From time immemorial, human beings seem to be at odds with one another. When these differences become so heated and unresolvable, it eventually erodes into physical violence. This violence has manifested into some of the most horrific exercises in human history, things which every school child is aware of and none of which we have to recount here. Although humans have been cruel and violent for a very long time, the 20th century may have epitomized that behavior. With two World Wars and many,...

When I first received my HTC One M8, I was in love with the 5-inch screen size, but the icons and font just seemed too big, wasting valuable screen real estate. Phablets, like the Samsung Galaxy Note 4, have only slightly larger screens, but don't seem to have this problem since manufacturers lowered the device's DPI, or dots per inch.
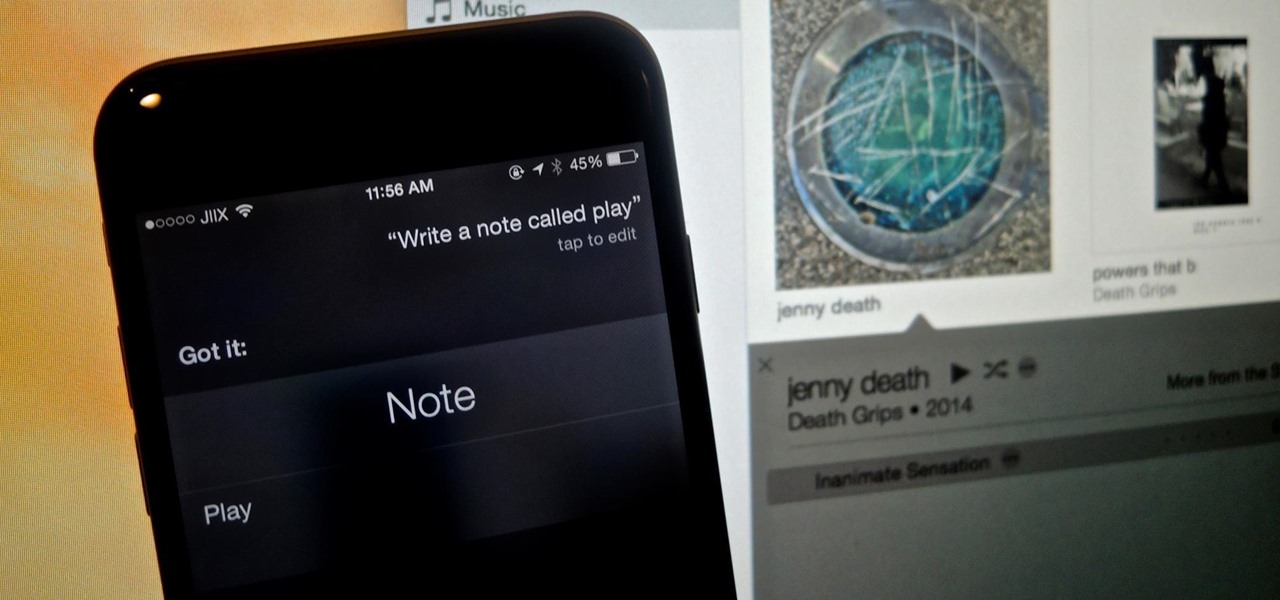
While Apple's Continuity feature has certainly impressed me, I can't help but feel like it could be used to create a better connection between my iPhone and Mac. Sure, Handoff allows me to pick up where I left off in certain applications between the two devices, and it lets me pick up calls and send text messages on my Mac, but I want even more functionality.

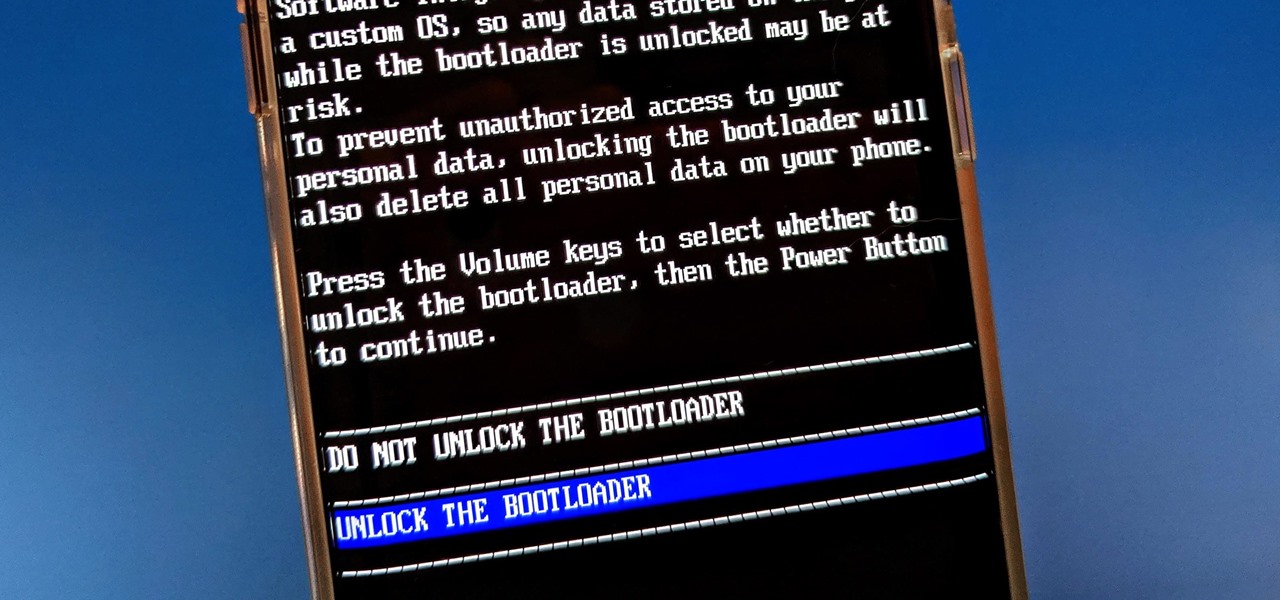
There are two types of bricks ("brick" as in "bricking your phone")—soft and hard. Soft bricks are recoverable—something has probably gone wrong with some critical system partition, causing a bootloop or inability to boot in some way. Fine. Re-flashing everything should fix that instantly. Hard bricks are not recoverable—if you manage to hard-brick your Nexus, you are in trouble.

