Instead of using Photoshop, why not give Apple's Aperture a try? Aperture is designed more for post-production work for professional photographers, letting you cull through shoots, enhance images, manage massive libraries, and deliver stunning photos.

This instructional photography video explains how to problem solve small product issues. Two ways to tackle a particular challenge is through pre-production and the other in post-production. There are many different ways a photographer can approach and deal with a challenge. The more knowledge you have about different methodologies about photography, the better and easier you will be able to solve those problems when they occur.
On your MobileMe Gallery Homepage, your visitors can see all of the albums that you posted for them to view, but if there are photo albums that you don't want everyone to see, you can simply hide the album from Apple's MobileMe Gallery Homepage. This video tutorial will show you how to do it, right from your Mac or PC, with Internet of course.

If you're creating a series of movies, you can use a video podcast to share your movie with team members and friends. A video podcast can be a series of videos you post to a website over time. Others can subscribe to your podcast and watch your latest movies whenever you add new episodes. Preparing a movie to be a video podcast is easy to do from iMovie.

All you need is some old discs and some other supplies to craft this incredible decluttering device.
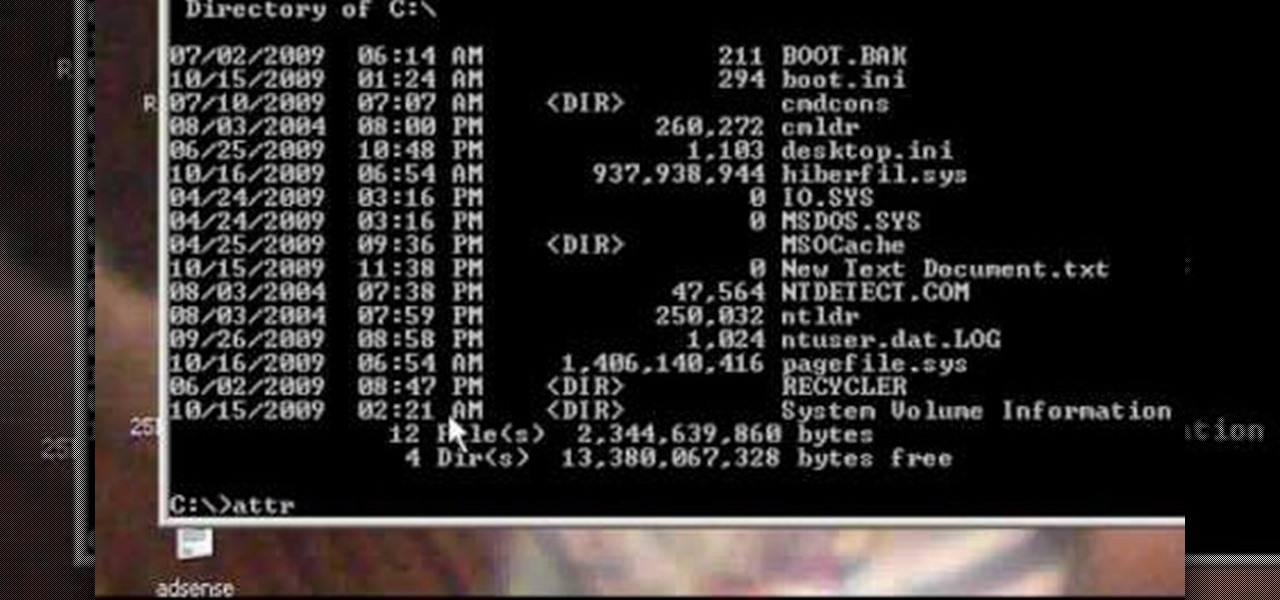
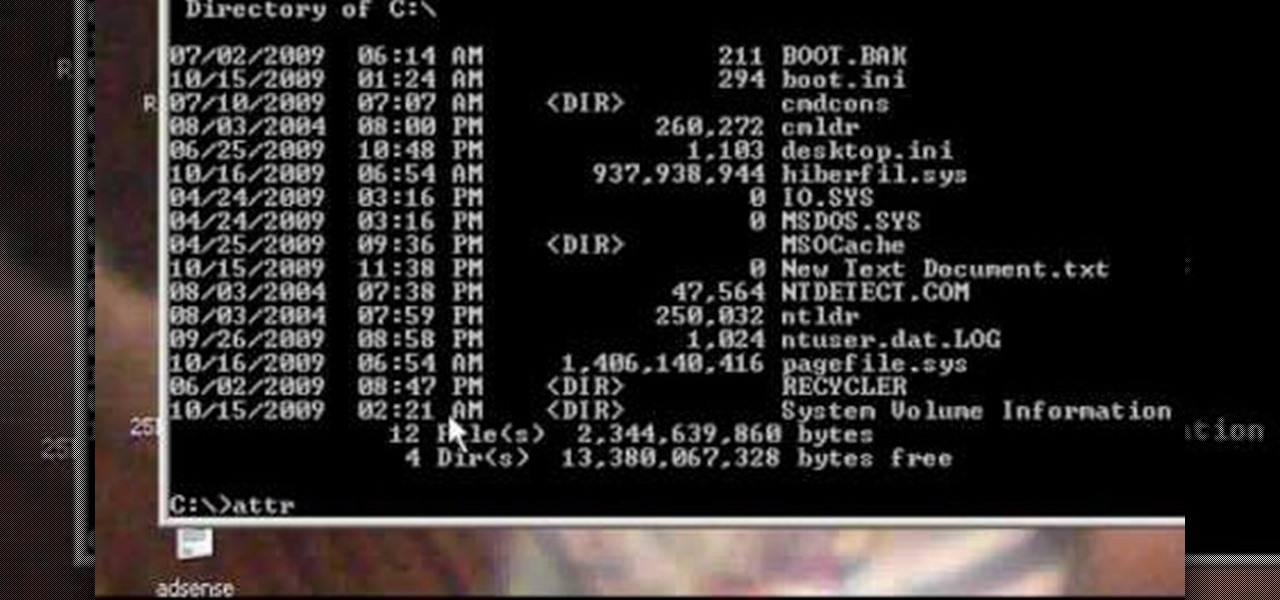
Clintprexis teaches viewers how tot delete a virus manually without using anti-virus. First, you have to kill the process that keeps the virus running. You can do this by opening up test manager by clicking CTRL+ALT+DEL. When you open task manager go to the process tab and kill the process that keeps it running. Now, you have to figure out which process is running the virus. You have to do research to find this and it is usually a 'wscript.exe'. Now you'll want to go to Start then go to run a...

