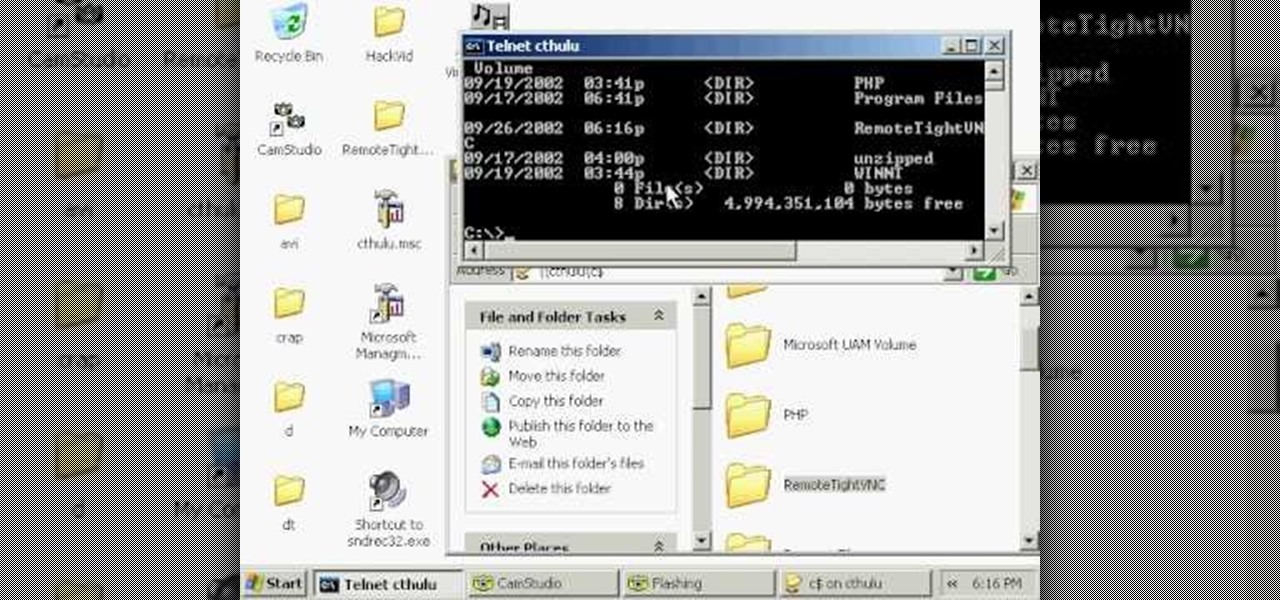
In this video tutorial, you'll learn how to install VNC, or Virtual Network Computing, remotely onto a Windows machine for GUI access. This tutorial assumes you know how to start a session and get into active command line access in a remote Windows PC. For step-by-step instructions, press play.
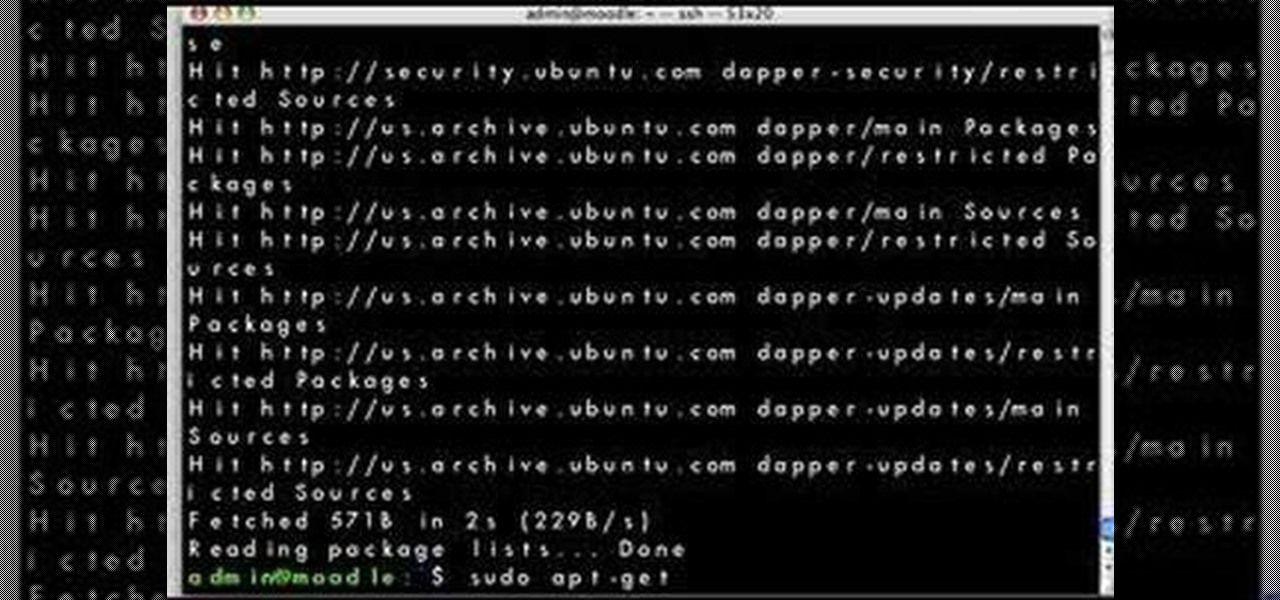
Looking for a simple way to update your Linux distribution? This video tutorial demonstrates how to upgrade your Linux distribution via the apt-get command in the terminal. To get started using the apt-get update tool, press play!