Google released its long-awaited Google Now launcher a couple months ago, allowing users to access Google Now with the simple command of the voice. As great as the feature is, it requires that our screens be on, unlike the Moto X's "active listening" service that operates with Google Now, activating through a screen-off state.

With the the general computer users understanding of Information security rising (at least to the point of not clicking on unknown links), and operating system security getting better by default. We need to look for new and creative ways to gain a foothold in a system.

Welcome back, my hacker apprentices! Metasploit framework is an incredible hacking and pentesting tool that every hacker worth their salt should be conversant and capable on.

Make voice commands on your myTouch 4G! This clip will teach you everything you'll need to know to use the myTouch 4G's Genius Button. Whether you're the proud owner of a T-Mobile myTouch 4G Google Android smartphone or are merely toying with the idea of picking one up sometime in the near future, you're sure to be well served by this brief, official video tutorial from the folks at T-Mobile. For complete instructions, watch the video!

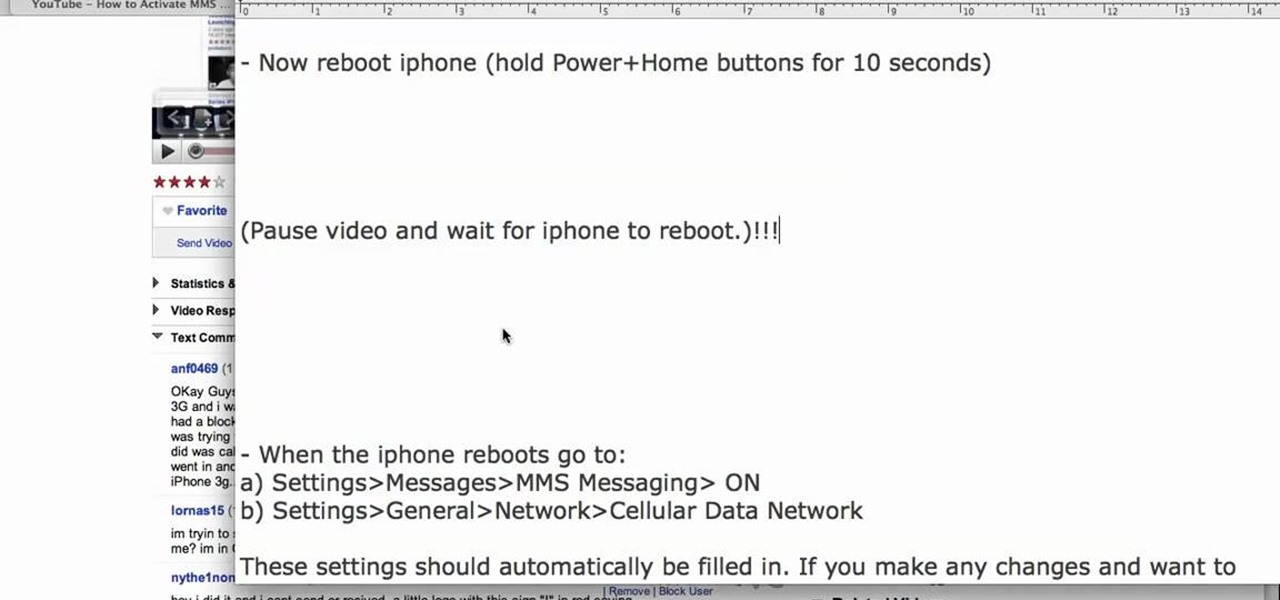
In this tutorial, we learn how to use MMS on T-mobile or ATT iPhone using 3.1 or lower. First, you need to make sure you have iTunes down and it's not running on your computer at all. After this, go to the start menu, then click on the run. Next, type in "command" and hit enter. Then, type or copy and paste "C:/Program Files/iTunes/iTunes.exe/setPreflnt carrier-testin 1" into the command console that comes up. Then, hit enter and reboot your iPhone. When this reboots, go to the settings menu,...

Shawn Powers teaches us how to install Truetype fonts on your Linux systems. First, log onto your web browser and go to Halloween Fonts. Once on this site, browse through the different types of fonts until you find one that you like. After this, save the file for the font onto your desktop. Now, install this font on your command line by first unzipping it. Go to the user share Truetype folder, then make a new custom folder. Move the file into the folder, then make sure the font and the folder...

This tutorial will show you how to hide files on your computer using an image file. The first step is to get an image file and edit it with Microsoft Paint or Adobe Photoshop. The next step is to save the image file as a jpeg file. Now create a WinRaR archive file and copy the files that you want to hide in the archive. The next step is to open Command Prompt: Click the Start button and click Run. Now enter "cmd" and hit enter. Now just enter the same commands from the video and hit Enter. Fo...

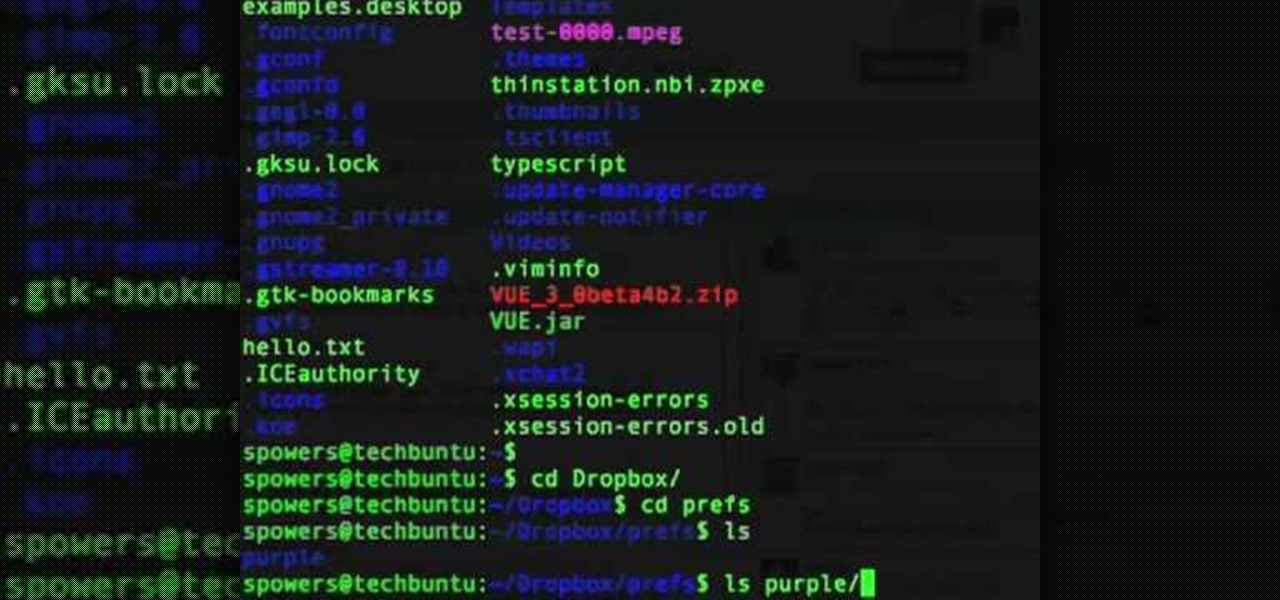
In this tutorial, we learn how to sync preferences with DropBox or Ubuntu one. This doesn't work for everything, but it will sync pigeon preference. It's a folder ".purple" and all the preferences are inside here. If you are familiar with using command prompts, then this will be very easy for you to do. Make a symbolic link from the command prompt to the drop box folder. On every folder, you will get the same result! This is very easy to do and just takes a few seconds to find, then you can c...

