The docking accessories available to owners of the Motorola Droid Bionic unlock several different functions dormant in the Android smartphones. The Vehicle Navigation Dock allows you to easily access Verizon's GPS system on the go, or give vocal commands so that you stay safe and handsfree with the Droid Bionic. The HD Station Dock allows you to connect your smartphone to a TV and view photos or use applications on the big screen. This guide by Motorola shows you how to access the different f...

In this tutorial, we learn how to jump start a car using another car's battery. First, you will need to position the two cars in front of each other. Turn off both of the cars completely, then attach the jumper cables. You need to connect the positive post of the dead battery to the positive post of the live battery. After you do this, Then, wait for a couple of minutes while the cars are connected and the battery is receiving power. Now, start the car that has the bad battery and it should s...
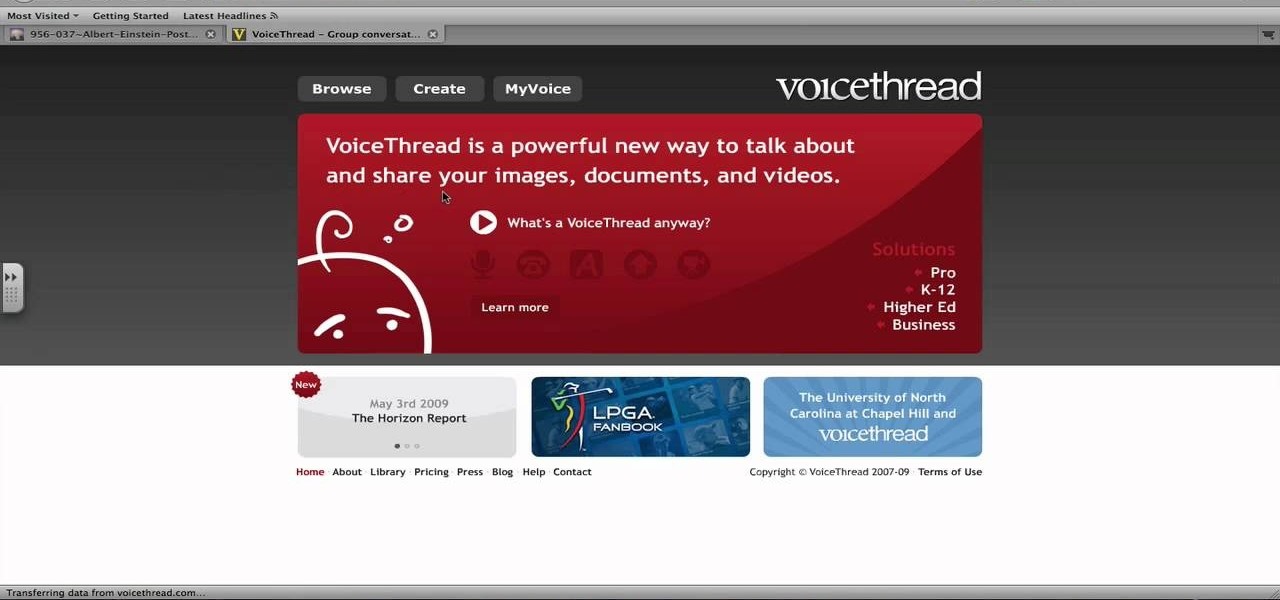
This video tutorial is in the Computers & Programming category which will show you how to use the online discussion site Voice Thread. Voice thread enables you to create an online discussion with your students. In this video you will learn how to open an account, how to open a thread and how to post a comment on it. Go to the site. On the right hand top corner you will find a coffee cup. If you click on that, it will ask you for a username, password and email for opening an account. After you...
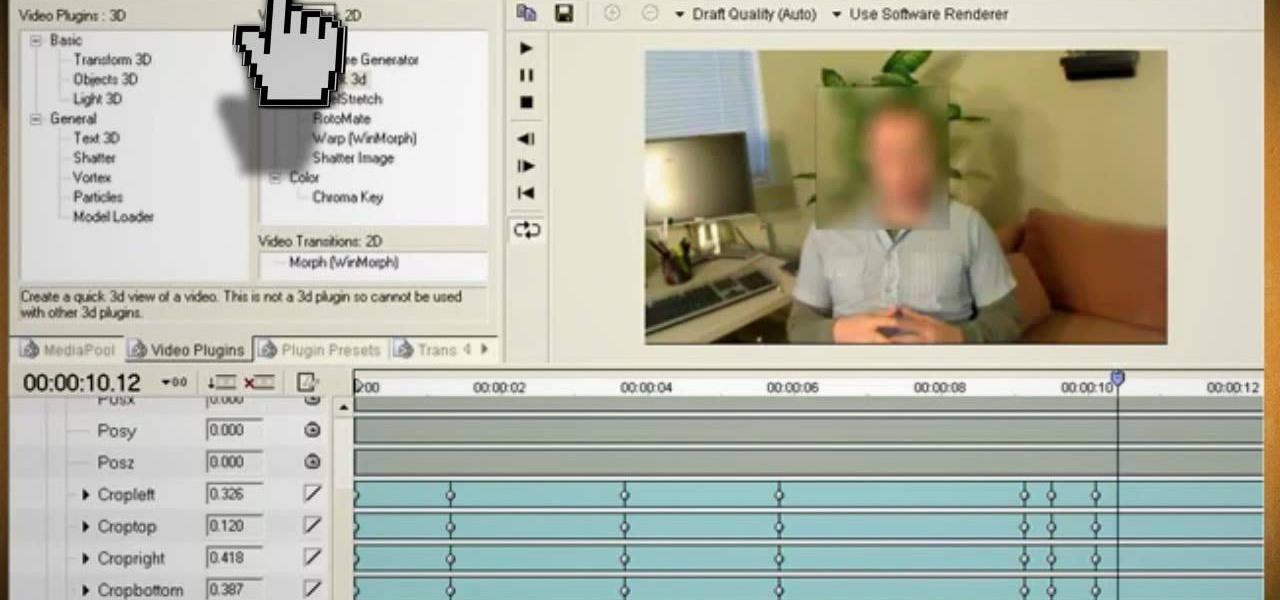
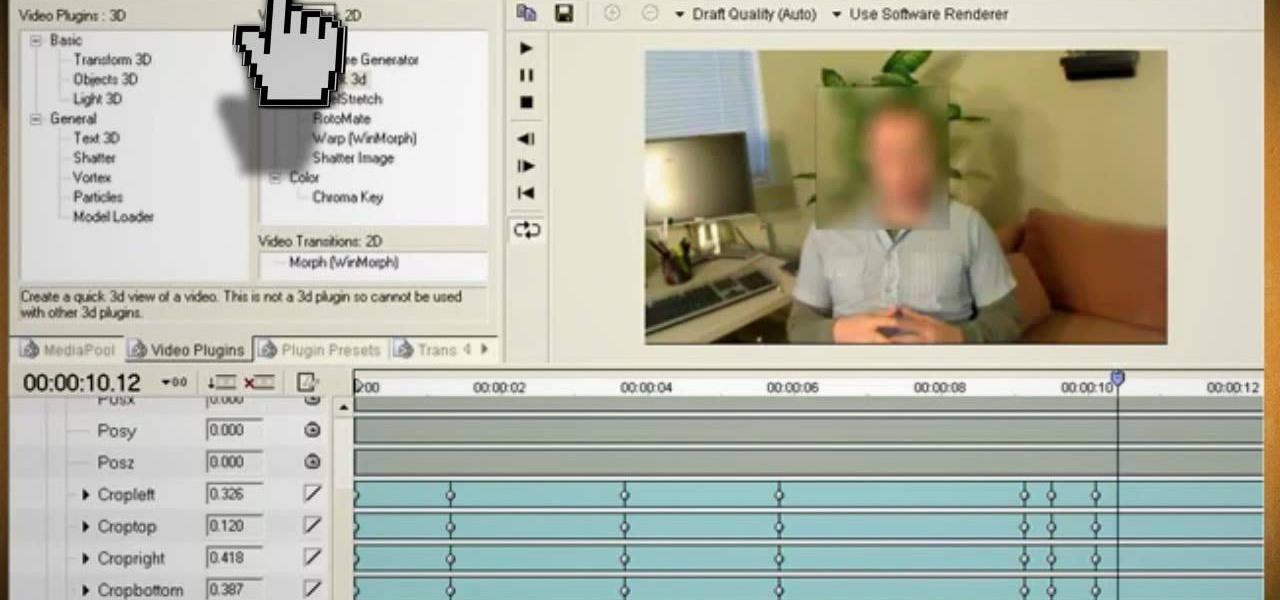