Non-linear video editing tools are great, but they're not always the best tool for the job. This is where a powerful tool like ffmpeg becomes useful. This tutorial covers the basics of transcoding video, as well as more advanced tricks like creating animations, screen captures, and slow motion effects.

In this tutorial, Gary Rosenzweig of MacMost.com shows you the basics of using the Terminal application. Learn how to navigate, list files, rename, copy and delete. Also learn some shortcuts that experts use.

With the Freeze Panes command in Microsoft Office Excel 2007, you can make sure specific rows and columns stay visible while you scroll. Take a look at this instructional video and learn how to freeze and unfreeze rows and columns, and make viewing your worksheet a snap.

This video tutorial shows how to train a dog to lay down. "Lie down" is a simple, basic, and useful word command to teach a dog.

Has your dog ever gotten off its leash, or made a quick escape from an open door? Training or teaching your pup to come to you on command is an essential part of obedience training. With a little practice, your dog will learn how in no time!

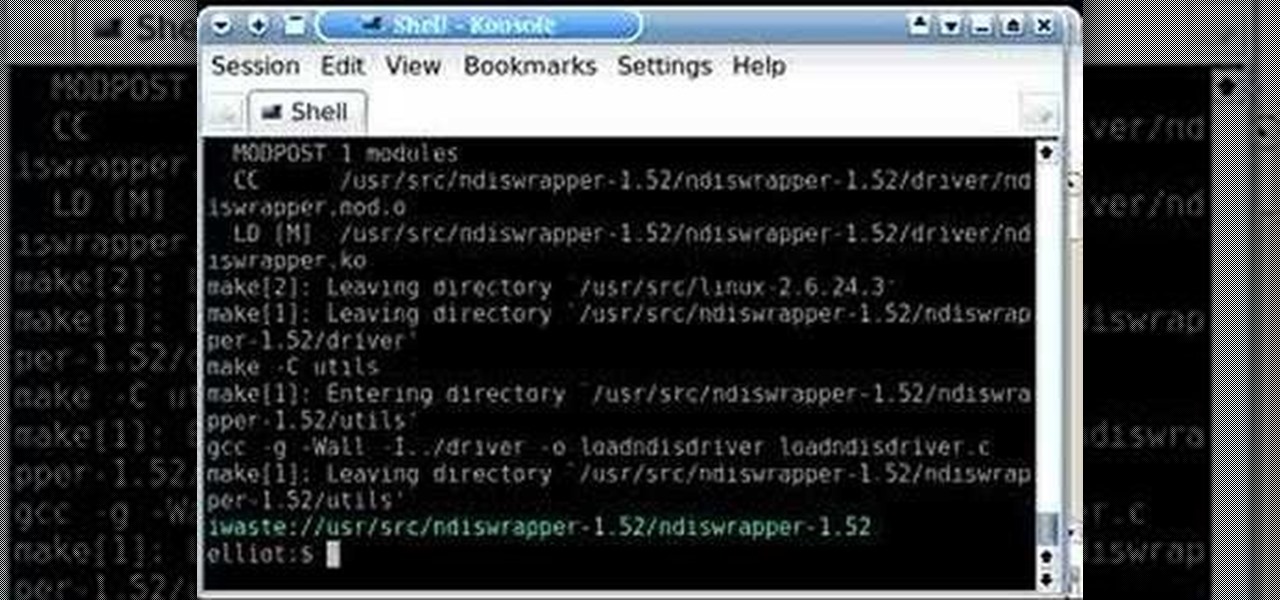
A tutorial on how to use ndiswrapper to use windows wireless drivers in Linux. A great explanation of commands without speeding through them.

