Today I will show you how to make a metasploit exploit really quickly. This tutorial is mainly applied to stack based buffer overflows and seh buffer overflows exploits .There is a simple way for rop exploits too but I will dedicate a special tutorial on this subject.

Managing hard drives in Linux is crucial to understanding your system and its operation as well as understanding the system you are exploiting or conducting a forensic analysis on. Linux has numerous commands that can provide us with information, control, and management of hard drives, and in this tutorial, we will examine a number of the most important ones.

The digital pen on the Surface Pro 4 and Surface Book is an indispensable tool for serious note-takers and artists alike.
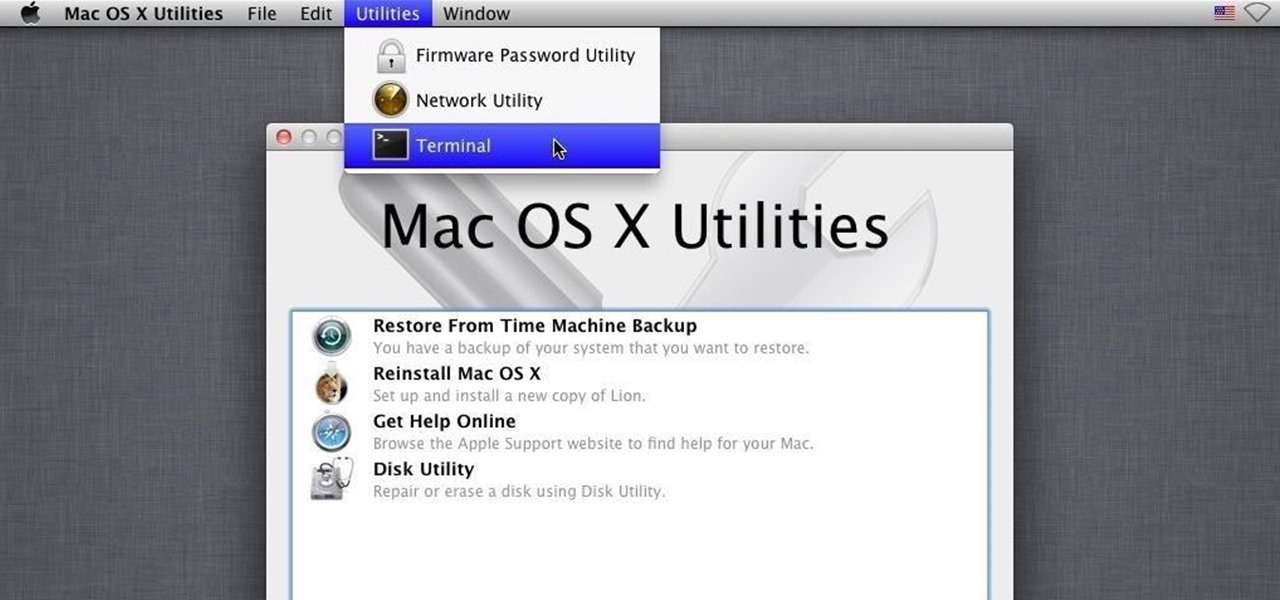
Hello, my fellow hackers. My name is cl0ck. I am a senior majoring in Computer Engineering with an emphasis is Security. I have been lurking the site for a while now reading and learning from the great minds that reside here. I, too, have some knowledge that I would like to share with all of you. This post actually comes from a personal problem I faced and had to find a solution for. Without further ado, here it is:

