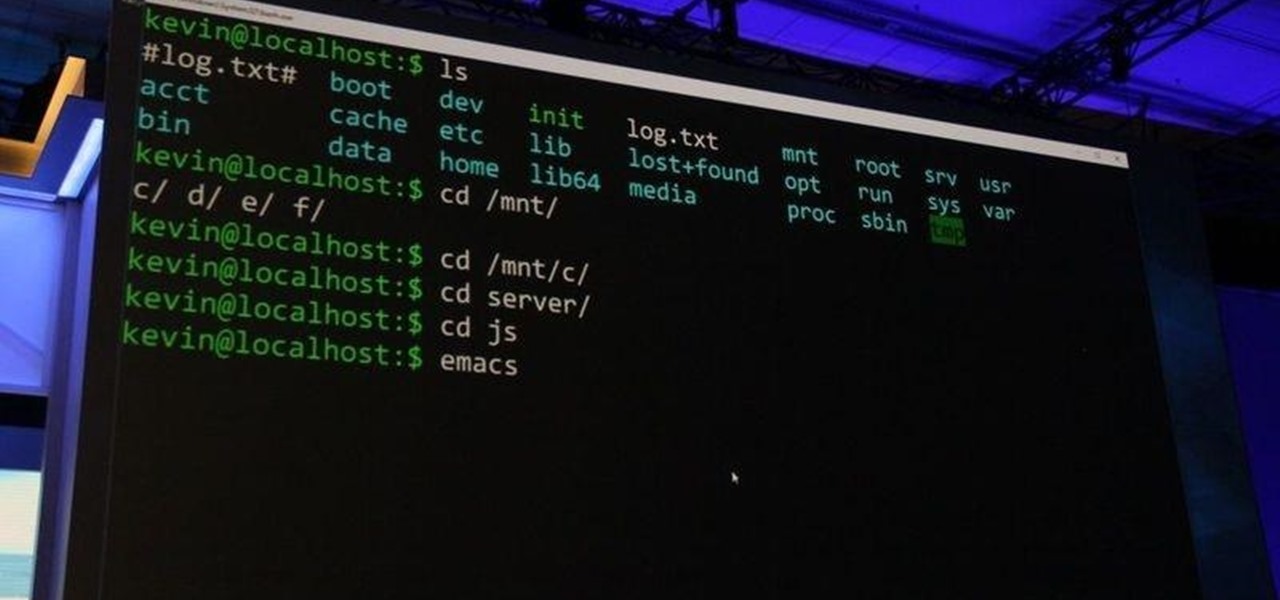
In this tutorial, we learn how to use Linux: Commandline Dependencies with gdebi. First, download a Deb file then use dpackage to install the package on the command line. If this fails, you will be able to use gdebi to install all the dependencies in command mode. This will save you time from trying to figure out how to open your file any other way. When you are finished, you will be able to open you file and enjoy what's inside. If you aren't familiar with how this works, search the internet...

In this video tutorial, viewers learn how to zoom in and out on a Mac computer. To access the zooming tool, begin by clicking on the Apple menu and select System Preferences. Under System, select Universal Access and check On under Zoom. In Options, users are able to set specific settings such as the maximum and minimum range of zoom. The keyboard shortcut for zooming in is: Option, Command and =. The keyboard shortcut for zooming out is: Option, Command and -. This video will benefit those v...

Just as lighthouses help guide journeying ships at sea back home, front posts help guide your knitting needle to where it should go for complex patterns.

Just as lighthouses help guide journeying ships at sea back home, front posts help guide your knitting needle to where it should go for complex patterns.