Photoshop Mama shows you how to use the Match Color command in Photoshop to match the color temperature from one image to another.

This Photoshop tutorial will show you one method for changing clothing color utilizing the Select Color Range command and fine tuning techniques to use on the mask of the Hue and Saturation adjustment layer. Also shows how to clone.

In this tutorial learn how to eject a stuck CD using a terminal command on your Mac OS X computer.

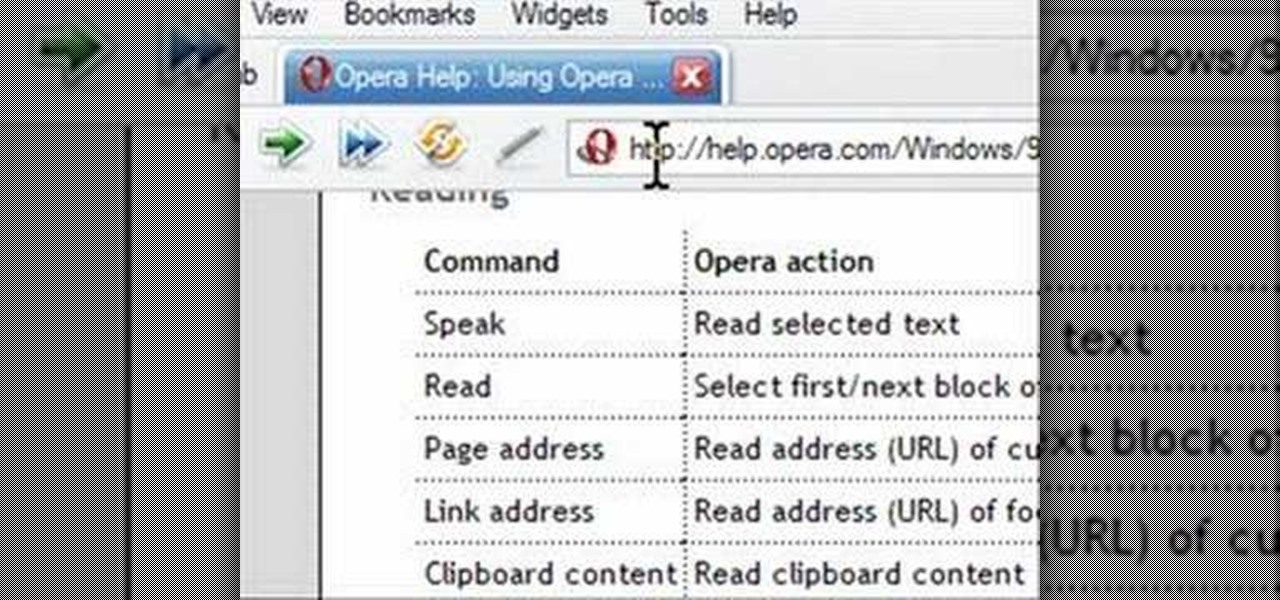
Opera has a feature where you can talk to it and it obeys your commands - and it works! No "voice training" required. Learn how to use Opera Voice.

