How To: Hack P.O.D. with Cheat Engine (09/23/09)
This is a Cheat Engine guide on how to hack this flash game - P.O.D. Kongregate Acheatment shows you how to hack P.O.D. with Cheat Engine (09/23/09). This P.O.D. cheat will give you a level hack.

This is a Cheat Engine guide on how to hack this flash game - P.O.D. Kongregate Acheatment shows you how to hack P.O.D. with Cheat Engine (09/23/09). This P.O.D. cheat will give you a level hack.

Hak5 isn't your ordinary tech show. It's hacking in the old-school sense, covering everything from network security, open source and forensics, to DIY modding and the homebrew scene. Damn the warranties, it's time to Trust your Technolust. In this episode, see how to defend your hacker space with a USB missile launcher.

What to teach your new dog an old trick? Then follow along with this pet how-to video to learn an easy way to teach your dog how to do a simple obstacle course. An obstacle course is a simple trick you can teach your dog with treats. Follow the steps below to teach him or her this great obstacle trick.

In this video Chris Pels shows how to create an MSBuild project that orchestrates the execution of the aspnet_compiler and aspnet_merge utilities for an ASP.NET web site. First, learn the fundamentals of the compilation process for an ASP.NET web site and the role of the two command line utilities. Next, see how to create an MSBuild project file and the primary elements such as PropertyGroup and Target. Then learn the details of how to execute the aspnet_compiler and aspnet_merge utilities fr...
Check out this instructional language video to learn how to speak Cherokee! In this lesson, learn how to conjugate the verb "To Sing" in the imperative (the command form), the future tense, and the present continuous verb tense. This is in the Eastern (Giduwa) Cherokee dialect. This video is great for beginners who want to improve their Cherokee language skills. Practice your Cherokee by learning to conjugate the verb "To Sing." Here is the list of forms:

The Apple Spotlight application in Mac OS X can do more than just searches for documents. Throughout your day, you may need to perform a calculation or look up a definition for a word. You can now do that directly from Spotlight. To acccess Spotlight, you can either click on the magnifying glass icon at the top right of your screen or hit command spacebar to bring up the search field. To learn more about using advanced features in OS X Spotlight, watch this video tutorial.

Microsoft Office Excel 2007 has a new design that makes your work easier, faster, and more efficient. The new Ribbon puts the commands you use most often in plain sight on your work surface instead of hidden in menus or dialog boxes. Ready-made cell styles let you quickly format your worksheet to make it easier to read and interpret. The new Page Layout view shows how your printed worksheet will look as you're creating it.

This is hardcore, serious hacking at its best. So it goes without saying that you probably shouldn't be attempting this computer hack unless you've successfully shut down your friend's computer at school using Command Prompt and sent out a fake virus to loved ones.

A guide to using the map editor in Command & Conquer 3. Part 1 of 4 - How to Edit maps in Command and Conquer 3.

Bill D., the tech lead at all3sports.com takes us through the steps involved in unpacking and assembling a brand new bicycle. The first he says is to set up or insert the seat post. He recommends using a work stand if you have one at home. He says not to unpack everything at the beginning, but to just expose the seat pack first. Use a wire-cutter to get rid of the film protection used for packing. He has mounted the frame-set on the work stand. The seat post goes into the frame-set. He asks t...