Watch this video and learn how to protect your identity on the internet. This clip will help you learn how to blur out your face and alter your voice when posting videos on the web, where your identity is an important secret. Stay anonymous while portraying your opinions. This software can also be used to avoid release issues with strangers in the backgrounds of your videos. Preventing passers by from having there picture posted with your opinions opening you up for legal action. This can als...
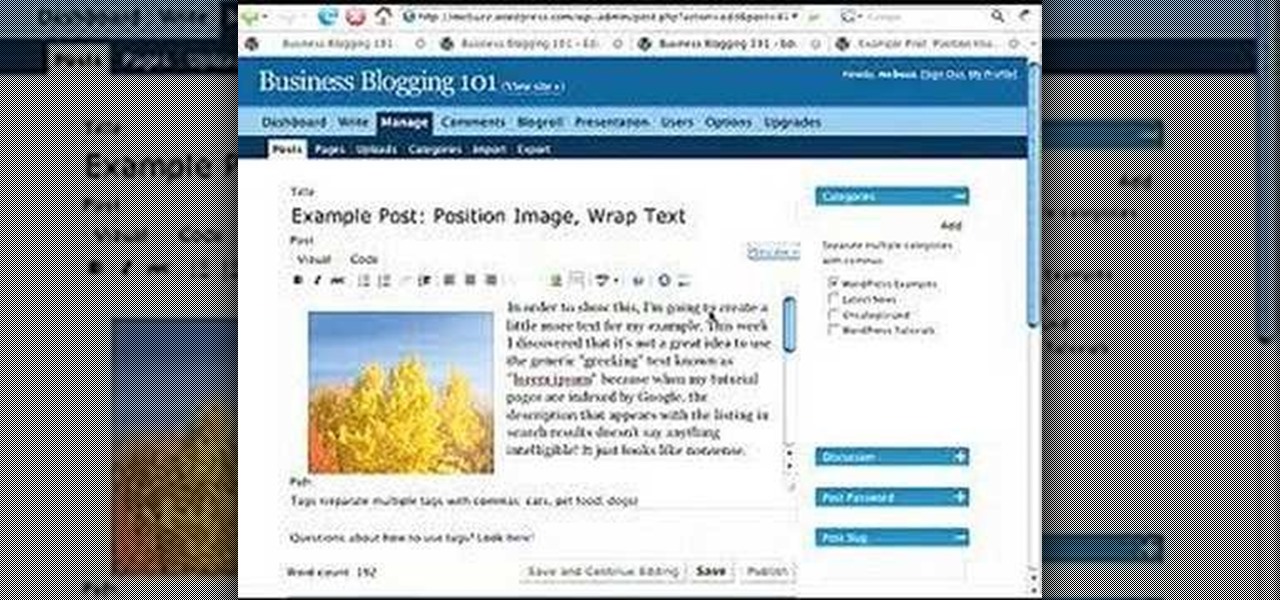
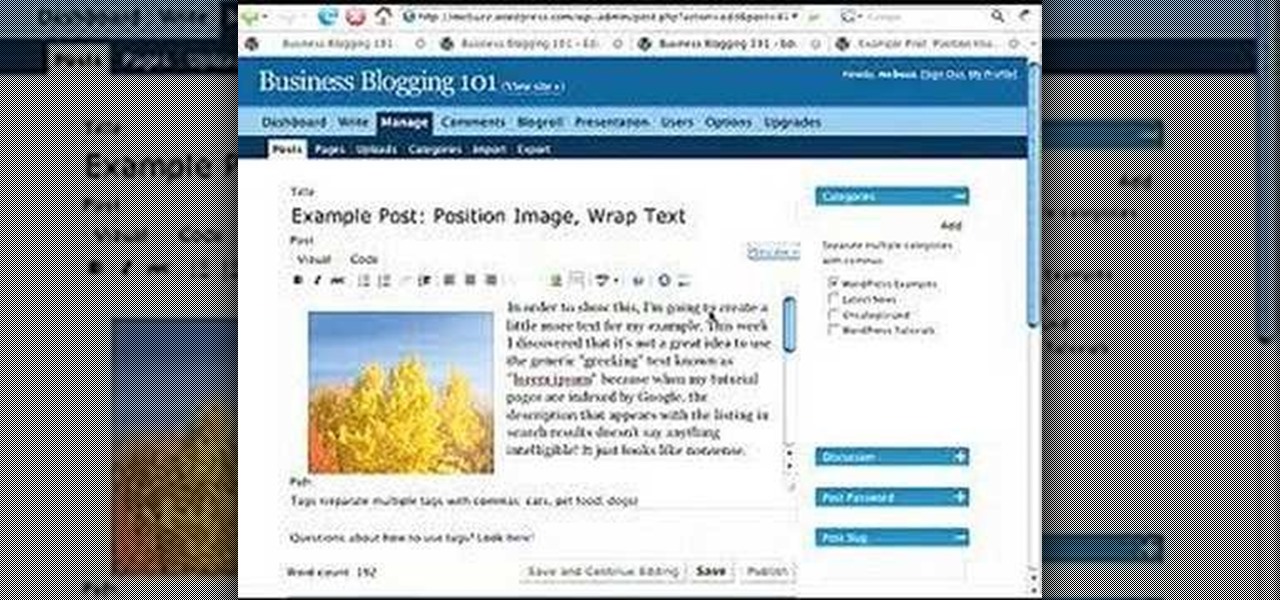
This video describes how to wrap text around an image in Wordpress. The video starts with an example describing the technique, showing a video left justified with text flowing around the right side of the image and then vice-versa. He then goes into the