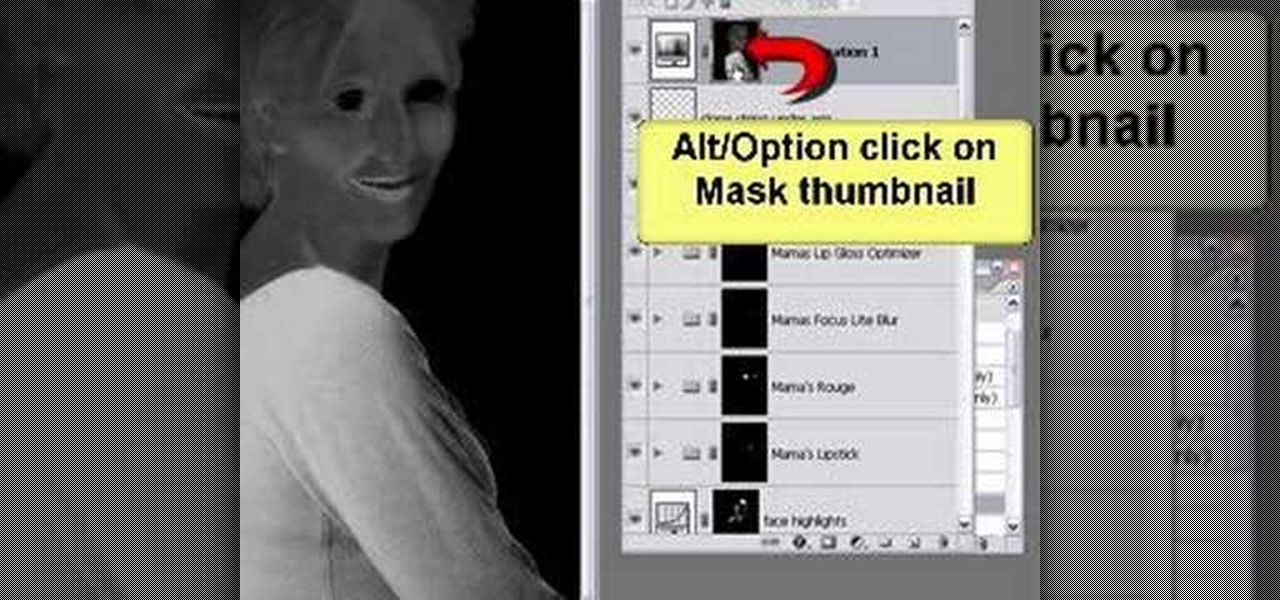
In this video tutorial you will learn to load and play actions in Photoshop CS2. Actions are sets of recorded commands. They are particularly useful to perform repetitive or multi-stepped tasks. The examples in the video are available if you are a member, but even if you're not, the process you learn is the same for any action you want to import or use.

The free download manager wget lets you download all the files on a page or directory with a single command. It also allows you to resume downloads after getting disconnected letting you start where you left off instead of starting the download at 0% again. Check out this tutorial and see how to install and use wget.

This Premiere Pro CS3 tutorial walks you through a few of the quickest and easiest methods for copying motion properties and video effects from one clip in a sequence to other clips.

The introduction of transparency has been quite controversial in print production over the past few years, though the fact is that for most transparency in Adobe files works just fine. However, those of us out there with older RIPs may have issues printing transparency. In this video you'll see how to flatten transparency in your PDF files before you ever hit the Print command.

Every time you place an image in InDesign, chances are you have to execute a fitting command to make it fit in the frame or area that you specified. In this video of the Creative Suite Podcast Terry White will show you ways to do it most efficiently. You’ll also see how to better integrate the Bridge into your workflow.