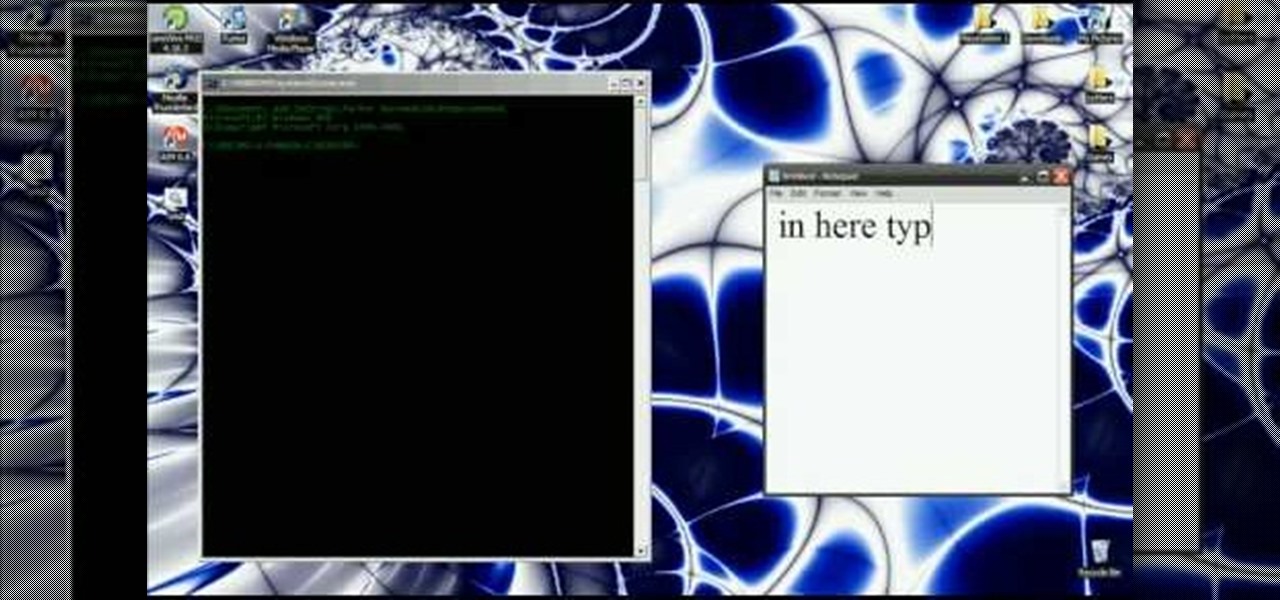
In this video you will learn how to get past website blocks on your school network. Some school computers have command prompts blocked. If this is the case then you will want to open a notepad. In the notepad type command, then save as something school related, making sure the file name ends with .bat. Do not save it on the desktop, but rather in a folder deeper on the unit. Once you've saved it, make sure no one is looking, then open the file. It will bring up a blank black window. In the bl...