welcome back my masters , teachers and classmates , in this second part of this 0-day series we will learn the basic of fuzzing, and i bought some gift for nullbyte(a 0 day vuln that will be released today exclusively on null-byte) .
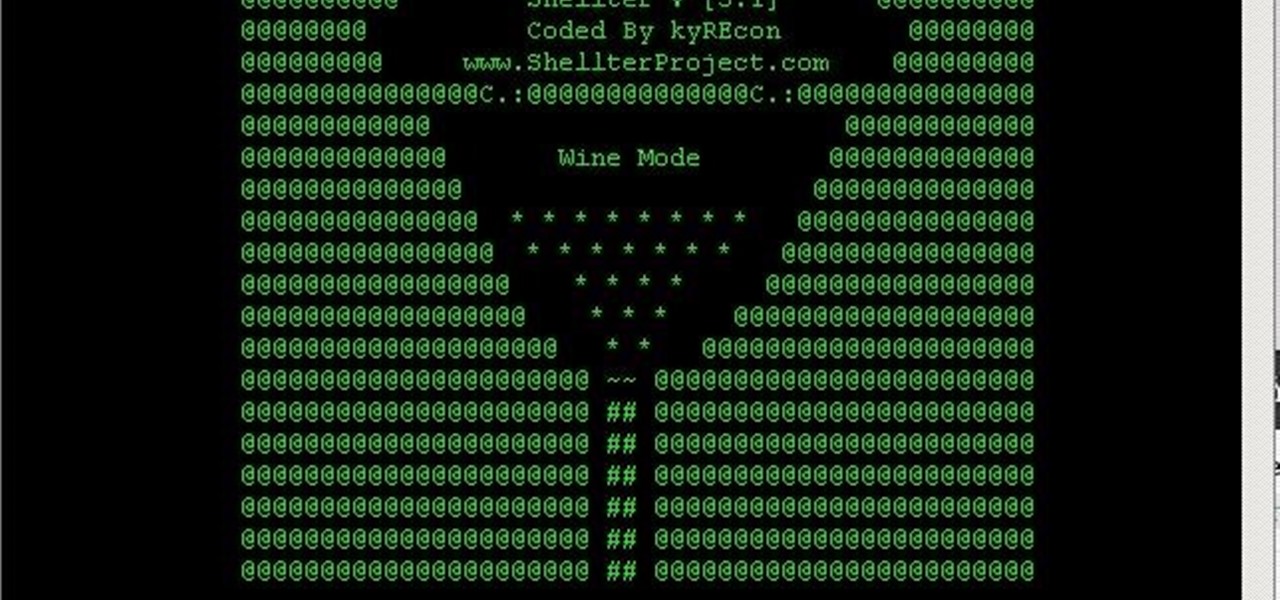
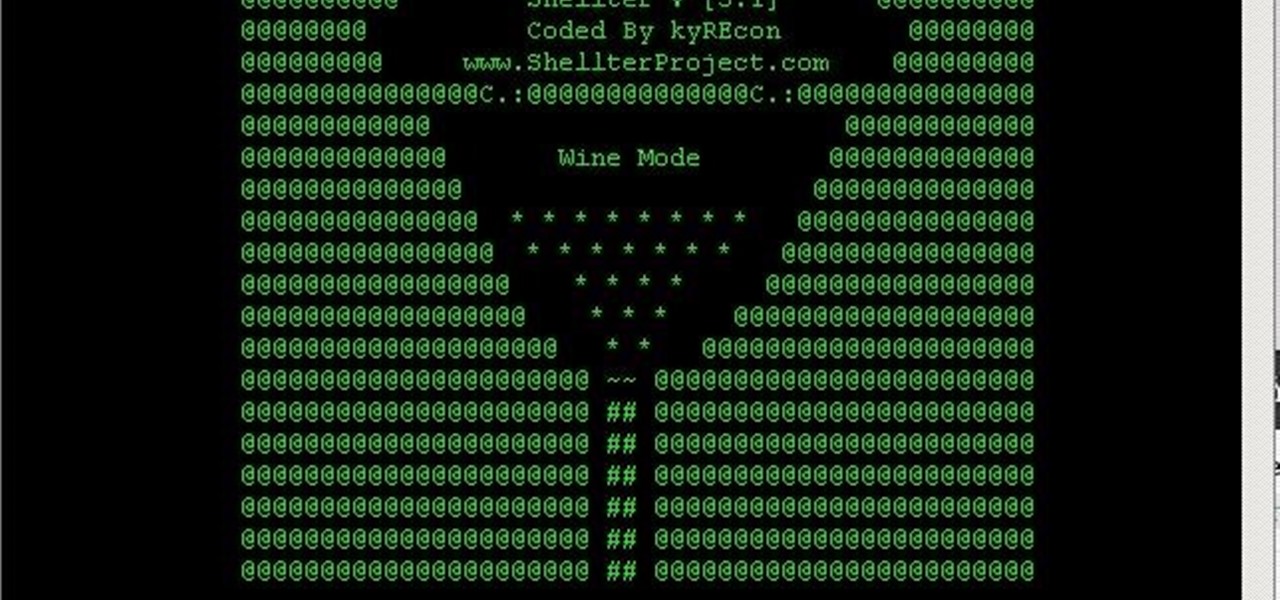
You always wanted to make an undetected payload and make it look legit, Well this is what this tutorial is about, You're going to learn how to backdoor any (Unfortunately only 32-Bit) software, Let's get into it

