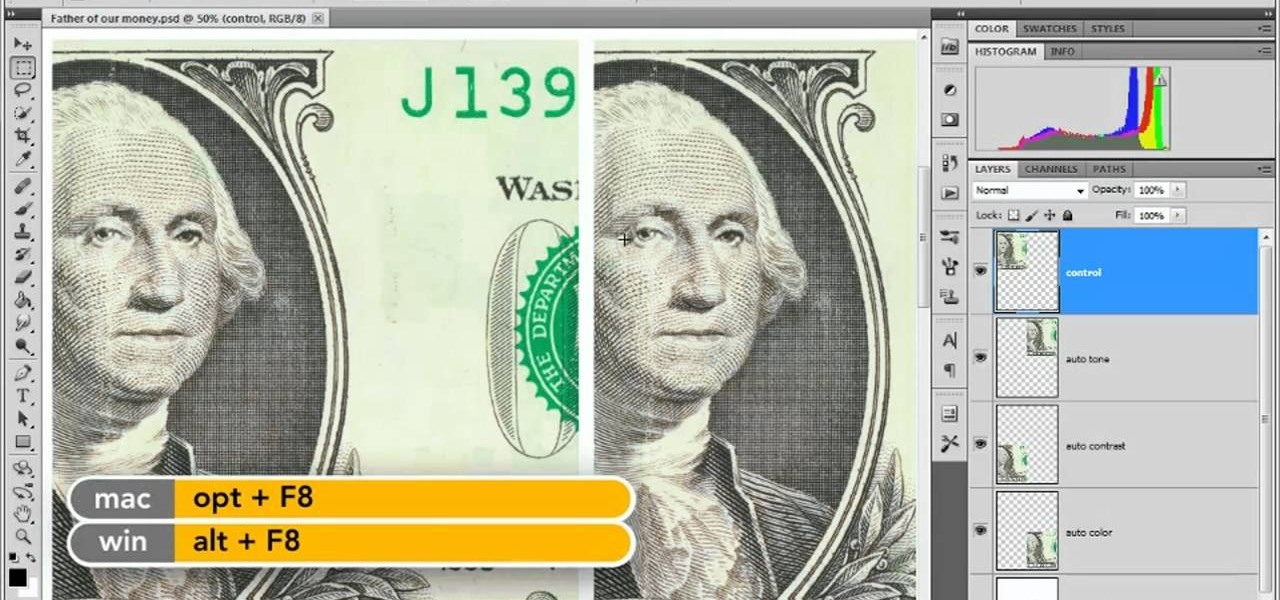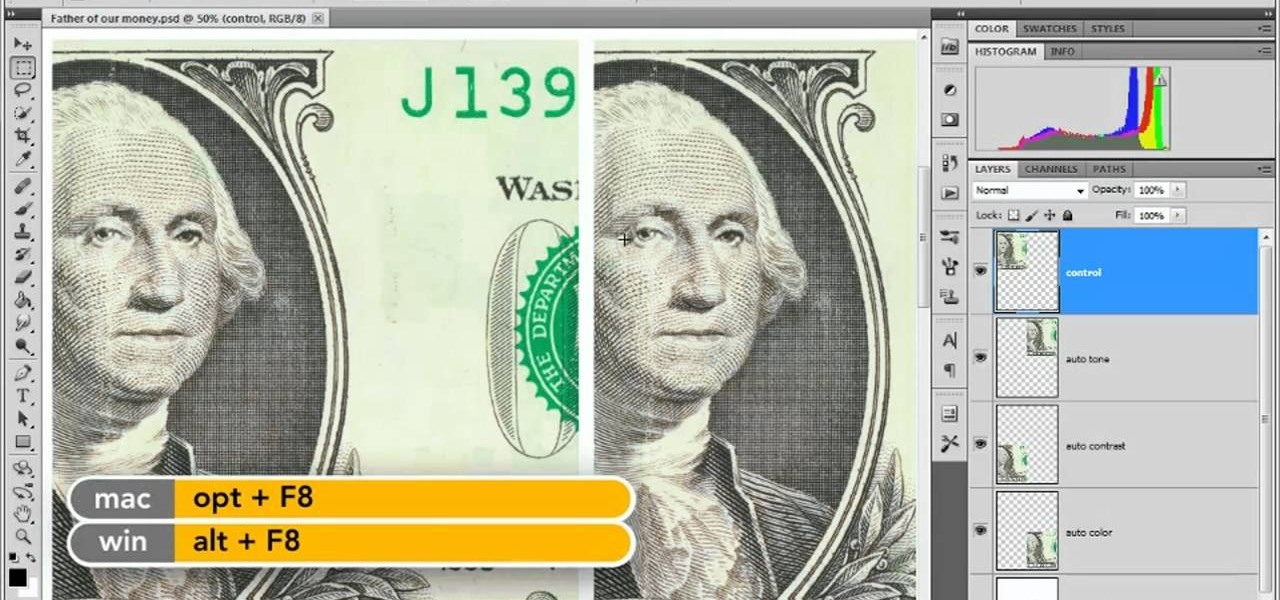
In this clip, you'll learn how to use the Auto Levels and Auto Curves commands to correct the luminance of an image on a channel-by-channel basis in Adobe Photoshop CS5. Whether you're new to Adobe's popular raster graphics editor or a seasoned designer looking to better acquaint yourself with the new features and functions of the latest iteration of the application, you're sure to benefit from this free software tutorial. For more information, watch this video guide.

