During our last adventure into the realm of format string exploitation, we learned how we can manipulate format specifiers to rewrite a program's memory with an arbitrary value. While that's all well and good, arbitrary values are boring. We want to gain full control over the values we write, and today we are going to learn how to do just that.

In our previous article, we learned how to take advantage of a feature, Dynamic Data Exchange (DDE), to run malicious code when an MS Word document is opened. Because Microsoft built DDE into all of its Office products as a way to transfer data one time or continuously between applications, we can do the same thing in Excel to create a spreadsheet that runs malicious code when opened. The best part is, it will do so without requiring macros to be enabled.

If you need a tiny, flexible attack platform for raining down human-interface-device (HID) attacks on unattended computers, the USB Rubber Ducky is the most popular tool for the job. By loading the Ducky with custom firmware, you can design new attacks to be effective against even air-gapped computers without internet access. Today, you'll learn to write a payload to make "involuntary backups" through copying a targeted folder to the Ducky's USB mass storage.

A new Google Search update lets job-seekers streamline their search process. Searches like 'jobs near me' are now designed to show relevant opportunities from multiple sites.

User interfaces for computers have evolved over the years, from the introduction of the keyboard and mouse on the personal computer, to touchscreens on mobile devices, to natural voice recognition. However, the same cannot be said for robots or drones—until now.

WordPress did not become what is arguably the most popular blogging and CMS platform on the planet because it was difficult to use. Rather, its user-friendly and rich feature set led to it finding a home on somewhere north of 70 million websites—and that's just counting blogs hosted on WordPress.com.

Hey guys I am starting this Series because I thought there was a lack of post about Hacking from Android.

This video will show you how to clean the battery cable terminals on your battery.

Welcome back, my nascent hackers! In the conclusion of the Mr. Robot television series, Elliot and fsociety successfully completed their mission of encrypting all of Evil Corp's data with AES-128 encryption and destroying the key.

So this is my methodology for this project of writing a rootkit. Please leave feedback on what is right/wrong. I tried to simplify concepts the best I could however...

Hello fellow training hackers. I do not know if many of you are familiar with ruby, but since it is a useful scripting language, that hasn't been covered too much here on Null Byte, I thought why not do some How-tos about it now and then.

Hello! I'm newbie at Null Byte and I want tho share some of my thoughts with you guys, hope you like it. I've been inspired by 3 facts for making this: 1- The post 'How to write better code', 2- A few illegible comments at some posts, 3- I myself have never written such a long text in English, this will be my first one!

Spotlight, Apple's selection-based search system, received a major facelift on Mac OS X Yosemite. Packed with dozens of new features, such as a central search window and increased app suggestions, the reworked Spotlight was a breath of fresh air.

NOTICE: Ciuffy will be answering questions related to my articles on my behalf as I am very busy. Hope You Have Fun !!!

Welcome back, my budding hackers! This is the initial post of a new series on how to hack Facebook. It's important to note here that each hack I'll be covering is very specific. I have said it before, but I feel I need to repeat it again: there is NO SILVER BULLET that works under all circumstances. Obviously, the good folks at Facebook have taken precautions to make certain that their app is not hacked, but if we are creative, persistent, and ingenious, we can still get in.

What if someone asks you to do a Nmap scan but you left your pc at home? What if a golden opportunity shows during a pentest but you were walking around the building, taking a break?

