Android 11 won't be available as a beta update for Pixel devices until May 2020. Until then, the only way to try the latest Android version is by manually installing it. Usually, this means carrier models are left out since their bootloaders are locked, but there's still a way to get it done.
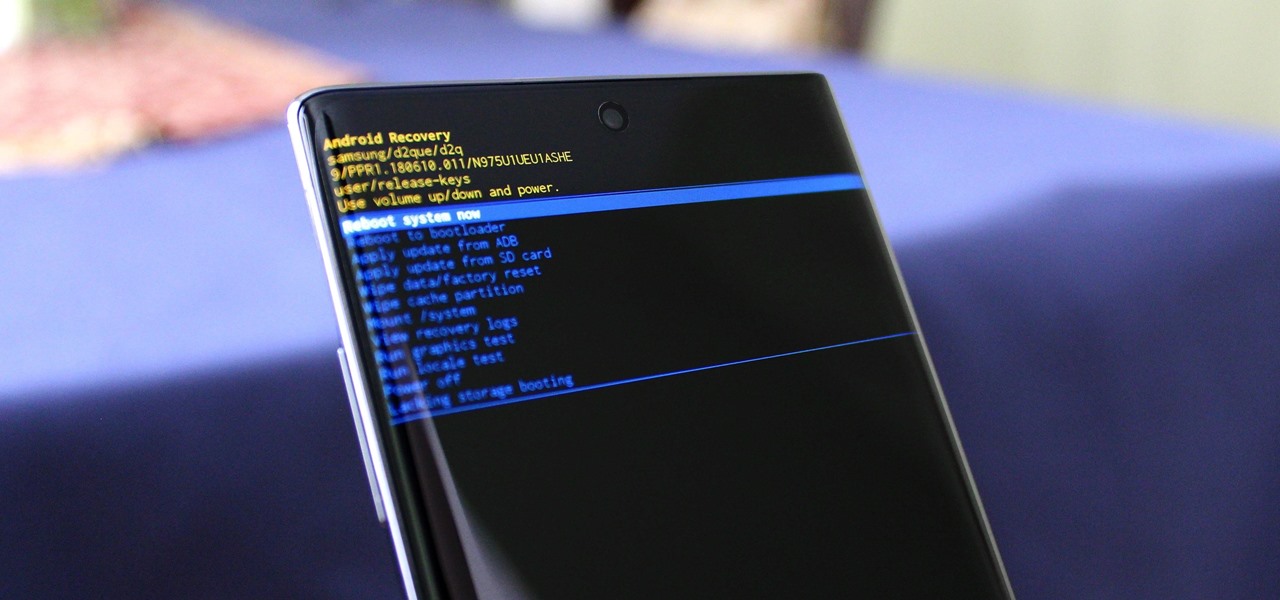
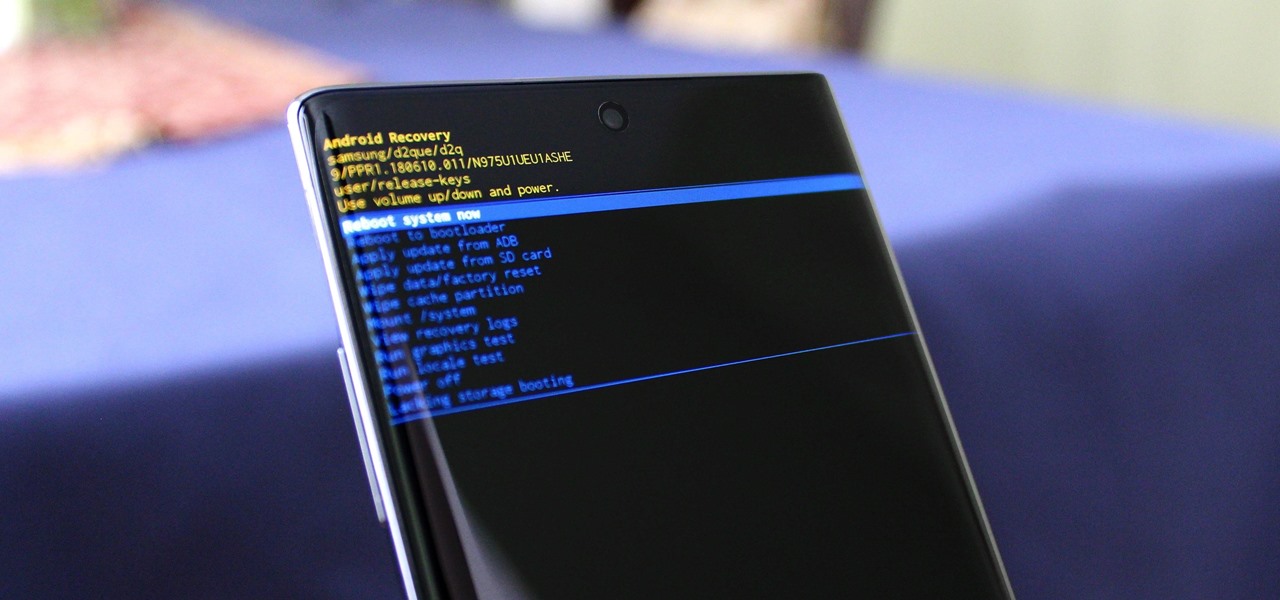
You can't call yourself an Android pro without knowing about Recovery or Download Mode. These menus are critical to do more advanced tasks on your phone, include sideloading software updates and un-bricking a device. But this year, Samsung changed the button combinations that will get you there.