Both Biedermeier and post-impressionist artists painted and sculpted in 19th century Vienna. Learn about a few famous artists with this free art history video series.

Arguably, "Stay" is the most important command you can teach your dog. When you train your dog to stay, be low to the ground and eye-to-eye level with them. Zak George show how to use a clicker and food treats to demonstrate how to teach a dog to stay. Also learn how to correct your dog when it breaks the stay command.

Here they are used to find anime episodes and movies, but you can use advanced Google commands to perform more dynamic searches on Youtube. Learn how to narrow or expand your searches and search for multiple items simultaneously.

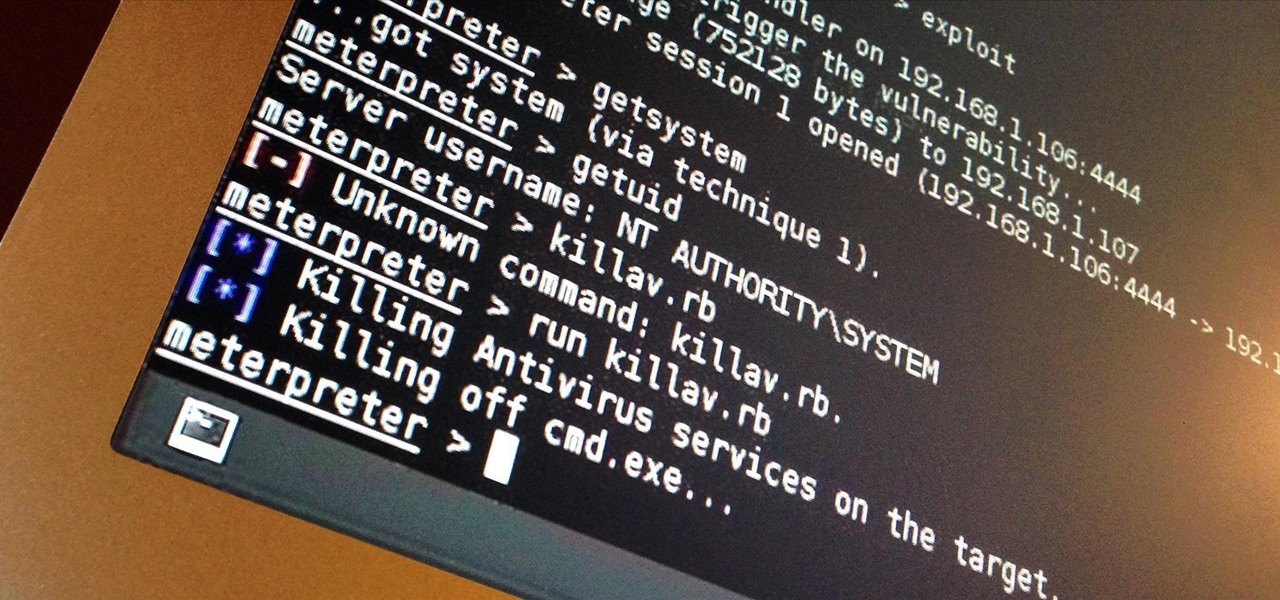
PowerShell Empire is a post-exploitation framework for computers and servers running Microsoft Windows, Windows Server operating systems, or both. In these tutorials, we will be exploring everything from how to install Powershell Empire to how to snoop around a target's computer without the antivirus software knowing about it. If we are lucky, we might even be able to obtain domain administrator credentials and own the whole network.

