Turn your possessions into cash and become an online selling machine. You will need: Something to sell, a computer with internet access, an eBay account, a digital camera, shipping supplies, something to sell,a computer with internet access, an eBay account, a digital camera, & shipping supplies.
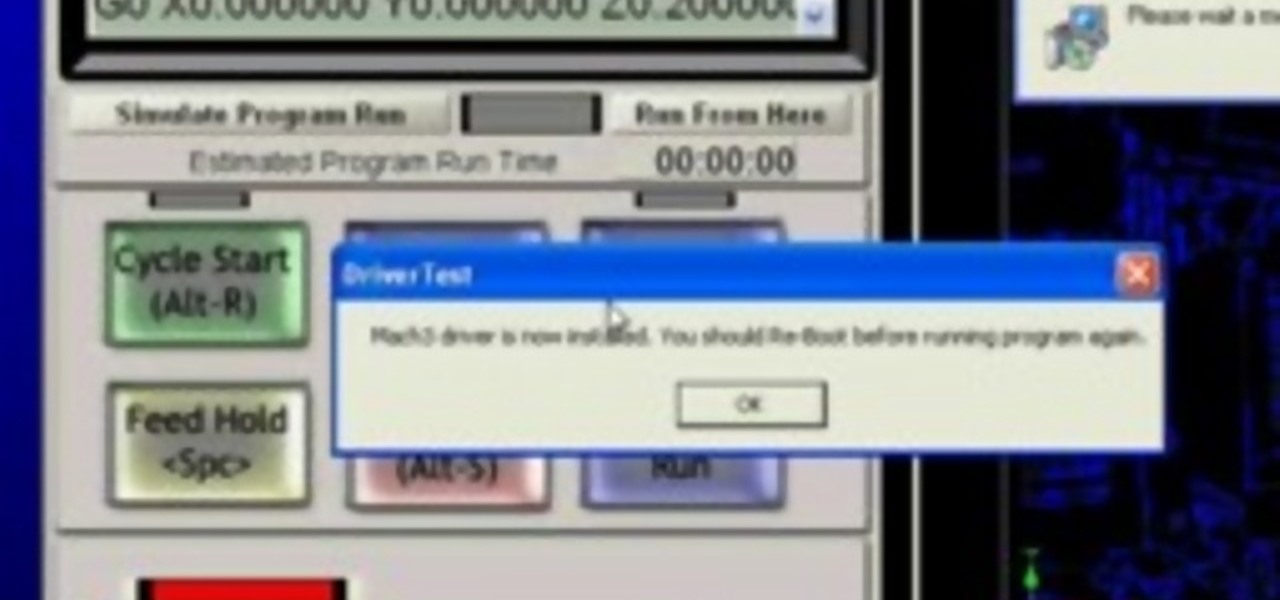
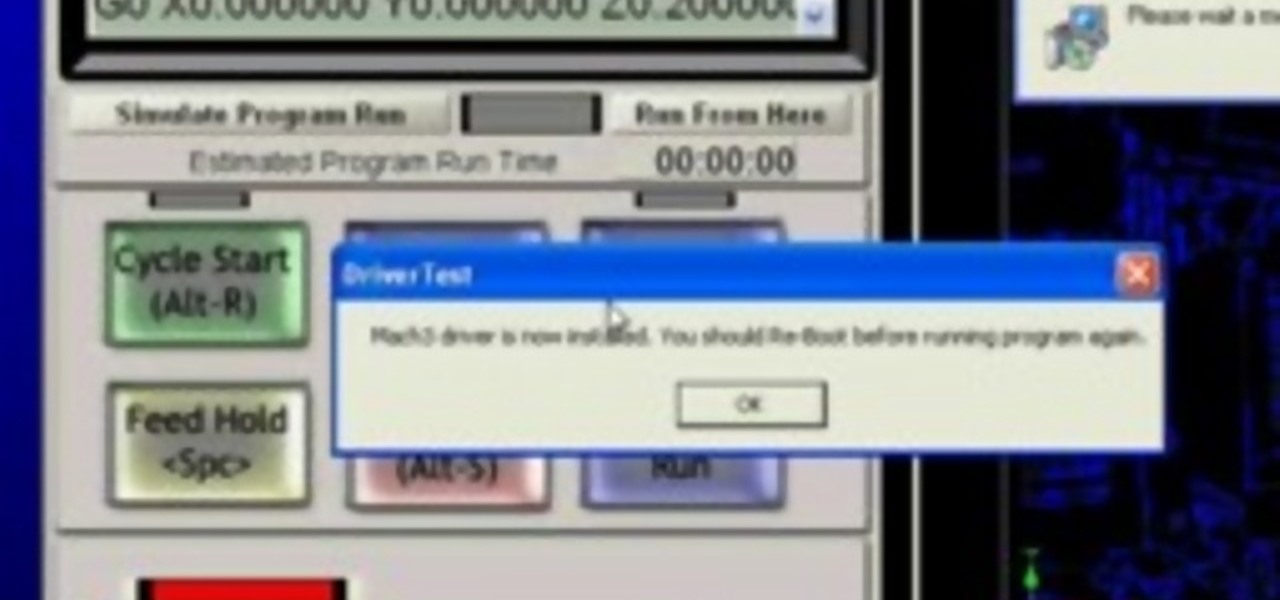
A CNC router machine is probably the most useful tool a hobbyist can own, but the price for a CNC machine on the market is way more than the average hobbyist is willing to spend. You can build your own CNC with very basic tools, little knowledge of machinery, mechanics, or electronics, but be warned, these machines are inherently dangerous, so wear the proper protection and use common sense. At the very least, read the instructions and precautions on every tool you use.
A CNC router machine is probably the most useful tool a hobbyist can own, but the price for a CNC machine on the market is way more than the average hobbyist is willing to spend. You can build your own CNC with very basic tools, little knowledge of machinery, mechanics, or electronics, but be warned, these machines are inherently dangerous, so wear the proper protection and use common sense. At the very least, read the instructions and precautions on every tool you use.