If you've been using Windows 10 for a while, you already know that Microsoft incorporated lots of new features into it. So you're probably familiar with Cortana (the new voice assistant), the Edge browser (their replacement for Internet Explorer), the newly resurrected Start menu, and all of the other big changes.

Recently, I've been learning Ruby as a second scripting language. But one topic I never covered with the many lessons online were sockets. So I did some research and came up with a very simple client/server connection that sends a string over the socket.

OTW's great Tutorial Hack Like a Pro: How to Save the World from Nuclear Annihilation gives me the inspiration to try this on Win7 sp1.

Hello Elite Hackers! Welcome to my 3rd Post, which explains how to hack any account like G-mail, Facebook, etc.

Reddit's overall design has stayed relatively unchanged for as long as I can remember. It's easy to use and is as popular as ever, so why mess with a good thing, right? Well, everyone's different, and if you're looking for ways to beef up your Reddit experience, try out the Chrome extension SHINE.

Welcome back, my hacker novitiates! Eluding and evading antivirus software and intrusion detection systems is one of the most critical tasks of the hacker. As soon as a new exploit is developed and discovered, the AV and IDS developers build a signature for the attack, which is then likely to be detected and prevented.

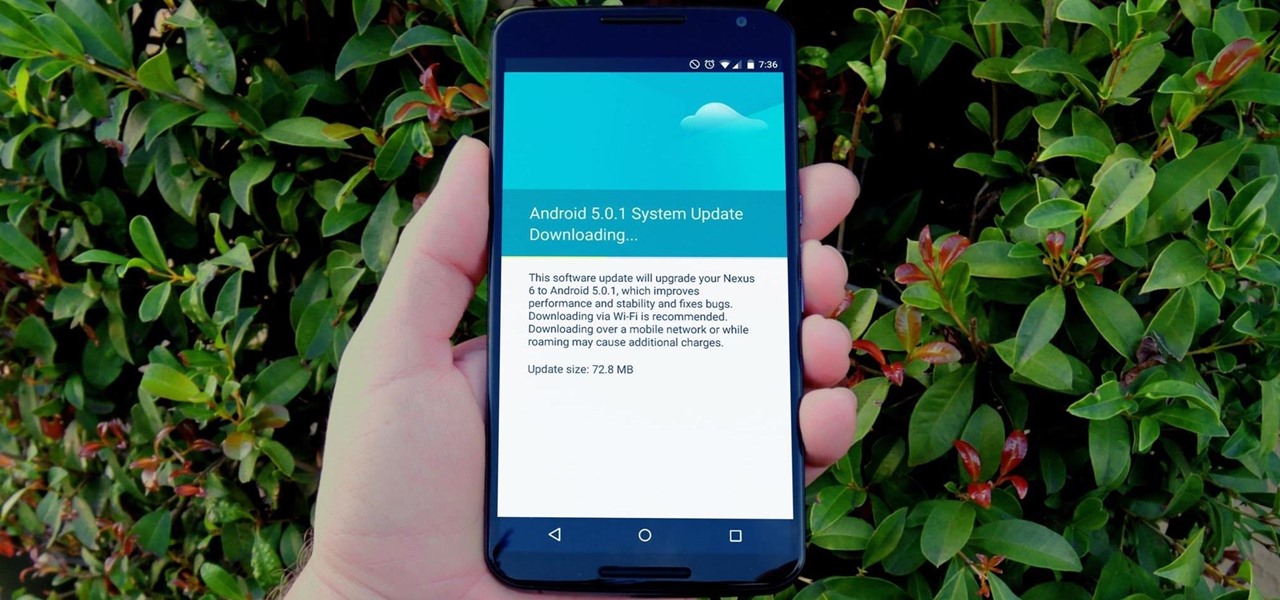
One of the main reasons to buy a Nexus device is the fact that they're always the first to get new Android updates. Another great selling point for the Nexus series is that the devices are amongst the easiest to root and mod. Unfortunately, though, these two features are somewhat mutually exclusive.