After years of user complaints, Samsung is finally letting us remap the Bixby button without the need of a third-party app. The new feature requires One UI a simple app update to Bixby, but there's one major downside: Samsung won't let you remap the button to open other digital assistants like Amazon Echo, Microsoft Cortana, and Google Assistant. Luckily, there's an easy workaround.

With just one line of Ruby code embedded into a fake PDF, a hacker can remotely control any Mac computer from anywhere in the world. Creating the command is the easy part, but getting the target to open the code is where a hacker will need to get creative.

In the previous article in this short series, we learned how to find our neighbor's name using publicly accessible information and how to monitor device activity on their home network. With this information at our disposal, it's time to get into installing and configuring the necessary tools to begin our attack on John Smith's computer.

Android used to have a notification ticker, but those days are long gone. Now, important new messages pop up on the top half of your screen with what's known as a "heads up notification." If you're in the middle of something, these popup notifications can be pretty annoying — luckily, it's pretty easy to turn them off.

As pentesters and hackers, we're going to be working with text frequently — wordlists, configuration files, etc. A lot of this we'll be doing on our machine, where we have access to whatever editor we prefer. The rest of it will be on remote machines, where the tools for editing will be limited. If nano is installed, we have an easy-to-use terminal text editor, but it isn't very powerful.

Welcome back, everyone! In this lesson, I'm going to go over the use of the echo function and variables, as well as basic syntax.

Right, So i've been asking alot of questions here on Null-Byte and everyone has been really helpful to me.

UPDATE: This post is outdated, the latest version with the correct links and updated instructions can be found at my blog, here - https://techkernel.org/2015/12/19/embed-metasploit-payload-in-apk-manually/

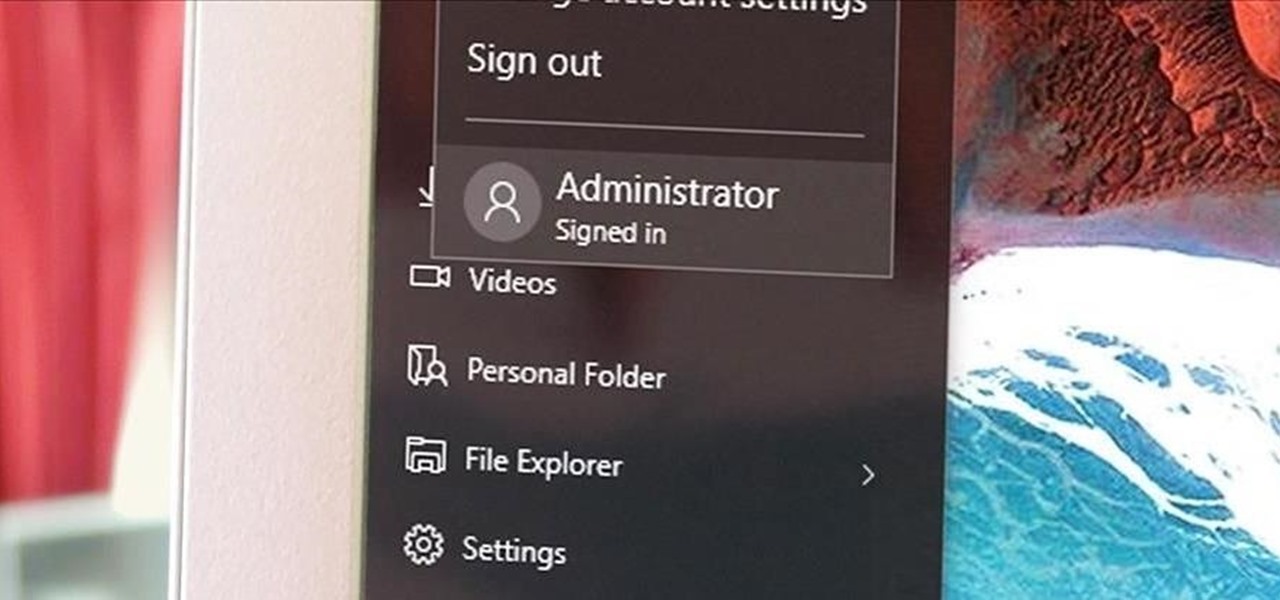
Windows has always had an "Administrator" account that allowed you to install programs and manage system files with elevated privileges. The difference between this account and a regular user account with administrator access was that you never got bothered by annoying User Account Control popups when you were logged in as Administrator.

