For some users, a search bar can be a really annoying thing. With Internet Explorer 7 and on, most people are interested in getting rid of the search bar. So in this tutorial, find out how to remove the search bar in Internet Explorer 8 using some simple steps. Enjoy and good luck.
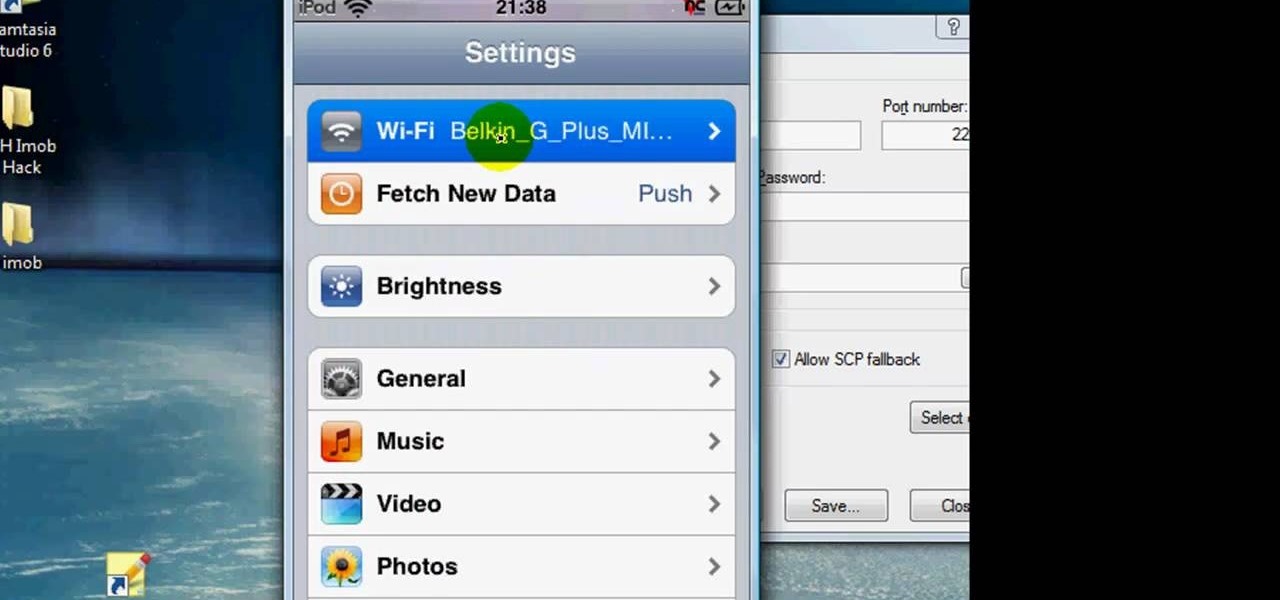
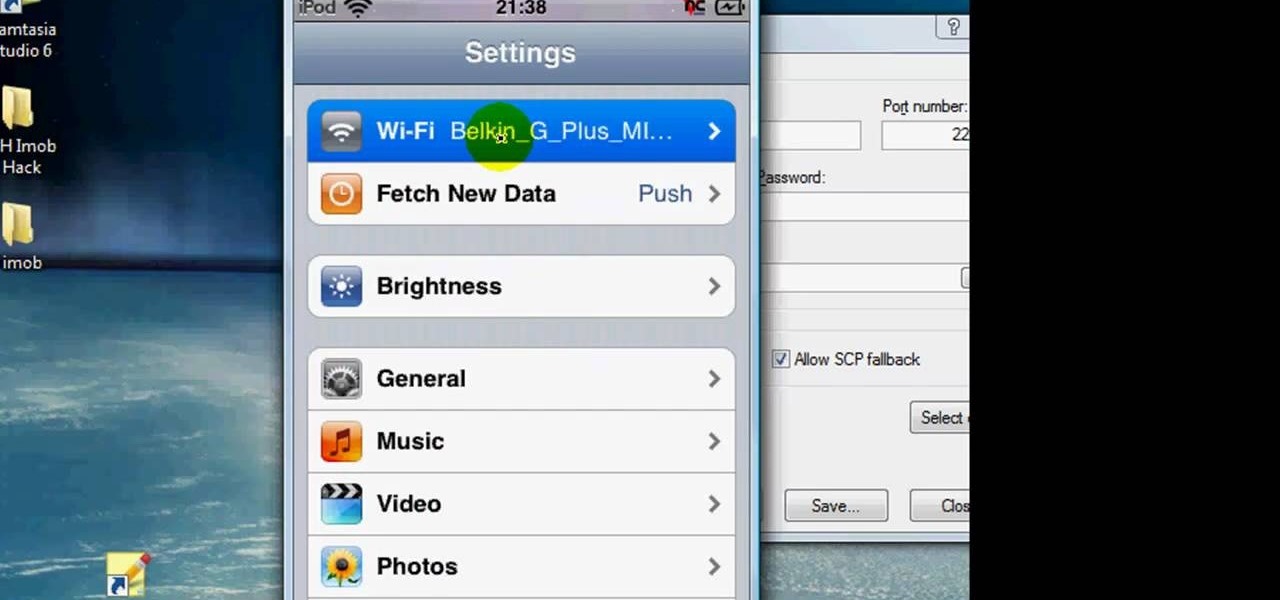
You can SSH on a iPod which is jail broken. To do this you will need the Cydia application. Open the application on your device. From the main menu of the application go to the search feature. Search for SSH. The first result is Automatic SSH. Click on it to download. Install the application. Go back to search and scroll down to find the OpenSSH program. Download and install it. Now from your desktop open your internet browser and search for WinSCP in Google. From the first result download th...