In this Software video tutorial you will learn how to use tool shortcuts in Final Cut Pro. To change opacity and the volume limit, click the little mountain button on the bottom and you will have two lines in the clip representing audio lines of two mono tracks. And you also have opacity located above the audio lines. With the help of the slide bar you can set the opacity. To get the pen tool press 'P'. To get out of any tool, press 'A'. To delete the entire audio track, select it, lock, dele...

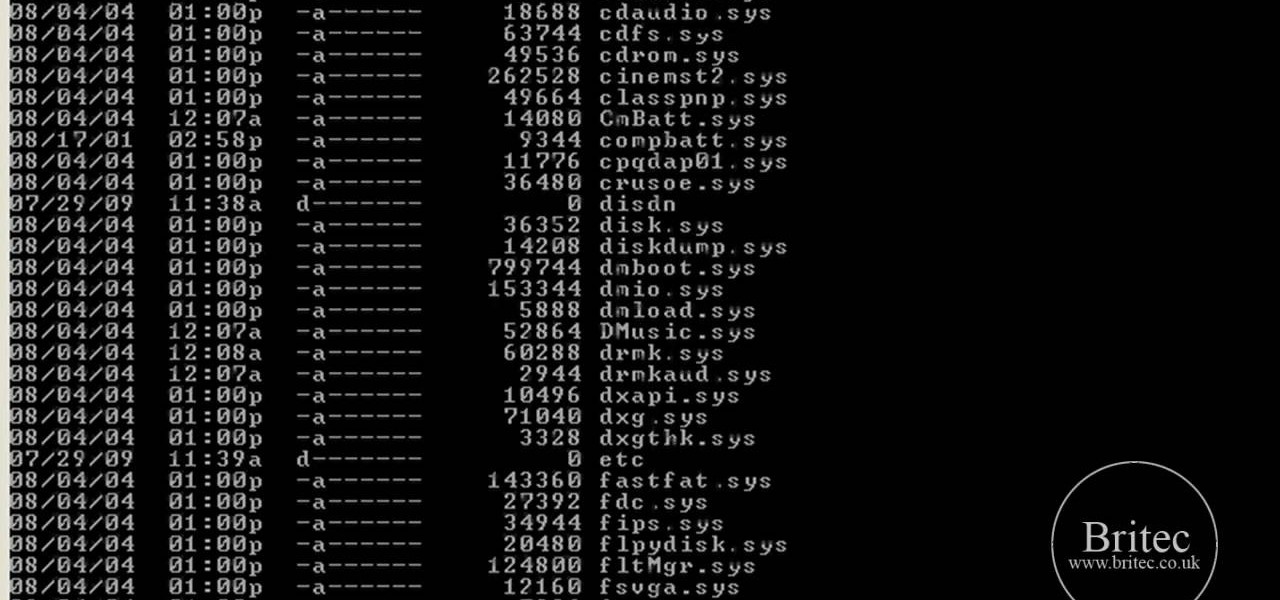
In this tutorial, learn how to fix a missing or corrupt error message "System32\Drivers\Ntfs.sys" Step 1:

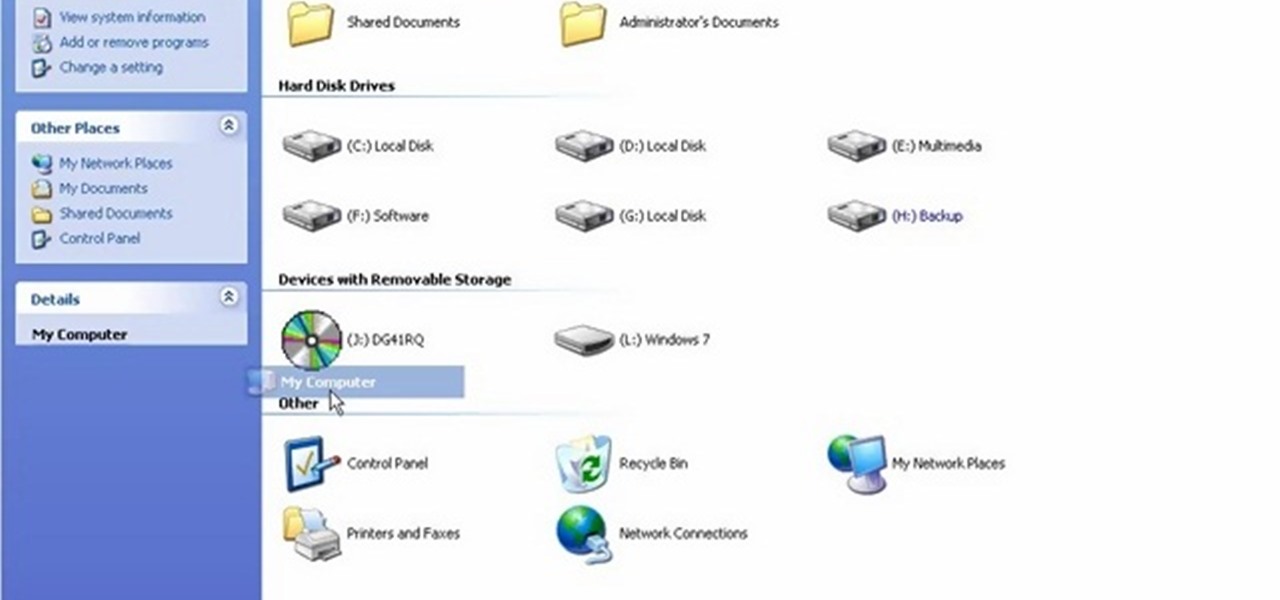
In order to install Windows 7 from a USB drive, while you are running XP, you will need a pen drive. You will also need a Windows 7 DVD and a pen driver.