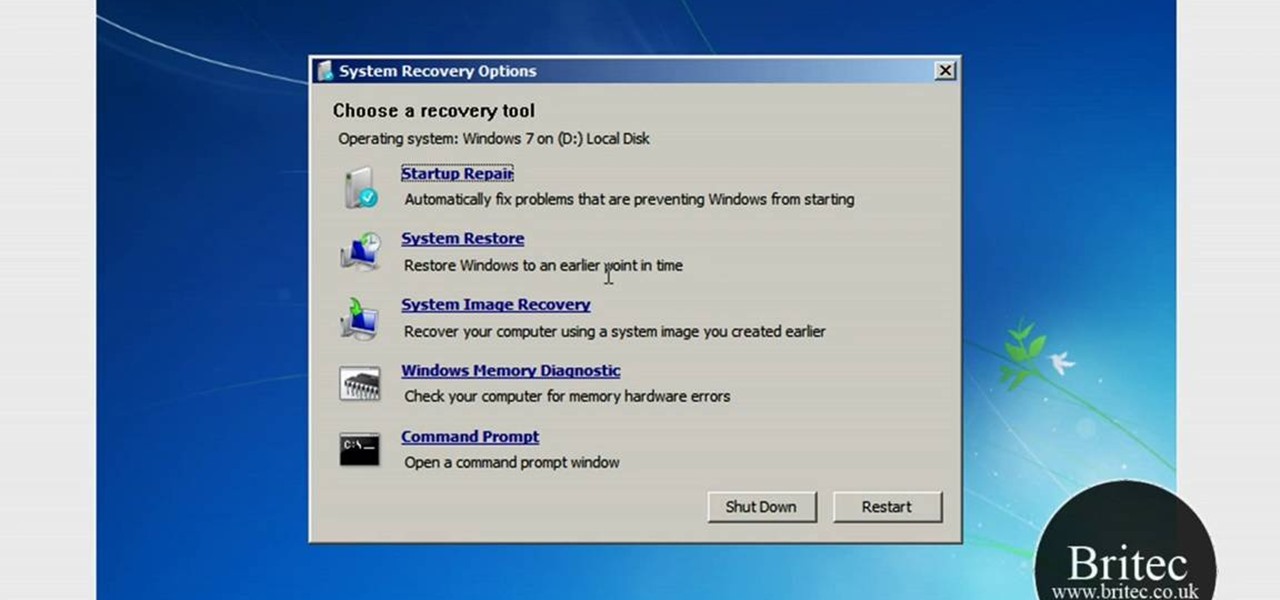
This video tutorial from Britec09 presents how to backup and restore Window 7 registry.First, press Start button and enter regedit command into Start Search area.Registry editor window will open, click File-Export.This option works on all Windows operating systems.Type file name - registrybackup and click Save. You can save it wherever you want, but in this video it was saved to Desktop.Next step is to reboot to Windows DVD. Insert you Windows DVD and reboot computer.Press any key to boot fro...