Yosemite brought a new, Alfred-like Spotlight search to our Macs, but at times I still find myself wanting more out of it. However, after stumbling upon Flashlight by developer Nate Parrot, I am now able to perform Google searches, look up weather, and even enter Terminal commands straight from Spotlight's search bar.

Social media is constantly evolving, and as a result, we're now capable of sharing much more than we were even just a few years ago. Television, on the other hand, continues to hold strong as one of America's favorite pastimes.

While the "Hey, Siri" feature in iOS 8 is useful for hands-free multitasking, you can only use the command when your device is actually charging.

In previous posts here, I have pointed out that hackers are in high demand around the world and in nearly every industry. Every military and espionage unit of every country is trying to hire high-quality, experienced hackers as fast as they can to hack their adversaries' computer systems in order to gain a strategic advantage and to spy.

Amid rumors of a 6-inch phablet Nexus and the impending release of Android "L", Google posted—then quickly removed—a trio of ads for their industry-leading mobile OS.

Now that you've updated your iPad, iPhone, or iPod touch to iOS 8, there's a lot of cool new things to explore. If you felt a little overwhelmed from all of the detailed information available in our Coolest Hidden Features of iOS 8 post, then I've got a simple breakdown of all of the new features available with quick links to their walkthroughs and pictures, if available. Watch the short video roundup, or skip below for the list.

As much as it pains me to say it, without my phone, I would pretty much be useless. I can barely remember what I had for lunch yesterday, let alone all of the hundreds of numbers in my contact list. That's why whenever I forget my phone at home, I am pretty much stuck having to choose whether I want to be late to wherever I'm going, or feeling completely lost and disconnected for the rest of the day.

Welcome back, my budding hackers! In my continuing effort to build your basic Linux skills for hacking, I want to show you how to build a secure "tunnel" to MySQL.

The sovereignty that's granted when we jailbreak our iOS 7 devices can only be described with one word—liberating. With this freedom comes countless themes and apps that let us manipulate our devices to really own them and turn them into something that is truly ours.

Instagram recently released their new Instagram Direct messaging feature in their Android and iOS apps, which lets users share private photos and videos directly with individuals or groups of up to 15 users. However, there are no restrictions on who you can send private photos or videos to.

With the Samsung Galaxy Gear smartwatch only several weeks old, the extent as to what you can do with it is limited since there are only about 70 apps in the Gear Store right now, and a lot of those need the full app installed on your Samsung Galaxy Note 3 in order to function properly.

Welcome back, my fledgling hackers! It's been awhile since we did a Metasploit tutorial, and several of you have pleaded with me for more. I couldn't be happier to oblige, as it's my favorite tool. For the next several weeks, I'll intersperse some new guides that'll help expand your Metasploit skills and keep you abreast of new developments in Metasploit, so look for them in the near future.

Welcome back, my budding hackers! I began this series on Linux basics because several of you have expressed befuddlement at working with BackTrack on Linux. As a hacker, there is no substitute for Linux skills.