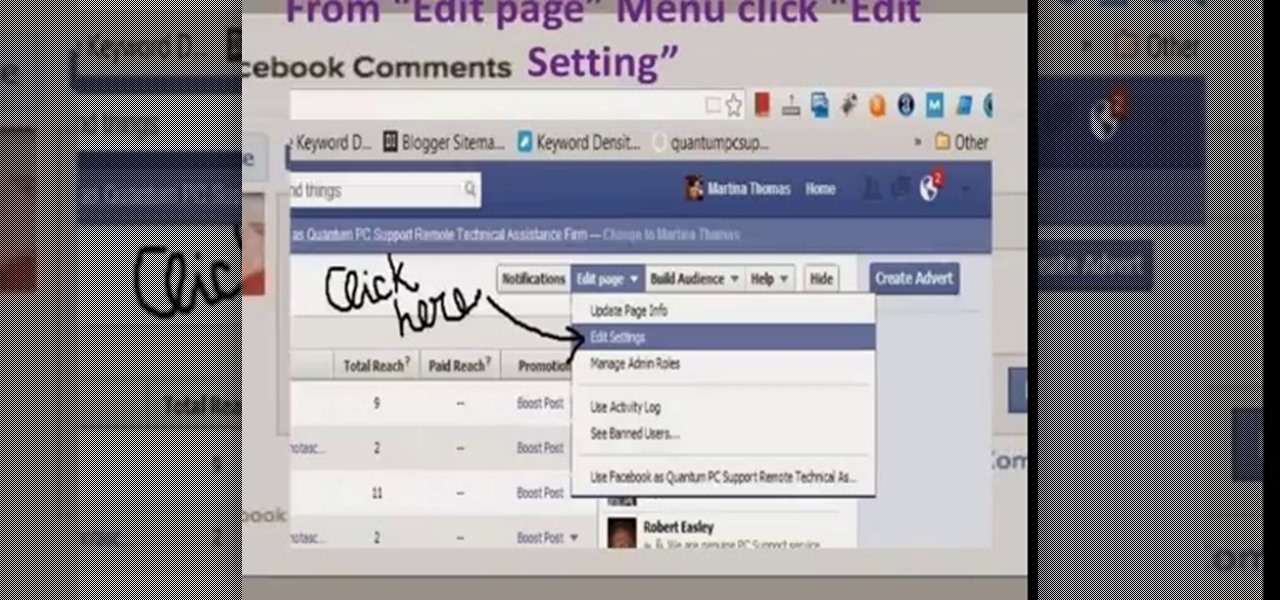
This video will show you how to stop Facebook comments in your post. This is useful to prevent spam comment or scam in a business page. Watch the video and Follow all the steps. Employ the technique in your Facebook account.

Welcome back, my aspiring hackers and those who want to catch my aspiring hackers! As most of you know, this series on digital forensics is inspired by the motivation to keep all of you all out of custody. The more you know about the techniques used by law enforcement and forensic investigators, the better you can evade them.

Today I am posting a double feature the first guide on the video shows you how to disable the Xbox controller guide button stats on the PC so you can use it as an extra button. The second guide shows you how to play the Alpha version of World of Warcraft.

Latest sneeze prank video, from professional pranksters over at DM Pranks Productions. This is a followup from the epic "sneeze prank gone wrong" I posted last week. Check this out, simply amazing!

Every year the fine folks at Row Three do a post-TIFF mega-wrap up, collecting the micro-blurbs of a bunch of attendees into a giant meta-analysis of what everyone liked, loved, hated, etc. etc.. We'll link to that post when it goes up on the weekend, but in the mean time, here's my contribution:

Hey everyone! This is BlueBandit, and below I have posted the newest video in my Let's Play of DKC2. If you enjoyed it, please go here to watch the rest, and also don't forget to subscribe!