A CNC router machine is probably the most useful tool a hobbyist can own, but the price for a CNC machine on the market is way more than the average hobbyist is willing to spend. You can build your own CNC with very basic tools, little knowledge of machinery, mechanics, or electronics, but be warned, these machines are inherently dangerous, so wear the proper protection and use common sense. At the very least, read the instructions and precautions on every tool you use.

A CNC router machine is probably the most useful tool a hobbyist can own, but the price for a CNC machine on the market is way more than the average hobbyist is willing to spend. You can build your own CNC with very basic tools, little knowledge of machinery, mechanics, or electronics, but be warned, these machines are inherently dangerous, so wear the proper protection and use common sense. At the very least, read the instructions and precautions on every tool you use.

A CNC router machine is probably the most useful tool a hobbyist can own, but the price for a CNC machine on the market is way more than the average hobbyist is willing to spend. You can build your own CNC with very basic tools, little knowledge of machinery, mechanics, or electronics, but be warned, these machines are inherently dangerous, so wear the proper protection and use common sense. At the very least, read the instructions and precautions on every tool you use.

A CNC router machine is probably the most useful tool a hobbyist can own, but the price for a CNC machine on the market is way more than the average hobbyist is willing to spend. You can build your own CNC with very basic tools, little knowledge of machinery, mechanics, or electronics, but be warned, these machines are inherently dangerous, so wear the proper protection and use common sense. At the very least, read the instructions and precautions on every tool you use.

A CNC router machine is probably the most useful tool a hobbyist can own, but the price for a CNC machine on the market is way more than the average hobbyist is willing to spend. You can build your own CNC with very basic tools, little knowledge of machinery, mechanics, or electronics, but be warned, these machines are inherently dangerous, so wear the proper protection and use common sense. At the very least, read the instructions and precautions on every tool you use.

A CNC router machine is probably the most useful tool a hobbyist can own, but the price for a CNC machine on the market is way more than the average hobbyist is willing to spend. You can build your own CNC with very basic tools, little knowledge of machinery, mechanics, or electronics, but be warned, these machines are inherently dangerous, so wear the proper protection and use common sense. At the very least, read the instructions and precautions on every tool you use.

A CNC router machine is probably the most useful tool a hobbyist can own, but the price for a CNC machine on the market is way more than the average hobbyist is willing to spend. You can build your own CNC with very basic tools, little knowledge of machinery, mechanics, or electronics, but be warned, these machines are inherently dangerous, so wear the proper protection and use common sense. At the very least, read the instructions and precautions on every tool you use.

The pavane originated in Europe in the 16th Century. This slow dance was common in Spain, England, France, and Italy. This demonstrational video shows you how to move your feet moving forward. This video is not instructional, although demonstrational, accounting for its modest WonderGrade.

Lower back injuries are common but preventable. Learn simple lower back exercises to increase strength from tips from a personal trainer in this free exercise video series.

In this video, Dominick of askmeDIY.com will demonstrate how to build a wooden pergola, a common fixture of modern gardens. Learn what materials you'll require and receive building tips in this tutorial.

Learn how you can play a common melodic ending passage on the banjo with this tutorial. This is an Earl Scruggs style banjo lick that can be used as a phrase ending lick or break it into fragment and use it in many ways. Watch this how to video and you can play this melodic ending passage on the banjo.

When you design your irrigation system and pick the plants for your garden you need to think about picking plants that have certain characteristics in common. This tutorial gives you tips on how to group similar plants together by light and water requirements.

Are you getting the most out of your sprinkler system? Are there parts of your lawn that always remain dry and brown? Every springtime you should perform an inspection of your sprinkler system. This how to video shows you the steps to appraising you sprinkler system and some remedies for common sprinkler problems. Watch this how to video and you can have a more beautiful lawn this spring.

Worried about your constant bad breath? Bad breath or halitosis is a common and embarrassing problem. This how to video explains why you might have bad breath and how you can get rid of it. Watch this tutorial and you'll have fresh breath in no time.