During the holiday season most of us have a Christmas tree up in our living rooms, filled to the brim with sparkly ornaments and twinkly lights. But the Christmas spirit tends to be a bit damper at work, where the most jolly it gets is making a makeshift post-it note Christmas tree on our cubicle wall.
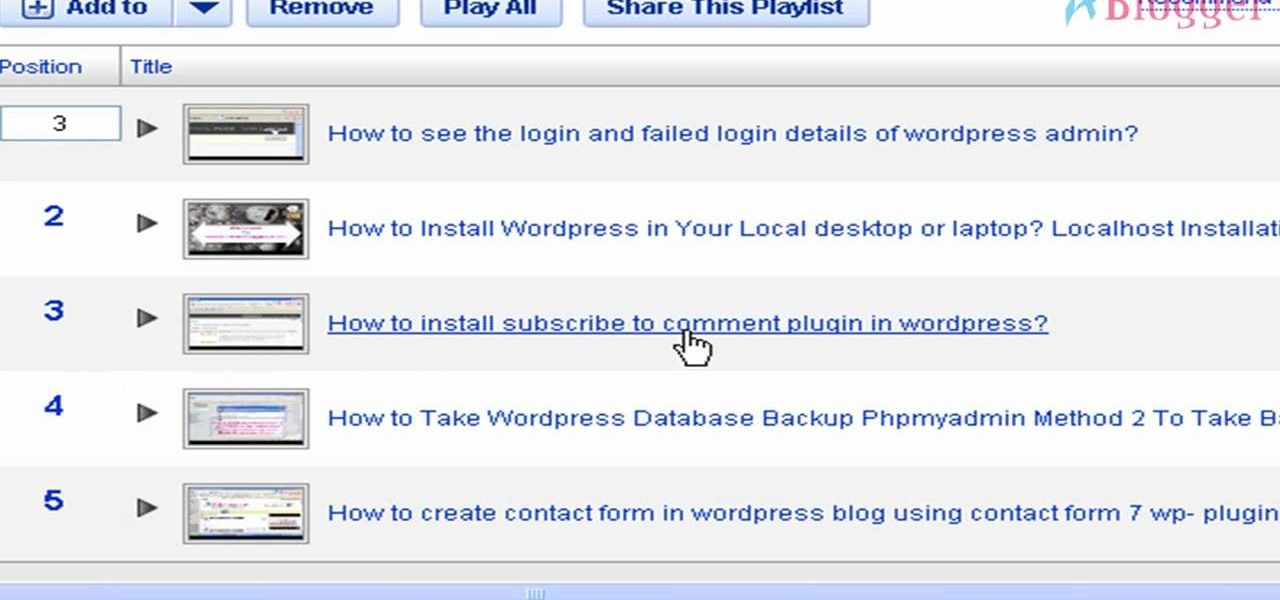
Once you have created a YouTube playlist on your YouTube channels, there's things you can do to customize it, like rearrangement of the uploaded videos. Reordering and rearranging the videos in your playlist is easy, so if you don't want your uploads to appear in reverse chronological order… you want your own order… watch this video to see how.
This quick video gives you some basic instructions on how to embed and remove a YouTube video in a forum. Though this video shows a specific Aussiebirds Forum, the information is applicable to many forums with the same type of format. It's as simple as a few clicks. You'll be adding videos before you can say "embed"!

Blogger is Google's blogging platform and this video shows how to signup, create, setup and start blogging on Blogger. You are given a run-through of going to blogger.com and signing up to create a blog, creating your account, naming your blog, selecting your template and finally creating the blog. After that you can go ahead and create your first post, format it, preview it and finally after everything is complete publish it on the web for everyone to see!

This software tutorial gives you a good overview of how to record screencasts using Camtasia Studio 5. You will learn how to set up your computer for recording, and how to do some post-processing effects and techniques to your screencast in Camtasia Studio 5 after you have finished recording. If you plan to make podcasts or screencast tutorials, Camtasia Studio 5 is a great software to use, and this video will show you how to get started with it.

Ever wanted to own a giant spider? Well you can't, but you can fake it instead using software like After Effects and Blender. This tutorial shows you how to use Blender to work on the 3D spider and then finish adding it into a scene using After Effects. The spider can be found here:

Ever experienced uncontrolled after bursts during semi auto play? Most gun triggers have four adjustments: tension, pretravel, activation point, and post travel. The wrong setting could damage your paintball gun's board. This video shows different ways of setting up a paint ball gun's trigger for efficient play and better control.

After knee surgery, the knee is usually stiff with reduced range of motion because of swelling in that region. In this instructional video, a physical therapist explains how to get the knee back to its best following surgery with rest, exercise and physiotherapy.

We all need a place to stick things such as notices and memos. If only there was some sort of board on which we could post these bulletins! Fear not, this video will teach you how you can make your own bulletin board using basic arts and crafts supplies.

In this video, Bob Schmidt shows you how to use heavy plastic to easily mix concrete. This is a great method for fence posts, interior work and any small to medium size project for your home remodel needs.

This video shows you how to light up a bluescreen for special effects. The bluescreen must be well lit in order for the effect to be more seamless win post production.