In this how-to video, you will learn how to change a guitar string on a Stratocaster. You need a guitar, a new set of strings, and a diagonal wire cutter. You might also need a string winder. You will need a guitar tuner and a guitar cable if you have an electric guitar. First, remove the broken string from the guitar. Push the broken string down and through the bridge. Remove the other end from the tuning post. Take the correct string and unroll it. Do not bend the string in any way. Take th...

Jim Reppond of Coldwell Banker Bain demonstrates the way of getting postlets into Facebook. He says that by adding the postlets in your Facebook page, one can click on the link and directly go the postlets page if they are interested. He asks you to then go to the postlets page and log in using your username and password. Once inside, you can click on the 'My Postlets' tab to see your active postlets. Then chose the postlet you want to add to Facebook and click on the respective 'HOST' button...

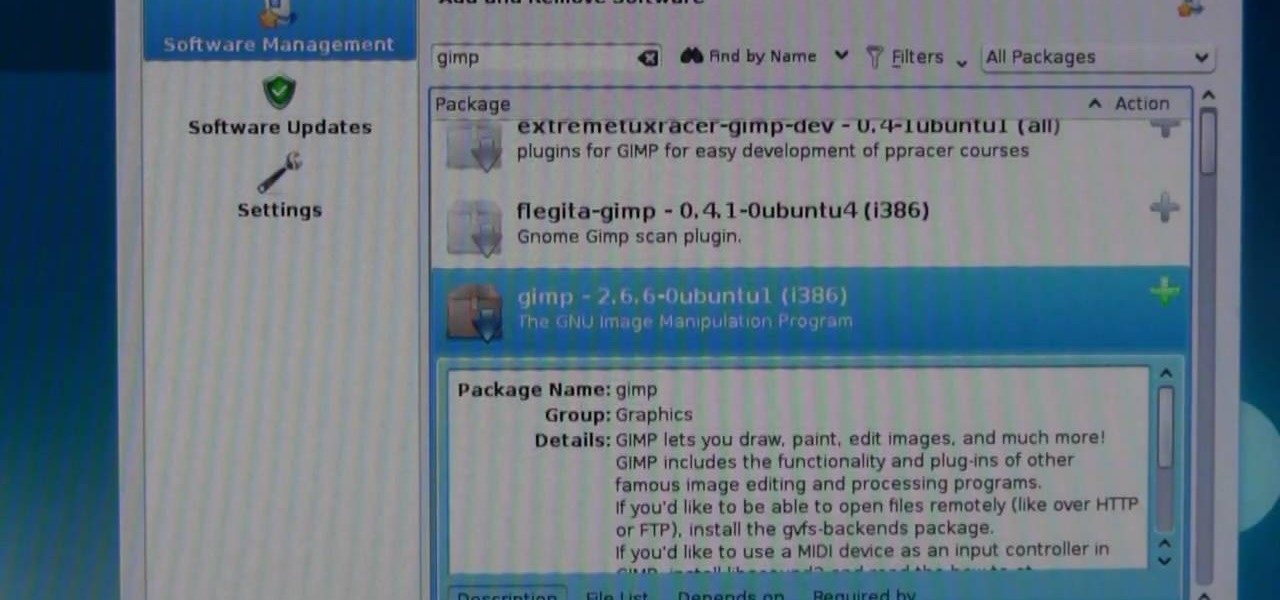
Finding Linux hard to handle after using Windows? Well this should help, here is how to install software on Linux. Start off by clicking on application launcher. Here go into applications, then into 'system' where you should find software management. In this program go straight into the settings and then edit software sources. Under 'downloadable from internet' make sure every option has a check against it. Now press the software management tab on the side. Now this is where you can get which...