In this how to video, you will learn how to teach your dog to retrieve. First, you should teach your dog the a regular retrieve. You will toss the object so that the dog sees where it lands. Next, give it the command to retrieve. Next, attempt the semi blind retrieve. This involves tossing the object, allowing your dog to see where it has gone. Next, distract the dog for a bit before giving it the command to retrieve. The full blind retrieve should now be attempted. This is done by hiding the...
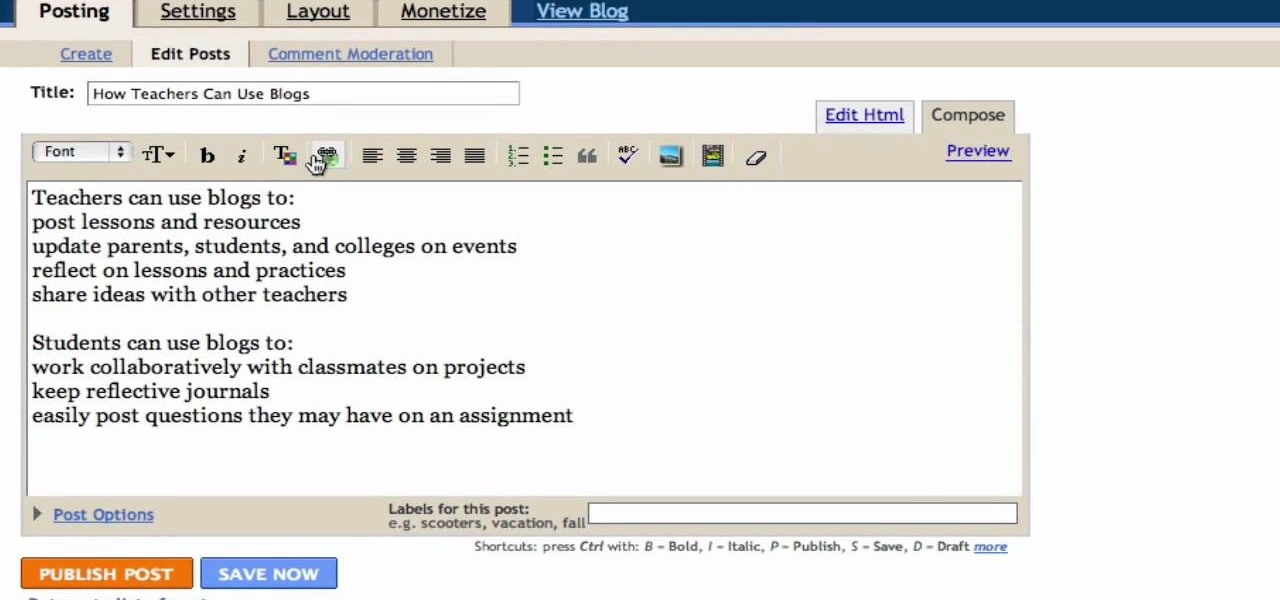
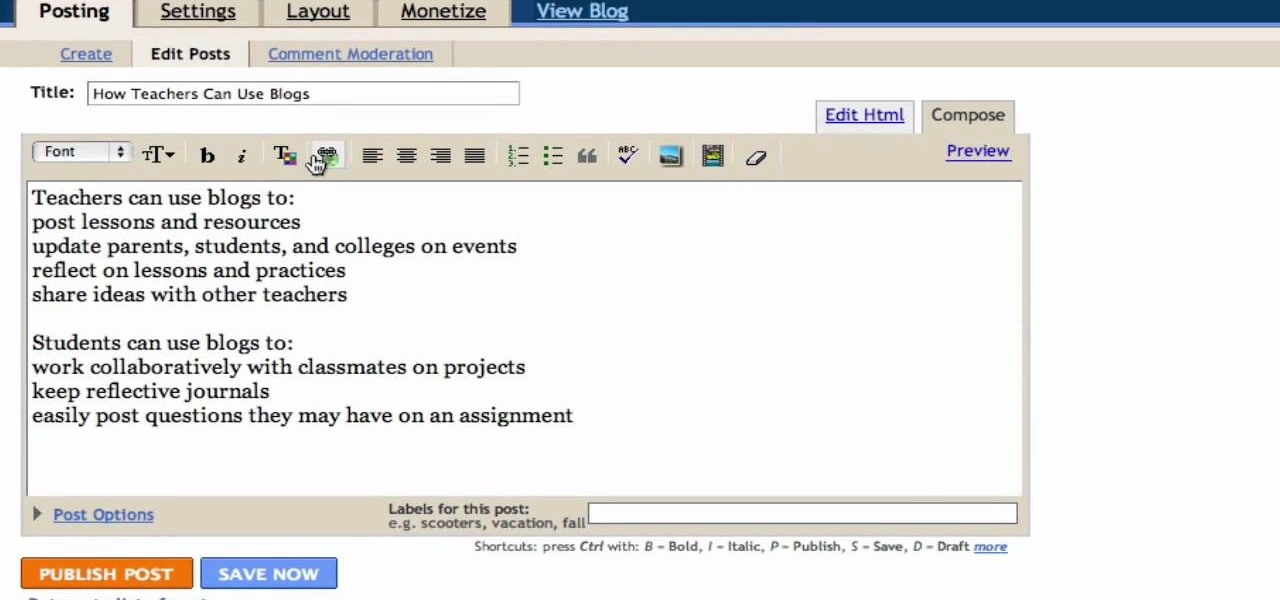
In this Computers & Programming video tutorial you will learn how to create a new account, add and edit in Blogger. First go to Blogger. On the home page click on ‘create a blog’. You will be taken to the account setting up page. Feed in all the details including our email. Then open your email and click on the confirmation link. You will then be taken to your dashboard or your home page. On this page you can click on ‘new post’ button and start writing your blog. When you do this a word proc...