To do this, you must be using Safari; make sure you are not using Firefox or another program. This can be very useful for quickly finding information on web pages. Press Command F. This will open up a toolbar on the top of the page which will ask you what you are searching for. Type the word you are searching for into the toolbar. The word will be highlighted on the web page; you can then click the next arrows to find the section of the page you are looking for. This can be used to find speci...
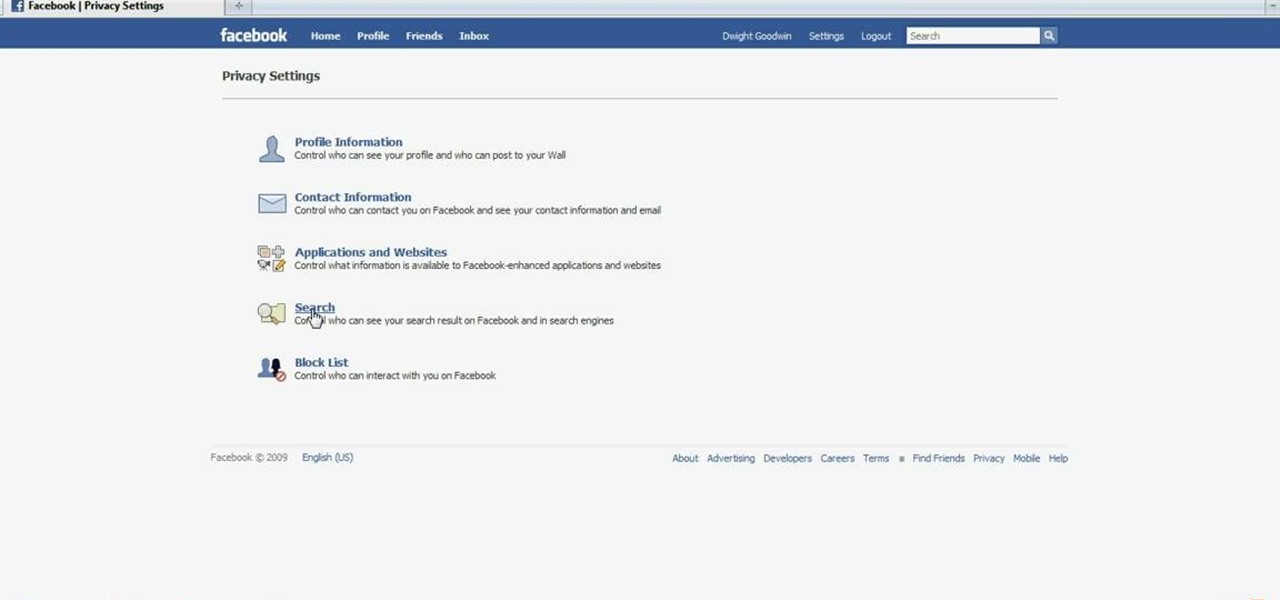