Imagine this scenario: You exploited a system using metasploit and you want to install a backdoor. You have a few options;

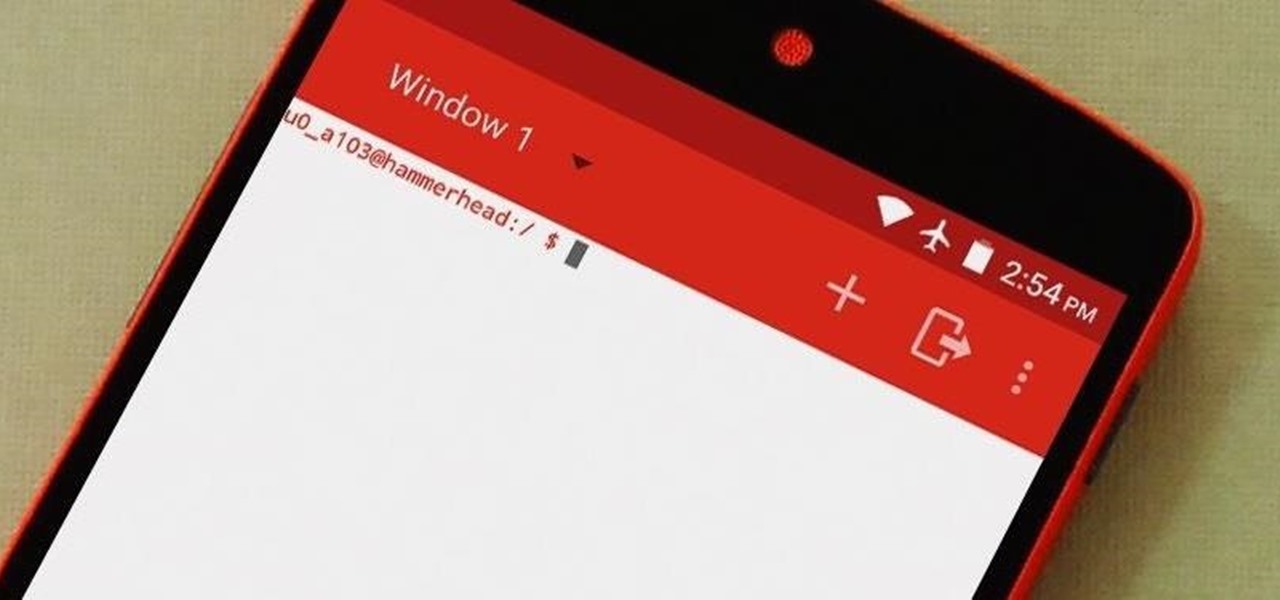
Deep down, Android is a fork of Linux, which is a desktop operating system that started out as entirely command prompt-based. For that reason, many system-level tasks can still be executed within a terminal emulator app.

Android Debug Bridge, or ADB for short, is a very powerful utility that can remotely execute commands on your Android device. This remote terminal interface, however, is not very "remote" at all. You have to be tied down to your computer to use it, since a USB cable is normally required.