In this video tutorial, viewers learn how to embed a YouTube video into a blackboard forum post. Begin by finding the YouTube video that you want and copy the URL. Then go to your blackboard post and go to a forum that you want the video to be in. Start a new thread and fill out the thread as you wish. Then click on the red F (Add Flash/Shockwave Content). Paste in the URL and fill in the file options. In the URL, delete "watch?", add / after v and delete =. This video will benefit those view...

Open your first image and go to the rectangular marquee tool and select all of the image. Next click command or control C to copy image. Then go to your second image and click command or control V to paste the image. Select both the layers (hold down shift when clicking the layer), then go to edit, auto align layers and choose the top option then click ok. Last add a mask to your top layer, this is done by selecting the gradient tool (make sure its set black to white, the mode is normal and o...

Nguyen Le, aka Knitknit teaches how to make knitted post cards. If you are teaching yourself how to knit, you will love this video. This is also a great way to use your knitted test swatches to make a special something to send to someone! You will need two colors of yarn, a hole punch, a post card, knitting needles, and a needle. Learn how to make a knitted post card by watching this video crafting tutorial.

If you're interested in seeing what it would be like to run Android on a real computer rather than a tablet or smartphone, you don't have to wait. This Android project has now made it possible to run Android in a virtual machine on either a PC or a Mac computer. You'll need the following command to merge the ISOs:

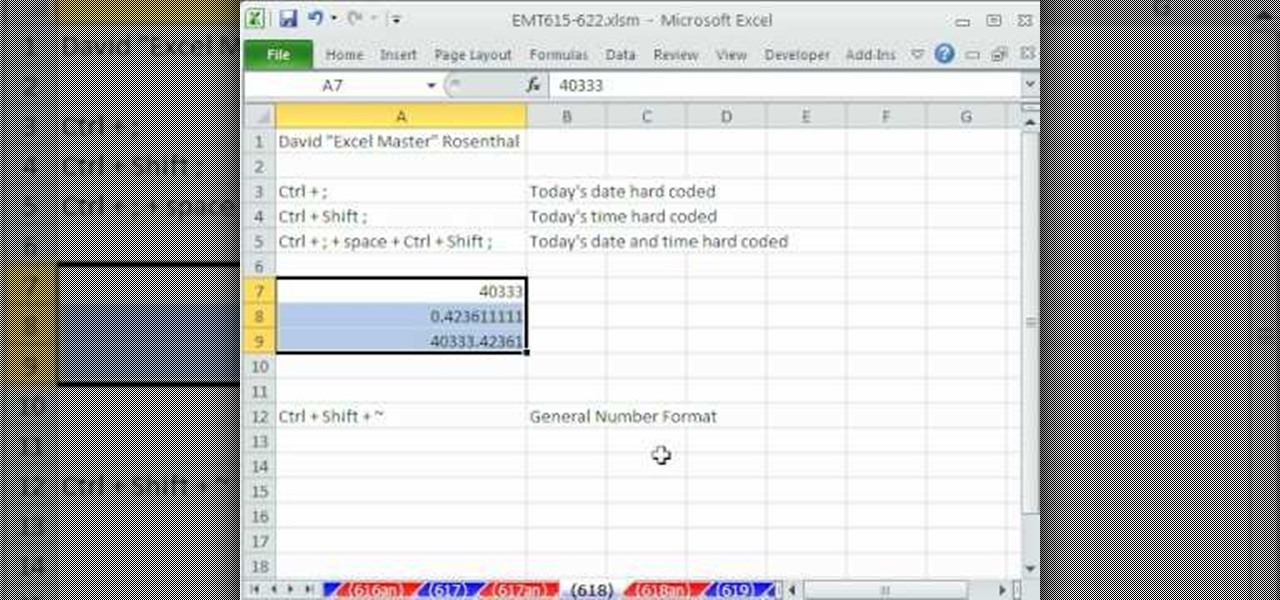
New to Microsoft Excel? Looking for a tip? How about a tip so mind-blowingly useful as to qualify as a magic trick? You're in luck. In this MS Excel tutorial from ExcelIsFun, the 618th installment in their series of digital spreadsheet magic tricks, you'll learn about a handy key command that will allow you to enter both today's time and date into a single Excel cell.