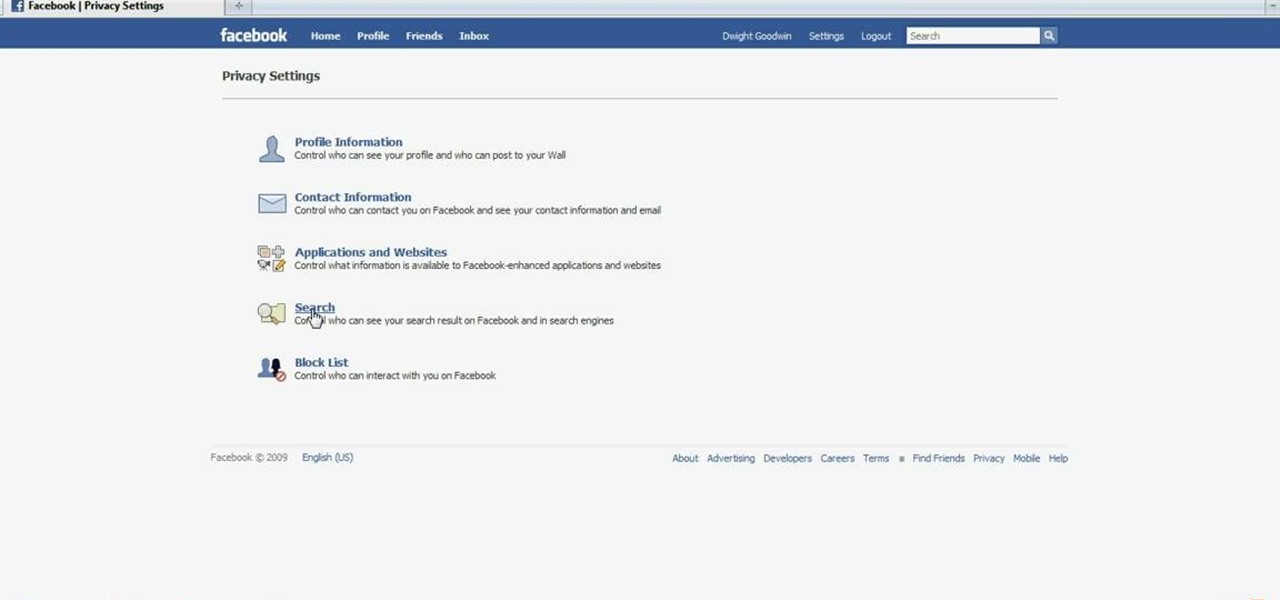
ClassroomNext demonstrates how to change your Facebook privacy settings. To adjust your Facebook privacy settings, first log on to Facebook and open up your profile page. If you would like to change your privacy settings so that your pictures are not indexed by search engines like Google and Yahoo, click on the settings options which is located in the toolbar at the top right of the Facebook page. Select the privacy settings option from the drop down menu. Next, click on the search option. Ma...

