Two years ago, driven by a good friend of mine i decided to give it a try on timelapse photography. I had a DSLR camera but didn't had an intervalometer, so i assembled a small electronic circuit on top of an Arduino Uno, made some basic code and did my first timelapse movie. The result was awful, but for some reason I was hooked.

In the Apple's iOS beta 3, we were introduced to a new iCloud Drive feature, an option to disable QuickType, time indicators for Recently Deleted pics, and a way to keep "self-destructing" media.

Welcome back, my tenderfoot hackers! In continuing my series on digital forensics using Kali, I want to introduce you to two complementary tools, both built right into Kali Linux. These are Brian Carrier's tools Autopsy and Sleuth Kit.

Clash of Clans is one of the most successful games ever to come out for Android and iOS. It has been downloaded over 50 million times from Google Play alone, and shows no signs of decline.

Love making gifts for your loved ones? Here is a tutorial that shows you how to make a play doh rose. It's really easy and fun to make.

There are over one million apps in the Google Play Store, and many of them are restricted to certain device types, brands, and Android systems.

Instinctively, we reach for popsicles and cold drinks when the temperatures climb, but doing something counterintuitive, like going for a hot drink or eating something spicy, is actually more effective at keeping you cool.

A dead British science nerd figured out the best way to cut a cake to preserve maximum freshness, and it's pure genius (well, sorta). His name? Sir Francis Galton, a polymath infamously known as the founder of eugenics, and apparently owner of a very big sweet tooth.

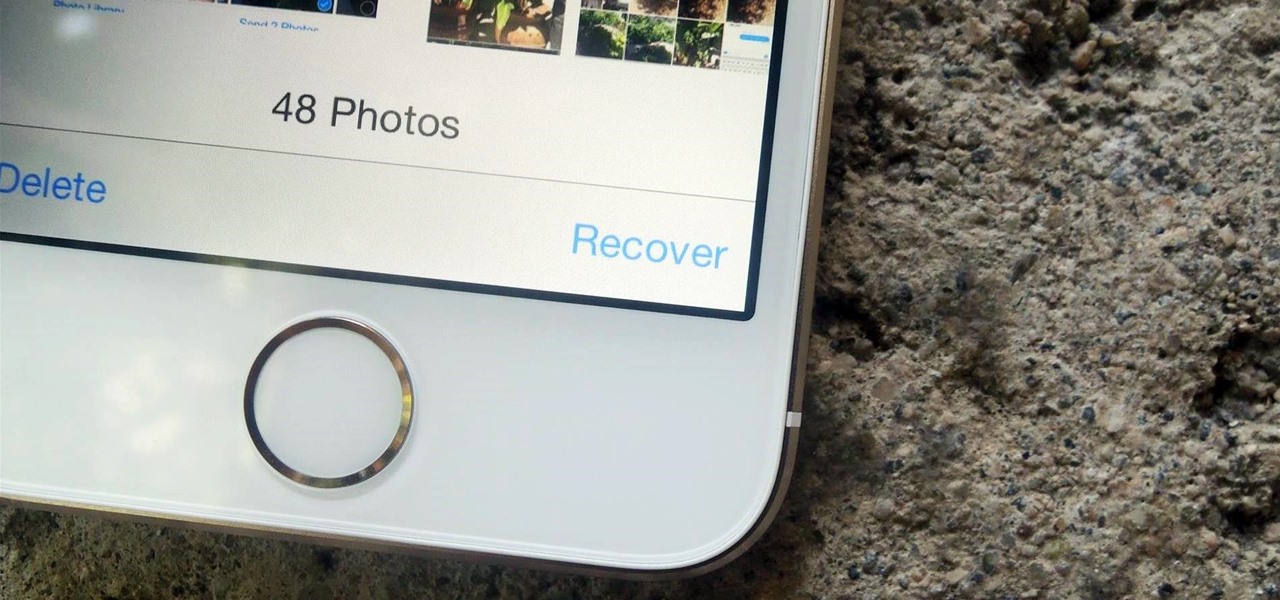
What happens when you accidentally delete a photo or video from your iPad or iPhone? How do you get it back?

Buying and drinking wine can be intimidating. There's so much to know, and so many ways to reveal your ignorance. If you're completely befuddled by wine and how to describe it, don't worry, you're not alone.

