The way you use your camera just got a bit more interesting. Phogy, a brand new camera app for Android, allows you to capture pictures with a 3D effect that comes alive when shifting your phone from side to side.

Sometimes, ceiling fans just don't cut it. They spin meekly, barely generating any air flow to cool down your sweltering room. Or, when turned up high, they can wobble wildly, shaking and vibrating as if the ceiling is about to come crashing down. If this sounds like your ceiling fan, chances are the solution is a simple as flipping a switch.

This video will show how to target your facebook post for a specific audience. With this tutorial video you could target a set of audience who has interest about the post.

Your new HTC One M8 has a ton of really cool features, some of which relate to waking the device up. A swipe up to unlock to your last active screen, a swipe down to access the voice dialer, and a double-tap (or knock) to wake the device and bypass the lock screen.

The "Knock Knock" features on LG's G2 phone have proven popular and useful enough to spawn various apps and mods cloning these abilities for other devices. Porting the "Knock On" feature to our Samsung Galaxy S3 isn't as easily doable, since developers would need to create a modded kernel, like they did for the HTC One. The "Knock Off" function, on the other hand, is a lot more manageable.

Now that Hangouts is Android's default messaging app, it's given us a lot of cool new features. A bouncing ellipsis lets you see when the other party is typing, and an indicator shows you whether they've read your message or not. You can even answer the age-old question of "Where you at?" with a tap of a button, sending a map of your location.

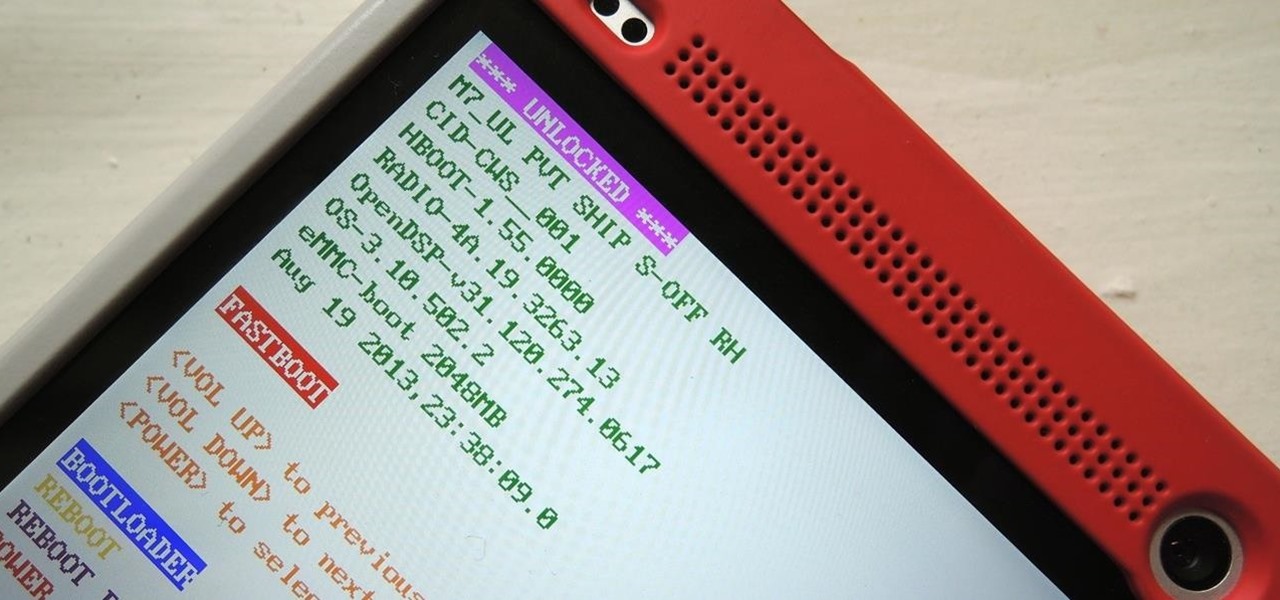
You've unlocked your bootloader and rooted your HTC One running KitKat, but there's still one lingering aspect of security you've yet to rid yourself of—S-On—the extra security measure HTC implemented into Sense.

The more you use your device, the more you'll download and install apps. These apps range from helpful to fun to simple distractions, but after a while, you may notice slow down on your device or a marked reduction in battery life.

Welcome back, my hacker apprentices! Several of you have written asking me how you can check on whether your boyfriend, girlfriend, or spouse is cheating on you, so I dedicate this tutorial to all of you with doubts about the fidelity of your spouse, girlfriend, or boyfriend.