The default Photoshop commands may not be enough for your designing needs. A quick way to enhance your Photoshop's ability is to use third-party add-ons. This tutorial teaches you to download, load and use ActionFx Actions in Photoshop CS2.

Your voice is the key to unlocking many features on your iPhone. For example, you can ask Siri to send a text message to a friend, add items to a list, run a custom shortcut, or turn on your lights, but Apple does not allow you to unlock your iPhone with a Siri voice command. Instead, you can turn to a lesser-known feature to unlock your iPhone without Face ID, Touch ID, or typing your passcode.

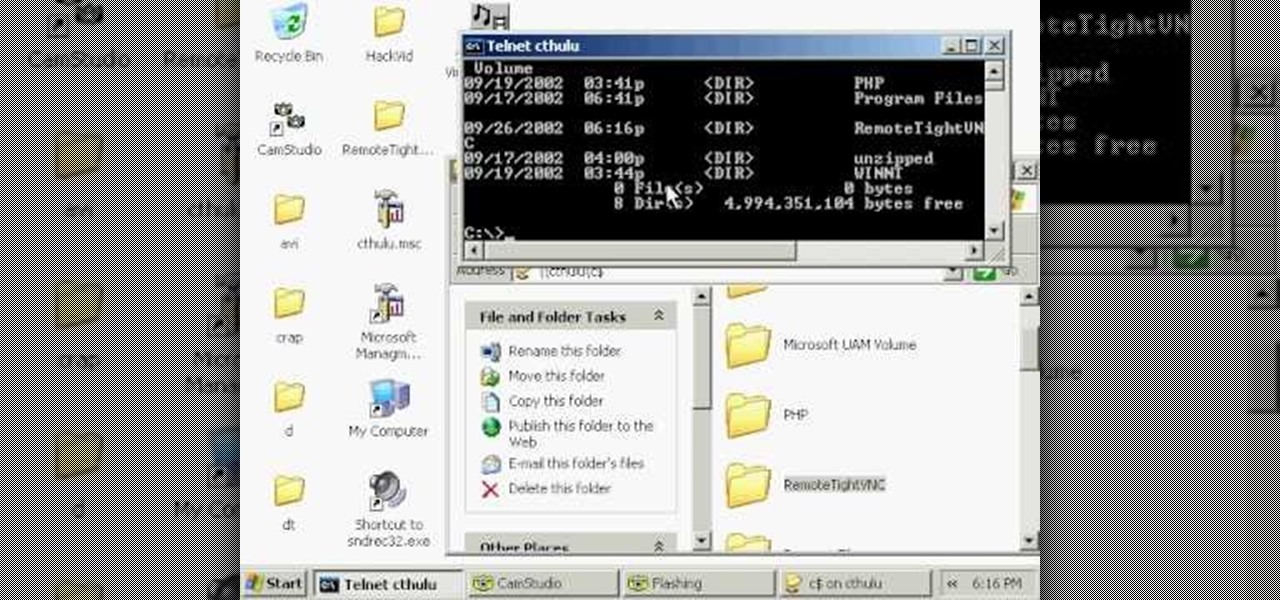
Whether you miss the good old days of Telnet or you want to know what hacking was like when security was nothing but an afterthought, Telehack is the game for you. The text-based hacking game is a simulation of a stylized combination of ARPANET and Usenet, circa 1985 to 1990, with a full multi-user universe and player interactions, including 26,600 hosts.

Compromised uTorrent clients can be abused to download a malicious torrent file. The malicious file is designed to embed a persistent backdoor and execute when Windows 10 reboots, granting the attacker remote access to the operating system at will.

With a cheap computer, smaller than the Raspberry Pi, an attacker can create a remote hacking device. The device can be attached to a target router without anyone's knowledge and enable the hacker to perform a variety of network-based attacks from anywhere in the world.

For those with small hands, smartphones have gotten out of control as of late. Nearly every flagship phone is over six inches in length, so many are forced to use phones that are too big for them and hope they don't fall. Well, thanks to one developer, using these phones can be a lot easier.