When I became serious about cooking, nearly every cookbook and guide I picked up emphasized the importance of using fresh stock, whether it was chicken, beef, or vegetable. When I didn't have time to make my own, I bought the highest quality boxed or canned stock I could find at the market.

Welcome back, my aspiring hackers and those who want to catch my aspiring hackers! As most of you know, this series on digital forensics is inspired by the motivation to keep all of you all out of custody. The more you know about the techniques used by law enforcement and forensic investigators, the better you can evade them.

It seems that Apple is taking a page from Google's book with their new "Hey, Siri" voice activation feature in iOS 8. This feature mimics the one found in Google Now, the voice-activated intelligent personal assistant available to just about all Android users. Apple's version allows you to bring up Siri with a simple voice command, but there's a small catch.

If you've ever seen one of those Samsung commercials from about a year back, you know that the Galaxy S series of phones come with a feature that allows you to do certain things by making gestures in front of your screen. They call this feature Air Gesture, and it enables you to perform certain functions without even touching your phone.

If you've followed our guide on unlocking KitKat's real full screen capability using the immersive mode mod, then your status and navigation bars will be hidden when not in use, giving you a more expansive full screen experience.

Over the years, we've probably all complained at some point about Android's lack of an "Undo" feature. When you're typing something out, there are times when you might want to go back a step.

Veering from common practice, XDA commenter, "the_commenter", discovered a changelog for the upcoming version of Android 4.4.3 tucked away on Google's servers.

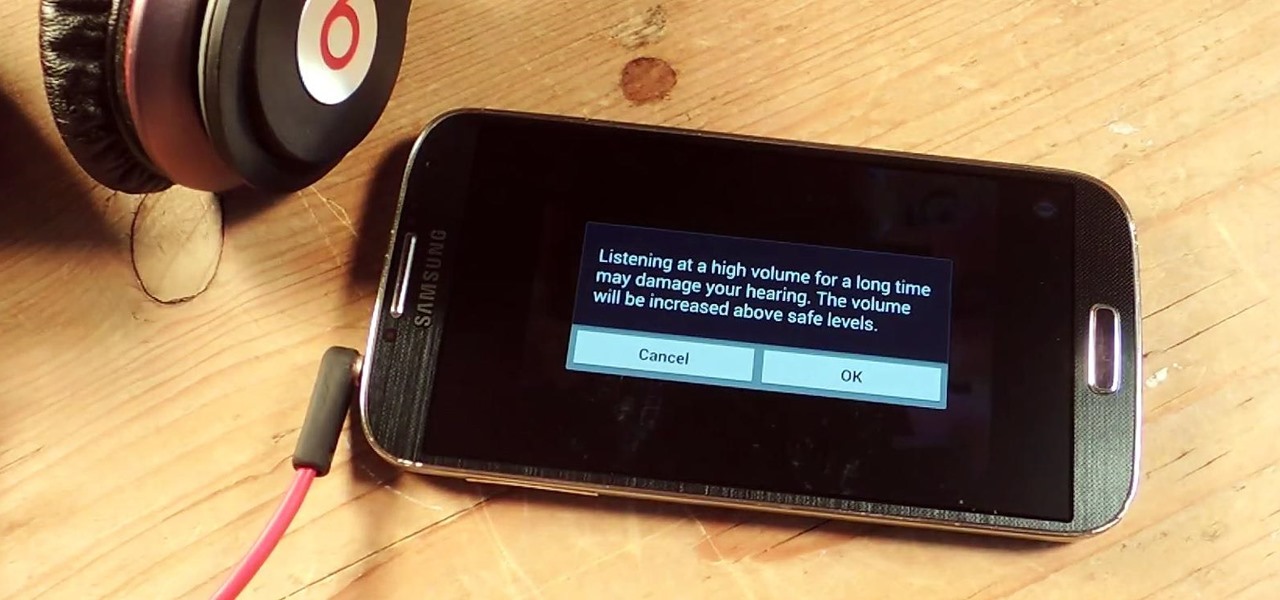
I've been told numerous times that I listen to music way too loud, to the point of potential hearing damage, especially when I have my headphones plugged in. Not only do my friends tell me this, but my Samsung Galaxy S4 likes to nag me as well. Once I pass a certain volume threshold (nine steps) with my headphones, I get that annoying high volume alert. Sorry, my hearing isn't as good as it once was, so let me jam in peace!