Wordpress editor and inserts an image into a new post. After the image has been inserted into the post, the video shows how to set the image alignment to the left. Once this setting is complete the text will then wrap around your image.
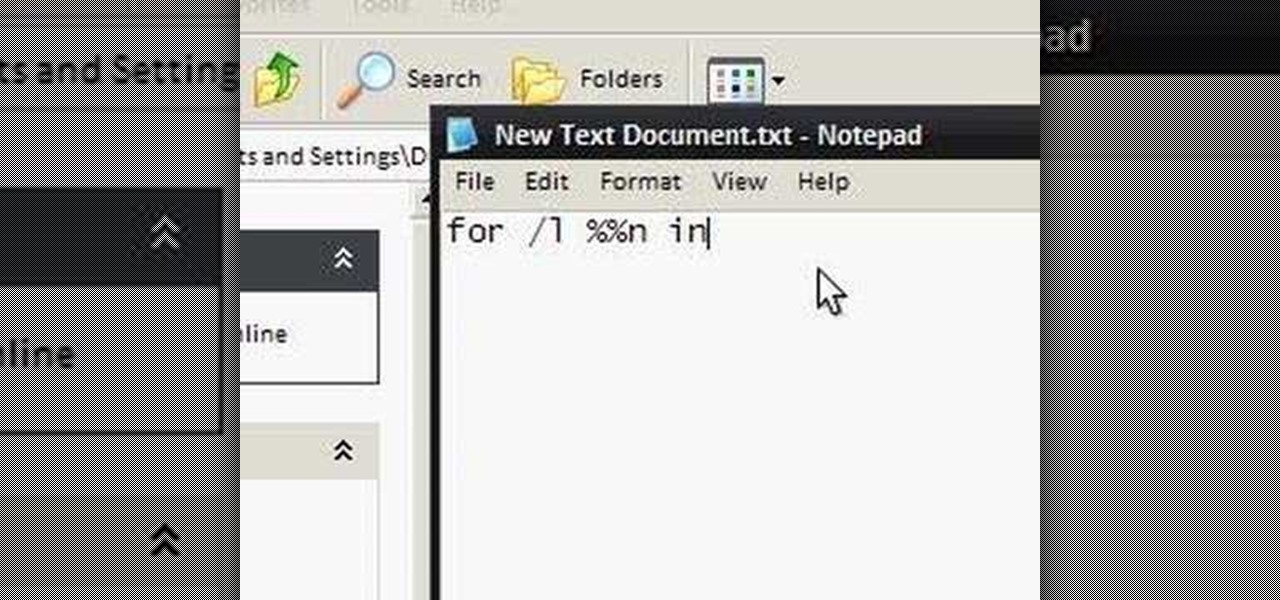
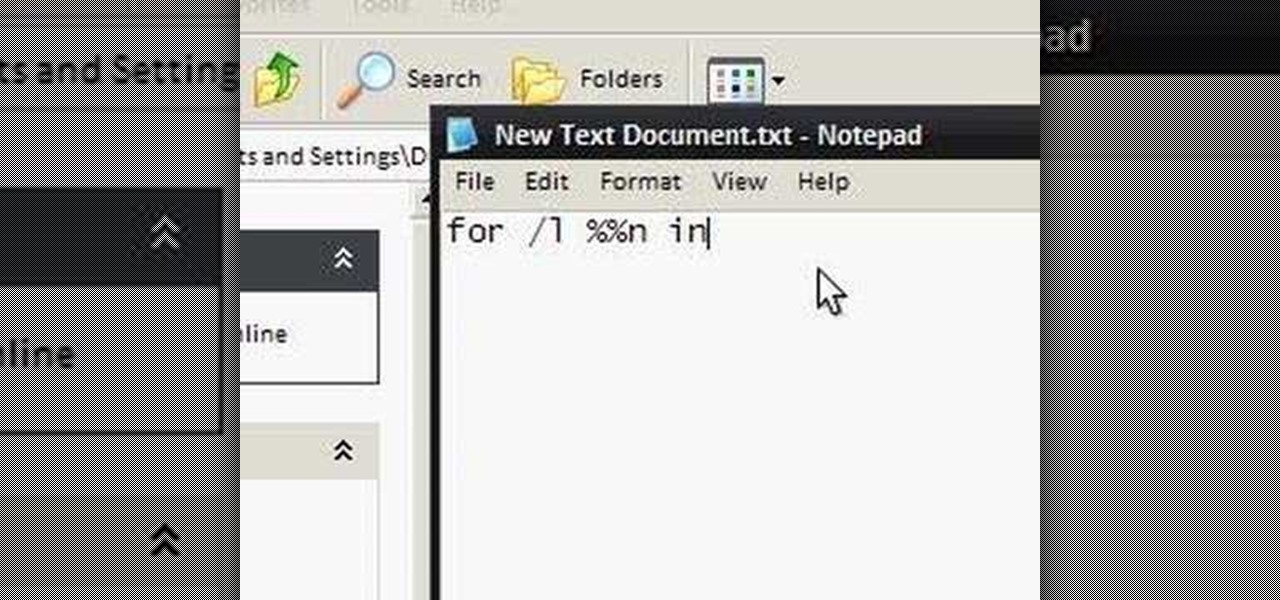
To make an annoying batch file to prank your friends you need to first right click on your screen and go to New and then Folder. In this New folder make a Text file and type in "for /l %%n in (1,1,10) DO md %%n" and that is it. Now this will loop from 1 - 10 and make a new folder for whatever n is. You can change the command if you would like to! Now, you can change this text file to 'Folder' and allow for this to be clicked. You can change the number "10" to any large number so the folder co...