In this video from NescoResource we learn how to answer the question in an interview of "Where do you see yourself in 5 years?" This question provides you an opportunity to show your commitment to that job and to demonstrate your knowledge of the company's and the role you could have in achieving that vision. To provide a thoughtful response, you need to do the homework on the company. Do not answer by saying you see yourself in the interviewer's job. This could really backfire on you because...

The first thing that comes to mind when your car is stolen is: ####!! However, once calm, cover these bases when your car is stolen to notify relevant parties and help ensure vehicle recovery or replacement.

If you're buried in e-mail (and who isn't?), Instant Search in Microsoft Office Outlook 2007 can save the day for you. The new Instant Search helps you quickly find e-mail messages, appointments, contacts, or any Outlook item. You don't even need to know which folder the item is in. Watch the demo to see how to use this fast search feature in Outlook 2007, and start finding what you want instantly.

With iOS 14, Apple finally lets us change the default browser on our iPhones. No longer do we need to settle for Safari if we'd prefer another option like Chrome or Firefox. However, we encourage you to consider switching your browser or your search engine — or both — to Ecosia. Here's why.

There's a lot of résumé writing happening right now. While it's a confusing and frustrating time, you don't have to wait to search for new opportunities. Maintaining a clear head and being proactive in your next career steps are two qualities that are necessary at this moment.

The still-unfolding story of China's Nreal augmented reality startup continues to develop, with each turn uncovering another unexpected wrinkle.

Amid the coronavirus chaos, two companies at the forefront of augmented reality technology took starkly different approaches to their upcoming developers conferences, as Facebook has canceled its annual F8 conference and Magic Leap plans to invite a limited number of attendees to its Florida headquarters for LEAP Developer Days.

Whenever a new Apple event invite arrives, the entire tech industry begins tearing the invite's graphics apart in a bid to decipher what the company may be planning on releasing in the coming weeks.

The end of year surprises keep on flowing from the Plantation, Florida offices of Magic Leap. This time, it's yet another game from the company's old partner Insomniac Games, and it's called Strangelets.

You may not have thought of dorks as powerful, but with the right dorks, you can hack devices just by Googling the password to log in. Because Google is fantastic at indexing everything connected to the internet, it's possible to find files that are exposed accidentally and contain critical information for anyone to see.

Open-source intelligence researchers and hackers alike love social media for reconnaissance. Websites like Twitter offer vast, searchable databases updated in real time by millions of users, but it can be incredibly time-consuming to sift through manually. Thankfully, tools like Twint can crawl through years of Twitter data to dig up any information with a single terminal command.

While the long awaited HoloLens sequel is scheduled to arrive later this year, Apple may force Microsoft to share the AR wearables spotlight, if reports of the company's first entry into smartglasses territory end up coming to fruition.

Augmented reality startup Nreal was a hit at this month's CES event, with some even calling the device a worthy challenger to the Magic Leap One.

Mobile augmented reality pioneer Blippar has now completed its fall from hopeful AR startup to the immersive computing history books.

Snapchat continues to deepen its roster of clients adopting its Shoppable AR Lens, with clothing giant Levi's and Disney becoming the latest brands to try on the e-commerce platform for size.

Automotive augmented reality company WayRay has set its destination for a $1 billion valuation with an estimated time of arrival of 2019, and it has just passed a major milestone towards that goal.

With the official launch of Magic Leap One expected by the end of summer (translation: days from now), Magic Leap's hype machine just took a big hit with the sudden loss of a key marketing executive.

Hackers rely on good data to be able to pull off an attack, and reconnaissance is the stage of the hack in which they must learn as much as they can to devise a plan of action. Technical details are a critical component of this picture, and with OSINT tools like Maltego, a single domain name is everything you need to fingerprint the tech details of an organization from IP address to AS number.

The easiest way around a security policy is to find users who don't follow it. The Have I Been Pwned database identifies accounts with information breached by major third parties like Yahoo and LinkedIn. With Maltego, hackers can locate breached accounts created using company email addresses, potentially giving attackers access to a company account if the employee reuses a compromised password.