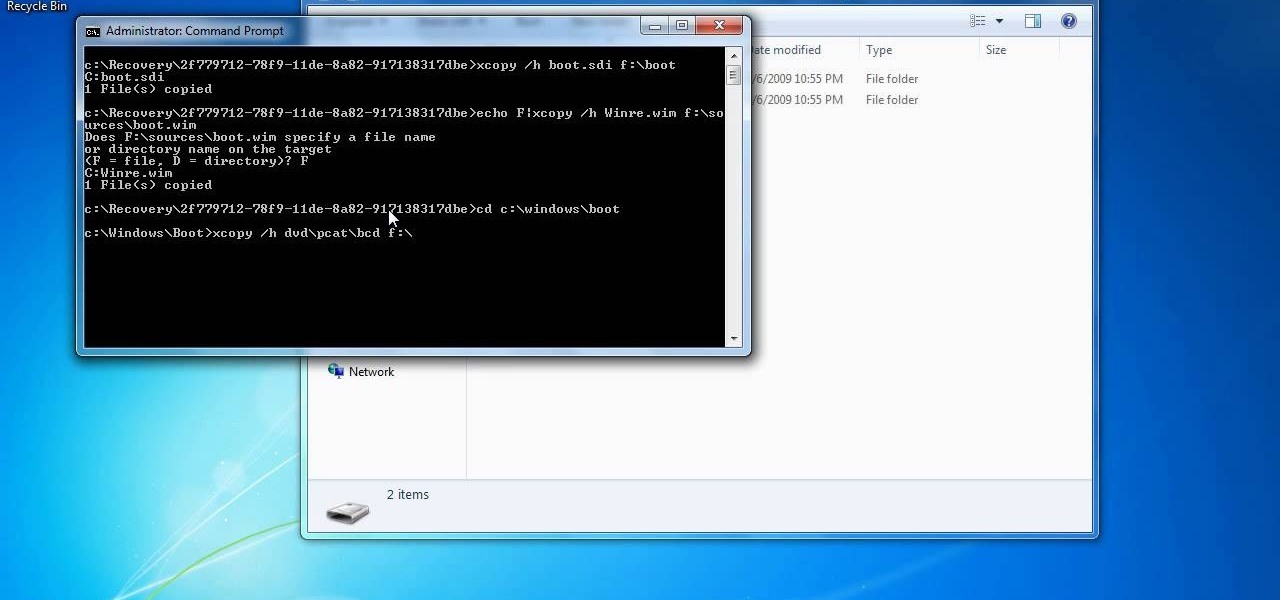
In this how to video, you will learn how to create a system repair disc on a bootable USB flash drive without having to burn a CD for your Windows 7 system. First, plug in your USB drive and create new folders in it. Name the first folder boot and the second sources. Next, open a command prompt and type in the cd c:\recovery, dir /a:sh, and so forth as shown. Once you have typed in the proper commands in the prompt, eject the flash drive. Restart the computer with the drive plugged in. Boot f...

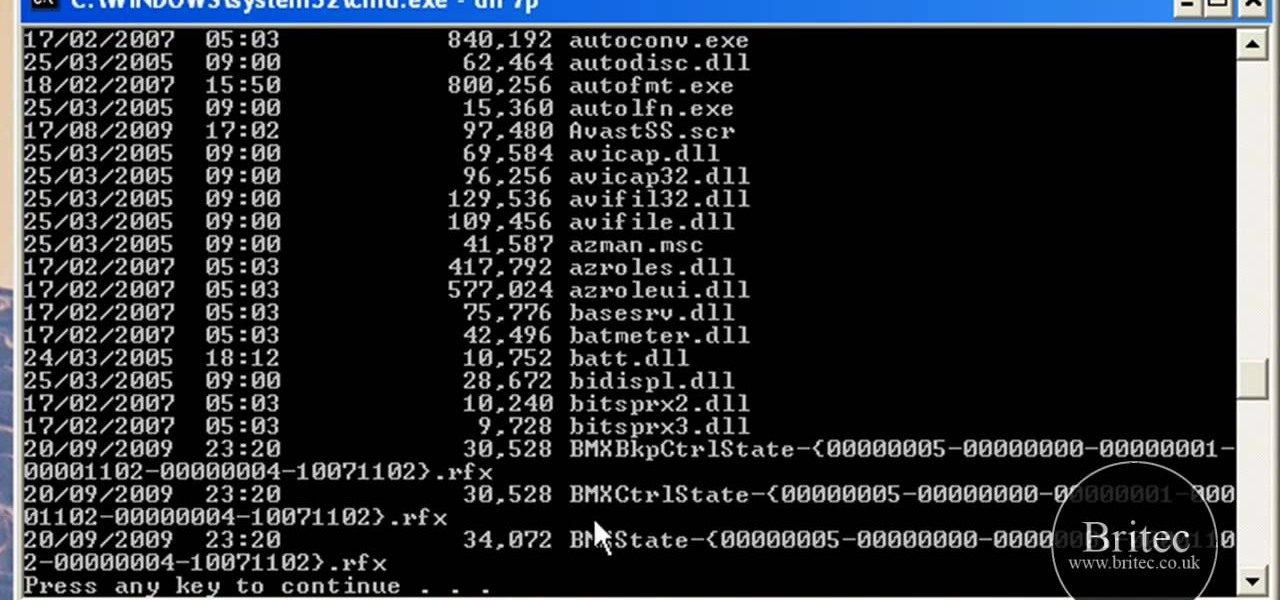
In this Computers & Programming video tutorial you will learn how to remove ntde1ect.com & autorun.inf virus & trojan files. Go to my documents > tools > folder options > view and unhide the files and click OK. Open up the task manager. Under properties, click on explorer and end that process. Then look for wscript.exe, select it and minimize the task manager. Now open up command prompt and type in ‘dir’ against C drive. This will not list the hidden files. So, you type in ‘attrib –r ...