This video demonstrates how easy it is to take a screenshot with shortcuts in Mac OS X. Pressing Command-Shift-3 will take a screenshot of the entire screen, while Command-Shift-4 will let you take a screenshot of just a selected area of the screen instead. For the latter, once you use the shortcut, your mouse pointer will turn into crosshairs, and you would click on one point of the screen, then drag and release your mouse to take a capture of the selected area.

Open your program to a new live set. By using three keys (in Ableton Live), Command (Ctrl), Shift and t, you can create a short cut. Create two new midi tracks making one for (side chain) bass and one for (side chain) kick. To rename a track choose the two keys Command (Ctrl) and r. Next, you can load up the presets, located on the side bar list, one a bass, and, then a basic kick drum by opening up impulse, electronics and Tremor 1994. Now create a couple of patterns. To do this go an empty ...

Only those with supreme command of the force can properly wield a light saber. But anyone in Terraria can have a phase blade, if they know the crafting recipe. Watch this video to learn how to make a phase blade.

The yearly Victoria's Secret Fashion Show is a fashion show unlike any other. Rather than stick thin waifs floating down the runway with "I'm hungry" plastered all over their gaunt faces, Victoria's Secret showcases models with healthy, toned bodies who command the stage with their cheeky and flirty antics.

Want to get all of the possible cheats for your Sims 3 game? This tutorial shows you how to open the cheat box, and then what commands you can enter to get more money, happiness for your sims and move objects wherever you want.

Suspect you might have a trojan virus installed on your computer? Find out! With the NETSTAT and FPORT commands, it's easy! So easy, in fact, that this home-computing how-to from the folks at Britec can present a complete overview of the process in just over five minutes. For more information, including step-by-step instructions, take a look.

In this video, we learn how to train legs to avoid failure using post exhaust training. First you will do a hack squat, which is where you will hold dumbbells and place your heels on a step, then squat down through the heels. Keep your chest up while doing this and you will work your butt, hamstrings and lower back. The next exercise you can do is a front lunge, which includes you lunging to make a 90 degree angle alternating between legs. The last exercise you can do is to hold a bar and squ...

This clip presents a general tutorial on how to work with and embed HTML code into your WordPress posts and pages. Every version of WordPress brings with it new features, new functions and new ways of doing things. Fortunately, the very same technology that allows an open-source blog publishing application like WordPress to exist in the first place also makes it easy for its users to share information about the abovesaid things through videos like this one. Take a look.

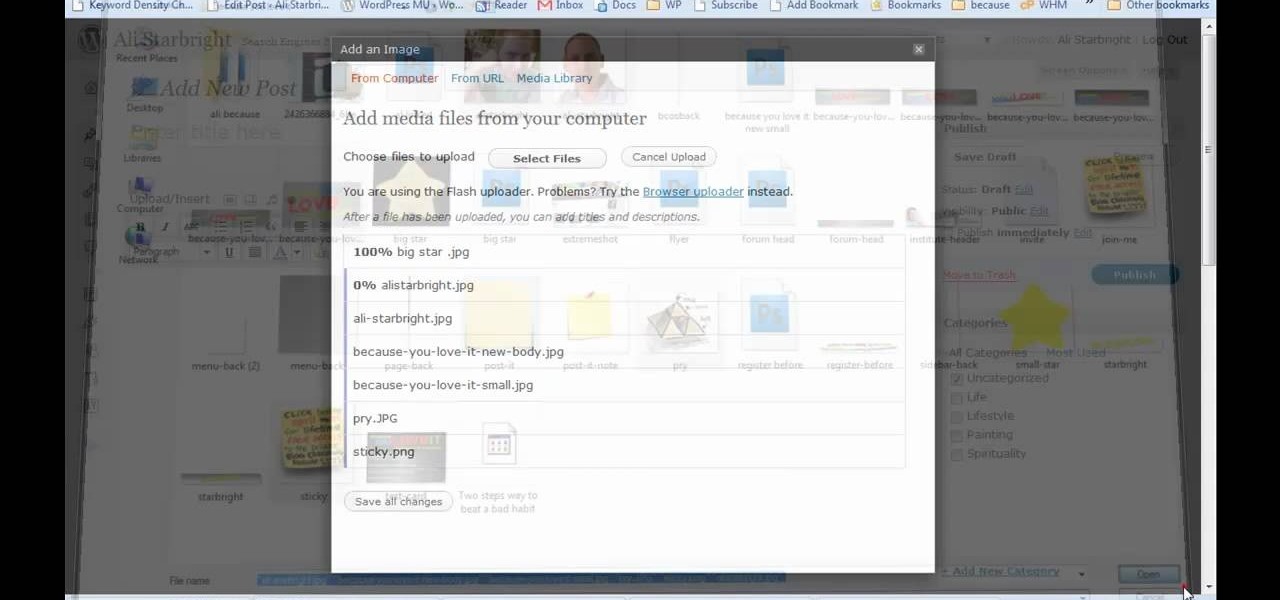
If you need to display thumbnails on a WordPress page and link the smaller thumbs to the original larger pictures, this post shows the process involved, using the Lightbox plugi,n which creates a special overlay effect when an image link is clicked on. Every version of WordPress brings with it new features, new functions and new ways of doing things. Fortunately, the very same technology that allows an open-source blog publishing application like WordPress to exist in the first place also mak...