If you're a fan of Gboard, Google's third-party keyboard for iOS, then you can already search Google, YouTube, and Google Maps from any screen you're on. But if you prefer Apple's stock keyboard or another third-party one on your iPhone, you don't have any Google search options ... at least, until now.

Update: Monday, 11 p.m. ET: In a report from Bloomberg, eMagin CEO Jeffrey Lucas has contradicted what appeared to be investor information found in SEC filings that surfaced on Monday. Although Apple is listed among several other investors in the company in filing, Lucas told Bloomberg that Apple is not, in fact, an investor in the company. Offering further clarification, Lucas told the news site that eMagin "listed those companies in the filing because it had discussions with them at industr...

Buyers can't wait for their Tesla Model 3 to be delivered. But with no clear arrival date in sight, buyers are starting to get a little antsy waiting to see what the Tesla Model 3 will look like up close. Luckily, Tesla accessories seller EVANNEX partnered with technology firm Kinetic Vision to try and satisfy buyers for a while by creating an app that lets you view an augmented reality Tesla Model 3 that's nearly life sized.

Nike's newest app is changing the way we shop. Called SNKRS, it uses augmented reality to sell the limited edition Nike SB Dunk High Pro "Momofuku" sneakers.

Theorem Solutions, a company that helps engineering and manufacturing companies reduce their costs, has taken the next step with their mixed reality technology. The company has now added their own app, called Visualization Experience, to the Windows Store for the Microsoft HoloLens

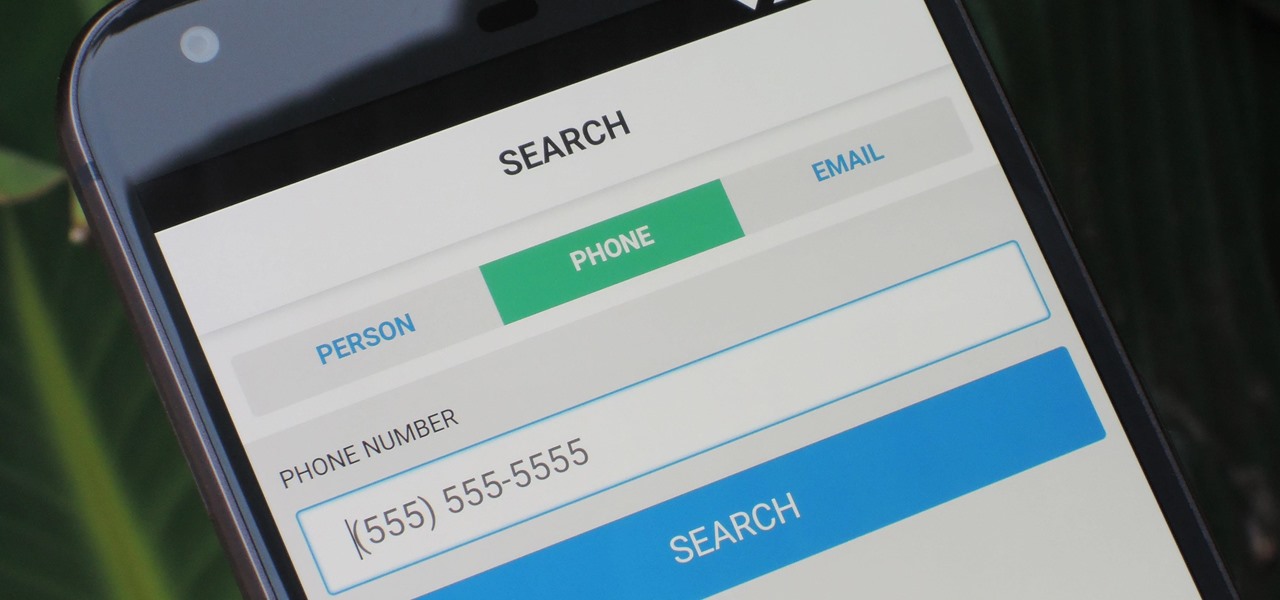
As much as you try to safeguard your personal information, you may have made a small mistake by giving your phone number to the wrong entity, and now you're being bombarded with dozens of spam calls every day. To help parse your call log and reject the proper numbers without answering or trudging through voicemail, a good reverse phone lookup app is needed.