With social networking systems, YouTube comments chains, chat rooms, bulletins boards, Twitter updates... It seems as if almost everyone has at one time publicly stated an opinion on the Internet. Nearly half of all prospective employers research job applicants online. Make sure that what you’re posting today doesn’t cost you a dream job tomorrow!

Do you constantly let people walk all over you? Go from doormat to dominator with this advice. You Will Need

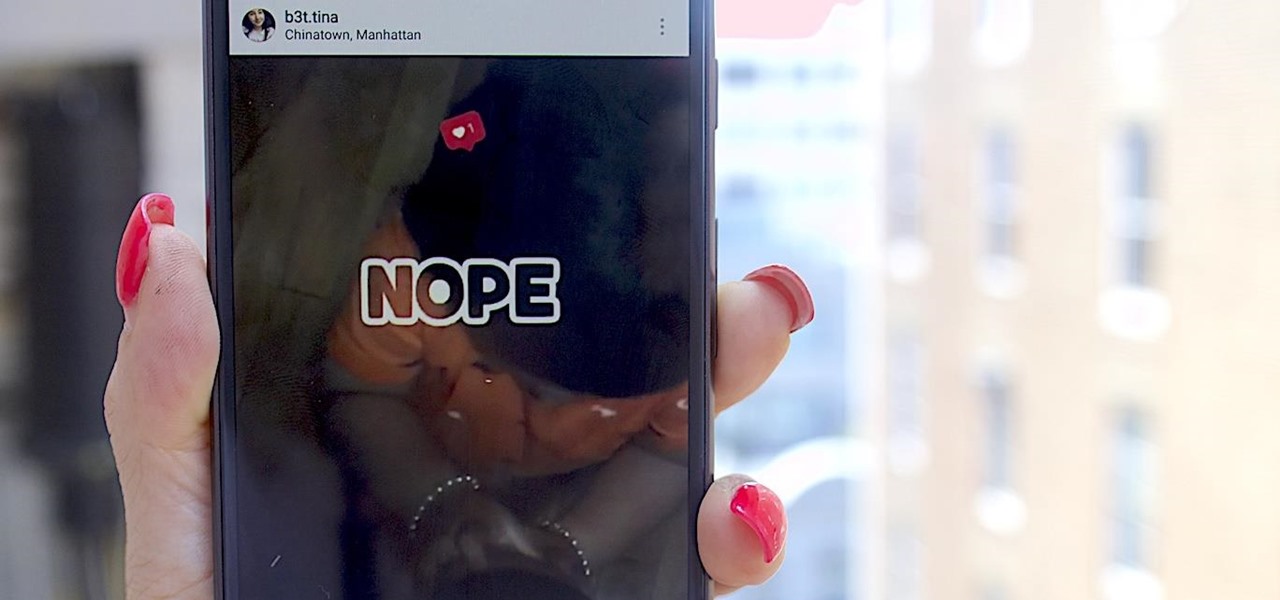
When you post a photo or video on Instagram, it's always nice to see positive comments from friends, family, and even fans. On the other hand, it's never fun to see spam or hate messages underneath your posts. Before, you'd have to delete these comments one by one, but now you can delete comments in bulk.