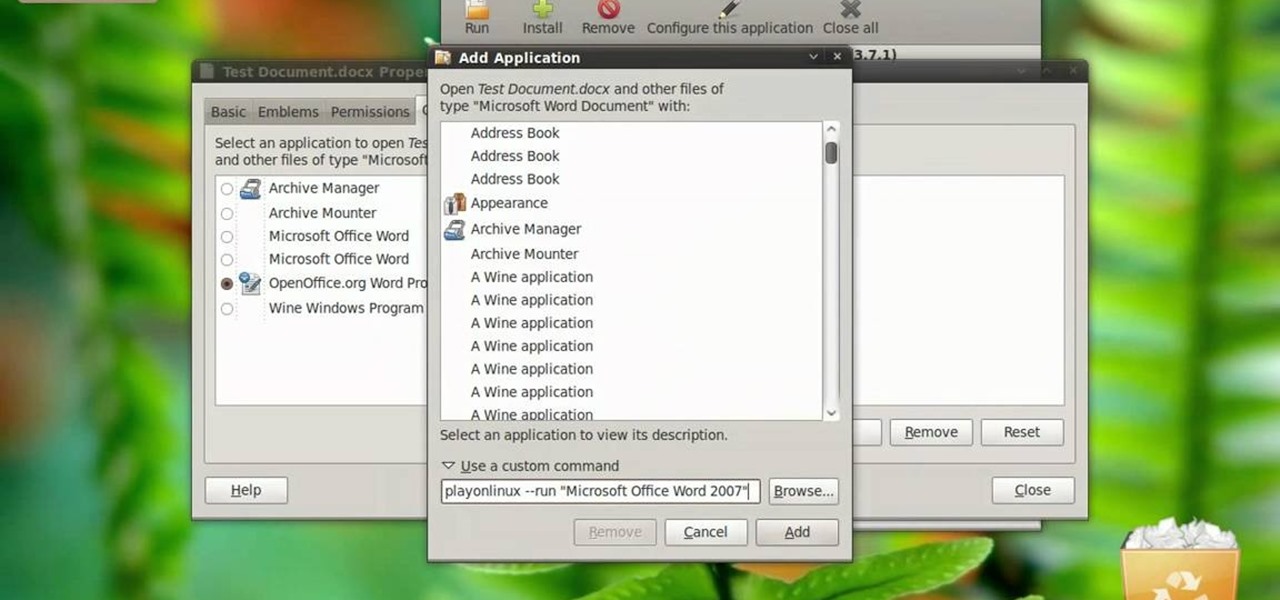
In this video tutorial, viewers learn how to open a Microsoft Word 2007 file by double-clicking it on Ubuntu 9.10. Begin by right-clicking on the file and go to Properties. Click on the Open With tab and select Use a custom command. Now type in [playonlinux --run "Microsoft Office Word 2007" and click Add. Select the custom command from the list and close the window. This video will benefit those viewers who use a Linux computer, and would like to learn how to open Microsoft Word 2007 files b...

Reformatting a flash drive will update its drivers and rid it of all data. This can help in a lot of occurances. This tutorial will show you exactly how to format flash drive properly.

In this video Guides4tech teaches the secrets of finding your local IP and MAC address in simple steps. First click 'Start' and select 'Run' on your computer. Now type 'cmd' to open the command prompt. In the command prompt type 'ipconfig/all' and press 'Enter'. Your IP address will displayed under the 'Ethernet adapter local area connection' menu. Your MAC address will be displayed as 'Physical address' under the same menu.

For anyone who has accidentally deleted a file, follow the steps in this tutorial to learn how to recover the file on Ubuntu. Learn what commands to type to run a search that will allow you to undelete a deleted file. This tutorial shows you letter by letter what command to type and in what format it should be typed to scan your hard drive for the deleted file. Once your search has found the file, the tutorial also shows how it can be recovered and then saved back onto your hard drive.

The instructor, Diesel, teaches how to bypass blocked websites at school like MySpace and YouTube. He shows how to make a batch file which opens the command prompt. Next, he shows how to ping a website like MySpace and how to extract the ip address of the website from the command prompt by using the mark option. Now, you can copy that address, paste it into the browser and go to the blocked site directly. By watching this video, you can easily learn to access blocked websites by bypassing them.

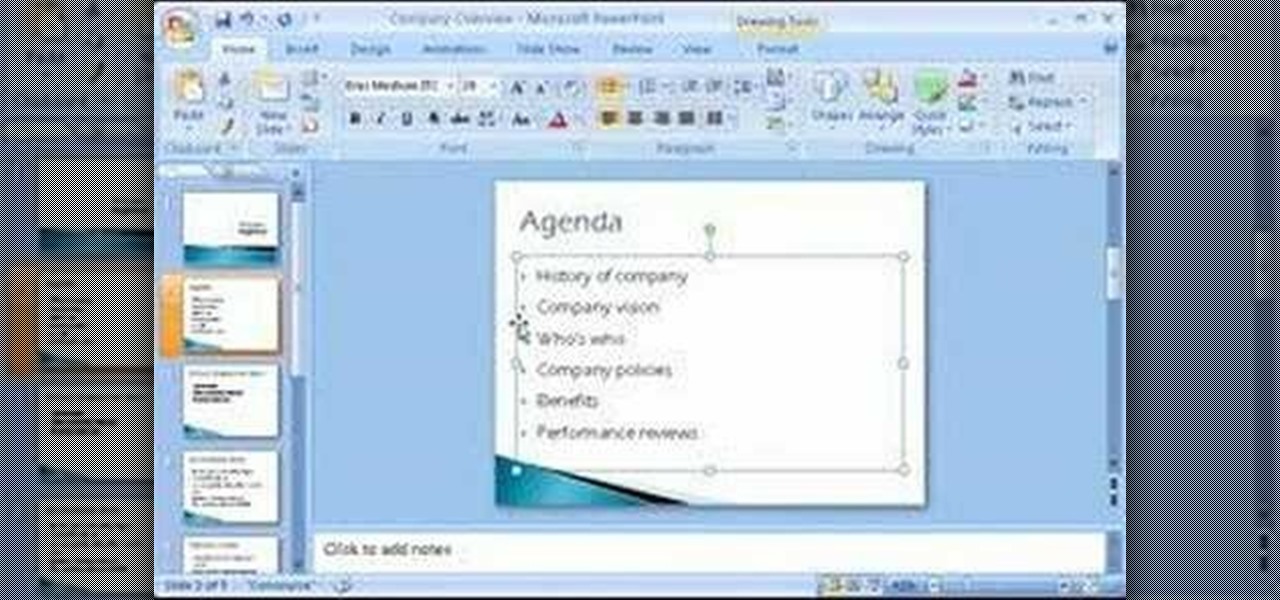
Microsoft Office PowerPoint 2007 has a new design. The new Ribbon keeps the commands that you use most often visible while you're working instead of hiding under menus or toolbars that you have to hunt for. Also, commands that you may not have known about before are now very easy to discover. When it comes to designing your slides, live preview of style galleries lets you see how things such as backgrounds and shape formatting will look before you apply them. A new SmartArt graphics feature o...

