Ever wanted to communicate with another driver on the road, but just didn't know how? Sure, you could flag them down by waving or honking at them, but that assumes that they're in close proximity, that you have a unobscured path, and that they're paying attention. And if you're in a fit of road rage, flagging them down probably isn't the best idea for either of you.

Thanks to Apple's implementation of Continuity on Mac OS X Yosemite and iOS 8, communication is truly a seamless thing. Without even looking at my iPhone, I can message or call friends comfortably from my computer or iPad.

While text messaging has become one of the most frequent ways we communicate with our friends, the missing body language, tone of voice, and eye contact can make it difficult to tell when someone is being dishonest. That said, it's not impossible. There are a number of subtle hints you can train yourself to recognize that will to help you detect written lies hiding in your SMS and iMessages. Here's what you should look out for.

Sprint and T-Mobile have agreed to a $31.6 billion deal that, if it gets through federal regulators—which is far from a sure bet—would create a formidable carrier to really compete against AT&T and Verizon. The deal comes packaged with a $1 billion "breakup" fee that Sprint would have to pay T-Mobile in the event the deal does not go through. After the deal, Deutsche Telekom, which owns about 67% of T-Mobile, would maintain a 20% ownership stake.
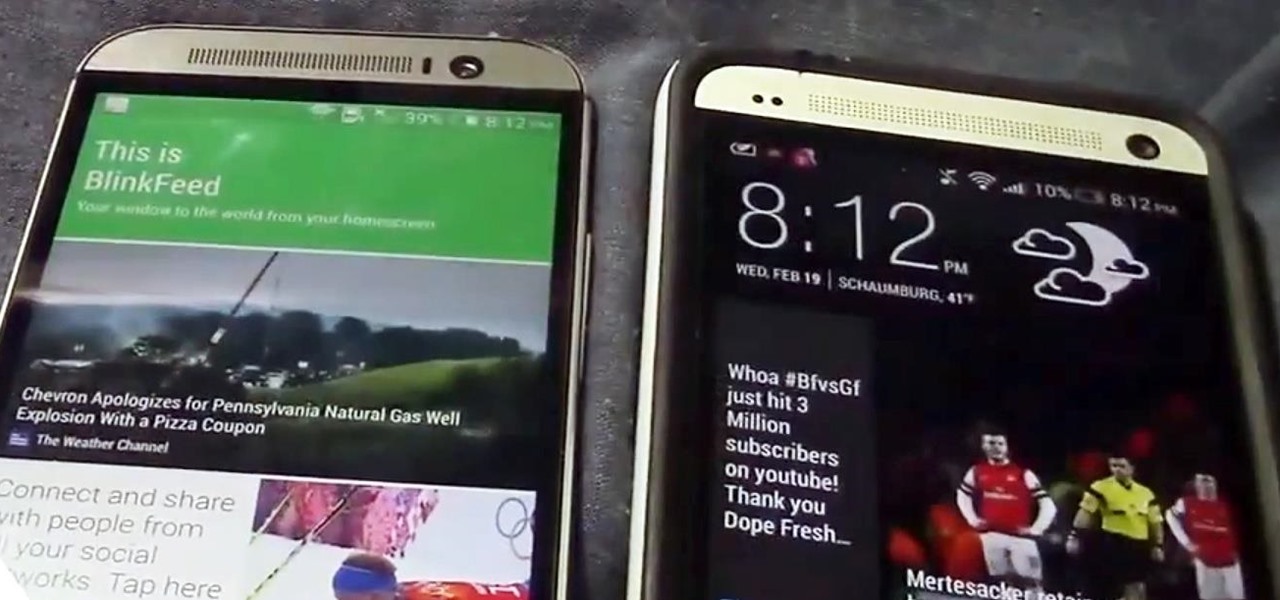
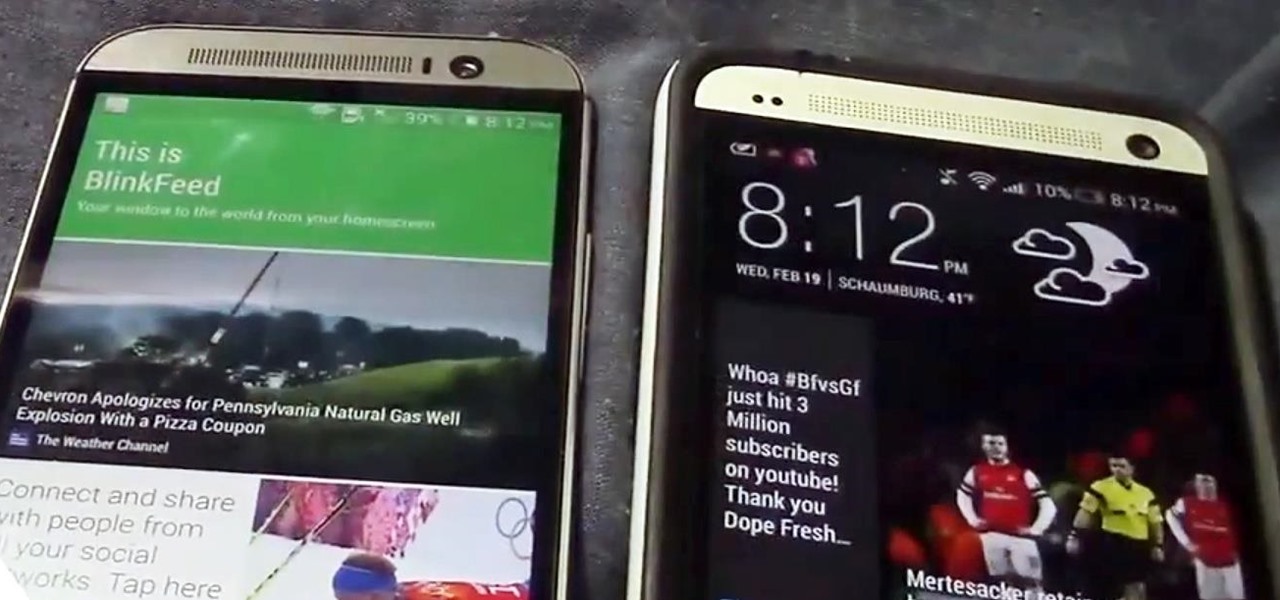
Confirming a lot of what we already knew, now we have a physical walkthrough video on HTC's new flagship, the M8. Or, maybe the "New HTC One", but let's hope that's not the name of the final product. Before we get to the video, here's what we already know:
Last week, Apple issued an iOS 7.0.6 update that fixed a serious security vulnerability that could allow hackers to steal passwords, read emails, and get info from other SSL-encrypted communications.