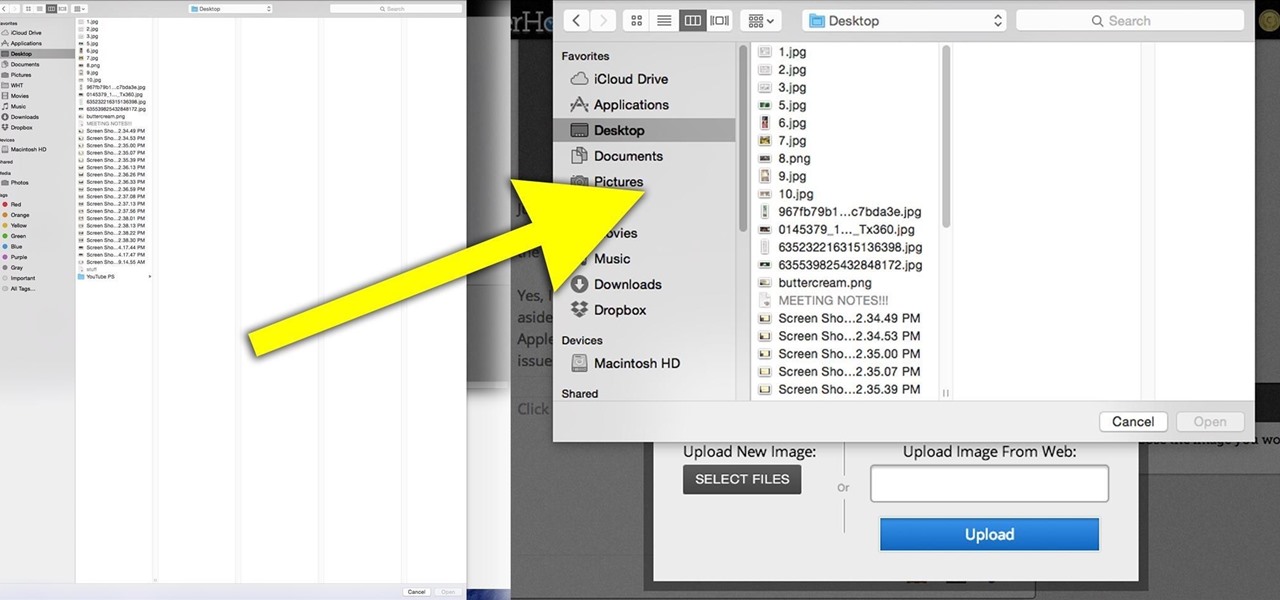
Yosemite is definitely an improvement over Mavericks, but there are still some painfully obvious and annoying bugs that occur within certain apps.

Anyone who has rooted their Android device has likely used a tool called Android Debug Bridge, better known as ADB, at some point during the process. For most, that is their only interaction with the ADB, but to be a true Android power user, you need to really know the tools at your disposal.

Watch out Samsung (and you too, Pebble, Sony and the still unrealized Apple), your hold on the smartwatch market is about to get a lot less firm. Announced today, Google has released Android Wear, their platform for developing smartwatches, along with a preview of the Moto 360 smartwatch from Motorola.

In my first tutorial on Linux basics, I discussed the importance of hackers using Linux and the structure of the directory system. We also looked briefly at the cd command. In this second Linux guide, I'll spend a bit more time with changing directories, listing directories, creating files and directories, and finally, getting help. Let's open up BackTrack and getting started learning more Linux for the aspiring hacker.

AppleScript is quite an easy scripting language to use. In this guide, I will be showing you several commands. Near the end, I will show how these can be used to create a fake virus that actually does no harm.

This is an instructional video on how to fold an octahedron with Post-It notes. Use 3 different colors of Post-It notes. Take 2 Post-It notes in the same color, fold it horizontally and diagonally to make four squares. Fold diagonally the sticky side, you will end up with a cross or a star. Put the tight corner between the gap, alternating the color. That's it! You will end with an octahedron Watch this video and make an octahedron using Post-It notes by yourself.

In this four-part video, learn how to create a CMS with PHP and MYSQL. The basics of a simple CMS are split up in the following four parts:

Rolling over is a simple trick that any dog can master, and it will help you build confidence in your dog. Learn how to teach your dog to roll over with this how to video.