Sagging screen doors are a common annoyance. This how to video shows you some simple solutions to fixing those sagging doors on the outside of your house.

Watch this how to video to learn how to make a sachet with common safe and natural household items. Use an old t-shirt, or any other old piece of garment, and your favorite sent

Pharmacist Sue Brenan answers common health questions.Watch this video to learn how to tell if you're dehydrated.

The Gorilla Guard trailer coupler lock (part # 63229 from Tow Ready is covered in this video. This is a trailer lock that fits common 1 7/8 couplers. This video shows you the operation of this lock

Here are a few tips on how one may think about overcoming a very common problem: Stagefright! Enjoy!

With InDesign's Dynamic Spelling you can check/correct your spelling as you go. Also with Autocorrect you can correct your common mistyped words automatically as you type them. In this video Terry White will show you how to enable Autocorrect and enter your own Autocorrect words.

This instructable shows you how to easily make a pressurized rocket from some common household materials.

Ever need ice right away but do not have time to run to the store? Here is an easy way to make water turn into ice instantly. Using a few common household products, produce ice from water in the matter of seconds and enjoy a nice tall glass of a chilled beverage.

Kickboxing is a great form of exercise, but to maximize the benefits of any exercise, you must observe proper form. This video demonstrates nine common mistakes in form and nine tips for preventing these mistakes.

It can seem as though there's a virtually endless number of essential programming languages to choose from these days. And complicating matters even further for aspiring or even established programmers, developers, and hackers is the fact that most languages are a bit esoteric and suited for only a certain number of relatively finite tasks.

Brute-forcing is an easy way of discovering weak login credentials and is often one of the first steps when a hacker finds network services running on a network they gain access to. For beginners and experienced hackers alike, it's useful to have access to the right tools to discover, classify, and then launch customized brute-force attacks against a target. BruteDum does it all from a single framework.

One of the first steps in attacking a web application is enumerating hidden directories and files. Doing so can often yield valuable information that makes it easier to execute a precise attack, leaving less room for errors and wasted time. There are many tools available to do this, but not all of them are created equally. Gobuster, a directory scanner written in Go, is definitely worth exploring.

The art of privilege escalation is a skill that any competent hacker should possess. It's an entire field unto itself, and while it's good to know how to perform the techniques involved manually, it's often more efficient to have a script automate the process. LinEnum is one such script that can be incredibly useful for privilege escalation on Linux systems.

NetBIOS is a service that allows for communication over a network and is often used to join a domain and legacy applications. It is an older technology but still used in some environments today. Since it is an unsecured protocol, it can often be a good starting point when attacking a network. Scanning for NetBIOS shares with NBTScan and the Nmap Scripting Engine is a good way to begin.

There are many ways to attack a Wi-Fi network. The type of encryption, manufacturer settings, and the number of clients connected all dictate how easy a target is to attack and what method would work best. Wifite2 is a powerful tool that automates Wi-Fi hacking, allowing you to select targets in range and let the script choose the best strategy for each network.

With the number of web applications out there today, it comes as no surprise that there are just as many vulnerabilities waiting for hackers to discover. Finding those vulnerabilities can be a difficult task, but there are plenty of tools available to make the process easier. While it won't help find any zero-days, web scanners such as Uniscan will detect common vulnerabilities.

Auditing websites and discovering vulnerabilities can be a challenge. With RapidScan and UserLAnd combined, anyone with an unrooted Android phone can start hacking websites with a few simple commands.

Having a dropped call can be incredibly frustrating, especially when you look down and see that your iPhone has full reception. While there's any number of issues that can cause this, one common and often overlooked issue is your iPhone failing to switch cell towers as appropriately needed.

After gaining access to a root account, the next order of business is using that power to do something more significant. If the user passwords on the system can be obtained and cracked, an attacker can use them to pivot to other machines if the login is the same across systems. There are two tried-and-true password cracking tools that can accomplish this: John the Ripper and Hashcat.

Perhaps the best thing about Android is the endless amount of customization you can add to your device. From icon packs to custom launchers and even custom ROMs, there's truly something for everyone. One of the most popular options among Android enthusiasts is adding a system wide dark theme. The methods to do this vary, but you can now automate this process thanks to Android Oreo.

The key to becoming a competent white hat is knowing how the technology that you are trying to exploit actually works. SQL injection is one of the most common methods of attack used today and also one of the easiest to learn. In order to understand how this attack works, you need to have a solid grasp of ... you've guessed it ... SQL.

In a LinkedIn post published on Tuesday, Microsoft's leading advocate for the HoloLens made a prediction that the mixing of immersive technologies will define augmented reality in 2018.

Many people think antivirus apps are useless — why pay a subscription fee when most malware can be avoided with common sense? But the thing is, there were an estimated 3.5 million malicious Android apps discovered last year, with many of them making their way onto the Play Store. As this number continues to rise, can you truly depend on common sense to protect you?