Hello my anxious hackers, the week has started and here we begin a new series that I think will help many here and not only, for those that have the opportunity to follow our tutorials but they are not yet part of the community.

Welcome back, my hacker novitiates! In an earlier tutorial, I had introduced you to two essential tools for cracking online passwords—Tamper Data and THC-Hydra. In that guide, I promised to follow up with another tutorial on how to use THC-Hydra against web forms, so here we go. Although you can use Tamper Data for this purpose, I want to introduce you to another tool that is built into Kali, Burp Suite.

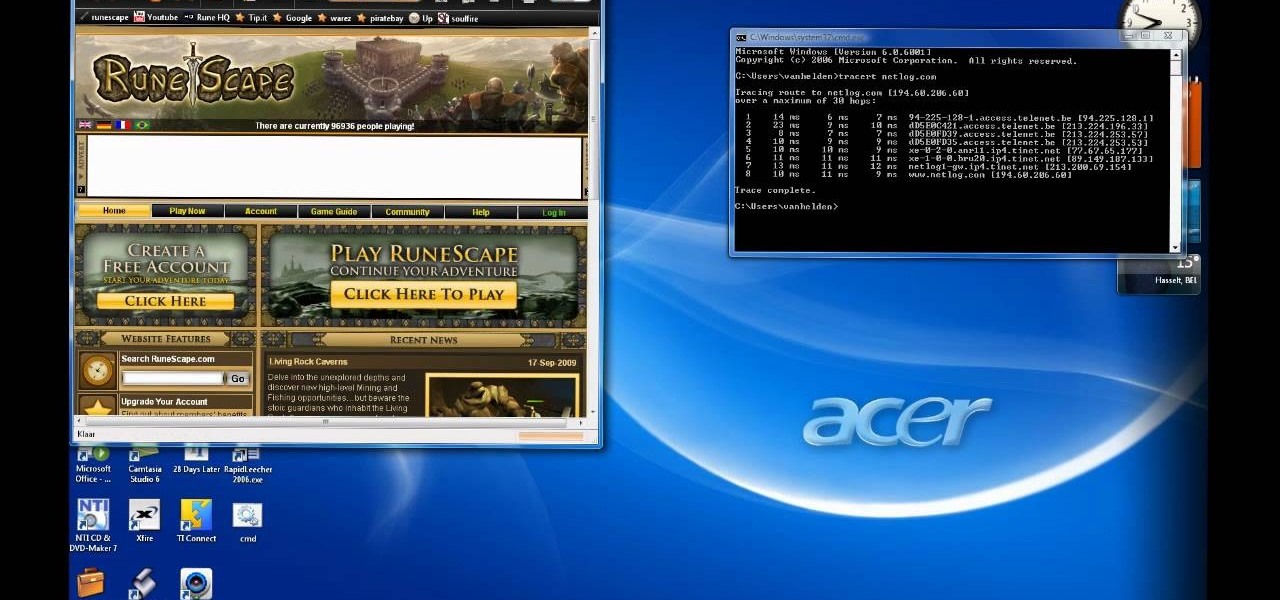
Every Windows system includes command prompt; and while a lot of people on Null Byte and WonderHowTo in general know how to use it, some people don't know anything about it, even how to access it.

Trying to focus on studying for your Stats final in the library but getting a serious ADD spell? Then make use of your time - while having a little fun with whoever else is in the library - by hacking into your computer's command prompt.

By enabling the dev console in Fallout 3, you can give yourself exactly the same kind of superuser game access that the developers have when they are working on the game. Here's an extensive list of console commands you can use to get all sorts of great stuff.

In this video tutorial, we learn how to customize the appearance of the default Microsoft Windows command prompt. For all of the details, including step-by-step instructions, and to get started customizing your own Windows command prompt, watch this home-computing how-to.

If you like shortcuts, then this shortcut for Windows XP should peak your interest. In this video, you'll learn the exact steps to adding a command prompt shortcut option to the Windows Explorer right-click menu. This allows you to access hidden functionality by adding a right-click option to select "Command Prompt Here" from the menu in Windows Explorer on a directory.