In the wake of the NSA controversy and its subsequent fallout, many dashed towards finding means of secure communication—using private internet browsing and encrypted text messaging applications—out of fear of being spied on.

Instagram recently released their new Instagram Direct messaging feature in their Android and iOS apps, which lets users share private photos and videos directly with individuals or groups of up to 15 users. However, there are no restrictions on who you can send private photos or videos to.

As the protectors of all things good, the Federal Communications Commission is usually busy behind the scenes pissing off Slim Shady, giving out fines for indecent nipple exposure at certain halftime events, and warning the NSA about losing any "confidential" phone information they steal from us.

Communication is the key to any healthy relationship, and when I say any, I mean human and non-human. Previously, one of the biggest culprits for not understanding what you meant was Siri, but now it looks like it has some competition with the new Kinect system, which can control practically everything on your Xbox One—if it can understand you.

Welcome back my precious hackerians. Today i would like to promote an OS which i have been using for the past couple months. I'm not talking about Backtrack 5 or Kali Linux. Something even more promising:

While the pope himself may not be Steampunk, you might be amazed at what is: the coronation stove. For those who don't know, it's been a tradition for a very long time to signal the election of a new pope (or the lack of a new pope) via colored smoke. More specifically, once the cardinals have all voted for the new pope during the conclave, the ballots are burned in a special stove in the Sistine Chapel, and the smoke is visible in St. Peter's square.

Do you guys remember those things you hold with your fingers to write stuff down? I think they're called pens, or something like that...

Social media is where we post our thoughts for the world to see, but sometimes a little more exclusivity is needed. And that's where Scrambls comes in.

Considering how often many of us fly on commercial airlines, the idea that a hacker could somehow interfere with the plane is a very scary thought. It doesn't help to learn that at Defcon, a researcher found that the Automatic Dependent Surveillance Broadcast (ADS-B), transmissions that planes use to communicate with airport towers are both unencrypted and unauthenticated.

Custom ring and text tones are great for knowing who's attempting to contact you without having to actually look at your iPhone. However, this feature is useless when your device is in silent/vibrate-only mode.

Not a social butterfly? You can go out into the world while ignoring a particular person or just not get caught up in a conversation with anyone at all. With the use of some distracting devices and a little acting you can be on your way.

Writing agendas are necessary to keep meetings organized and on schedule. Get tips on writing an agenda from a communications and public speaking expert in this free instructional video series.

This MS Office software tutorial shows you how to use some tips and tricks for the coolest features of Microsoft One Note. OneNote 2007 is great for notetaking during meetings or as a project communication tool at the office. Whatever you may need to keep track of, the tips and tricks in this OneNote tutorial will help you get started.