This is the most important thing that a dog should know. In this video will learn the fundamentals of how to begin to teach this. It is by no means entirely conclusive to the training that is involved in teaching stay. Tab with his German Shepherd "Solea" demonstrate the do's and don't when training your dog to "stay". You'll also learn the importance of this command for the dogs safety.

Check out this lesson on how to understand your dog and train her to listen. This video will show you how to use a clicker to communicate with your dog. It will also show you how to teach your dog the "Leave It" command. This is a helpful video for training puppies and older dogs.

Following the success of Mimic Baby (sign language for babies) Selena Lohan developed Mimic Mutt - sign language for dogs. It turns out it's easier to communicate with your dog using regular sign language than voice commands. Watch the video to find out more.

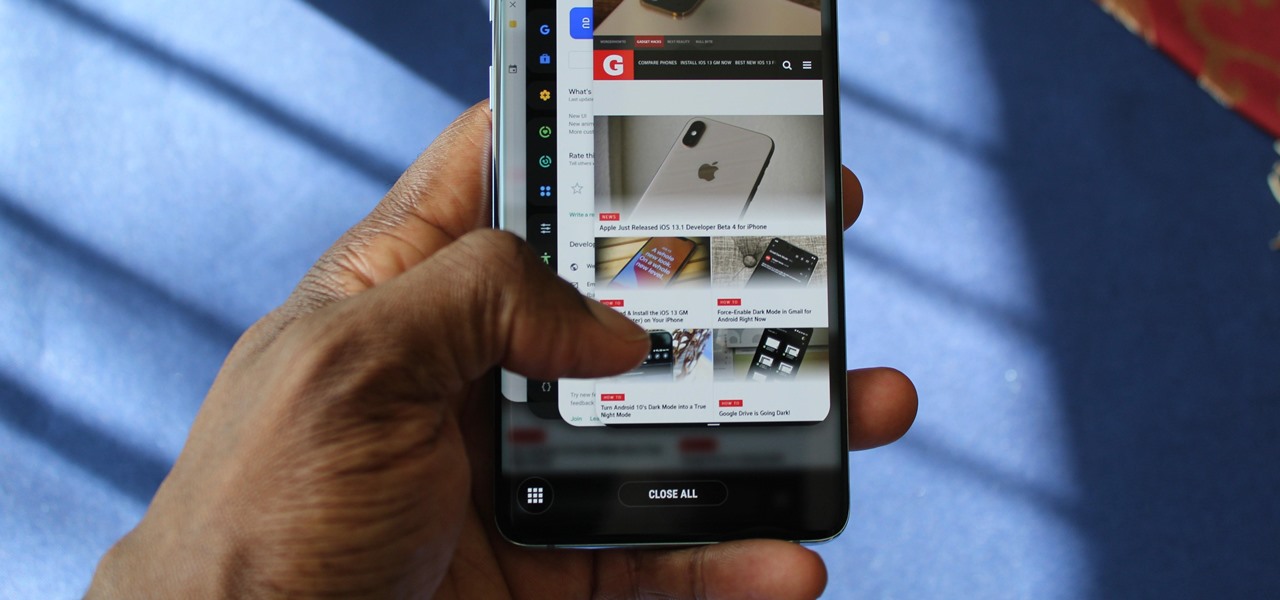
In previous Android versions, you lost about an inch of screen real estate to the status bar and navigation bar. But if you enable Android 10's new navigation gestures on your Samsung Galaxy, you can regain the bottom part — and with the help of ADB, you can reclaim the top portion as well.

The biggest hurdle to rooting is that it usually requires a computer. Things get complicated when you're trying to use a desktop operating system to exploit a mobile OS, and the connection isn't always reliable. But with the help of Magisk, you can now use one Android phone to root another.

UnrealIRCd is an open-source IRC server that has been around since 1999 and is perhaps the most widely used one today. Version 3.2.8.1 was vulnerable to remote code execution due to a backdoor in the software. Today, we will be exploiting the vulnerability with Metasploit, examining the underlying code to understand it, and creating our own version of the exploit in Python.

Lover it or hate it, Android 10 is a big improvement over Android 9 Pie. Based on previous versions, most flagships released in the last two years will get Android 10, but the question is when. So while you wait for those cool new gestures, how about I show you an app that gives you a nearly identical experience?

