
News: May 2010 NPD Sales Results
Yes, they are May numbers, NPD is late by a month due to "IT" problems. They might have well blamed it only oil spill crisis.


Yes, they are May numbers, NPD is late by a month due to "IT" problems. They might have well blamed it only oil spill crisis.

ZERO WASTE. Yes, You read that right. This kitchen of the future aims to have zero waste. Ekokook the kitchen concept out of design company Faltazi gives us hope for a greener future. How is this possible you ask when in most homes 85 or 90 percent of a family's trash is generated in the vicinity of the kitchen? Ekokooks kitchen system is divided up into disposing and storing your waste in three mechanized sectioned systems Solid Waste, Liquid Waste and Organic Waste. Solid Waste- The solid w...
Microsoft Ribbon hero is an application that turns the office into game. It is designed to boost skill and knowledge in Microsoft Office’s latest version. It is released with office 2007 as a social game for increases productivity in office applications. It is compatible with Microsoft Excel 2007, Microsoft Word 2007, and Microsoft PowerPoint 2007 as well as those three programs in Microsoft Office 2010, available as a beta download.

Some say Nigel Richards is to SCRABBLE what Garry Kasparov is to chess, but that doesn't make him perfect.
JUAREZ. PH33R. SUX0R. If you know what these mean, then you probably spend way too much time on the internet. If you're as bewildered as I was, these words actually mean something in leetspeak.

Word of mouth is that Zynga is preparing to harvest the world. Is this a horror movie? No, but FarmVille has already invaded millions of homes, and now it wishes to conquer our pockets. They're gearing up for a mobile platform, one that will reach millions more via the iPhone, iPod Touch, iPad, and Android.

Popsci has posted 2009's most amazing scientific images, and there's quite a few great ones in there. A few of our favorites below, click through for all 62.

Have you been wondering if George Washington is related to you, what about Christopher Columbus, maybe even John Wilkes Booth? Well, with a little help from Ancestral Quest, you might just find out.

The motivation for the Add Shadow command, according to sources at Macromedia, was in response to a popular enhancement request to add "perspective shadow-like" capability to Fireworks. In this Fireworks 8 video tutorial you will learn how to use distort to add perspective shadows to your objects. Make sure to hit "play tutorial" in the top left corner of the video to start the video. There is no sound, so you'll need to watch the pop-up directions. Add perspective shadows in Fireworks 8.

Whether you're a student, a toastmaster, just writing, or making articles on WonderHowTo, you will have to come up with a topic. The topic should be able to guide you to some of the things you want people to know about. Here are some ways that you can can come up with a topic.

Soft boxes diffuse and enlarge your light source. Learn about soft boxes in this free video on studio equipment for photography. Use soft boxes in photography - Part 1 of 30.
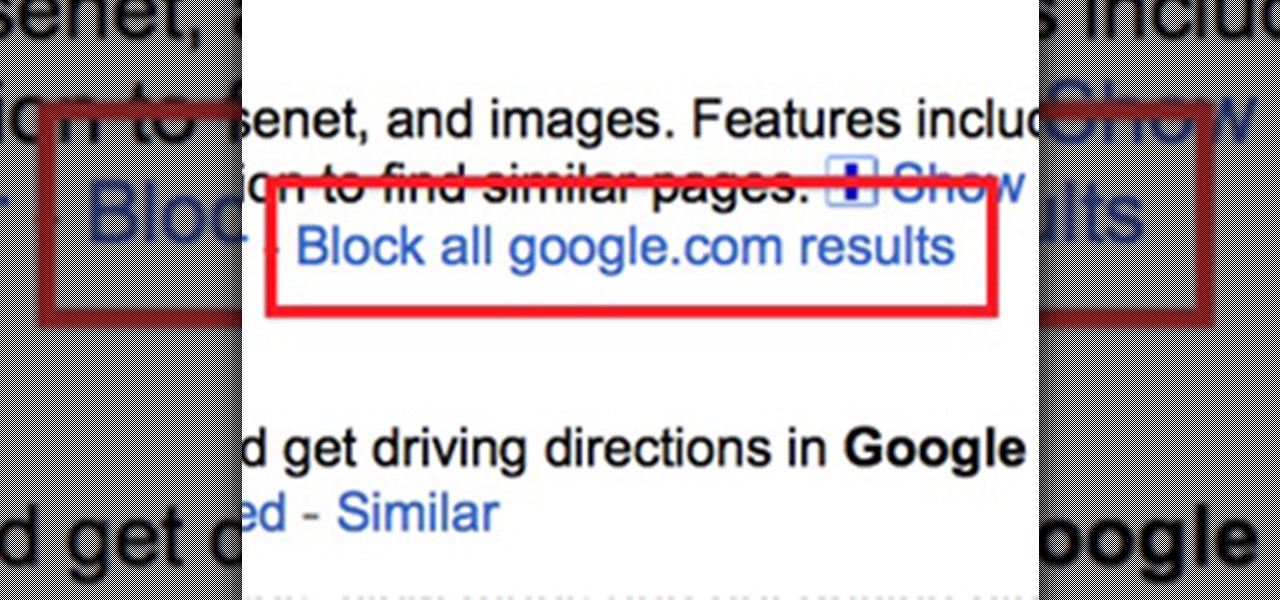
Google recently rewrote their search algorithm to make "low-quality sites" disappear from your front page results, putting the emphasis on better, more relevant answers with original content and in-depth information. And now Google has added a new feature to their search system that gives you some of the control of what you see in your results.