Software issues occur more frequently on jailbroken iPhones, though, they're usually minor bugs that can be fixed easily with a respring. But if your device freezes up, restarting is the only way to get back to normal, which also means having to re-enable your jailbreak. There is one way, however, to respring without interacting with the touchscreen and having to re-jailbreak.

Without admin privileges, installing additional software, or modifying the Windows 10 firewall, an attacker can alter a router and perform a variety of exploits. It's accomplished by forwarding requests from Kali through a backdoored Windows computer to the router gateway with simple SSH tunnels.

It's been said time and time again: reconnaissance is perhaps the most critical phase of an attack. It's especially important when preparing an attack against a database since one wrong move can destroy every last bit of data, which usually isn't the desired outcome. Metasploit contains a variety of modules that can be used to enumerate MySQL databases, making it easy to gather valuable information.

Router gateways are responsible for protecting every aspect of a network's configuration. With unfettered access to these privileged configurations, an attacker on a compromised Wi-Fi network can perform a wide variety of advanced attacks.

Reconnaissance is one of the most important and often the most time consuming, part of planning an attack against a target.

If you want to carry a variety of network adapters without looking suspicious, a perfect solution is accessing them through Airserv-ng. Tucked away in the Aircrack-ng suite, this tool allows a hacker to plug any number of network adapters into a Raspberry Pi and access them over a Wi-Fi or Ethernet connection.

Slack is meant for business, but it's inevitably used for personal reasons too, or even just to goof off with colleagues. However, you never know who's looking over your shoulder (nosy coworker? boss?), and you could get in trouble for something sent to you. That's why you might want to hide images and GIFs to help keep your conversations private.

We're basically living in the future, so let's work like we are. For decades, we have, without question, opened a word processor like Pages, and clicked or tapped our way to starting a new document. What's wrong with that? It's unnecessary. We all have a digital assistant living in our iPhone, one that can start up a new Pages doc by verbal request.

When new Android versions come out, the modding community has to find new ways to root the OS. It's a fun cat and mouse game to follow, but it also means the process of rooting isn't exactly the same as it was the last time you did it. Android 10 changes how root works on a system level for some devices, but luckily, the developers are already on top of things.

If you find yourself with a roommate hogging limited data bandwidth with video games or discover a neighbor has invited themselves into your Wi-Fi network, you can easily take back control of your internet access. Evil Limiter does this by letting you control the bit rate of any device on the same network as you, allowing you to slow or even stop data transfer speeds for them completely.

MouseJack vulnerabilities were disclosed over three years ago. Some wireless keyboard manufacturers have since issued firmware updates, but millions (if not billions) of keyboards remain unpatched worldwide, either because they can't be updated or because the manufacturer never bothered to issue one.

