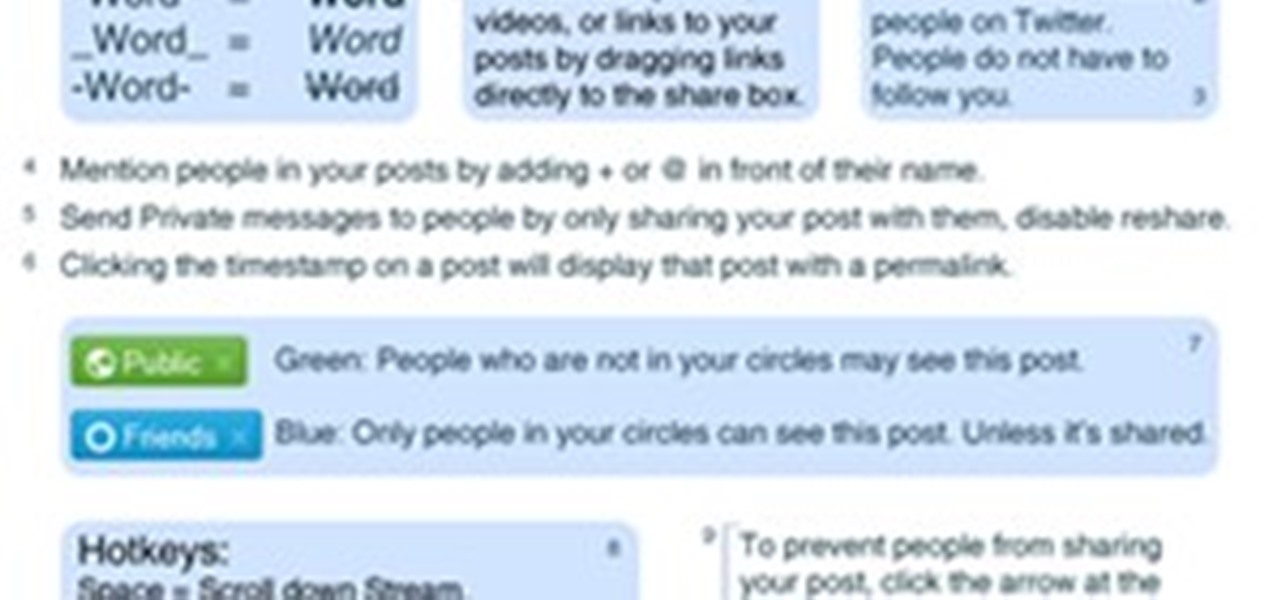
With the Google+ team members being generous and free-flowing with advice on some of the more advanced features of Google+, we'll be publishing a weekly summary of the latest pro tips. Chances are, if you've been following the Google+ team members, you've seen some of these already but you don't have them all in one handy place.

Anonymity is very important to many internet users. By having your "e-identity" exposed online, you can be stuck with a number of unwanted issues, such as:

I want to write this article because in my childhood, I had experienced internet stalking which ultimately ended in physical stalking which then lead to several attempted abductions. I have now learned how to use the internet safely, who to communicate with and I've learned how stalkers work.

By Ethical Traveler As the world becomes ever more interconnected, being an ethical traveler becomes both easier and more urgent. Travelers today have access to far more information than we did even 10 years ago. We can observe–almost in real time–the impact that smart or selfish choices, by governments and individuals, have on rainforests and reefs, cultures and communities.