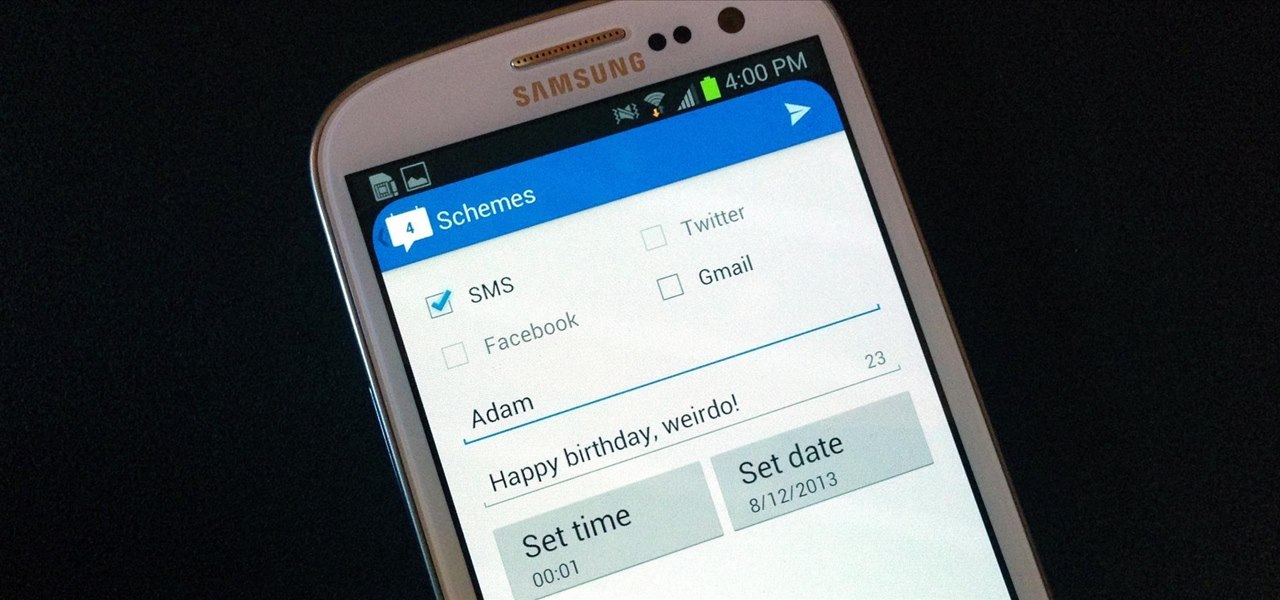
I'm sorry your mom hates you now, but it's pretty hard to forgive someone who forgets to say "Happy Mother's Day." Your poor ole ma could've spent anywhere from 10 to 20 hours popping you out, so the least you could do is set aside two minutes every year to say thanks. If you live to be 90 years old, that's only 3 hours over your entire lifetime!

A few weeks ago, Facebook published a blog post called "Proposed Updates to our Governing Documents," which outlines a few changes in their policies and user voting system. These changes would essentially take away users' right to vote on future changes to Facebook's data use policy while also taking away Facebook's responsibility to alert users of those changes. If the new policy is enacted, the vote will be replaced with "a system that leads to more meaningful feedback and engagement," what...

At the most recent Apple event, the company announced its new Fusion Drive, a hybrid hard drive designed to increase performance and speed by combining traditional and flash storage. It's composed of a small solid-state disk and a larger spinning hard disk drive, and files and applications are moved back and forth between the two based on how often you use them. A chunk of memory is reserved for whatever task you're currently doing, which means that multitasking doesn't slow down your compute...