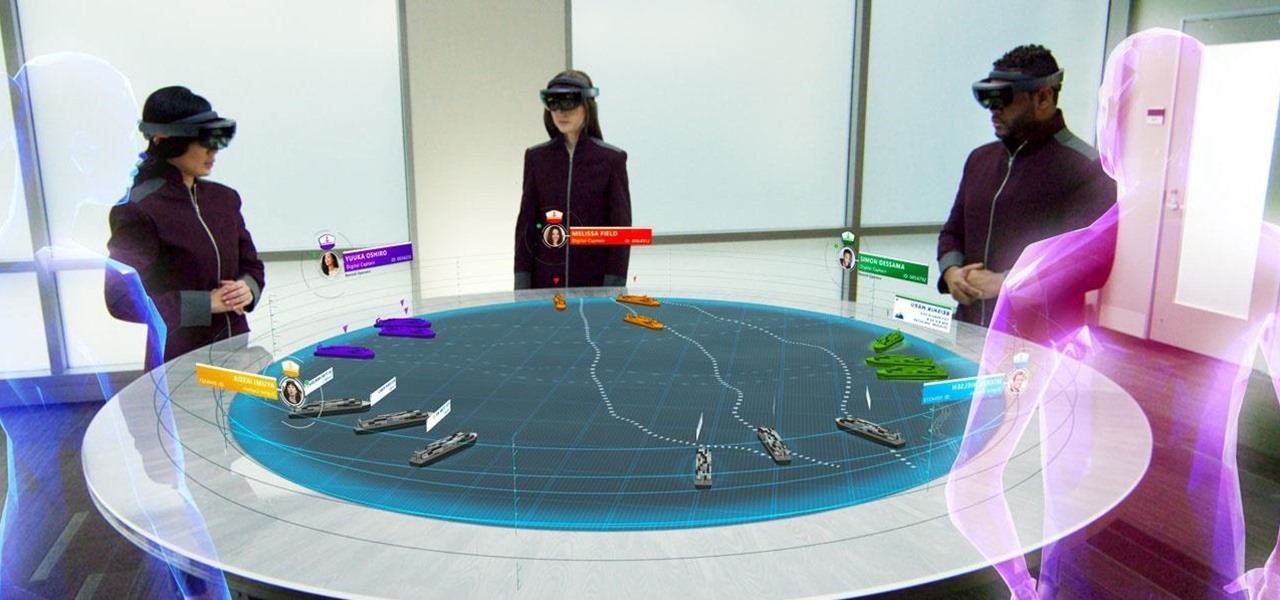
Simulated training can help soldiers and sailors learn how to use their weapons safely, but simulations can sometimes lack the stressful environment of a real firefight.

Computers all over the world rely on a program called "libssh" to use the SSH communications protocol, which allows trusted users to log in and administer computers remotely. Due to a flaw in libssh, fooling a computer into granting SSH access is as easy as telling it you already have permission. The vulnerability can lead to an attacker gaining complete control over a device.

Samsung isn't known for its timely rollout of major Android updates, and Android 9.0 Pie won't be an exception. If we go by their Oreo update timeline, we can expect Android Pie to officially touch down for the Galaxy S9 and S9+ sometime around November, with the final version rolling out the around the first quarter of 2019. But a leaked version of the beta has already hit the internet.

It's not uncommon for hackers to attempt to move laterally between devices in proximity of a compromised device to maintain a prolonged presence in the network. Malware utilizing USB flash sticks to self-replicate and compromise air-gapped machines isn't a new concept.

Web application vulnerabilities are one of the most crucial points of consideration in any penetration test or security evaluation. While some security areas require a home network or computer for testing, creating a test website to learn web app security requires a slightly different approach. For a safe environment to learn about web app hacking, the OWASP Juice Shop can help.

At I/O 2018, Google showcased features that would make the Google Assistant easier to communicate with. While some people were impressed with (and maybe creeped out by) Google Duplex, one feature that was well received was the ability to talk to the Assistant without the constant "Hey Google" before each question.

Kali Linux is established as the go-to operating system for penetration testing, but in its default configuration, it's less than ideal for regular desktop use. While in many scenarios, a live boot or virtual environment can resolve these issues, in some situations, a full installation is better. A few simple changes can be made to a Kali Linux desktop to make it safer to use in this environment.

Although the HoloLens is still primarily the domain of developers and researchers, the device is nevertheless on the cutting edge of showing us what will be possible with augmented reality in the coming years. The latest example comes via Microsoft Japan and a new concept video that shows off how the HoloLens will be used in the relatively near future to pilot autonomous ships.

Shodan calls itself "the search engine for internet-connected devices." With so many devices connected to the internet featuring varying levels of security, the special capabilities of this search engine mean it can provide a list of devices to test and attack. In this tutorial, we'll use Python to target specific software vulnerabilities and extract vulnerable target IP addresses from Shodan.

In a previous article, we learned how to take advantage of a feature, Dynamic Data Exchange (DDE), to run malicious code when a Microsoft Word document is opened. The biggest challenge of this attack is that it requires getting the user to agree to a pop-up prompt. Fortunately, since I posted that article, many new obfuscation techniques have been discovered to make this easier. Today, we explore and combine some of them to make the ultimate hidden DDE attack.