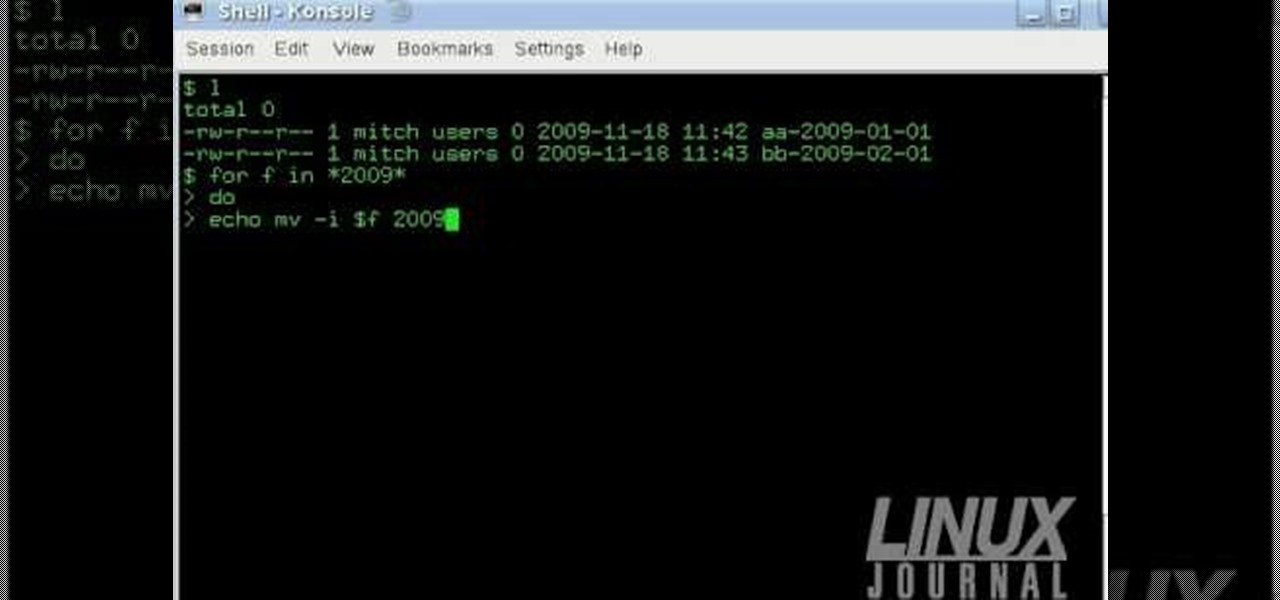
The Linux command shell provides a very powerful interface for doing various system tasks. This video explains with an example, how to use a bit of programming techniques to batch rename files with similar naming conventions.

The come command is the most valuable training tool for your dog. Learn the importance of dog training and how to get your dog to come with this free dog training video series.

A lot of time can be wasted performing trivial tasks over and over again, and it's especially true when it comes to hacking and penetration testing. Trying different shells to own a target, and testing out privilege escalation commands afterward, can eat up a lot of time. Fortunately, there is a tool called One-Lin3r that can quickly generate shells, privesc commands, and more.

With a tiny computer, hackers can see every website you visit, exploit services on the network, and break into your Wi-Fi router's gateway to manipulate sensitive settings. These attacks can be performed from anywhere once the attacker's computer has been connected to the router via a network implant.

Google, Amazon, and Facebook are always listening. But what's worse? Hackers are listening, too. Windows PCs are particularly vulnerable, but with a few simple commands, a remote attacker can even take over the microphone on someone's Mac computer, streaming audio and listening to private conversations in real time without the victim's knowledge, abusing an overlooked security consideration.

Screenshots taken from a compromised computer can provide hackers with access to private emails, photographs, and information found in sensitive documents. This data can be used by the attackers to build profiles of a target for social engineering attacks and blackmail or even just to release the information out in the wild.

PowerShell Empire is an amazing framework that is widely used by penetration testers for exploiting Microsoft Windows hosts. In our previous guide, we discussed why and when it's important to use, as well as some general info on listeners, stagers, agents, and modules. Now, we will actually explore setting up listeners and generating a stager.

Google Assistant is a handy little feature at most of the time, but it's upping the ante in honor of April Fools' Day this year.

The Pixel and Pixel XL both use AMOLED screens, which are noted for their deeper blacks and sharper contrast ratios when compared to traditional LCD panels. However, AMOLED displays still have one fairly major downside, and that's the fact that they're vulnerable to screen burn-in.