Unless you're using something like 360 Vault to store photos and videos, people you lend your iPhone to can easily browse through the gallery without you knowing. It makes me anxious just thinking about it.

I can be pretty forgetful. If there's something important to remember, I need to jot it down right away or risk losing it forever.

Welcome back, my greenhorn hackers! After the disaster that was Windows Vista and the limited and reluctant adoption of Windows 8 and 8.1, Windows 7 has become the de facto standard operating system on the desktop/client.

My friends can be pretty shitty sometimes, but they're my friends nonetheless. On various occasions, they've secretly taken my device and made me look foolish by posting crude and embarrassing posts to Facebook, Instagram, or Twitter. With friends like these, who needs enemies, right? And it's because of these types of friends that we need to substantially upgrade the app security on our devices.

Having quick and immediate access to your notifications is one of the most important features for any modern day phone, but these alerts can be easily missed when your device isn't in the palm of your hand.

For my money, one of the greatest improvements brought about from the smartphone revolution is the advent of visual voicemail. No longer do we have to slog through dial menus or trudge through every single message to get to the next. We can just look at our messages, right there on our screens, organized neatly like emails or text messages.

Silence is golden, especially when you're sleeping and about to lock lips with Kate Upton in a dream (or Ryan Gosling, for all you ladies). The last thing you want is your tablet rudely interrupting your passionate kiss with blaring notifications. It's even worse in real-life when you're in an important meeting and you forgot to silence your Android up.

There are a gazillion lock screen apps available on Google Play, but the majority of them are subpar and not worth your time. However, in my opinion, there is definitely one out there worth your time—one that constantly learns and adapts to what apps you use when and where to determine which shortcuts to give you.

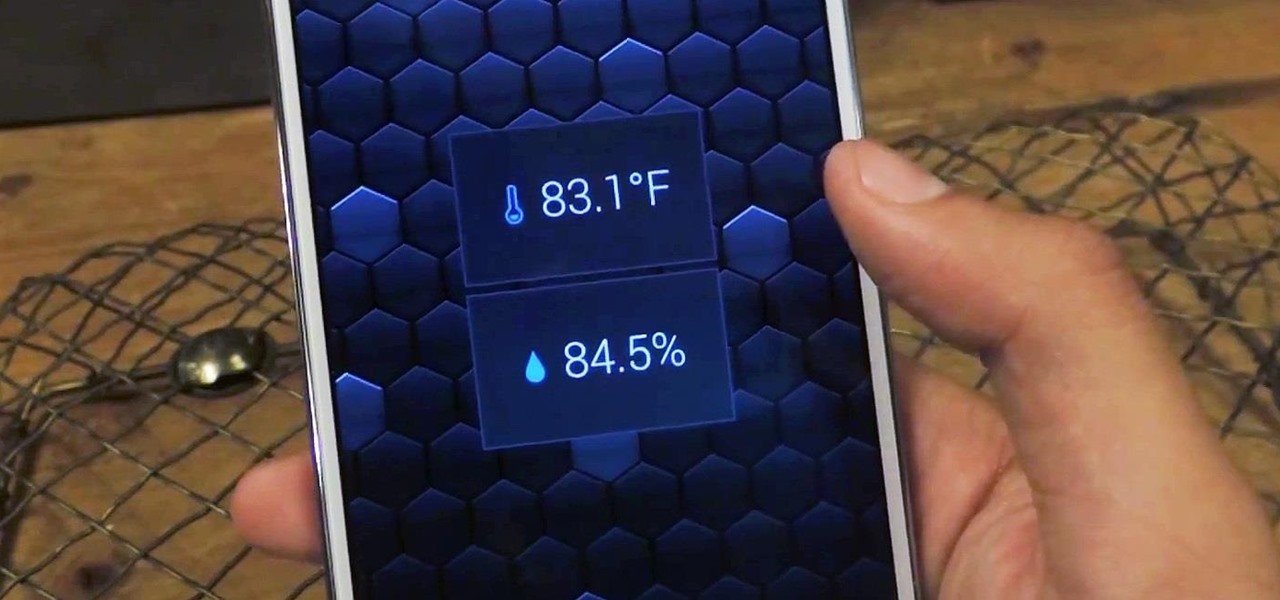
The majority of Android devices have built-in sensors underneath the hood that measure motion, position, and several environmental parameters that provide data needed to monitor your movements and adjust accordingly.

Initially introduced as an Easter egg deep within Android's operating system, the Daydream screensaver feature turned official in the release of 4.2.2 Jelly Bean. Now, it's been out for a few months, which means developers have already figured out how to take advantage of it in their own ways.