First of all you need to work around the stitch that you have made in the previous row. To make this front post double crochet you have to first loop over the yarn on the hook. Now pass this into the first stitch of the previous row at the bottom. Go around the stitch to the back and from there you have to come back again to the front. Now yarn over and pull it through the loop. Again yarn over and pull it through the two loops as shown. Again yarn over and pull it through the last two loops ...

This video shows the method to use glue-in bails and caps and Morano glass bead to make a simple Christmas tree ornament. Apply adhesive to the post on the glue-in cap. Apply enough adhesive so that the cap makes good contact with the Morano bead and does not ooze out from the sides. Insert the cap into the Morano glass bead and put it upright until adhesive sets on the bead. Put adhesive to the post on the bail. Put it into the bead and leave the adhesive to set. Put the ribbon through the b...

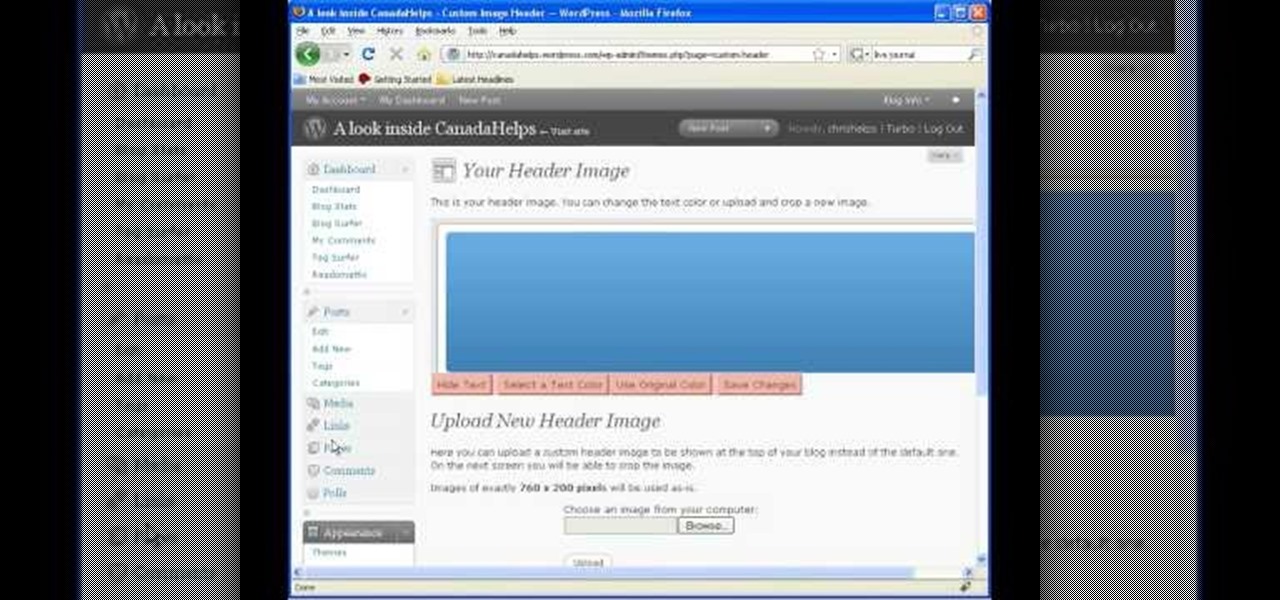
In this video tutorial, viewers learn how to start and set up a free blog. Viewers will learn how to setup a free blog for a charity, make a blog entry, edit and customize a blog and share a blog with their network. A blog is a online journal that provides the reader with regular posts on various topics. Three of the most popular blogging sites are: Blogger, Word Press and Live Journal. When creating a blog, keep the posts short and meaningful. Try to engage the reader. Update your blog regul...

Elijah from 360 Degree Social gives a tutorial on how to block specific people from seeing your Facebook posts. When someone you don't have in your inner circle, sometimes you don't want them to see everything that you do on Facebook. You go into the upper right hand corner and click on Account, then click on Profile Information. It used to say Status updates, but now says Posts by Me. After choosing the Custom options, you can type in a "friend's" name and they won't see any of those status ...