Hello fellow Nullbytiens, I'm Washu, a long time commenter but first time poster. Today we'll be making an IRC bot, if you haven't seen OTW's post about the new IRC channel I would encourage you to go check it out. He does a good job at explaining what IRC is and how to get set up.

Do you ever thought that you can't control an Internet disconnected system? I saw a funny video in Chema Alonso's youtube channel (A well-known hacker of my country and creator of Fingerprinting Organizations with Collected Archives among other security tools), and decided to post something similar.

Want to get even this Halloween? Want to scare somebody with nothing but a few lines of code? Here's how it can be done...

I've done numerous tutorials in Null Byte demonstrating the power of Metasploit's meterpreter. With the meterpreter on the target system, you have nearly total command of the victim.

In this tutorial, learn how to get your dog up and moving with the release command. Whether you need your pup to get off of the sofa, or just want them to walk out of a command like "sit" or "stay", check out this video.

Do you need to create graphics for video editing systems like Final Cut Pro, Avid, or Adobe Premiere? Are you looking to get more from Apple Motion or Adobe After Effects? Then you need to learn Adobe Photoshop.

The future is here! Your Android phone can respond to a wide variety of voice commands - and not just to call people, you can use voice commands to send e-mail, search for directions or find the nearest gas station!

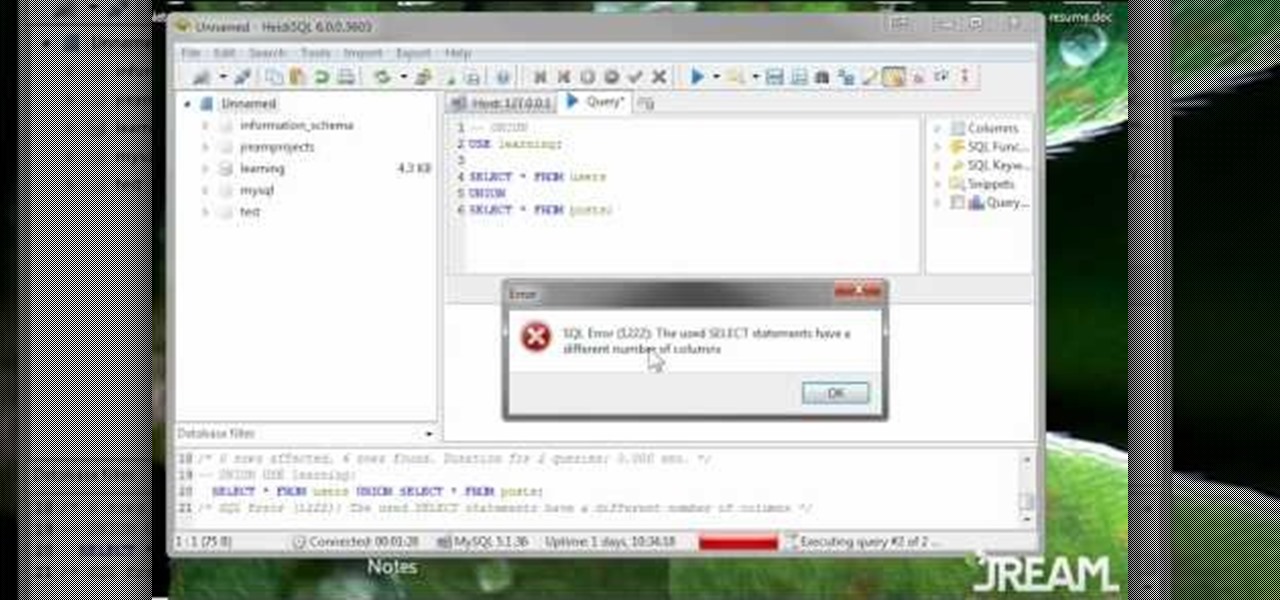
When you use the UNION command, you are stacking one result set on top of another. This is slightly different from the JOIN command, and this video is here to explain what the difference is and the best way to use UNION in your own MySQL database programs.

Cortex Command is a great little indie strategy game which gives you a series of missions to complete. This walkthrough shows you how to successfully accomplish the bunker mission in Cortex Command. Hint: it's all about having enough rockets to launch!

Go hands free by using voice commands on your HTC 7 Trophy! This Windows Phone 7 owner's guide will teach you everything you'll need to know. For all of the details, and to get started using voice commands on your own HTC 7 Trophy, watch the clip!

In this clip, you'll learn how to issue voice commands to a Garmin 3790T portable GPS units. Not only are voice commands convenient, they're also safer than attempting to physically interact with your GPS while driving. For complete instructions, take a look.