Automation is everywhere in our daily lives. Faucets and hand dryers that turn on for you when they detect your presence. Automated teller machines to handle your bank account. Timed sprinklers to water your lawn every morning. DVRs to record your favorite TV shows when you're not home.

Like the buttons on your computer's mouse and keyboard, the Home key on your Samsung Galaxy S4 serves a vital function in navigating through your device. It can get pressed dozens of times a day, going through hours of use and abuse.

Phone interruptions are commonplace, as is evident by my historically epic missed phone call list, ranging from annoying sales people to my mom checking in every five minutes to see if I'm still alive.

Welcome back, my fledgling hackers! It's been awhile since we did a Metasploit tutorial, and several of you have pleaded with me for more. I couldn't be happier to oblige, as it's my favorite tool. For the next several weeks, I'll intersperse some new guides that'll help expand your Metasploit skills and keep you abreast of new developments in Metasploit, so look for them in the near future.

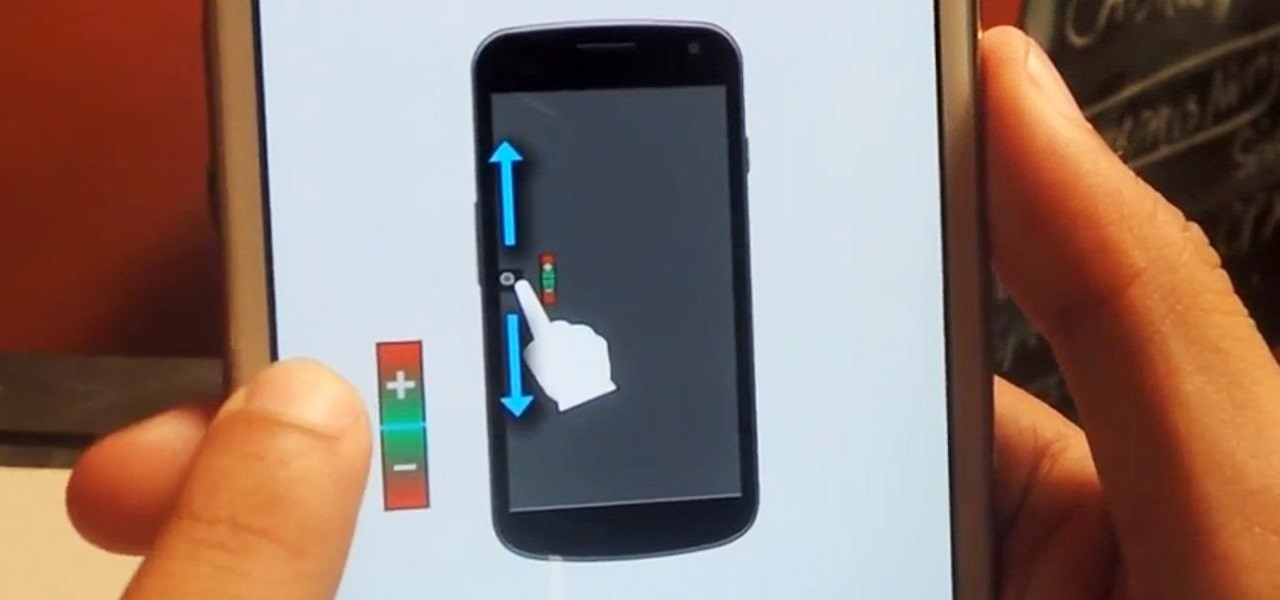
One of the more challenging things about using the Samsung Galaxy Note 3 is the ability to use it with one hand, due to its enormously large (but wonderful) screen size.

While Siri came up on the scene with hardly any competition back in 2011, Google Now has not only caught up to Apple's intelligent personal assistant, but also excelled in certain areas—with its ability to quickly answer questions, give recommendation, and even deliver information that it predicts a user will want.

The Nexus 7 is a huge jump in screen size when coming from a phone, but obviously this tablet is still smaller than some of the major players such as the Nexus 10, Galaxy Tab, etc. One way to squeeze out a little more space is to eliminate the navigation and status bars.