Considering that Google makes Android, it's rather strange that the operating system doesn't have a baked-in solution for doing a reverse image search. Sure, you can long-press pictures in Chrome to search for other instances of a photo, but it's not possible with pictures you find in other apps, or photos you've downloaded to your phone.

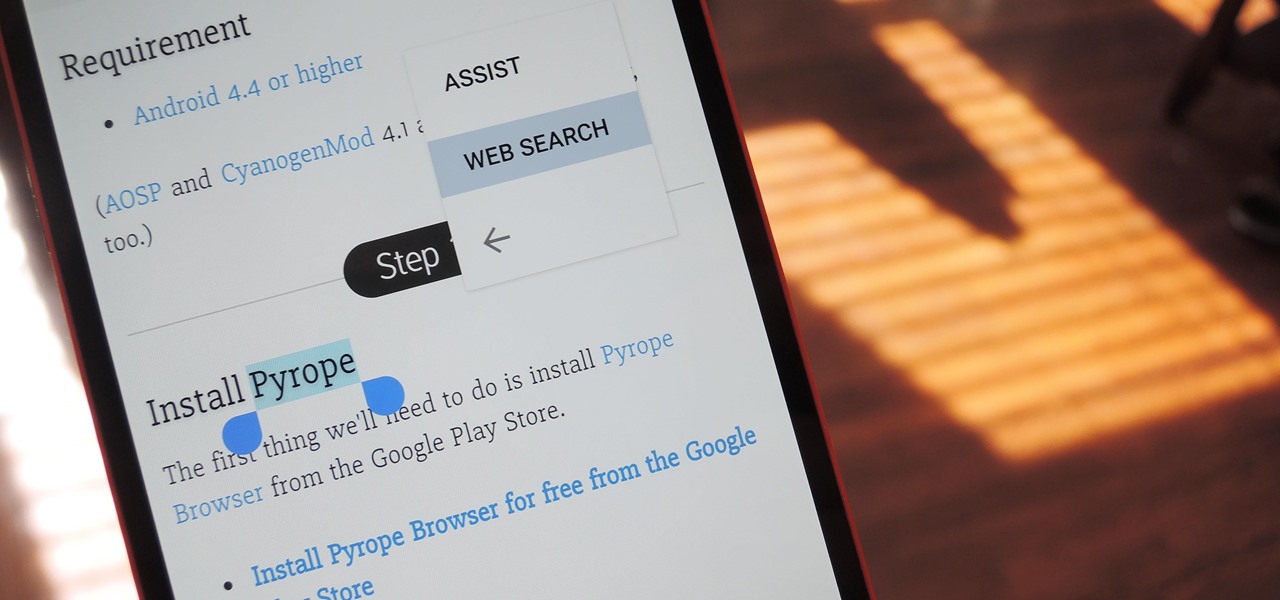
Chrome's text selection interface is pretty nice, but it could definitely use some improvements. For instance, when you're in Incognito Mode, you can't perform a web search for words you've highlighted. And when you're typing out a forum post or using any text input field, for that matter, there's no option to search or share any of the text you've written.

Welcome back, my greenhorn hackers! Throughout this series on Metasploit, and in most of my hacking tutorials here on Null Byte that use Metasploit (there are many; type "metasploit" into the search bar and you will find dozens), I have focused primarily on just two types of modules: exploits and payloads. Remember, Metasploit has six types of modules:
Hello I have now asked for help a few times, so I figured I should contribute with what I can offer as of right now, which is many valuable sites if you need to look someone up.

Apple certainly took a page from Google Now with its new "Proactive" search page in iOS 9. Located to the left of the home screen, the page provides quick access to contacts you've recently corresponded with, suggested applications, nearby places, and news articles based off of your Safari activity.

