Koadic allows hackers to monitor and control exploited Windows systems remotely. The tool facilitates remote access to Windows devices via the Windows Script Host, working with practically every version of Windows. Koadic is capable of sitting entirely in memory to evade detection and is able to cryptographically secure its own web command-and-control communications.
This video illustrates the method of using Facebook smileys. The process is composed of the following steps -Step 1While typing a wall post or a message in Facebook , click on the smiley button present in the top right corner of the text box where are typing your text.Step 2You will be presented with a drop down menu with the smileys that can be used in Facebook. Select anyone of them and insert them in your post by right clicking on it.Step 3You can add any number of smileys by following the...

Speed up your Nuke 5 workflow with the handy key commands dmeonstrated in this clip. Whether you're new to the Foundry's popular node-based compositing application or a seasoned post-production professional just looking to better acquaint yourself with Nuke 5's new features, you're sure to be well served by this video tutorial. For more information, including a detailed overview, watch this free video guide.
Watch this video to learn a simple cheat that will make your paper longer. Good trick to know when you are in a crunch and need to stretch your class paper. You will need to use your existing term paper and either Microsoft Word or Open Office to use the Find&Replace command. Here's some forums you can post anonymously with other like-minded, less scrupulous people: http://academicdishonesty.net

Welcome back, my neophyte hackers! Metasploit is such a powerful tool that I can only scratch the surface of its capabilities here. As it has developed over the years, it is now possible to use Metasploit for nearly everything from recon to post exploitation to covering your tracks. Given its versatility, every aspiring hacker should have at least a tentative grasp of Metasploit.

So you've managed to get a shell on the target, but you only have measly low-level privileges. Now what? Privilege escalation is a vast field and can be one of the most rewarding yet frustrating phases of an attack. We could go the manual route, but like always, Metasploit makes it easy to perform local privilege escalation and get root with its exploit suggester module.

Hi guys. I'm here to go for level 7 now lets get it start but i apologize u all that i posted this very late but now lets rock:

Most users don't realize how much valuable data is in their network traffic. With a few simple tools, an attacker can quickly pick out cookies, passwords, and DNS queries from a macOS device as it covertly streams the victim's network traffic to the attacker's system. Here, we will cover two methods for analyzing packets flowing from a Mac.

Hello all! In this tutorial, I'd like to show you one way of getting root on OS X. Check out this GitHub page for a recent privilege escalation exploit that was recently discovered. I've tested it and it works on both OS X 10.9 Mavericks and OS X 10.10 Yosemite, but appears to have been patched with OS X 10.11 El Capitan. If you check out the file main.m you can see where most of the magic is happening. This source code can very easily be changed to make it do more than just the system("/bin/...

No operating system is stricken with as many vulnerabilities as Windows, and it's often a race to release the latest patches to fix things. From an attacker's point of view, knowing which patches are present on a Windows machine can make or break successful exploitation. Today, we will be covering three methods of patch enumeration, using Metasploit, WMIC, and Windows Exploit Suggester.