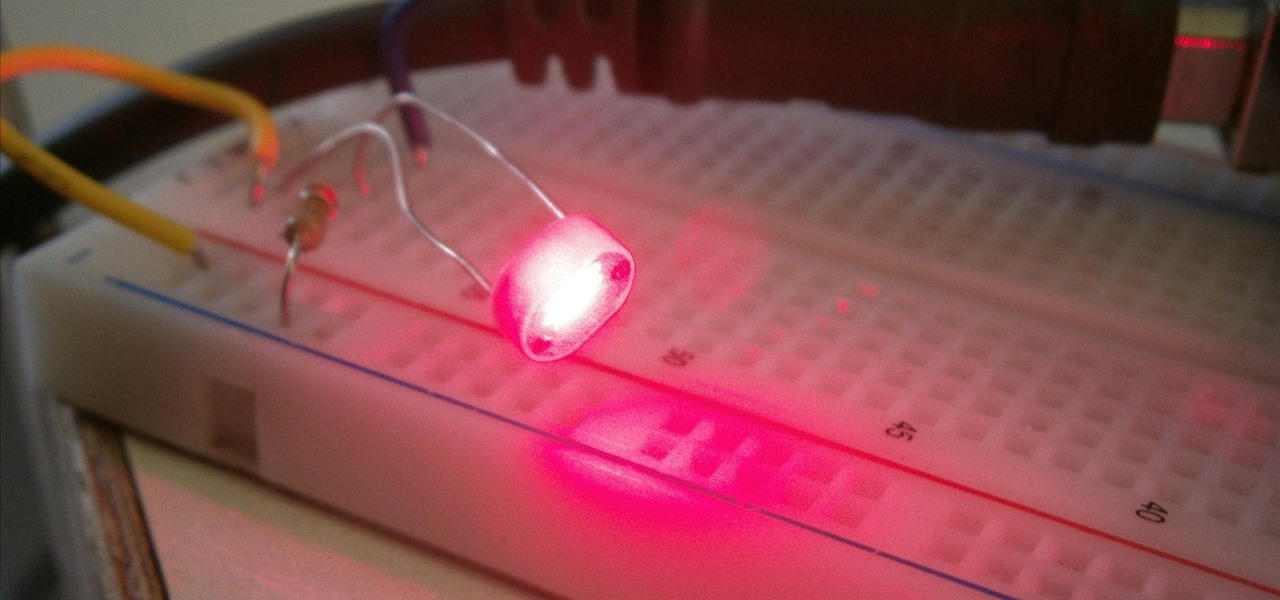
The mighty Arduino microcontroller can be used to show children how robots work, it can be used to hack into hotel rooms, or it can be used to let you know when you've got a new job opportunity!

Doorbells are a great idea. They let you know when someone who's not a burglar is trying to enter your house, apartment, or squat. They eliminate the need for lots of noisy yelling and startling door pounding.

So the beta version of Minecraft 1.8 is officially out and you want to explore the new worlds and features of the pre-release. The best way to explore is to move around super quick right? So take a look at this walkthrough on sprinting and flying in Minecraft 1.8.

If you can't get access to a wifi hotspot or an Internet connection with your PSP, you can use this method to get online. You will need access to a computer that is online, and a USB cord that can connect the computer to your PSP. Then, open up the command prompt on your computer, configure your IP and then add your PSP as a device on the network. This method uses the DNS method of getting to the Internet rather than having to hack a wifi connection.

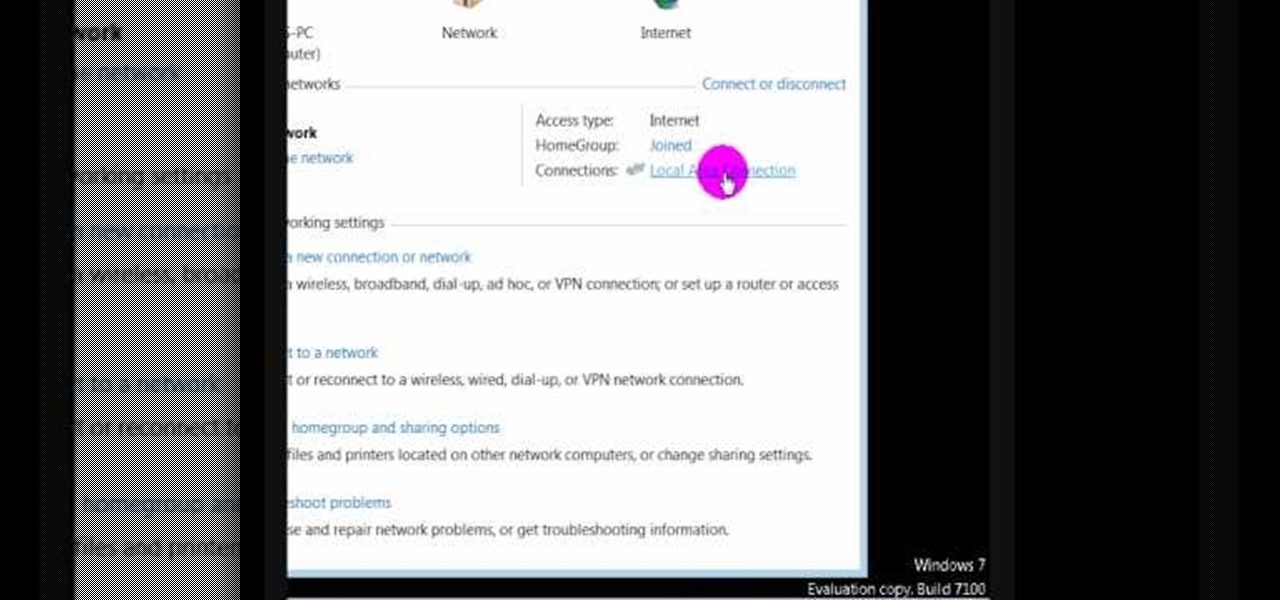
In this video we learn how to find the IP address of your computer. First, go to your desktop and click on the network in the lower right hand corner. The network and sharing center will now pop up on your computer. Click on the link that says "local area connection". Then a new window will pop up, click "details". Once the information comes up you will be able to see your IP address along with a ton of other information about your network. Another way to find your IP address is to go to the ...