Learn how to move correctly and quickly while playing defense on the low post.

Learn how to practice rebounds and low post play with this great 2 on 2 basketball drill. For this drill you want to use guards, and teach them to crash from the outside.

Learn a great 2 player drill for practicing rebounds and low post play - the rebounding one-on-one drill.

Just because it's barbeque doesn't mean it has to be unhealthy. In this video Bethenny Frankel shares with you her recipes for a great post-skiing barbeque including: grilled turkey sausage with dijon dipping sauce, grilled goat cheese and sundried tomato pesto, panini's and grilled cilantro pesto chicken quesadillas.

This video tutorial will talk about html formatting on YouTube. specifically how to make your comments bold, italicized (italics), underlined, or all of the above. It also explains html entities.

This video demonstrates how to watch, save and share movies with Windows Movie Maker. The video walks you through saving and compressing the movie, emailing it to another person, and posting the movie on the web.

For whatever reason, you may want or need to remove multiple posts from your Instagram grid. If you only have a couple to hide from the public, archiving or deleting posts one by one is fine, but there's a much faster way when you have tens or even hundreds of Instagram posts to purge from your account.

People use browsers for all types of things, and in general, we trust a lot of personal information to them. That's why browsers are a perfect attack surface for a hacker, because the target may not even know they are infected and feed you all of the information you could want.

When you think about your Apple Watch, what comes to mind? Fitness tracking? Replying to texts? There are a lot of things Apple Watch is good for, but social media doesn't appear to be one of them based on the App Store. If that's your perception, however, it's time for a reality check because you can start browsing Twitter and Reddit on your Apple Watch right now.

SMB (Server Message Block) is a protocol that allows resources on the same network to share files, browse the network, and print over the network. It was initially used on Windows, but Unix systems can use SMB through Samba. Today, we will be using a tool called Enum4linux to extract information from a target, as well as smbclient to connect to an SMB share and transfer files.

You may have recently seen a plethora of Instagram users, including celebrities and politicians, sharing a screenshot declaring that the platform will implement a new "rule" where it would own and could use your photos and videos however it wishes. The screenshots are part of an internet hoax, one that's been around in one way or another since 2012, but what can Instagram actually do with your media?

When researching a person using open source intelligence, the goal is to find clues that tie information about a target into a bigger picture. Screen names are perfect for this because they are unique and link data together, as people often reuse them in accounts across the internet. With Sherlock, we can instantly hunt down social media accounts created with a unique screen name on many online platforms simultaneously.

Gathering information on an online target can be a time-consuming activity, especially if you only need specific pieces of information about a target with a lot of subdomains. We can use a web crawler designed for OSINT called Photon to do the heavy lifting, sifting through URLs on our behalf to retrieve information of value to a hacker.
So, you rooted your Pixel 2 or 2 XL and everything seems to be working quite well. However, a month passes, and you get a notification to install the monthly security update. Like clockwork, Google has been pushing out OTA security patches every single month for a while, but there is a new problem for you at this point — as a rooted user, you are unable to apply the update correctly.

For some Android users, this guide is sacrilege — but for others, iOS is just an attractive operating system that can be admired without feeling like you've betrayed your own phone. If you're one of those Galaxy Note 9 owners that have peeked across the aisle and desired an interface as clean as the one on the iPhone XS Max, you can configure your Note 9 to look like its rival with some tinkering.

A convincing domain name is critical to the success of any phishing attack. With a single Python script, it's possible to find hundreds of available phishing domains and even identify phishing websites deployed by other hackers for purposes such as stealing user credentials.

After two years of poor sales, LG decided to shake up its mobile division. New executives are at the helm, and changes to their flagship lineups are already underway. Specifically, the V series is expanding, as LG announced the second new device in the series, the LG V35 ThinQ.

Local port forwarding is good when you want to use SSH to pivot into a non-routable network. But if you want to access services on a network when you can't configure port-forwarding on a router and don't have VPN access to the network, remote port forwarding is the way to go.

Waze is the go-to navigation app for millions of drivers, and it's easy to see why. Benefits such crowd-sourced traffic data, police trap locations, and road work avoidance are just the tip of the iceberg. It can almost be overwhelming, but with these simple tips, you'll master Waze and start navigating like an expert in no time.