In this tutorial, Josh Millward teaches us how to post pictures onto a Facebook account. First, log into your Facebook account. Once you're logged in, click on your profile and click "photos". Choose where you want to upload the photo to, you can upload it to an existing album or you can upload to a new album. You can choose which uploading tool you'd like to use. Browse through your files and choose the pictures you want to load into your album. Now click "upload" after agreeing to the terms...

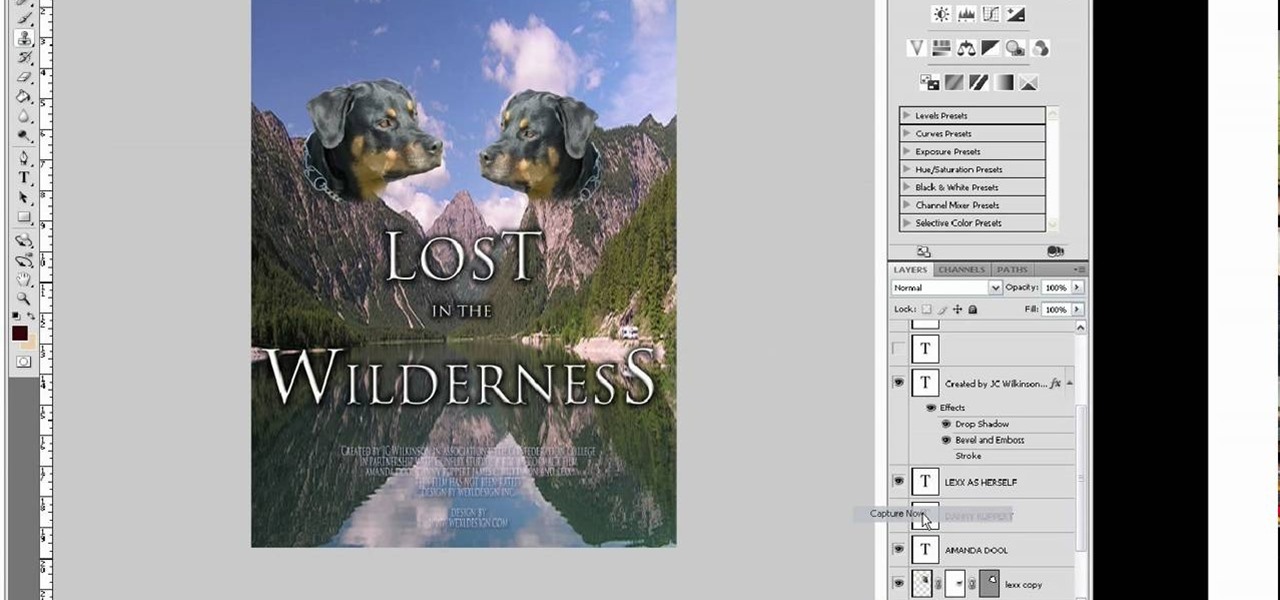
Are you in production for the next big blockbuster film? Well you might need a movie poster and this video will help. This video will show you exactly how to conjure up a custom movie poster using Adobe Photoshop CS4.

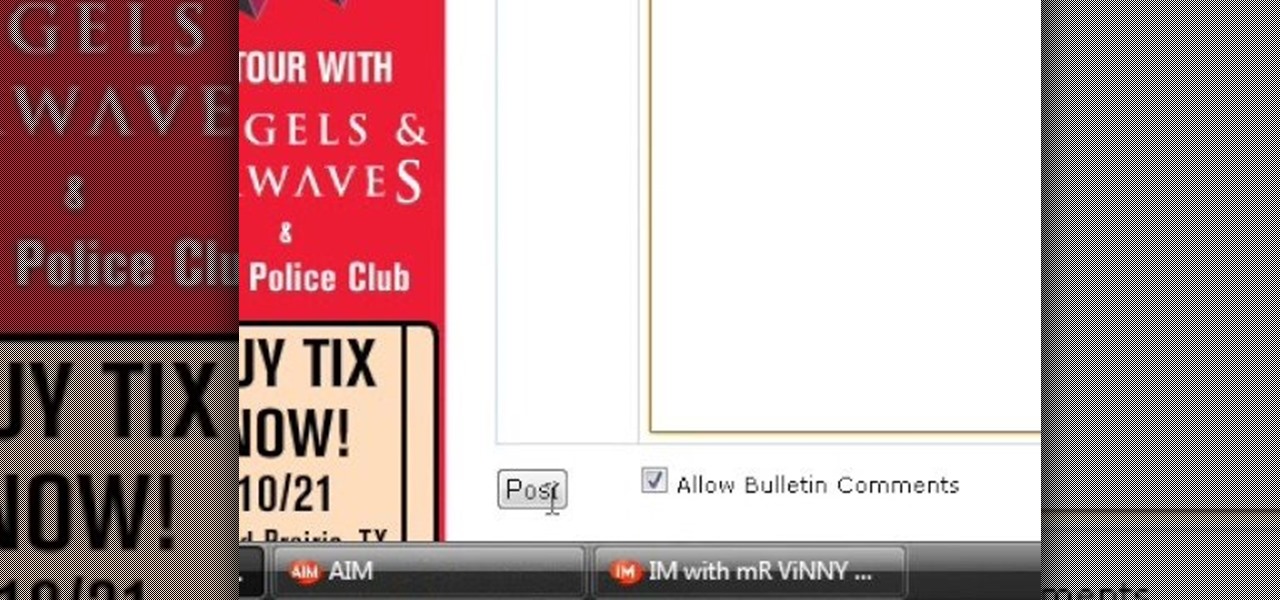
This video explains how to bold, italicize, underline or center text in a MySpace bulletin to those of us who are used to simply pressing a button in Microsoft Word. The instructor explained and demonstrated how to post in each of these styles in a clear and concise manner. In order to include one of these styles in your post, you must bookend the text your want formatted with codes to start and end the formatting. For example, to bold the phrase "I'm done!" you would enter the following text...