Who doesn't want to be able to speak like a New Yorker? Whether for acting, comedy or impressing your friends and family, speaking in a New York dialect will provide you with hours of entertainment. Learn how to speak in a New York dialect in this free video series from communications and public speaking expert, Tracy Goodwin.

Learn a little bit about technology with help from EMBARQ. Watch this how-to video tutorial on installing your 2Wire Gateway for EMBARQ High-Speed Internet. This will cover exactly how to install your EMBARQ 2Wire Gateway modem for Internet. This is the complete process step-by-step from box to connected online.

Learn a little bit about technology with help from EMBARQ. Watch this how-to video tutorial on installing your EMBARQ 660 Modem. This will cover exactly how to install your EMBARQ Modem for EMBARQ High Speed Internet service. This is the complete process step-by-step from box to connected online.

Learn a little bit about technology with help from EMBARQ. Watch this how-to video tutorial on testing your phone line (NID) if you have no dial tone. If there is no dial tone on your home lines, just test your NID (Network Interface Device) on your house to see what's going on. This is an important step to getting your High-Speed Internet up and running.

A field hockey defense must control the opposing team's offense. Communication and positioning are paramount when building an effective field hockey defense. Learn how to play field hockey defense in this video tutorial.

Teaching a child to go underwater may be easier than it sounds. Children have a natural reflex to go underwater but can lose it. Learn how to teach a child to go underwater in this swimming video tutorial.

Improving interpersonal perception builds communication skills and can provide relationship help. Part 1 of 6 - How to Improve interpersonal perception.

Giving a welcome speech is a good way to make someone feel comfortable in a new company. Learn how to give a great welcome speech from a communications expert in this free instructional video series.

Balboa is a form of swing dance is danced in close embrace, and is led with a full body connection. The Balboa is the subtle communication between the leader and follower and because of that the Balboa is considered more of a "dancer's dance" than a "spectator's dance".

Balboa is a form of swing dance is danced in close embrace, and is led with a full body connection. The Balboa is the subtle communication between the leader and follower and because of that the Balboa is considered more of a "dancer's dance" than a "spectator's dance".

A year and change into its shift towards enterprise customers, Magic Leap has updated Lumin OS and the corresponding Lumin SDK with some key prerequisites for the business sector.

The COVID-19 pandemic forced many businesses into remote work models, whether they were ready or not, making Zoom a household (or home office) name for its video conferencing service.

The past year has revealed a gaping hole of opportunity in the world of business called virtual meetings. Some existing players like Zoom hopped on that opportunity, while others like Skype seemed stuck on the sidelines, and Google Meet just managed to catch up in time to snag some of the shift in remote work.

We are now in the age of 5G. Carriers worldwide are upgrading their networks to the newest standard for mobile, which will dramatically improve your phone experience. How? By giving it download speeds and latency that surpass Wi-Fi. But before you upgrade, there are few things you should know first.

In the last decade, the number of people working remotely in the US has increased dramatically, and so has their need for technology and software to supplement that remote work. Whether you work from home or a coworking office space, the requirement for highly compatible and helpful productivity apps is a must if you want to get things done successfully.

You may have recently seen a plethora of Instagram users, including celebrities and politicians, sharing a screenshot declaring that the platform will implement a new "rule" where it would own and could use your photos and videos however it wishes. The screenshots are part of an internet hoax, one that's been around in one way or another since 2012, but what can Instagram actually do with your media?

Threats to your privacy and security are everywhere, so protecting your data should be the highest priority for anyone with a smartphone. However, one threat many people overlook is the company who supplies the operating system your Android phone runs — Google.

It has been a long while since I last came here to write an article. Graduate school keeps you busy. After I looked over what I had written previously, I decided that I should introduce another fun topic from cryptography. In this case, steganography.

Welcome back, my hacker trainees! A score of my readers have been begging for tutorials on how to hack Wi-Fi, so with this article, I'm initiating a new series dedicated to Wi-Fi hacks. This will probably be around 6-9 articles, starting with the basics of the technologies. I can hear you all groan, but you need to know the basics before you get into more advanced hacking. Then hopefully, developing your own hacks.

In this article, I'll be explaining the basics of how microcontrollers work, physically and virtually. First off, microcontrollers are no simple thing, so don't be discouraged if you find it mind-boggling! The world of microcontrollers is fascinating, engaging, and an awesome hobby; it never gets boring. I'll be focusing more on I/O and analog based microcontrollers, such as those running Arduino, and using Atmel chips as examples (these are most commonly available, and easy to program).

Good communication is essential when managing teams and overseeing complex projects. Whether you're developing the latest and greatest app or trying to get ahead of a large data science project, effective communicators are always in high demand.