When the Nexus 5 was released, a new version of Android came along with it called KitKat. In the 4.4 update were some fancy new UI elements, one of the most noticeable being the translucent decor. By that, I mean the status and navigation bars being semi-transparent.

The new HTC One and Nexus series devices have already replaced their physical navigation keys with soft keys, and it's inevitable that we'll see more and more of this on future mobiles. Samsung continues to buck the trend entirely, but no manufacturer as gone as far as to remove the volume rockers.

We've already taught you a few tricks for getting chilled, rock-hard butter to spread easily on toast, and some of you probably bypass that issue entirely by purchasing spreadable butter from the supermarket. But why waste your money when you can make a healthier, tastier version at home for a fraction of the cost?

Doritos Locos Tacos were the brilliant concoction of a man named Todd Mills who never worked for Taco Bell, and never made any money from his creation. He originally pitched the idea to Frito-Lay, and when they said no, he took matters into his own hands by creating a Facebook page.

You've seen the Samsung Fingers and the Emoji Translator, and I know you spent a good part of the day catching Pokémon, but now that April Fool's Day is officially upon us, the flood of gags has reached a tipping point. Here's the best of what we've seen today.

I never want to bump into my ex-girlfriend while out in the city (talk about a buzz kill), so if I could get an alert telling me that she's at Shortstops down the street, I'll avoid that area completely. This is where the new, interesting app Cloak - Incognito Mode for Real Life from dev Brian Moore comes in.

Watch out Samsung (and you too, Pebble, Sony and the still unrealized Apple), your hold on the smartwatch market is about to get a lot less firm. Announced today, Google has released Android Wear, their platform for developing smartwatches, along with a preview of the Moto 360 smartwatch from Motorola.

Imagine that Tinder fornicated with Facebook and had a baby. The product of that union would be the hideous, yet overwhelmingly interesting SocialRadar, an app dedicated to stalkers and stalkees.

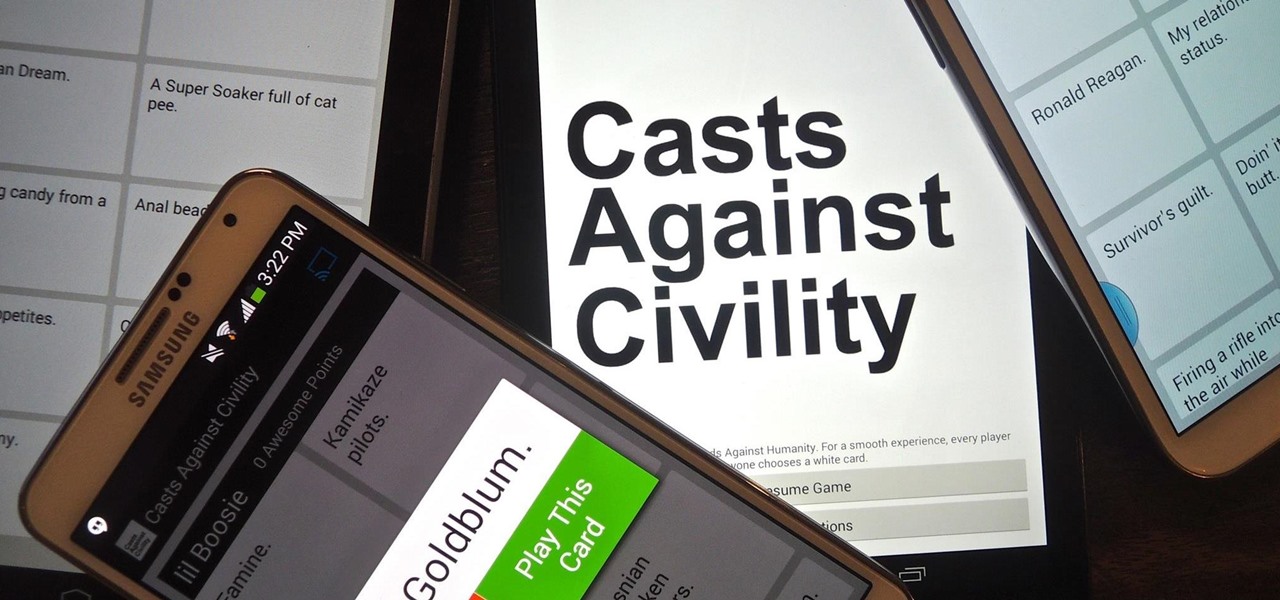
If you've never played Cards Against Humanity, it's time to get initiated. Originally funded through Kickstarter, the free to download card game is basically an obscene version of Apples to Apples.