Ryan instructs you how to post pictures on Facebook. 1. Go to groups and choose which groups you want to post pictures.

For all you Facebook-addicts out there (or anybody else that needs to access blocked websites anywhere they want), this is a video that you will want to watch. In just a minute and thirty seconds, any ordinary person can learn how you can access any website they want anywhere they want, bypassing any blocks and firewalls that the network administrator has put up to stop users from getting to their desired website without using complex computer commands or other complicated methods.

Learn how to install Aircrack on your iPhone to hack into almost any WiFi network. First download Aircrack from iHackMyi, then follow these steps:

Watch this software video tutorial to learn how to control full-screen playback with keyboard commands in VLC Media Player. The tips in this how-to video will help you easily use VLC Media Player shortcuts to make full-screen playback more convenient.

USB flash drives are great for moving files on and off of a linux server, but how do you do it? This quick tutorial shows you how easy it is!

These are some great ways to finish off walking your dog - the military finish, the sit command and more! This video shows you how easy it is to get your dog to heel.

The Bridge CS3 is loaded with new features and performance enhancements. Some of the new features aren't as obvious. In this video we'll take a look at the New Synchronize Window command as well as some other hidden features in the slideshow area.

Wi-Fi networks come in two flavors: the more common 2.4 GHz used by most routers and IoT devices, and the 5 GHz one offered as an alternative by newer routers. While it can be frustrating to attack a device that moves out of reach to a 5 GHz Wi-Fi network, we can use an Alfa dual-band adapter to hack Wi-Fi devices on either type of network.

If left unattended, a hacker with a USB Rubber Ducky and physical access to the computer can infiltrate even the most secure computer. Such attacks often go undetected without the use of a tool like USBRip, which can provide you with assurance that your device hasn't been compromised.

Samba can be configured to allow any user with write access the ability to create a link to the root filesystem. Once an attacker has this level of access, it's only a matter of time before the system gets owned. Although this configuration isn't that common in the wild, it does happen, and Metasploit has a module to easily exploit this security flaw.

Correctly identifying the underlying technologies that run on a website gives pentesters a considerable advantage when preparing an attack. Whether you're testing out the defenses of a large corporation or playing the latest CTF, figuring out what technologies a site uses is a crucial pen-tester skill.

Passwords on Windows are stored as hashes, and sometimes they can be tough to crack. In certain situations, though, we can get around that by using the hash as is, with no need to know the plaintext password. It's especially interesting if we can manage to get the hash of an administrative user since we can then authenticate with higher privileges by performing an attack known as pass the hash.

The next libSSH or OpenSSH exploit may be just around the corner. Keep your SSH service out of Shodan's database before hackers find new ways to bypass the password protecting the server.

A lot of people still trust their web browsers to remember every online account password for them. If you're one of those users, you need to adopt a more secure way of managing passwords, because browser-stored passwords are hacker gold mines. With a USB Rubber Ducky and physical access to your computer, they can have a screenshot of all your credentials in their inbox in less than 60 seconds.

Hacker's are always looking for new ways to exploit systems and exfiltrate passwords, even in hashed form. Sophisticated brute-force attacks powered by high-end GPUs can perform millions of password attempts per second. But Ubuntu and Debian users aren't completely helpless. There are ways to harden the hashed password to better defend against Hashcat attacks.

Websites are often misconfigured in ways that allow an attacker to view directories that are not ordinarily meant to be seen. These directories can contain sensitive information such as private credentials or configuration files that can be used to devise an attack against the server. With a tool called Websploit, hackers can scan targets for these hidden directories without difficulty.

Before you can dive into customizing your OnePlus 6T, you must take the initial step of unlocking the bootloader to gain the ability to install TWRP, Magisk, custom ROMs, and other mods.

Facebook added a new feature that lets you post 3D versions of your portrait mode photos for all your family and friends to see on their smartphones, computers, and virtual reality goggles. These new 3D photos add a whole new dimension to your images with movement and more depth.