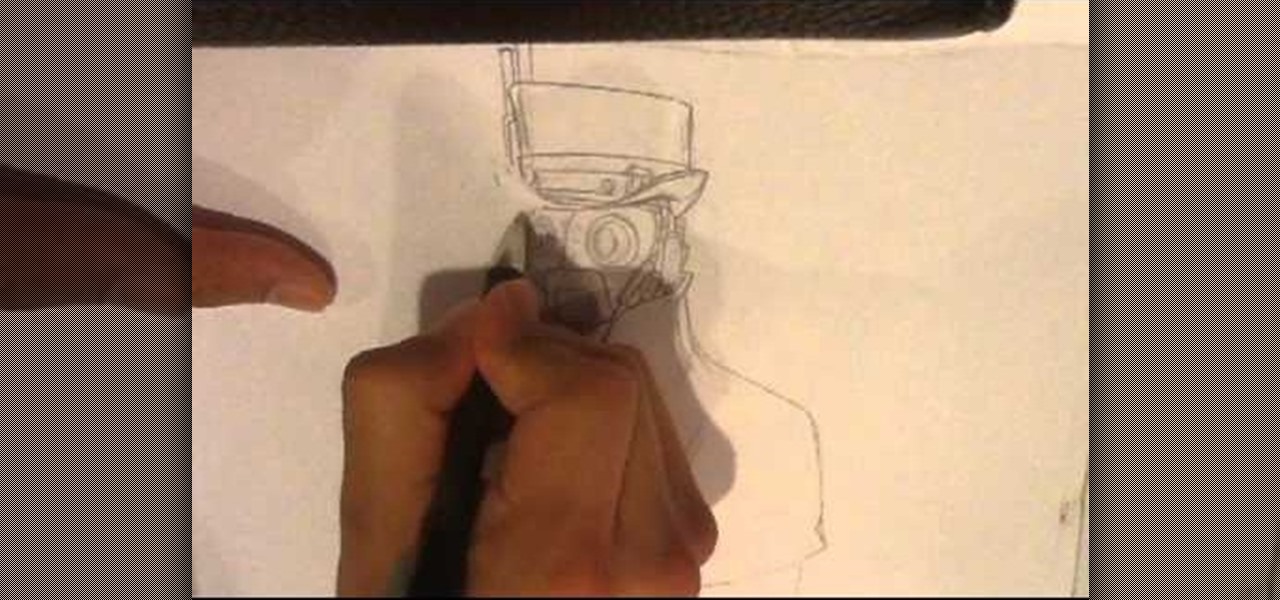
How to Draw Steampunk. I go over a little bit on steampunk information. The various sources to get knowledge on steampunk looks. On my drawing sites, there are other drawing videos, art videos, art tutorials, and more how to draw fantasy posts. Easy things to Draw. For my main blog go here:http://howtodrawfantasyart.blogspot.com/

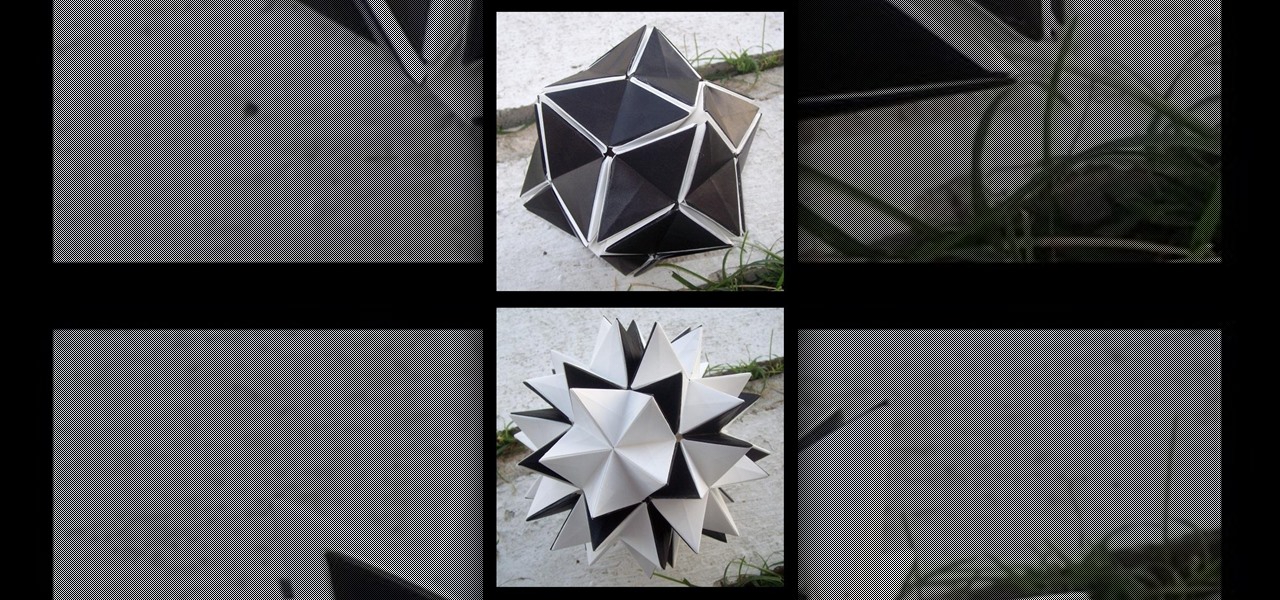
This video tutorial will show you how to make a beautiful Revealing Flower. The awesome thing about the Revealing Flower is that you will be able to open and close the petals. It will take 90 pieces of paper. Do not use printer paper. (you might as well use Post-Its) You will also need glue. Here's the video tutorial:

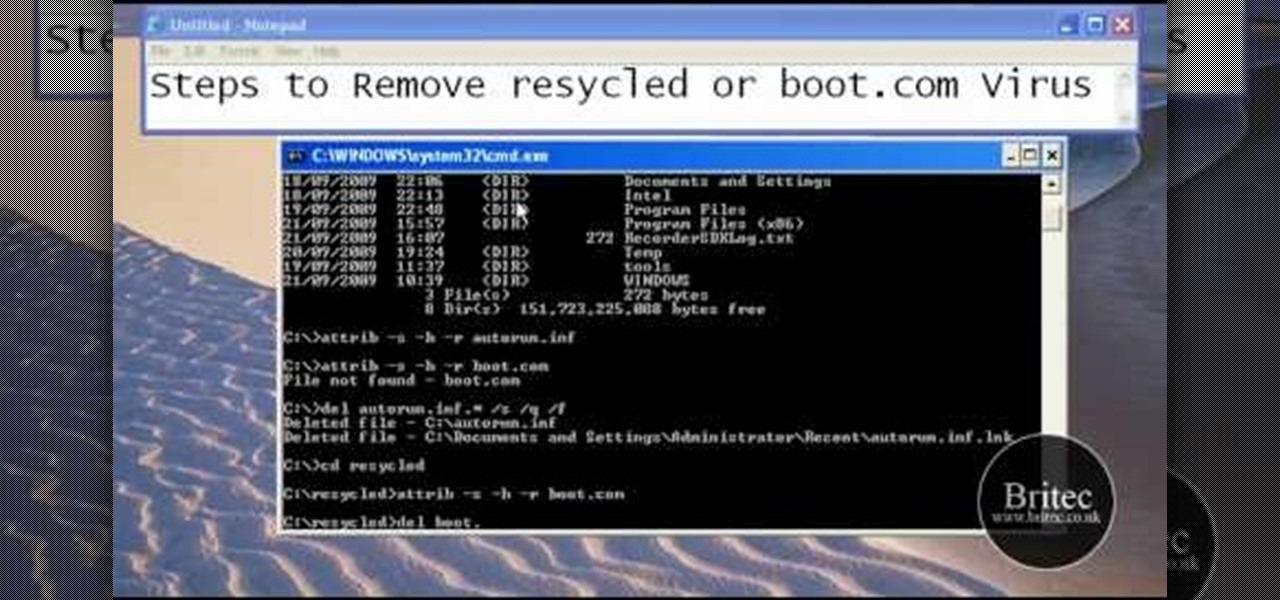
This tutorial describes the procedure to remove autorun.inf and boot.com virus. This virus is commonly called as resycled/boot.com virus, which could damage the system files and may steal important information from the system.This can be removed by any malware / spyware remover like Malewarebytes.

Design Sponge has posted some very pretty, tiny terrariums and air plants to brighten up these cold winter months. Buy them through Etsy seller Tortoise Loves Donkey or make your own. Scroll down for Design Sponge's terrarium how-to.

Thinking of deep frying a turkey this Thanksgiving? Careful, or this might happen: Video: .

It was bound to happen with all those numbers floating around in your brain – you've forgotten your Windows password. Here's how to recover it.

This fashion how to video has great tips on how to dress the post-partum body. If you just had a baby, you'll notice that your old clothes just don't quite fit. Get some great fashion tips on how to disguise those troubled areas after pregnancy to make your feel better.

This video shows how to thread your bobbin on a side threading sewing machine. We start off by making sure that the needle is in the most upright position. The upper thread guide when moved to the most top of its travel, the needle is in the most upright position.Then you take the bobbin case and your bobbin. Make sure the thread is coming up over the top towards you and not underneath and over the back. Slip in the bobbin into its case, put the thread through the groove under the potential s...

As your home ages, so does your deck in the backyard, but there are ways to resolve this issue. If that wooden deck is looking weathered or worn, you can simply replace the components with composite materials without a complete rebuild. Composite doesn't splinter or have knots, and it's low maintenance. This two-part video, brought to you by Lowe's, will show you exactly how to renew your deck with composite decking.