Android is all about the fine details. You can make a little tweak here and a little tweak there and completely customize your experience to be exactly how you want it to be. Sure, you don't need to customize LED colors or screen record, but it's nice to know you can.

In direct competition with Pandora, iTunes Radio, and Spotify, Samsung has just launched Milk Music—a strangely named, yet completely free music streaming service for Android.

Rock-hard ice cream is the bane of my culinary existence. If I try and scoop it out with a spoon, the spoon invariably bends. If I use a traditional ice cream scooper, I end up with a torqued wrist and one or two pathetic curls of ice cream for my efforts.

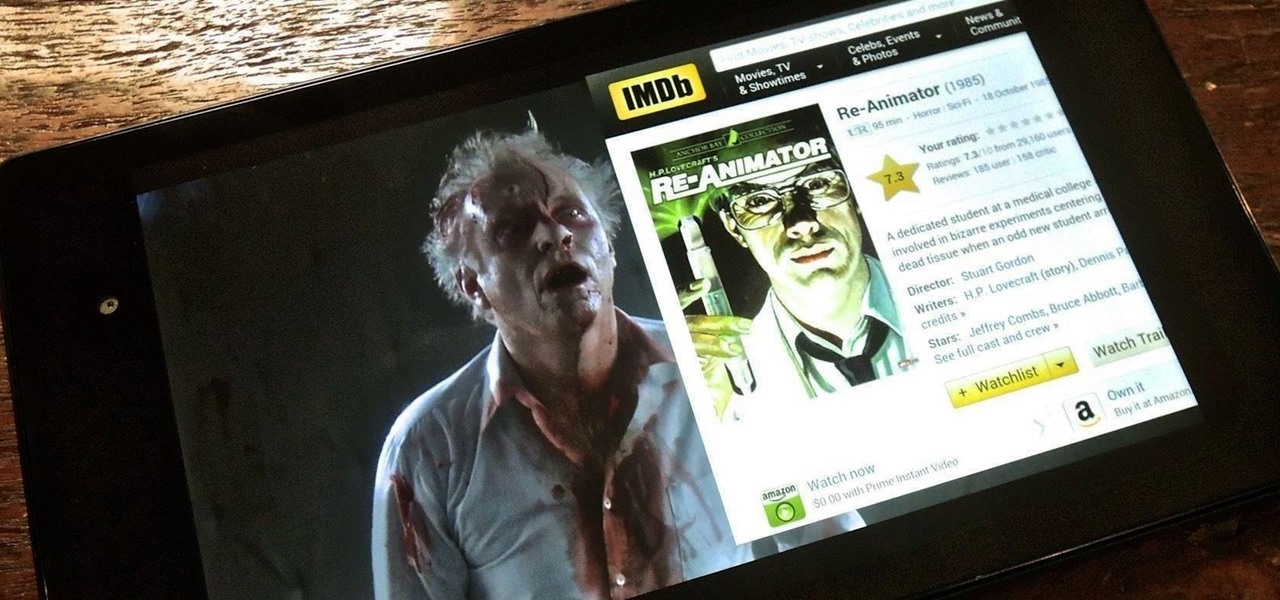
Efficiency is one integral attribute that I need from my Android device. I want to be able to multitask like a maniac and do things on the fly. While multitasking itself is nothing new, actually being able to watch Netflix while scrolling through IMDB at the same damn time was reserved mainly for newer Samsung-ier devices.

Greetings, all ye happy miscreants! In my last article, I showed a certain technique for throwing a knife without spin. If you haven't read that article yet, do so now. This article will be useless to you if you have not read my article on proper throwing technique. Anyway, in this article, I will show you a cool trick you can do with my throwing technique.