Giving up your Wi-Fi password can be giving up more control than you think. Because of the way Chromecast and other IoT devices communicate, anyone on the same Wi-Fi network as your device can often make it do whatever they want. With a script called "Cast All the Things," we can hijack a Chromecast to play nearly any kind of media with a single command in terminal.

Android 9.0 Pie moved the status bar clock from the right corner to the left to accommodate phones with notches, but there's one major downside for Samsung users: since no Galaxy phones have a notch, all this did was take away space for the notification icons that would otherwise start from the left corner.

With the number of web applications out there today, it comes as no surprise that there are just as many vulnerabilities waiting for hackers to discover. Finding those vulnerabilities can be a difficult task, but there are plenty of tools available to make the process easier. While it won't help find any zero-days, web scanners such as Uniscan will detect common vulnerabilities.

Encrypting payloads and encoding stagers are more effective against macOS than one might think. It's very easy to evade VirusTotal and macOS antivirus software using a few simple tricks.

A powered-off MacBook can be compromised in less than three minutes. With just a few commands, it's possible for a hacker to extract a target's password hash and crack it without their knowledge.

The newest version of macOS has arrived. While everyone's mind is being blown by Mojave's groundbreaking new Dark Mode, we'll be taking advantage of its insecure file permissions to establish a persistent backdoor with a self-destructing payload that leaves little evidence for forensics.

One of the most critical bugs to come out in the last five years was Shellshock, a vulnerability which allows attackers to execute arbitrary code via the Unix Bash shell remotely. This vulnerability has been around for a while now, but due to the ubiquity of Unix machines connected to the web, Shellshock is still a very real threat, especially for unpatched systems.

Developed by Open Whisper Systems, Signal is a free, open-source encrypted communications app for both mobile and desktop devices that allows users to make voice calls, send instant messages, and even make video calls securely. However, a vulnerability was recently discovered for the desktop version that can be turned into a USB Rubber Ducky payload to steal signal messages with a single click.

A powered-off Windows 10 laptop can be compromised in less than three minutes. With just a few keystrokes, it's possible for a hacker to remove all antivirus software, create a backdoor, and capture webcam images and passwords, among other highly sensitive personal data.

The internet is constantly under siege by bots searching for vulnerabilities to attack and exploit. While conventional wisdom is to prevent these attacks, there are ways to deliberately lure hackers into a trap in order to spy on them, study their behavior, and capture samples of malware. In this tutorial, we'll be creating a Cowrie honeypot, an alluring target to attract and trap hackers.

Drivers the world over are painfully aware of the inherent danger of taking their eyes off the road even for a second. In fact, according to the National Safety Council, 27% of all car crashes result from distracted driving due to attempted cell phone use. Fortunately, Waze comes with a feature that can help keep you from being a part of this grim statistic.

Every morning I head on over to my gym to start storying away classes full of people dripping in sweat. This always makes me feel super awkward because it's not exactly the most photogenic time to take a picture, and if it was me, I would probably give that person a dirty look and hope they'd just eventually go away.