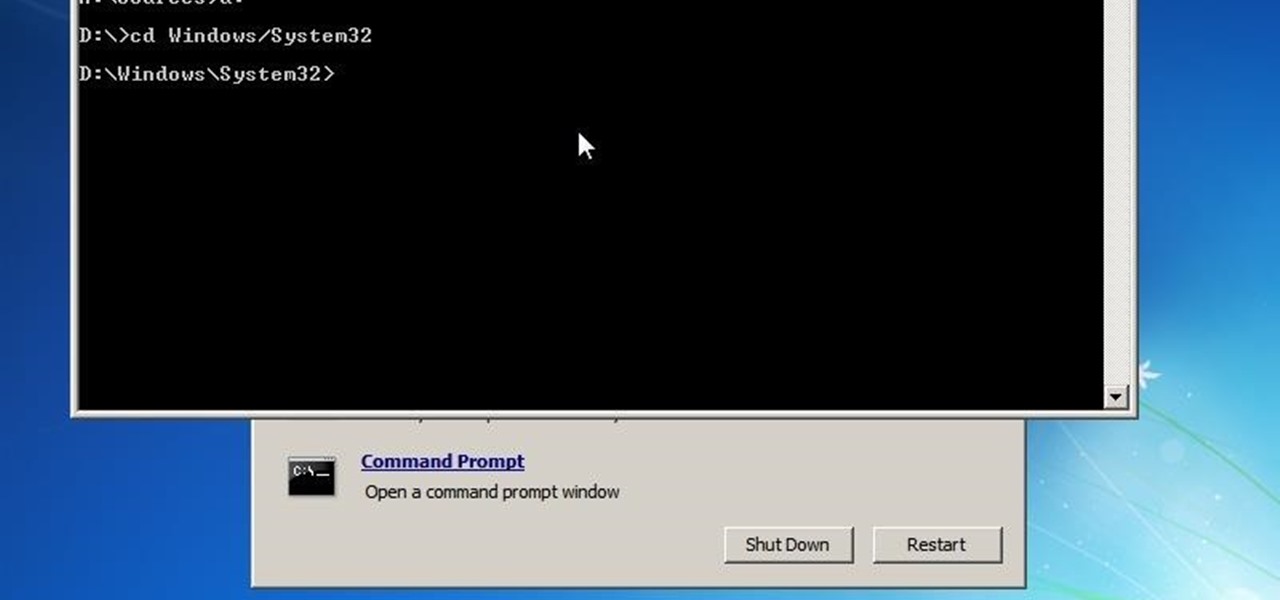
In this tutorial, we learn how to run a command prompt as administrator (Vista or 7). First, you will click on the start menu, then search for the term "prompt". Launch the command prompt, then a window will pop up with a black window. Type something in to see if it tells you the operation needs elevation. Now, click the start menu and type in "prompt" again. Then, click on the command link, right click, then click "run as administrator". Now, the new window will pop up that says "administrat...

File permissions can get tricky on Linux and can be a valuable avenue of attack during privilege escalation if things aren't configured correctly. SUID binaries can often be an easy path to root, but sifting through all of the defaults can be a massive waste of time. Luckily, there's a simple script that can sort things out for us.

Hello! This is my first post on this awesome website! I know that Windows exploits are less common than the more advanced hacks, but I found something I deem pretty cool and figured why not share it with you all. Alright, enough about me, lets begin.

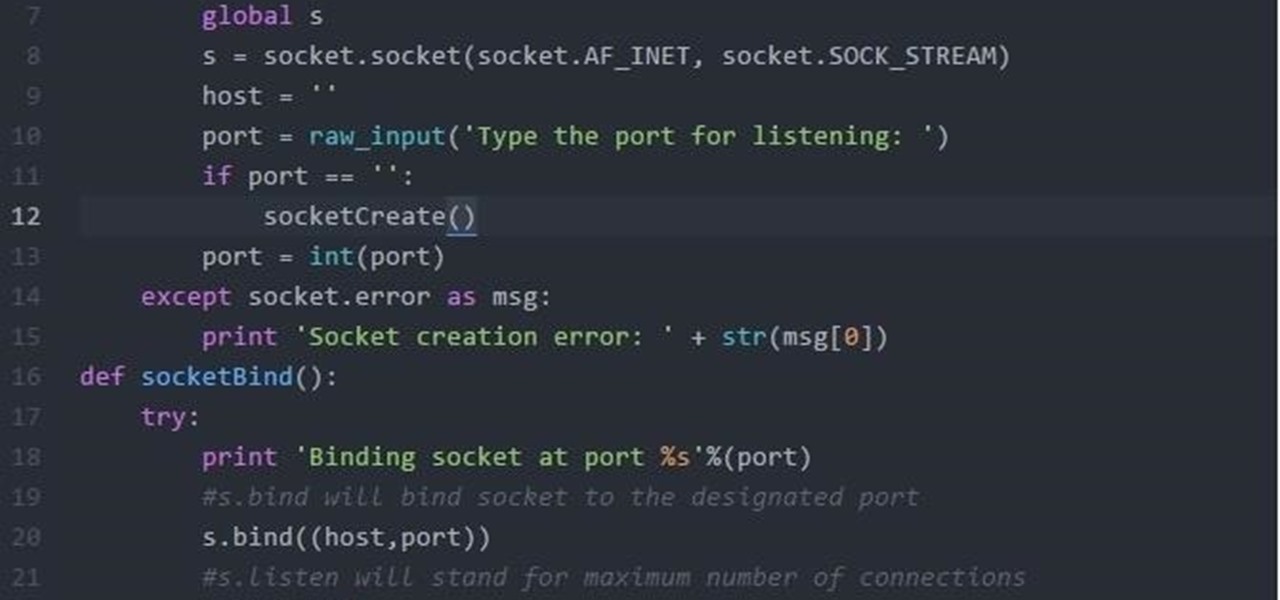
Hi Folks. This is my first post. I will teach how to create a server and client python reverse shell using sockets and python language. The script i'll post here is going to be very simple, and from here you'll have the possibility to adapt to your own purpose. For example, my original script can download files, upload files, make changes to registry, create user accounts and more. I'm sure you could do it on your own too.