The first thing you'll always have to do before getting your customization game on with most phones is to unlock the bootloader. Doing so opens the true potential of the device, allowing you to root, install TWRP, Magisk, custom ROMs, and other mods. No matter your wants or needs, there's no way around it — the bootloader must be unlocked to modify the system.

In about 27% of all car crashes, someone was using their cell phone. You may think texting is the big problem here, but many fail to realize that even the smallest smartphone interaction could spell disaster. Thankfully, Google Maps has rolled out an overdue feature that'll help ensure a safer drive.

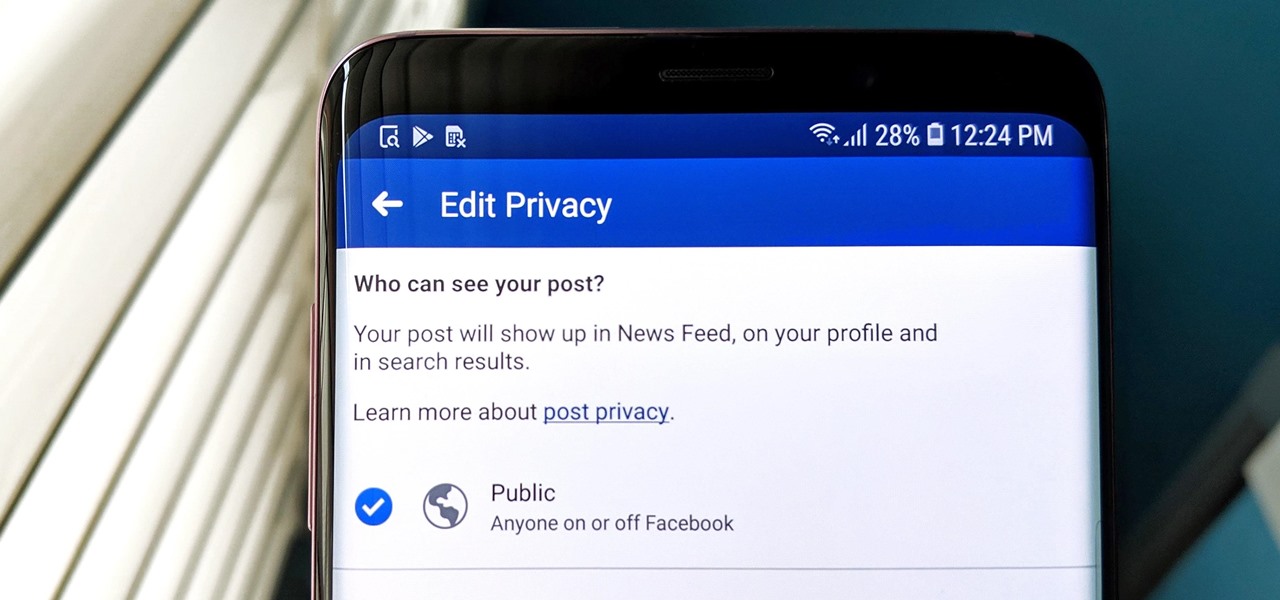
Facebook has grown into one of the central hubs of the internet where ideas are shared with others. But with the rise of brand development, individuals and companies need to get their messages out beyond their group of Facebook friends so it can be seen by more of the world.

Depending on how you use your phone, you may have noticed your status bar is a bit crowded due to various icons being enabled. While some icons make sense to have, such as Wi-Fi and Bluetooth, the VPN key icon can be redundant, especially if the app uses a notification. Good thing, there is a way to get rid of the icon.

Don't think because your MacBook is using FileVault disk encryption your device is secure or immune to hackers. Here's how to find out if that FileVault password is strong enough to withstand an attack from a motivated attacker.

When you've had enough of someone's annoying baby videos or cat photos on Instagram, you would have to either unfollow them or even block them outright. Now, you don't have to cut ties with them completely — you can just mute them instead, a feature that Instagram's parent company, Facebook, has allowed on its platform for some time.

Analysis of photographs and social connections can be a huge component of social engineering. Understanding who a person is, as well as who they know, can establish links within a company. This information could be used by hackers to execute elaborate social engineering attacks.

While installing the new Android 9.0 Developer Preview is fairly easy if you're using a Windows machine, it's a little trickier if you want to use macOS instead. To help you get the latest Android OS on your Google Pixel phone, we'll break down the whole process so using your Mac can be as simple as Windows.