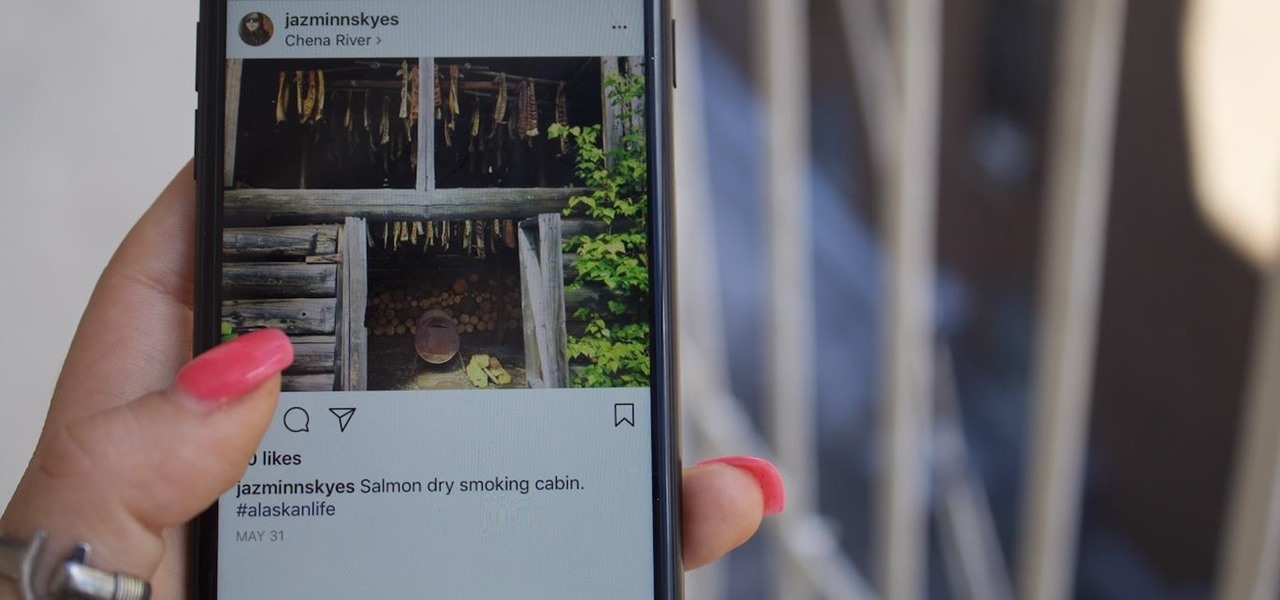
Get ready IG influencers, the Instagram promotional world as you know it is about to change. Instagram is one of the top places for influencers to make money with product promotion. So, of course, it is to be expected that these IG dominators would run into their fair share of disasters. Especially since over 90% of celebrities and influencers on Instagram don't follow FTC guidelines.

The act of liking someone's really old Instagram post is called "deep-liking," which is pretty apt if you think about it. While going "deep" into older posts on the feed of your ex or crush or whoever, your finger may slip accidentally and double-tap on a photo or video that you'd rather not let them know you're looking at.

Several Samsung phones have a feature that turns the screen black and white when the battery is getting low. This takes advantage of the AMOLED display in these devices, because unlike red, green, and blue pixels, no battery power is used to display black pixels on this type of screen.

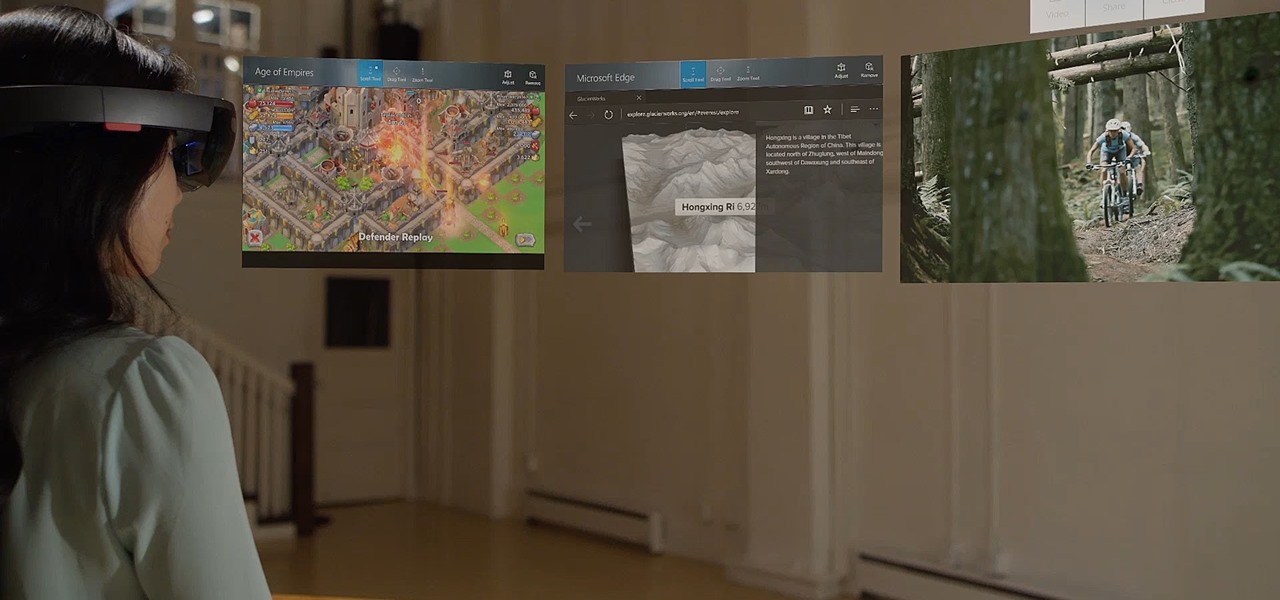
Microsoft released a robust version of the HoloLens when shipping the developer kits, but there's still lots of room left to grow. Today, they've released the first update to Windows Holographic, the operating system of the HoloLens, with a whole bunch of cool new features like voice commands and app multitasking.