Learn how to use the Web Capture and Compare Documents commands in Acrobat 9 Pro with this tutorial selected by experts at Adobe. You can use this command to compare the differences between two versions of a web page. First, you have to convert the pages to PDF files using the built-in Convert-to-PDF command in Acrobat 9. Then, select the Compare Document command from the Document menu, choosing the settings. The program will run through the two files, compare them and present the results in ...

Center yourself and your geometry, in modo that is! The Center command is a crucial component for all modelers. The modo center command allows you to center any piece of geometry along the X Y or Z axis. Learn the ins and outs of the modo Center options here.

If you're a Win XP user you know frustrating it can be using the command prompt... especially if you need to type a long string of commands, or worse, a subdirectory. Tekzilla shows you how to do this easily

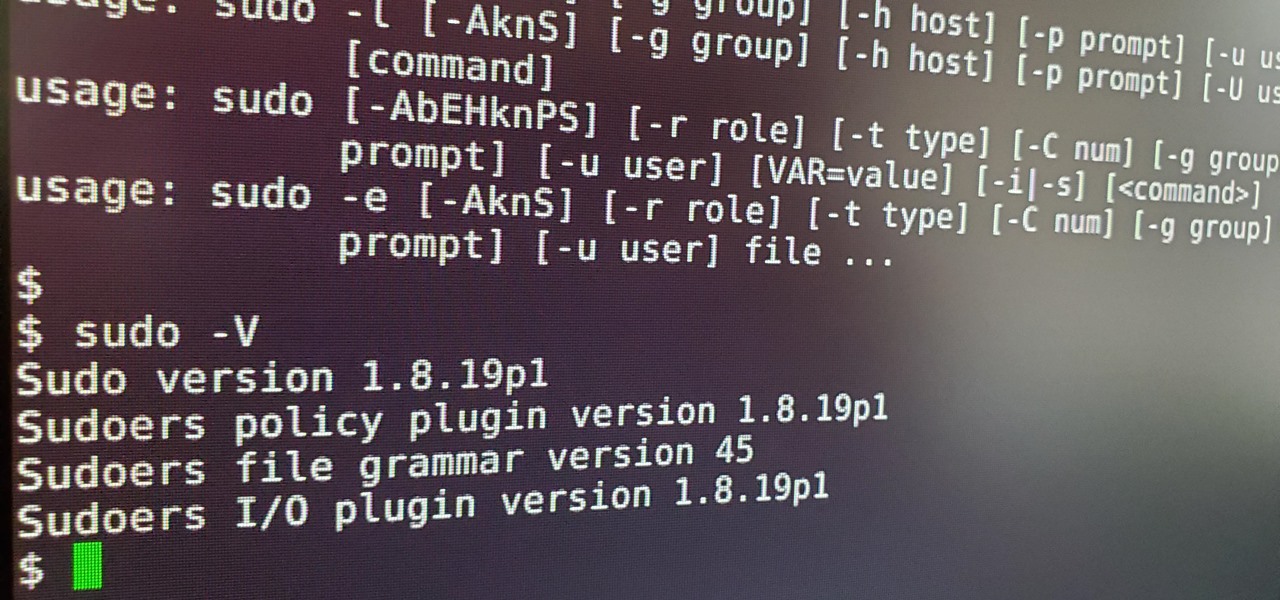
Anyone who has used Linux long enough is familiar with sudo. Short for superuser do (or substitute user do, depending on who you ask), it allows users to run commands as either root or another user on the system. From a hacker's point of view, sudo is often all that stands between them and root access. We'll be exploring an older vulnerability in sudo that allows a user to run commands as root.

With a simple social engineering trick, sudo passwords can be captured in seconds without the target's knowledge. The passwords can then be saved to a file or exfiltrated to another computer on the network.

Instagram has extensive tools built in for creating and editing posts and Stories, but there could always be more. Third-party apps can help you add photo and video effects for even more visually stimulating content, as well as create announcements, text-based images, and everything in between. However, now that Shortcuts exists on iOS, you may no longer need all those extra apps on your iPhone.

With the rise of website encryption (TLS), sniffing passwords from network activity has become difficult. However, it's still possible to quietly exfiltrate a target's network traffic in real time to extract passwords and sensitive information. Pertaining to macOS, there are two methods for retrieving traffic from a backdoored Mac.