Teaching your dog to sit establishes trust and also creates a foundation for other tricks. Learn how to teach your dog to sit with this dog training video.

Post-mount brakes are just one of many types of brakes that can be installed on a mountain bike. This video features detailed instructions on how to set up a post mount brake on an IS mount, making your mountain bike stop like Deepwater Horizon spill refuses to. It is a complicated process, but a rewarding one.

This video shows us how to build a garden bench out of cinder blocks. Before you get started, you need to refer to the How To sheet #320 for all your materials and make sure you have everything you need.

A mailbox can be the first thing people see on your property, so it's important to get a nice one and install it correctly. But installing a mailbox post and mailbox can be a surprisingly tricky project, involving making holes in the ground and trying to get the post to stand at just the right height. In this video, Mark Donovan of HomeAdditionPlus.com shows us how to install a mailbox the right way.

In this clip, you'll learn how to generate admin command prompts on a desktop or laptop computer running the MS Windows Vista operating system. For more information, including a complete demonstration of the process and detailed, step-by-step instructions, watch this home-computing how-to.

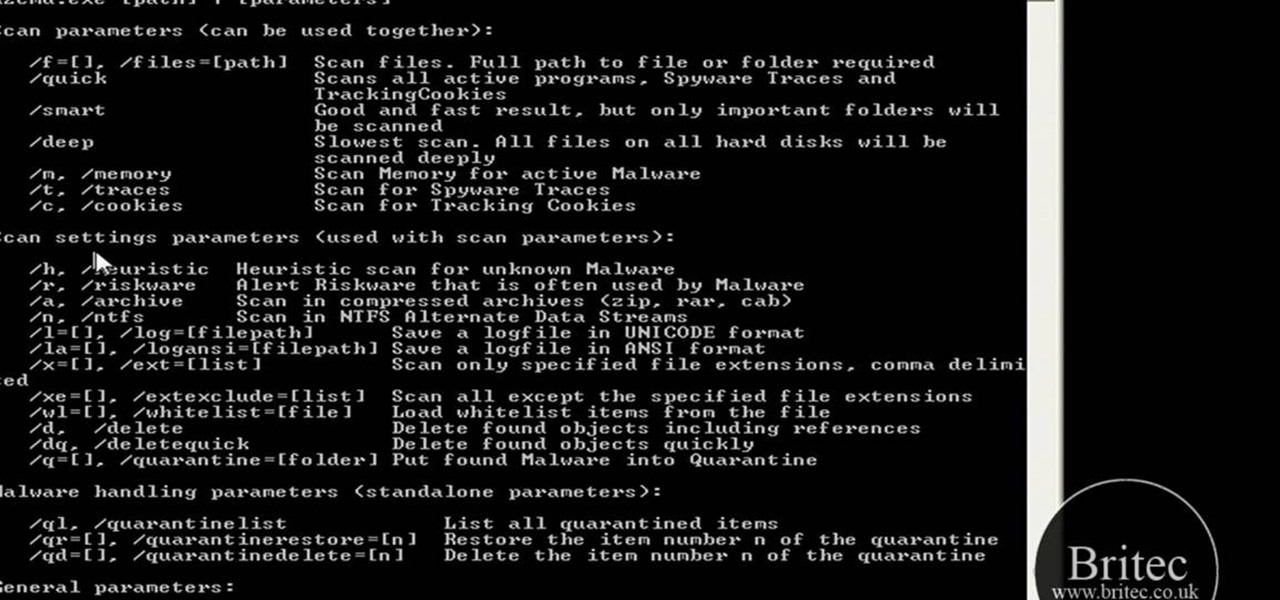
Want to know how to remove viruses, adware and other sorts of malware from the Windows command line? It's simple! So simple, in fact, that this home-computing how-to from the folks at Britec can present a complete overview of the process in just over four minutes. For more information, including step-by-step instructions, watch this video guide.

Interested in adding a shortcut to the command prompt to the right-click Explorer menu in Microsoft Windows XP? It's easy! So easy, in fact, that this home-computing how-to from the folks at Britec can present a complete overview of the process in just under five minutes. For more information, including step-by-step instructions, take a look.