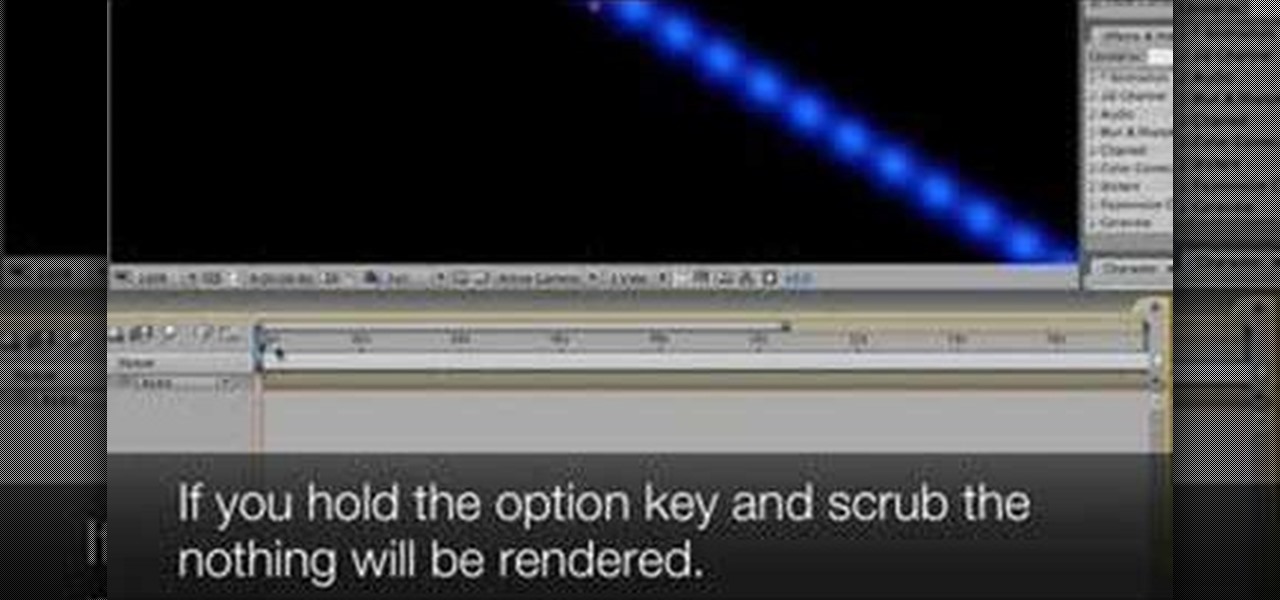
Take a look at this instructional video and learn how to scrub the audio with the program After Effects. You can go about performing this by simply holding the command key and scrubbing the timeline, then that will scrub the audio and render the video. If you hold the option key and scrub nothing will be rendered. But if you hold both the command and the option keys, no video will be rendered but you can scrub through the audio without waiting for the video to render.

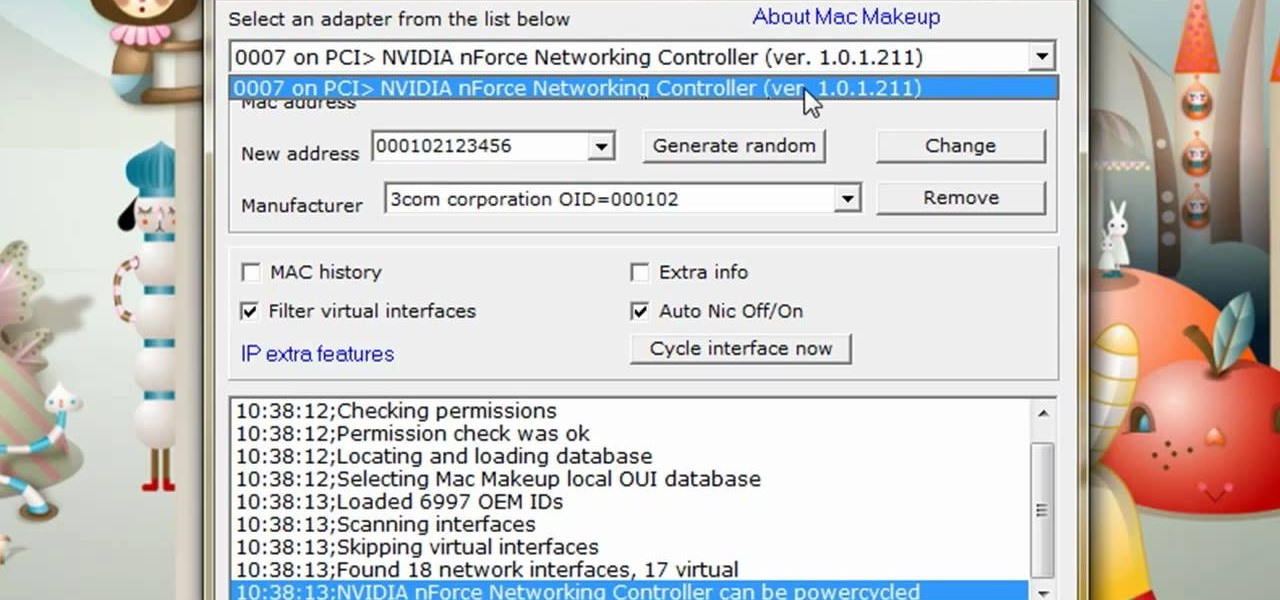
The video is about how to change the IP address. MAC address is the unique identifier a site of the most network adapters. MAC address is used to determine what IP address the computer will have and one way to change the IP address is by changing the MAC address. The method is only applicable for the windows systems and for the MAC systems you need to look at the link provided. In Windows in the start menu, type cmd in the run/search box, which will launch the command window. Type ipconfig/al...