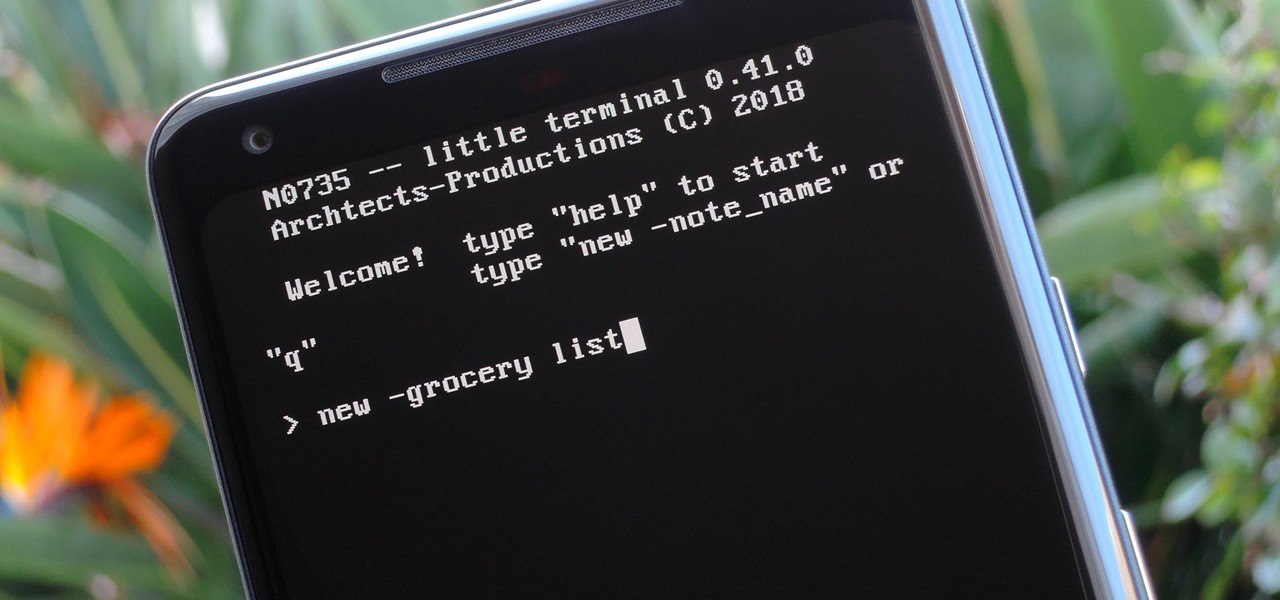
Deep down inside, Android is really just a fork of Linux, the popular open source desktop OS. You can see traces of its roots everywhere, and this lineage still holds a certain appeal with many Android fans. If you're in that boat, you'll love the newest notes app we just found.

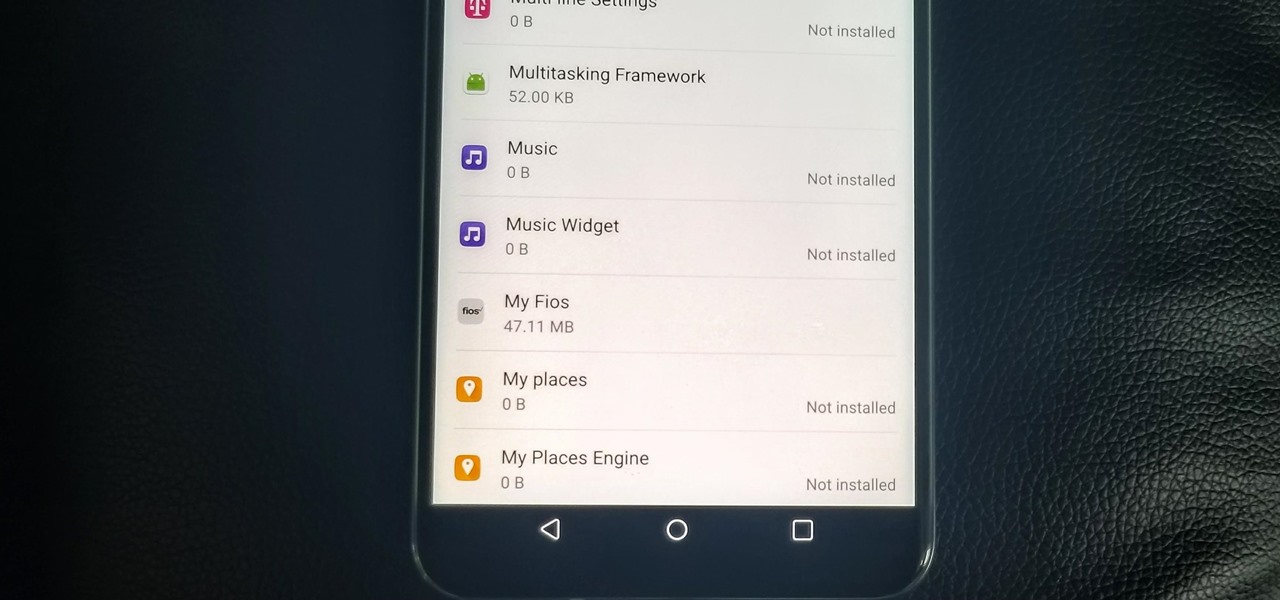
With the V30, LG has really delivered an amazing smartphone that hits all the major features consumers want. Amazing camera, beautiful edge-to-edge display, great battery life, water resistance, and smooth performance — there isn't much not to like about the LG V30. Unfortunately, it does suffer from heavy bloatware thanks to the carriers. The good thing is, unlike in the past, you are not stuck with it.