There are many password-cracking tools out there, but one of the mainstays has always been John the Ripper. It's a powerful piece of software that can be configured and used in many different ways. Metasploit actually contains a little-known module version of JTR that can be used to quickly crack weak passwords, so let's explore it in an attempt to save precious time and effort.

Popping a shell is often the main goal of a hacker, and it can be exciting when executed properly, but sometimes they do have their limitations. Metasploit's Meterpreter probably needs no introduction, but this powerful, dynamic payload can offer a leg up over normal shells. To prove it, we'll show how to take a normal command shell and elevate it to a Meterpreter session.

Deleted bank statements and private photos are still within an attacker's grasp, so don't think that emptying your recycling bin is enough to keep your files from coming back to life. It's possible for a hacker to recover compromising files and images from a backdoored computer completely without the victim's knowledge.

Yes, I understand some people may consider this a repost. However, I have been searching for this answer for 3 weeks and after reading numerous reddit post, Kali Forums post and Null byte post I finally have gotten it to work for me. I would like to compile and share this information with you guys.

The ability to see the world around you and instantly share that "vision" is something that makes Google Glass great for everyday use. No reason to pull out your phone to show off the amazing sushi plate you were just served—look at it, give a couple of quick taps and voice commands, and boom, your social network is salivating in jealousy.

Passwords stored in web browsers like Google Chrome and Mozilla Firefox are a gold mine for hackers. An attacker with backdoor access to a compromised computer can easily dump and decrypt data stored in web browsers. So, you'll want to think twice before hitting "Save" next time you enter a new password.

Hello Guys, Today I have made a script for ddosing sites with VBScript! And I don't know how you guys do it, but I've made a script that refreshes the page in a chosen amout of milliseconds. And if you want it a number of times or if you want it to go on and on. And this is a script to run it on your botnet. But again I don't know if this works on your botnet too.

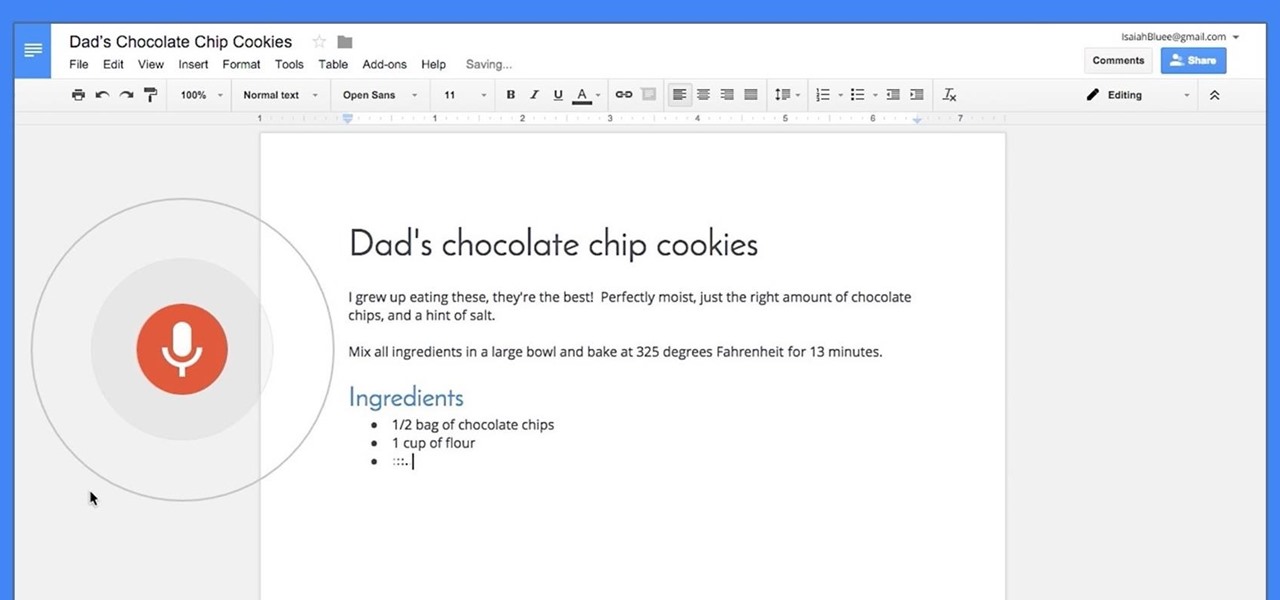
Google launched voice typing for Google Docs last Fall, and followed that up about six months later with voice commands that let you format and edit text as well. You can do things like select text, apply format settings like alignment and headings, and add and edit tables—all with your voice.