In this video, we learn how to enable the Windows default administrator account to appear at the log in screen. First, go to your "start" menu and type in "cmd". Right click "cmd" and click "run as administrator". Now click continue and type in "net user administrator /active:yes", (making sure you put the appropriate spaces), and press enter. Now it will say your command was done successfully on the space underneath where you just typed your text. When you restart your computer you will now ...

First, on your computer access your command prompt and type in ipconfig. Find the line called default gateway and write it down for later. Type your default gateway into your internet address bar and it will bring up your router setup page. Find your upnp and enable it, this will open your NAT. Start your XBox 360 and go to system settings on your XBox dashboard, go down to network settings and test your connection. Next go to IP settings then manual then IP settings. You want to change your ...

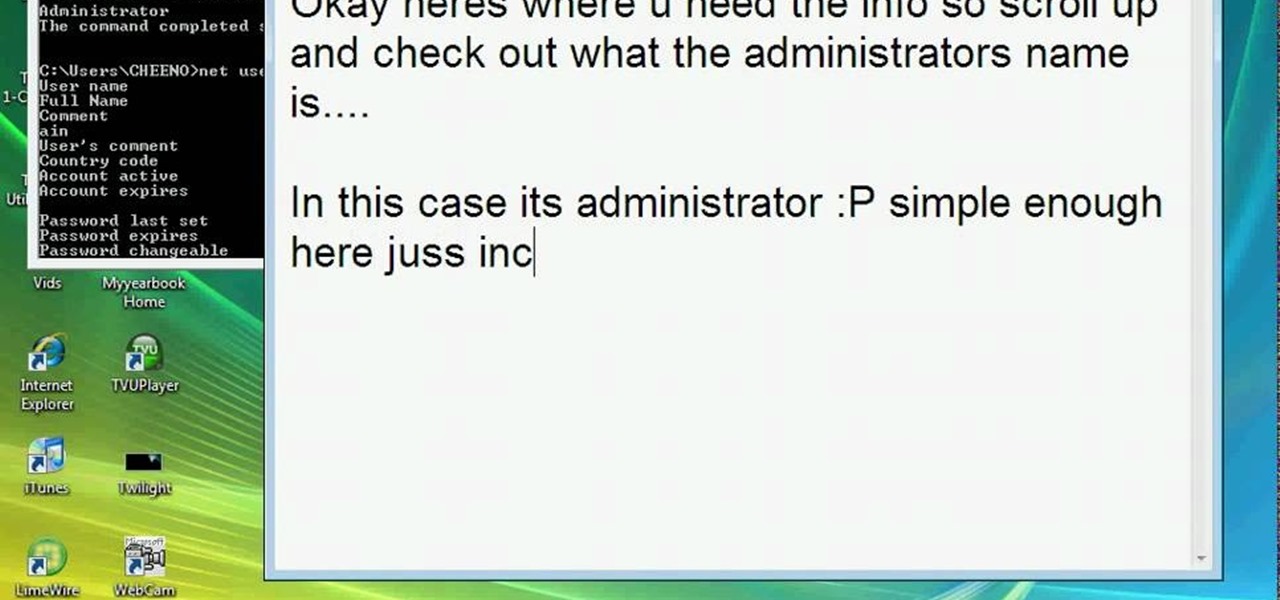
This video teaches how to change/hack administrators Account/Password. Click START and find CMD. Type "net user" without the "". Now type "net user administrator" without the "". Scroll up the screen and find the administrator's name. Now go back down and type "net user administrator *" without the "". Now it will ask you for a new Password. Type a new Password which you won't forget. Now another command prompt will pop up. Just type in exit to come out of the CMD. Don't get caught and do it ...

A video from PC Mech that shows you how to install application in Sabayon Linux, a Linux flavor that is based on Gentoo Linux and is known for its ease of use.

Look at the Main Menu on our screen. If the Icons on the screen do not respond to your commands, it means that the system is corrupted. To fix this problem, hold and press down the Power and Menu button at the same time for about 6-8 seconds or until you see a black and white Apple logo right on the middle of the screen; after the icons disappear. This means that your system is rebooting without losing any of your original data. This ensures the system functioning properly again as soon as yo...

New to Ubuntu Linux? This computer operating system could be a bit tricky for beginners, but fret not, help is here. Check out this video tutorial on how to download files from FTP with Terminal on Ubuntu Linux.