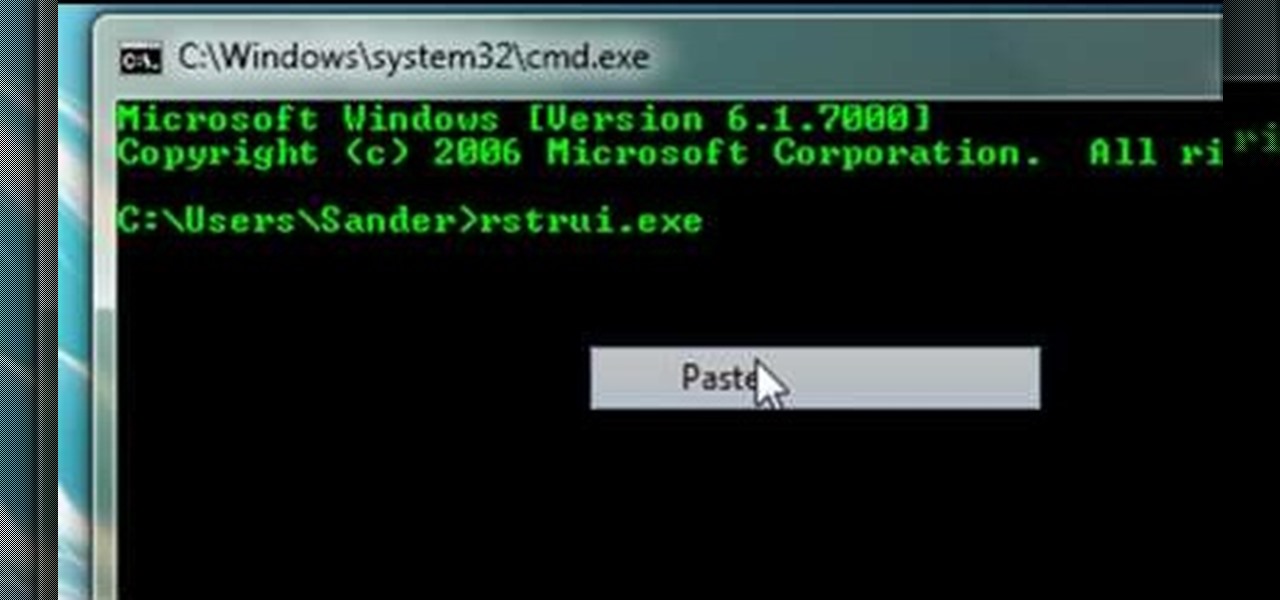
Computers aren't perfect. Just like people, they have their set of flaws and issues that can be resolved quickly and easily. You just have to take the right approach. So in this tutorial find out how to use command prompt on your computer to help restore it. Enjoy!

Ever plug in a Windows keyboard to a Mac only to be frustrated by the swapped layout? This computer tutorial video shows you how to iron out the mix up with this quick tip. Watch this how-to video to learn how to easily make the transition from Mac to PC (and vice versa) by taking control of your command keys.

Linguist Bud Brown shares some insights and advice about learning Vietnamese. This video talks about how to say the imperative (command) form.

These tricks are all based on nothing more than solid command of double flips. Watch an actual demonstration of double flips. Learn how to use consistency and command.

Bob and Brett show you how to burn your mixes on CD using a command called "bounce" in Pro Tools.

OnePlus phones are easy to root, but that also means they're easy to brick if you get trigger happy with your superuser privileges. If you find yourself in this situation, you'll quickly realize the OnePlus firmware download page doesn't provide files you can flash in Fastboot mode.

One vital part of Android 10's new navigation system is the "QuickStep" gesture. Swipe up from the bottom of your screen, then pause. You'll see your recent apps along with a dock containing a handful of icons for quick access. This dock is provided by the phone's launcher, which means your home screen is now integrated into the multitasking UI. So what happens if you change your home screen app?

Apple's Gatekeeper security software for macOS (Mac OS X) is vulnerable to remote attacks up to version 10.14.5. An attacker that's anywhere in the world can exploit MacBooks and other Mac computers by sharing a single ZIP file.

It's important to know who you're dealing with after hacking your target's MacBook. Getting remote access is simple, but covertly gathering information about the user and their system can be a challenge.

Gmail conversations, Facebook private messages, and personal photos can all be viewed by a hacker who has backdoor access to a target's Mac. By livestreaming the desktop or exfiltrating screenshots, this information can be used for blackmail and targeted social engineering attacks to further compromise the mark.