NOTICE: Ciuffy will be answering questions related to my articles on my behalf as I am very busy. Hope You Have Fun !!!

Welcome back, my rookie hackers! I recently began a series on using Metasploit, and my goal with it is to teach you the very basics the incredibly powerful hacking tool has to offer while progressively moving on to the more advanced features.

Welcome back, my tenderfoot hackers! I have written many tutorials on hacking using Metasploit, including leaving no evidence behind and exploring the inner architecture. Also, there are my Metasploit cheat sheets for commands and hacking scripts.

This video demonstrates how to open up the command line prompt and various commands which you can use to make your Windows experience easier. After clicking on the "Run" option from the start bar of Windows, you can then type "cmd" into the box, opening up the command prompt. The appearance of the command box can be changed by left clicking the small icon at the top left, going to properties, and changing the appearance. One useful command in the prompt is "ipconfig", which you type into the ...

Command prompt and other commands can save you lots of time on your computer. Use these shortcuts to bypass longer keystrokes and access blocked sites. There are many things you can do with cmd prompts and this tutorial will tell you about all of them. Learn step by step how to use and take advantage of these commands in the following video.

Train a dog to leave toxic food alone. Learn how to teach your dog to stop chewing, eating, or digging with the leave it command in this free pet training video.

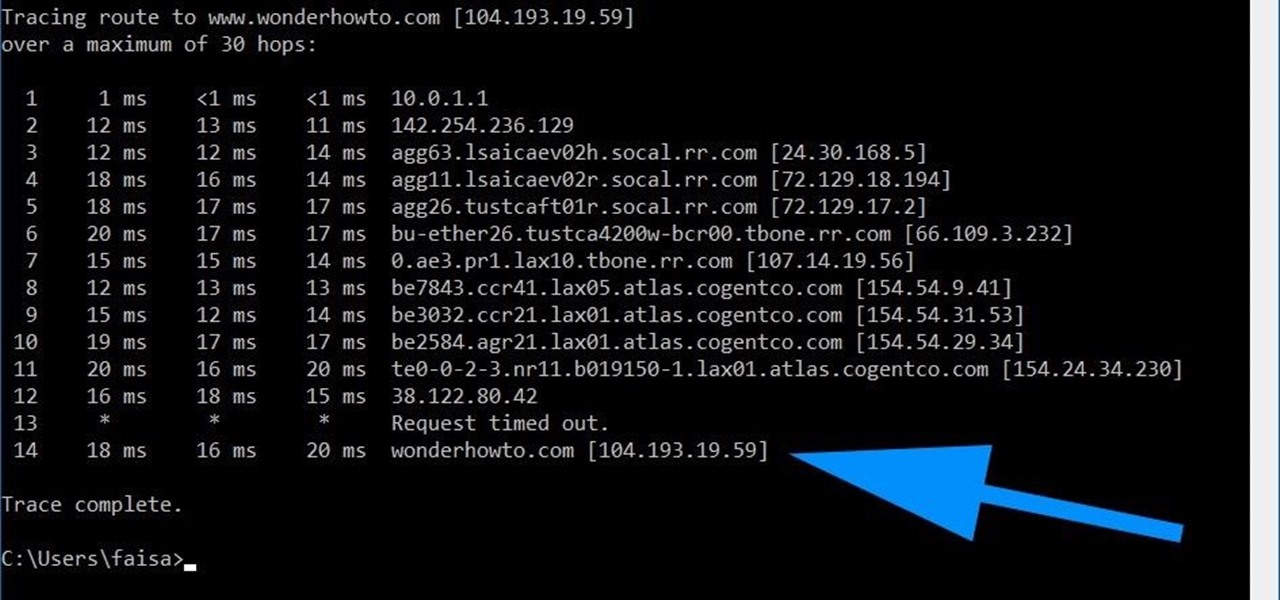
Using a simple trace trick, you can easily look up the IP address and its location for any website. This method uses a command line command to first find the IP address of a given website, and then uses a free online tool to get that IP's location.