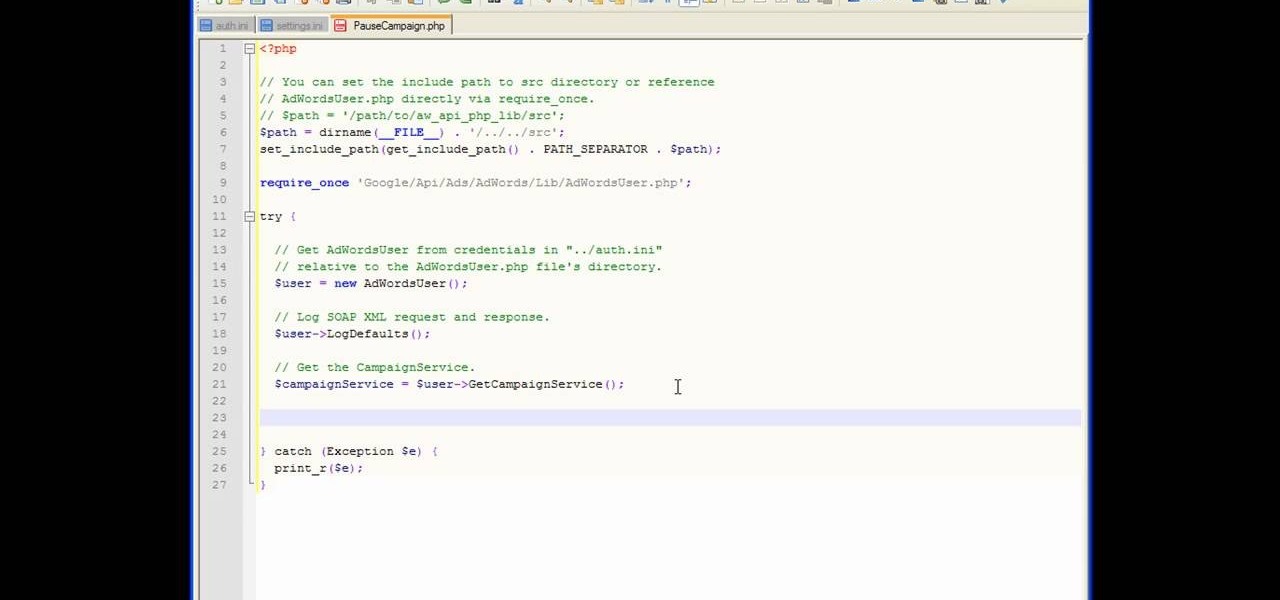
In this tutorial, we learn how to get started with the AdWords API PHP client library. First, download the library by going to the API documentation online. From here, set the authentication information and then open up the library. Now, save the changes to the file and use a sandbox environment. The examples folder has all versions that the API library supports. You can browse the campus folder with the search button, just type in the command of what you want to see. After you do this, you c...

This video tutorial is in the Computers & Programming category which will show you how to hack a wireless network with WEP encryption. This video is intended only as a means of testing the security of your own network. Go to Backtrack Linux, download the backtrack4 and burn it to a DVD. Now put it in a computer with a wireless card and restart the computer so that it boots to the DVD. When it boots up, type "startx" to start the interface. Bring up the command prompt and type in "/etc/init.d/...