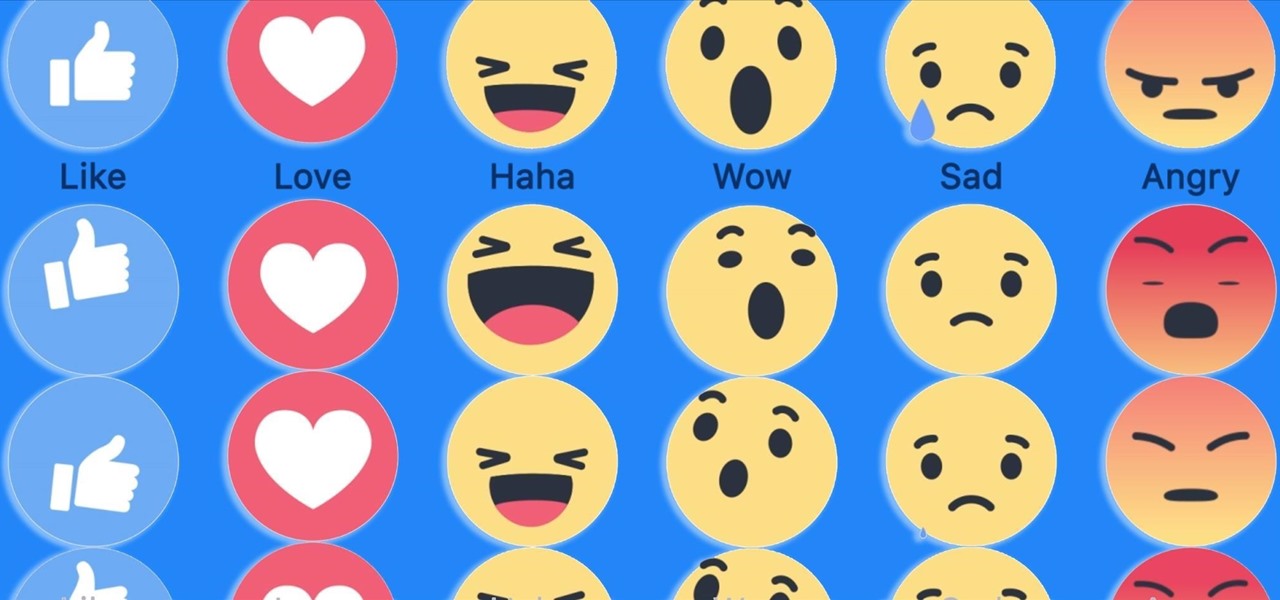
Have you ever run across a Facebook post that you don't necessarily want to "Like," but you're not really passionate enough about to bother stringing together a couple words for a comment? Well, you're in luck, as Facebook added five new "Reactions" that let you do more than just like a post, and they're now live for everyone.