Facebook makes it easy to show how much you appreciate a funny status, great picture, or cool news article using their iconic "thumbs up" button, but what about those terrible jokes and annoying baby pictures? Where's the "thumbs down" for that crap?

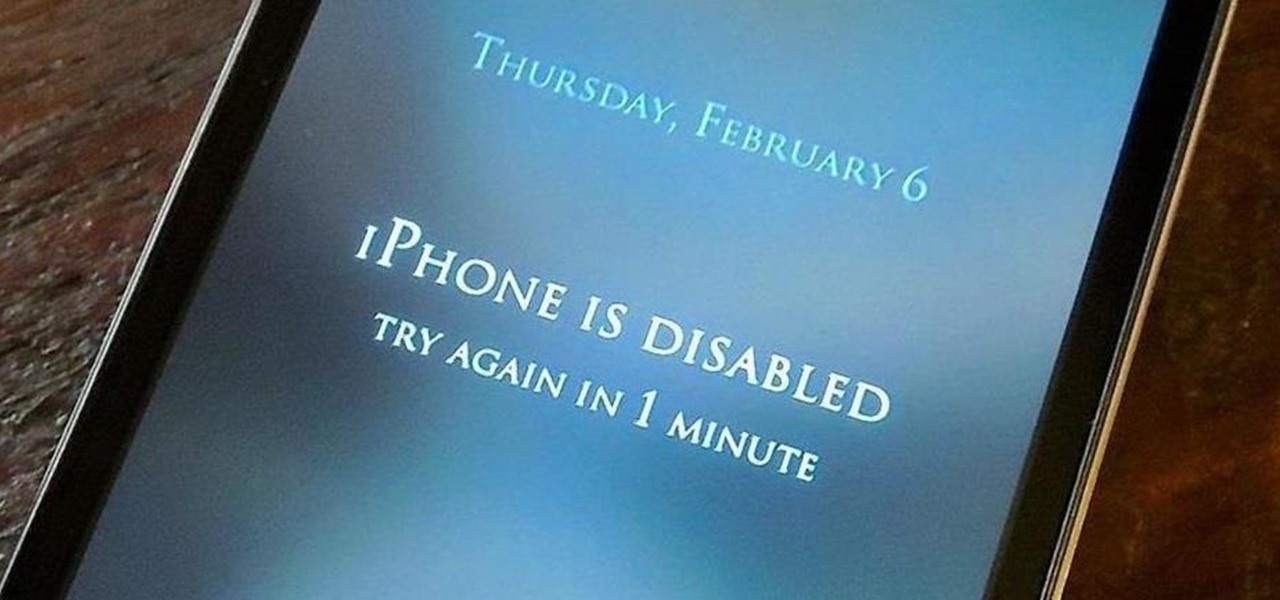
The lockout feature in iOS 7, which securely locks your device after a few incorrect passcode entries, can be a real pain in the ass sometimes.

I have Verizon, America's largest 4G LTE network, as my cell service provider, but there are times when I find myself with a pretty shitty signal, rendering my upload and download speeds substantially slower than usual.

Exclusive to only a handful of smartphones, including the Nexus 5, the Google Experience Launcher allows us to open Google Now simply by speaking out a certain phrase, at any time—dubbed a "hotword."

Ever since its introduction back in iOS 6, AirPlay has been helping us iOS and Mac users stream content over to an Apple TV or third-party speaker system. It's an incredibly useful feature. However, it's also severely limiting. The few compatible products out there are extremely expensive, making wireless streaming a not-so-easy task.

Personally, I think Velveeta is pretty gross. Nothing about its texture, flavor, or color resembles real cheese. But your taste in cheese isn't the important part—what matters is having something good to eat while you watch the game.

Welcome back, my tenderfoot hackers! I recently began a new series on digital forensics to help tenderfoot hackers from being detected and ultimately, incarcerated. In this installment of that series, we will look at recovering deleted files. This is important to hackers because you need to know that even when you delete files on your computer or on the victim's computer, a forensic investigator can usually recover them.

Silence is golden, especially when you're sleeping and about to lock lips with Kate Upton in a dream (or Ryan Gosling, for all you ladies). The last thing you want is your tablet rudely interrupting your passionate kiss with blaring notifications. It's even worse in real-life when you're in an important meeting and you forgot to silence your Android up.