In this tutorial, we learn how to customize bash prompts with the PS1 variable. The PSI variable will say what something does. You can change this using the export command. Basically, you just type in the same thing and add in something. You can do this by simply typing it in using your keyboard. After this, press enter on your keyboard, then continue to change more things. There are a ton of different things you can do with this. You can find more from the website: http://pastebin.com/f2309f...

You can kill the x in Ubuntu with dontzap. Its really convenient if you like it. First thing you need to do is to download this package called dontzap. Now you can run the command sudo dontzap -d, it will disable that feature that Ubuntu uses and it will let you kill x by just pressing the ctrl + alt + backspace. It is really simple as that and there is no chance that you accidently pres the ctrl + alt + backspace and kill your x session. So after that you need to reboot your computer and you...

In this video, we learn how to change The Windows 7 Start Orb. First, you will need to download Universal Theme Patcher to your computer, which you can find at: Freeware Geeks. Once you download this, install it to your computer and make sure you choose the right type to download. Also, download the registry files from MediaFire, click the "take ownership" option when you right click on this, then double click on it. When the window comes up, click to add the ownership option. Now, go to the ...

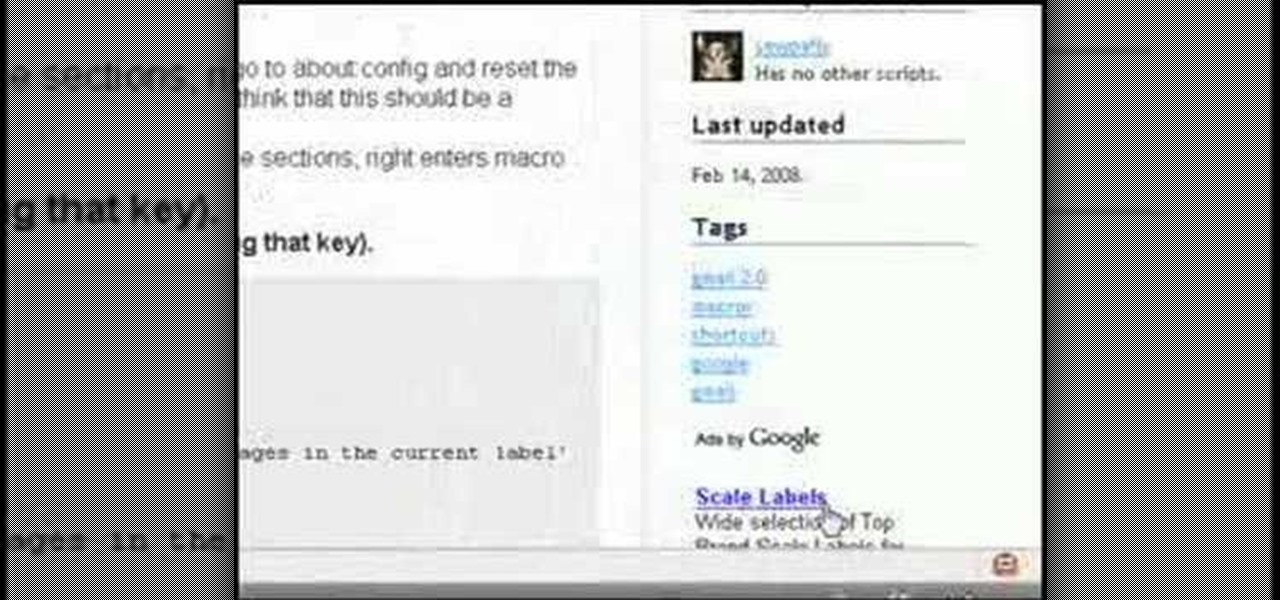
In this tutorial, we learn how to create interactive shortcuts in Gmail:Greasemonkey. Start off by searching for "Greasemonkey", then click on the very first result. Click to install this, then once you have it you need to restart Firefox. Now, on the bottom of the screen you will see a little monkey icon. After this, type in "Greasemonkey scripts" into Google, then search for "modified Gmail macros" and install this. After this is installed correctly, go to your Gmail account. First, type in...