The pictures we upload online are something we tend to think of as self-expression, but these very images can carry code to steal our passwords and data. Profile pictures, avatars, and image galleries are used all over the internet. While all images carry digital picture data — and many also carry metadata regarding camera or photo edits — it's far less expected that an image might actually be hiding malicious code.

The primary method of activating Siri is done by pressing and holding either the Home or Side button, depending on the iPhone model, but there's a much better way to ask a question to Siri or command it to do something — and you don't need to touch your iPhone at all to do it.

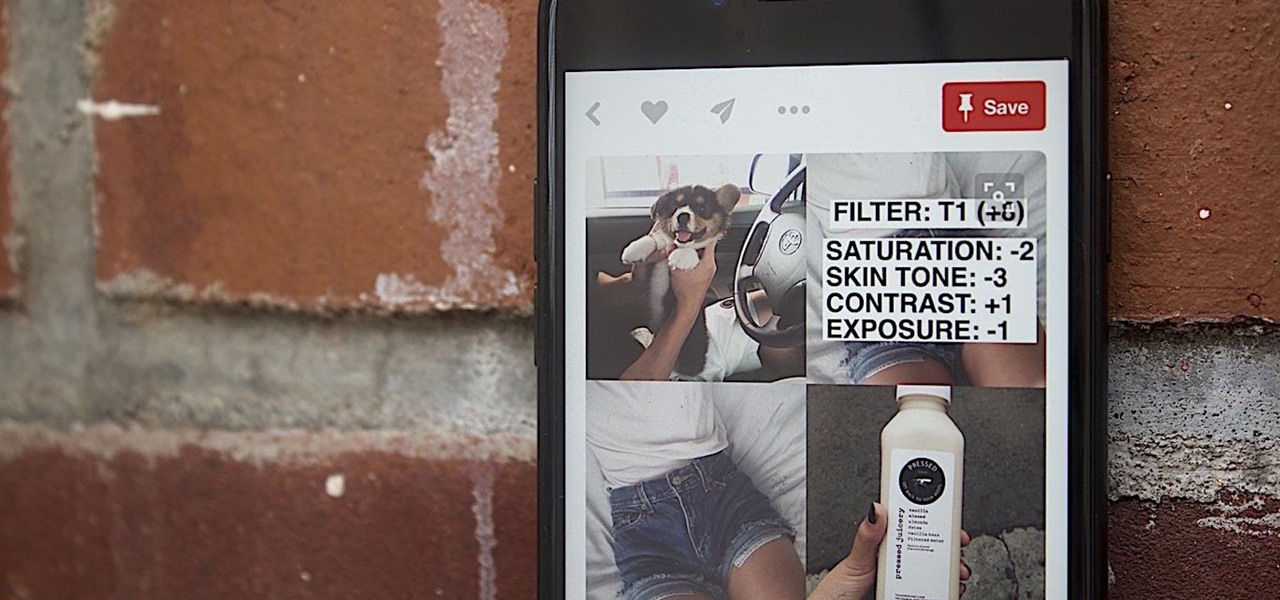
The Stories feature on Instagram has a pretty great editing program, and it's one that I think is extremely undervalued. Instagram Stories goes beyond just its Snapchat-like features, but also allows you to create more creative and original content to post on your actual profile page.

A router is the core of anyone's internet experience, but most people don't spend much time setting up this critical piece of hardware. Old firmware, default passwords, and other configuration issues continue to haunt many organizations. Exploiting the poor, neglected computer inside these routers has become so popular and easy that automated tools have been created to make the process a breeze.

This is probably one of the coolest Instagram hacks I've come across. I never knew that there could be an actual formula for creating the perfect feed, but the fact that someone thought of it is really awesome.