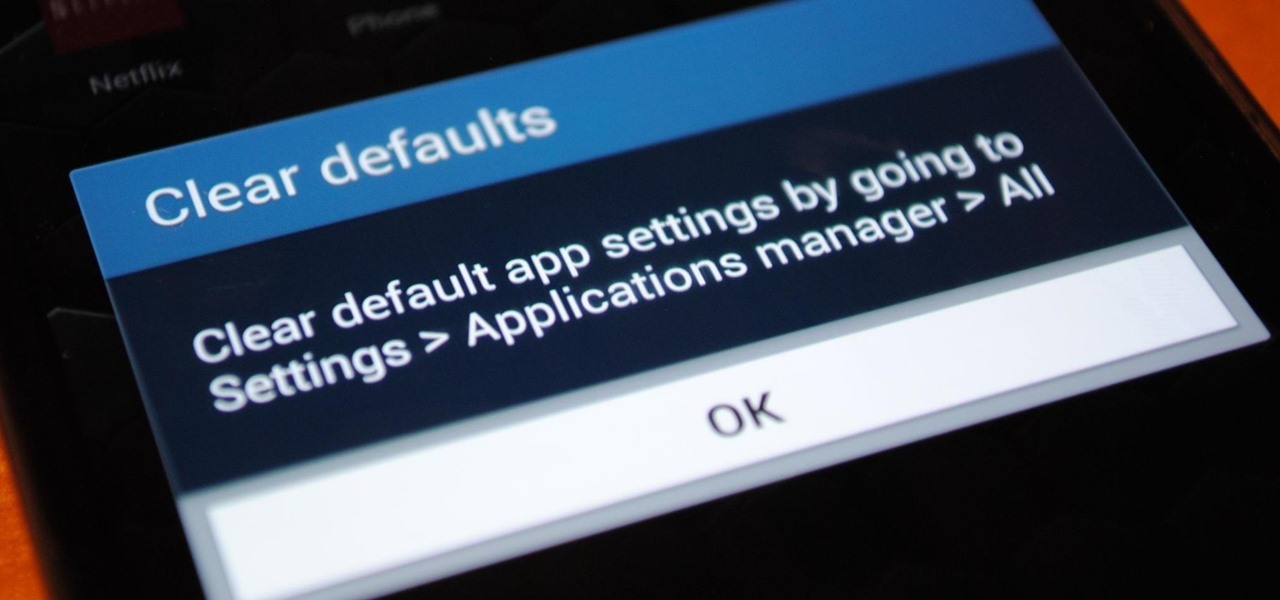
Customization is one of Android's popular selling points, and going hand-in-hand with that is being able to set default apps for different actions. Whether you want to play a song, navigate somewhere, or send a text, you can set a go-to app for each of those tasks.

If you've had the pleasure of owning both an iOS and Android device, you may have noticed one subtle difference on each one's PIN unlock screen. Android's lock screen requires you to press "OK" after entering the PIN, whereas iOS's simply unlocks the screen right after the last digit.

Big bad Apple recently announced its next iterations of iPhones and the world went crazy—as usual. Displaying an array of cool colors and futuristic features, the new iPhone 5S and 5C will both be rocking iOS 7, a sleek, modern operating system that gets rid of the old icons and glossy finish for a more flat and contemporary design.

Tony Stark is a smooth talking, genius billionaire playboy that occasionally saves the world... what's not to like? The Marvel films starring Robert Downey, Jr. have grossed well over a billion dollars in the U.S. alone, so it's needless to say that Iron Man is a very popular superhero.
This how to will show you how to program a fairly simple Hacking bat file. First open notepad.

Welcome back, my fledgling hackers! One of the first issues any hacker has to address is reconnaissance. Before we even begin to hack, we need to know quite a bit about the target systems. We should know their IP address, what ports are open, what services are running, and what operating system the target is using. Only after gathering this information can we begin to plan our attack. Most hackers spend far more time doing reconnaissance than exploiting.

Android gets a lot of love for its immeasurable amount of customization, and for the most part, you don't even have to do any heinous hacking to swag out your Samsung Galaxy S3 or other Android device.

This is a photography how-to video, where American photographer Eric Levin takes us on the set of a photo shoot with punk band Ice Nine Kills. This is a really good step-by-step "how-to" guide to the perfect photo of a music band.

Welcome back, my novice hackers! My recent tutorials have been focused upon ways to NOT get caught. Some people call this anti-forensics—the ability to not leave evidence that can be tracked to you or your hack by the system administrator or law enforcement.

With the introduction of Vine and the subsequent Instagram update, abbreviated video sharing has come to the masses, to be experimented with in an unprecedented way.

Welcome back, my fledgling hackers! Nearly every commercial enterprise worth hacking has an intrusion detection system (IDS). These network intrusion detection systems are designed to detect any malicious activity on the network. That means you!

Due to its enormously awesome size, the Samsung Galaxy Note 2 usually takes two hands to maneuver through photos and texts, write emails, and get directions on the map.

In this guide, you'll learn how to make your own boric acid from borax and other common chemicals to produce a green flame when mixed with methanol.