In my previous article, we learned how to generate a vulnerable virtual machine using SecGen to safely and legally practice hacking. In this tutorial, we will put it all together, and learn how to actually hack our practice VM. This will provide some insight into the methodology behind an actual attack and demonstrate the proper way to practice on a VM.

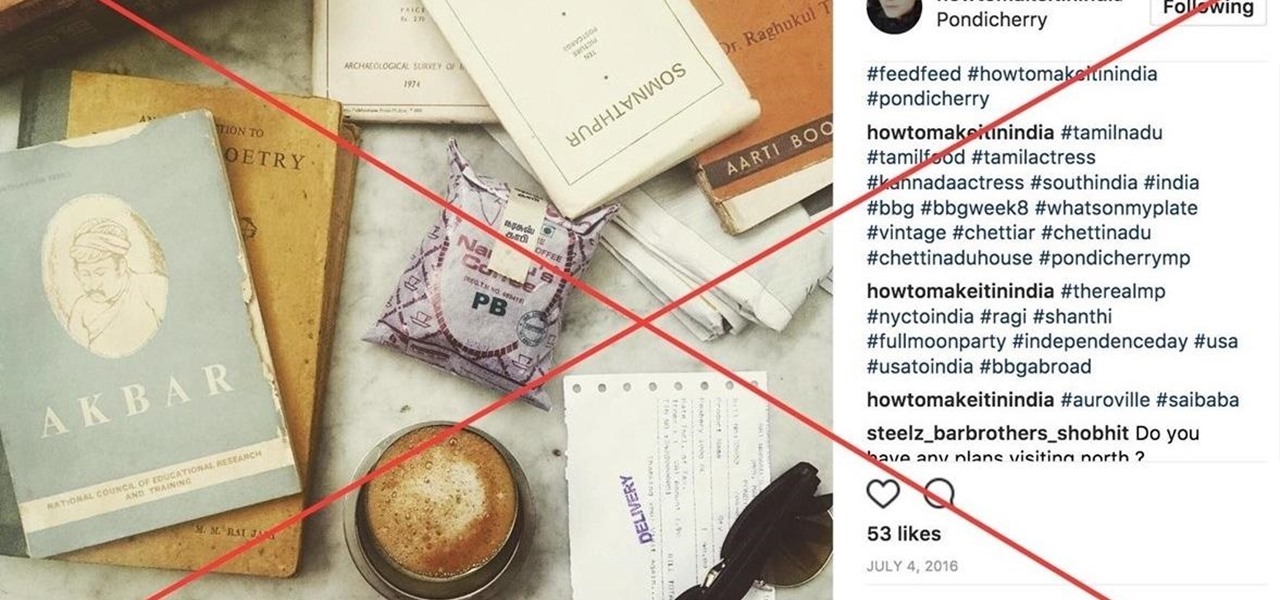
In this article, I am most likely going to humiliate myself by showing you all the horrible hashtagging I am wont to do. When it comes to hashtags, well, everybody knows if you desire any chance at all of getting noticed on Instagram, you got to hashtag.