Spotlight, Apple's selection-based search system, received a major facelift on Mac OS X Yosemite. Packed with dozens of new features, such as a central search window and increased app suggestions, the reworked Spotlight was a breath of fresh air.

This video will show you handy tips and tricks about Google search engine. These tips will help you to speed up your computing or browsing experience. This video contains tricks like Search by location, Filter image search, how to see sites that aren't online, movies running in a city theaters etc. This video is the 2nd part of the serial. You could also watch the part 1 here vimeo.com/104089915.

This video will guide you 5 useful tricks and tips for Google search engine. These tips include search operators, search in a single site, get definition, calculation and currency conversion, fast essential information etc. So please watch the video and follow all the steps to employ in your machine.

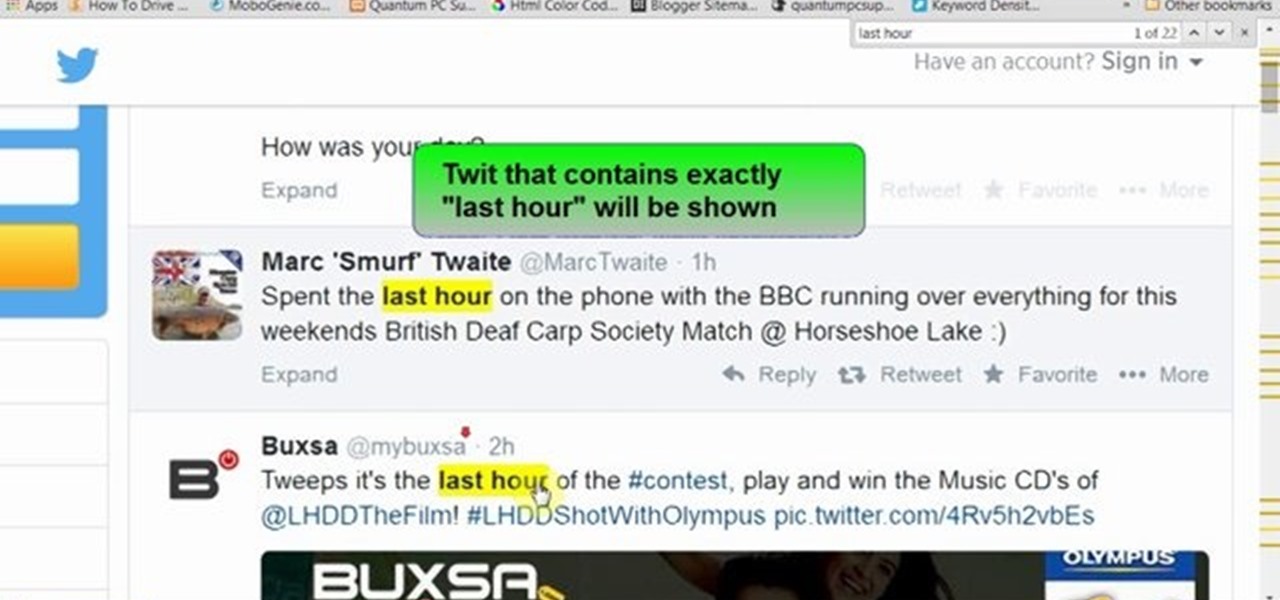
This video will show you how to search Twitter by parameters without sign up or log in. Here a person can use search parameters to find the desire twits. So there is no headache for signing up or logged in for searching. So please Watch the video and follow all the steps to do it yourself.

This video will show you how to search on twitter using parameters without Signup. You don't need to be sign up for twitter search. Anyone could use this twitter search feature and utilize parameter. Watch the video and follow all the steps carefully.

Welcome back, my tenderfoot hackers! I have written many tutorials on hacking using Metasploit, including leaving no evidence behind and exploring the inner architecture. Also, there are my Metasploit cheat sheets for commands and hacking scripts.