Post-exploitation is often not quite as exciting as popping the initial shell, but it's a crucial phase for gathering data and further privilege escalation. Once a target is compromised, there's a lot of information to find and sift through. Luckily, there are tools available that can make the process easy. One such tool is Postenum.

After backdooring a MacBook not protected by FileVault or using a fake PDF to gain remote access, an attacker may wish to upgrade their Netcat shell to something more fully featured. While a root shell allows attackers to remotely modify most files on the MacBook, Empire features some useful post-exploitation modules which make hacking Macs very easy.

Hello everyone! I'm glad to post my first tutorial and hope you will appreciate it.

March, 2047. A massive nuclear fireball explodes high in the night sky, marking the dramatic beginning to the Third Tiberium War and long-awaited return of the most groundbreaking Real-time Strategy franchise (RTS) of all time. This is Command & Conquer 3: Tiberium Wars.

Keep a dog off of high objects and keep them from jumping up on guests. Learn how to teach a dog the off command in this free video on pet training.

You know it's not safe to drive and oeprate your cell phone, so why not learn how to take advantage of the latest voice features on the Samsung Rogue? Just watch this video and you'll be dictating, and voice commanding and controlling in no time. Give your thumbs a break, dictate your texts - the Rogue even recognizes commands such as "smiley face" and translates them into the appropriate emoticon. Cool!

The new Siri app allows you to use voice commands to search, use apps, and more. The app is available as a beta version in the iOS 5 release for the iPhone 4S. This guide will show you how to use different voice commands to control Siri.

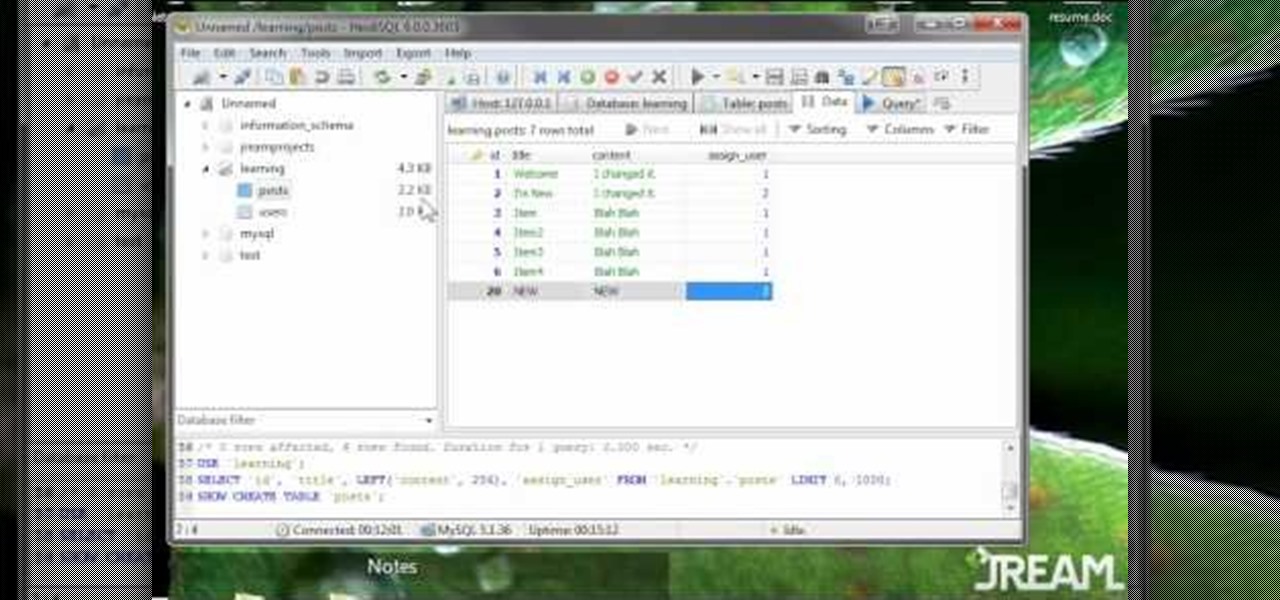
JOIN commands in MySQL can be scary, and a bit tricky to master - but that's where this video comes in. This clearly and succintly demonstrates what a JOIN in MySQL is and how you can painlessly use these commands in your projects.