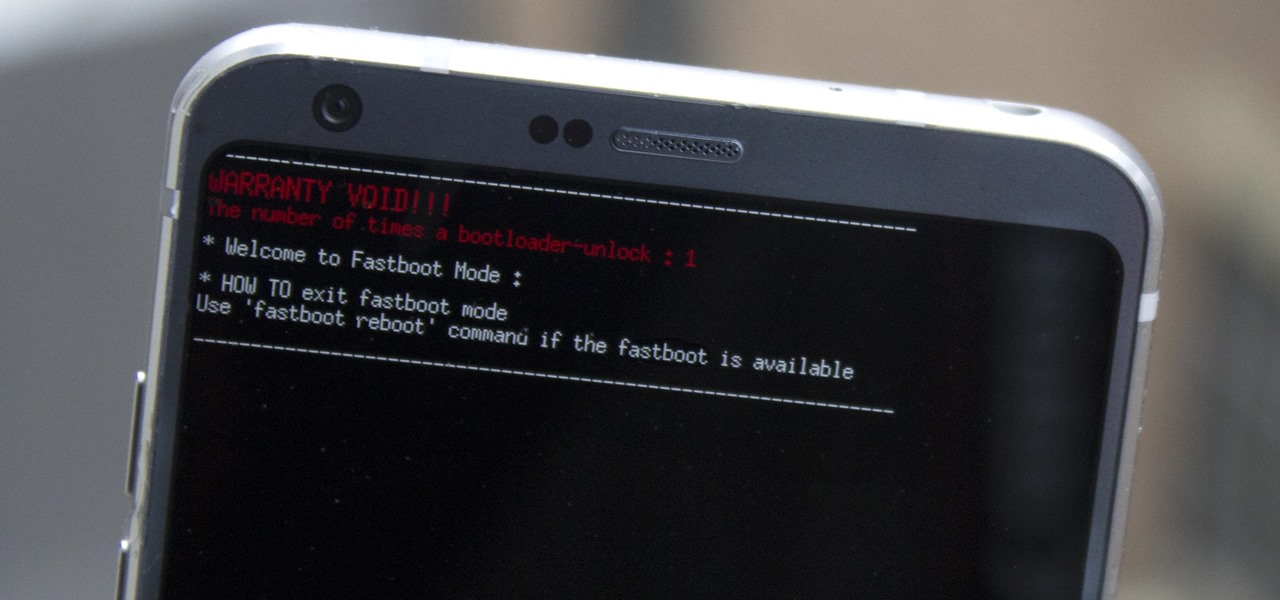
Preorders for the LG G6 have all been fulfilled, and the phone has been up for grabs at local cell phone providers for three weeks now. However, not every LG G6 was created and released equally. The T-Mobile variant of the LG G6 features an unlockable bootloader, while most other North American variants come with a tightly locked down bootloader, which effectively limits the full potential of your brand new fairly expensive phone.

One of the biggest features to come out with Android O was the addition of a new System UI Tuner submenu that lets you customize the navigation bar at the bottom of your phone's screen. But as it turns out, this same feature can be enabled on devices running Android Nougat, even without root access.

One of the only downsides to the Pixel XL is that Google's flagship phone does not have stereo speakers. But if Android's awesome development community has taught us anything over the years, it's that limitations like these can be bypassed with some creative software tinkering.

When it comes to modding an Android device, a custom kernel can take you farther than almost anything else. Most offer the ability to overclock your processor for performance gains, change your CPU governor, or even under-volt to increase battery life, among other features.

As most of you know, I am a strong advocate for using Linux for hacking. In fact, I would go so far as to say that you cannot be a hacker without knowing Linux well. I laid out various reasons for this in my "Why Every Hacker Should Know & Use Linux" article, and I even have a lengthy, continuing series on Linux Basics to help those new to Linux master it.

Welcome back, my budding hackers! Metasploit, one of my favorite hacking/pentesting tools, has so many capabilities that even after my many tutorials on it, I have only scratched the surface of it capabilities. For instance, it can be used with Nexpose for vulnerability scanning, with Nmap for port scanning, and with its numerous auxiliary modules, nearly unlimited other hacking related capabilities.

When using Linux, we often need to install new software, a script, or numerous large files. To make things easier on us, these files are usually compressed and combined together into a single file with a .tar extension, which makes them easier to download, since it's one smaller file.

Recently, I've been experimenting with BeEF (Browser Exploitation Framework), and to say the least, I'm hooked. When using BeEF, you must "hook" the victims browser. This means that you must run the script provided by BeEF, which is titled "hook.js", in the victims browser. Once you've done that, you can run commands against the victims browser and cause all kinds of mayhem. Among these commands, there is an option to use the victims webcam. This is what we'll be doing here today, so, let's g...

Returning your device to stock, whether it is because you need to sell it or just want to receive OTAs again, is not always a simple process. Since HTC has released countless variations of both the M7 and M8 HTC One, it can be a pain in the ass finding the right files and tools to get your phone back to stock settings.

Hello, ladies and gents! Today I will be discussing the fun and excitement of backdoor on an OSX system.