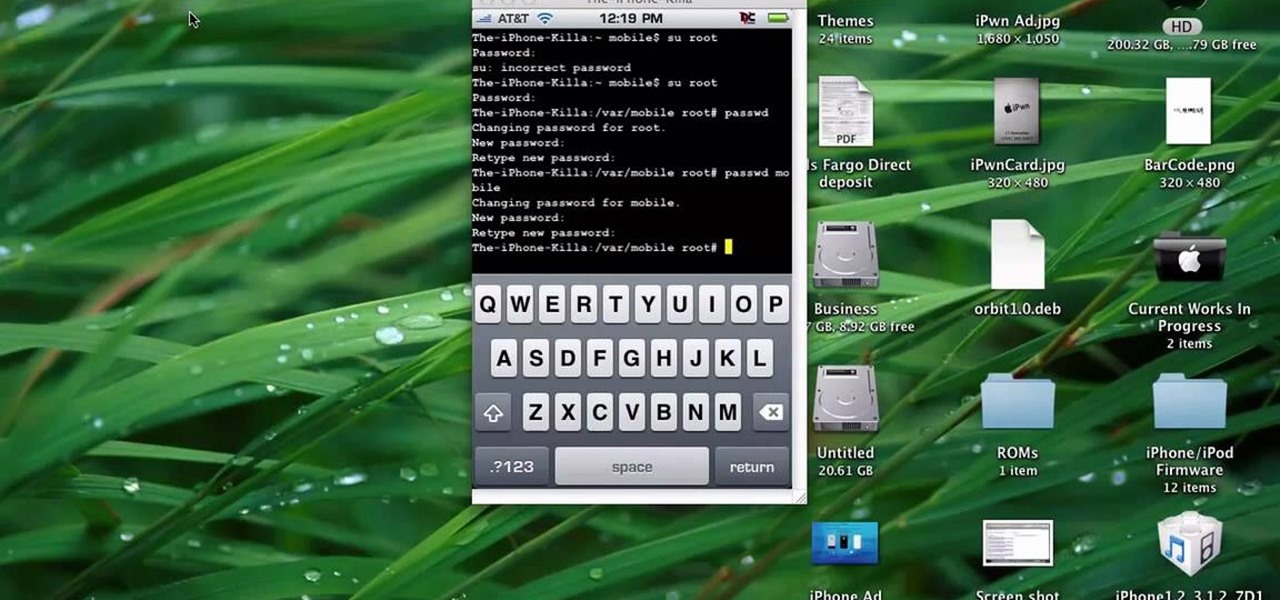
This quick tutorial runs you through a fast and easy way to make your iPhone or iPod Touch more secure. However the best security is abstinence. Just don't run the programs that leave your devices vulnerable unless you need them.

Learn to fabricate the halo and window posts with some tubing and a Millermatic welder into a dirt track racecar being built from a 1981 Camaro. The materials and tools needed for this project include a 1 3/4 x .120 tubing, an "Affordable Bender" bender, a Millermatic welder and a Hypertherm 43 plasma cutter.

Not stretching after a good run will definitively set you up for injury or muscular pain. While stretching before a workout lubricates your joints to prepare them for work, stretching afterwards helps prevent you from building too much bulk so you get long, lean muscles, and so your tensed up muscles can relax again.

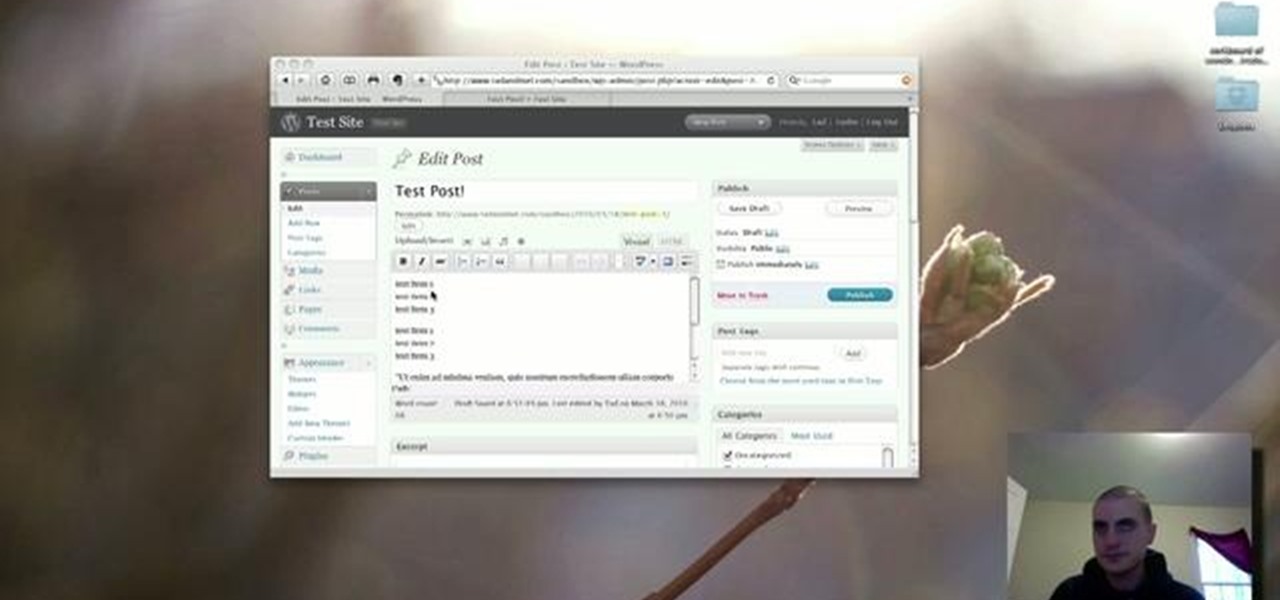
In this clip, learn how to generate ordered lists in the WordPress post editor. Every version of WordPress brings with it new features, new functions and new ways of doing things. Fortunately, the very same technology that allows an open-source blog publishing application like WordPress to exist in the first place also makes it easy for its users to share information about the abovesaid things through videos like this one. Take a look.