This video is all about the basic movement commands in one of your units in StarCraft 2: Wings of Liberty. This is the basics, so you better know this stuff before you get too involved. Learn about what the computer mouse can do for you when moving your units and learn a whole lot more! This is the basic unit movement.

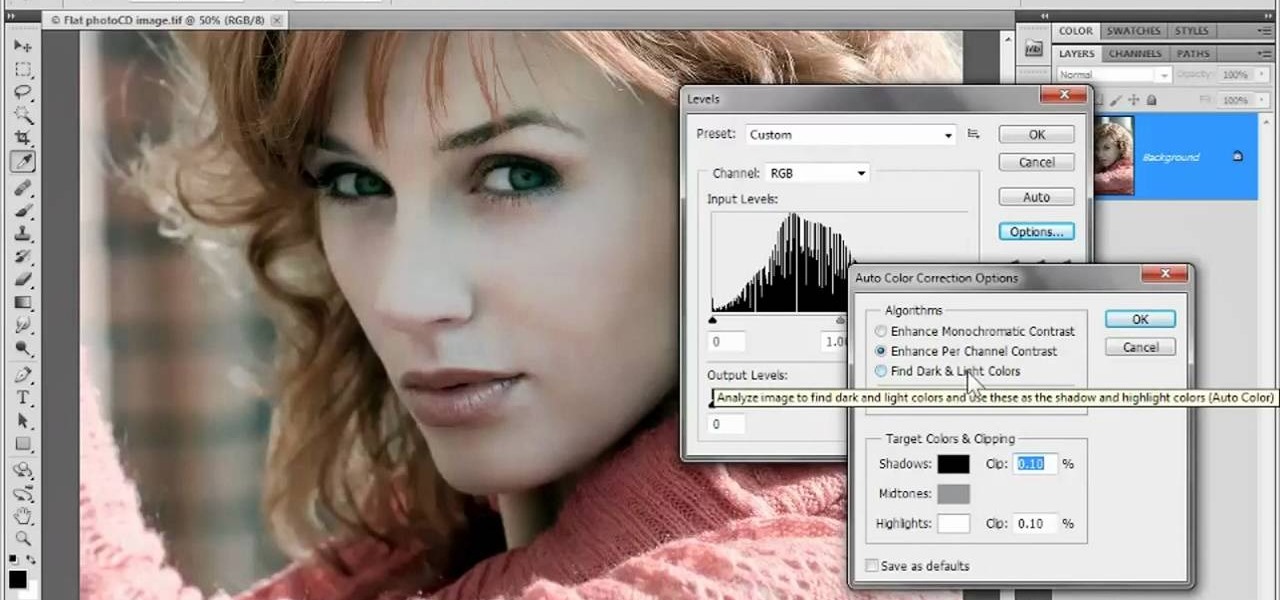
In this clip, you'll learn how to adjust luminance with the Levels command in Photoshop CS5. Whether you're new to Adobe's popular raster graphics editor or a seasoned designer looking to better acquaint yourself with the new features and functions of the latest iteration of the application, you're sure to benefit from this free software tutorial. For more information, watch this video guide.

Looking for a guide on how to get the most out of the auto commands in Adobe Photoshop CS5? Whether you're new to Adobe's popular raster graphics editor or a seasoned designer looking to better acquaint yourself with the new features and functions of the latest iteration of the application, you're sure to benefit from this free software tutorial. For more information, watch this video guide.