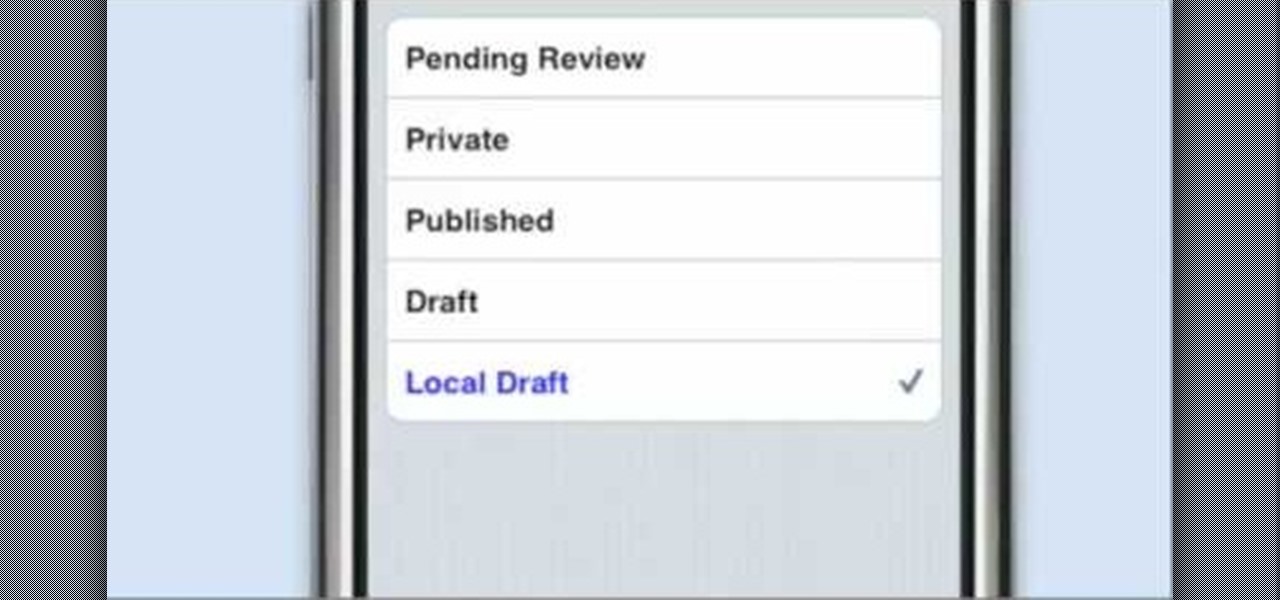
A new introduction into the iPhone community is WordPress which easily allows you to easily control things like your WordPress blog on the move. Start off by tapping in your blog details, start writing a new post with a single tap, setting your tabs or publishing data right from the main editor through this. This also allows you to add photos directly taken from your iPhone's camera, you can change your publish date and set a password on your posts to decide who has access to them. Finally yo...

This six minute video shows you how to sell your car on craigslist. First, go to craigslist.com and click on the nearest city (or country). Follow the links to list an ad for a car for sale. You will want to put the kind of car in the posting title because that is used in sorting search results. In the posting description it is important to be as specific as possible - again describing the car, giving some history of the car like if it has ever been in an accident and if you have had any work...

This will show you how to do the Lebron James Signature Move from Nike series on NBA superstars bball skills.

TWRP won't be ready for the Pixel 4 and 4 XL until months after release. But since you can already root with Magisk and tinker with the OS, you might find yourself in a situation where your phone won't boot, yet you don't have a custom recovery installed to fix it. Luckily, there's still a way around this.

One of the most common web application vulnerabilities is LFI, which allows unauthorized access to sensitive files on the server. Such a common weakness is often safeguarded against, and low-hanging fruit can be defended quite easily. But there are always creative ways to get around these defenses, and we'll be looking at two methods to beat the system and successfully pull off LFI.

The OnePlus 7 Pro is truly the best phone that the company has ever created to date — it's even one of the hottest phones around regardless of OEM. It offers an awesome display with minimal bezels, a smooth 90-hertz refresh rate, a pop-up selfie camera, and the best triple camera system in a OnePlus phone so far. It can truly compete with other flagship phones while keeping the cost down.

The main draw for Google's Pixel series is the software. It rocks a clean version of stock Android instead of a heavy OEM skin like TouchWiz, it gets frequent prompt OS updates, the camera software is downright amazing, and it has perhaps the most fluid UI of any phone. But an understated advantage of the software is how dead-simple it is to modify with root-level tweaks.

Locating and abusing files containing unsafe permissions is an easy and surefire way to elevate shell privileges on a backdoored macOS device. This time around, we'll be more aggressive and attempt to phish a user's login password by prompting a convincing popup message merely asking the target for their password.

In most macOS hacks, a non-root terminal is used to create a backdoor into the device. A lot of damage can be done as a low-privileged user, but it has its limitations. Think twice before granting a file permission to execute — an attacker might be able to convert your harmless scripts into persistent root backdoors.

It's possible to stream a MacBook's entire computer screen without using Apple's Screen Sharing application and without opening any ports on the target device. A hacker with low user privileges on the backdoored Mac may be able to view a victim's every move in real time no matter where they are.

Nearly one year after its announcement, AirPlay 2 has finally landed on iPhones everywhere. Not only can you easily control multiple speakers including Apple TVs and HomePods from your iPhone, but you can use Siri to help you get the job done. It's one of the iOS assistant's best features, and if you're running iOS 11.4 with a compatible speaker, you can try it out right now.