We all want a faster, more efficient web browsing experience. Some immediately flocked to Google Chrome as soon as it was released, because of its super fast speeds. Others restrained themselves and continued to wait for Microsoft and Mozilla to play catchup. And the time is almost here for all Internet junkies to improve their game.

Kill with skill. That's the motto of the newly released Bulletstorm, available on PlayStation 3, Xbox 360 and Windows. It may sound ridiculous and somewhat obnoxious by itself, but it's actually in regards to its many "ridiculous skillshots" that a player can perform. And yes, ridiculous skillshots was an actual quote, straight from Epic Games.

Summary

This past weekend's workshop on replacing normal levers with buttons masquerading as levers went really well. Lots of players showed up and everyone had a great time. Most importantly, everyone learned how to make and use a T flip-flop!

After his fall from Asgard into space, the Asgardian Loki meets the Other, the leader of a warmongering alien race known as the Chitauri. In exchange for retrieving the Tesseract,2 a powerful energy source of unknown potential, the Other promises Loki a Chitauri army with which he can subjugate the Earth. Nick Fury, director of the espionage agency S.H.I.E.L.D., arrives at a remote research facility during an evacuation. Physicist Dr. Erik Selvig is leading a research team experimenting on th...

WonderHowTo is a how-to website made up of niche communities called Worlds, with topics ranging from Minecraft to science experiments to Scrabble and everything in-between. Check in every Wednesday evening for a roundup of user-run activities and how-to projects from the most popular communities. Users can join and participate in any World they're interested in, as well as start their own community.

Big brother is watching when you're playing around on another system—and big brother is that system. Everything from operating systems to intrusion detection systems to database services are maintaining logs. Sometimes, these are error logs that can show attackers trying various SQL injection vectors over and over. This is especially so if they are using an automated framework like sqlmap that can spam a ton of requests in a short time. More often than not, the access logs are what most amate...

Since the rise of private property and industrial production, modern capitalism has been on a undeniable crash course with Mother Nature. It's no so much that we'll end up murdering the entire planet, but just that the planet will quietly smother us with a pillow of famine, heat, cold and hurricanes. We over-farm land and replace the nutrients in the soil with oil. To package our oil-based produce, we wrap them in synthetic oil-based plastics, soon to be discarded in a trash heap or ocean.

If you’ve never heard of the term search engine optimization or SEO, then your website probably isn’t optimized for search engines and it’s hindering your site’s ability to get all of the traffic that it should. Read on for an explanation of what this entails and how it can help your website.

If you know anything about search engine optimization and online marketing then you know that having as many links going into your site from good sources is very important. And if you’re not really experienced at building links or SEO in general then you might not know the best way to get good links for your site. So please read on and I’ll present to you what I feel is the best way to get good quality links for your site.

In the last article, we left off with the Tor network and its hidden services. As I mentioned, Tor is not the only option in the game, and I want to offer a general introduction to I2P.

Grab your thinking caps and get your hack on. Null Byte is officially seeking contributors on a weekly basis who are willing to take the time to educate the Null Byte community on anything, from hardware hacks to life hacks. Contributors that write tutorials will be featured on the Null Byte blog, as well as the front page of WonderHowTo (providing it's up to par, of course).

Normal body temperature, normothermia or euthermia; is a range of temperature rather than a fixed number. That Range represents the temperature that could be measure form the body under normal conditions.

Here's something fun for the Null Byte community to do—a coding competition! This week, I wanted to get everyone involved by offering you all a nice library of possible program types to choose from and try to code. At the end of this competition, all of the submitted programs will be reviewed by the community and myself. The coder that receives the most votes will be dubbed THE BEST.

I'm sure we've all heard about MSN and Yahoo! Messenger, right? They can be useful, but the setup can be quite time consuming for those who need to use it just once or twice—and the privacy statements are a real bother. For example, we must provide our real details. You could use Fake Name Generator, but if you get caught, you will have your account suspended. I don't have a law degree, but to my understanding the United States recently passed legislation that gives the authorities the power ...

The community tore up the first realistic mission last week. You've applied the techniques learned in the basic missions to a real scenario, so I'm pretty content. The realistic missions are where the learning gets intense and where we can apply real knowledge to extremely realistic situations. We will also be continuing the normal Python coding and hacking sessions. These sessions are created to bring our community together, to learn from each other, and grow together. Everyone is welcome, f...

In this article, I'll show you how to make a portable prank stun-baton. Powered by static electricity, simply charge up the baton, and discharge it for a static surprise. The concept behind this device ties in with Leyden jars, and their tendencies to retain static electricity.

As per Alex's request, I am posting about generating word-lists in Python. However, this is my FIRST attempt with Python, so please provide me with critiques and any and all comments. I really want to know what you think as there was a little bump here and there seeing as I am transitioning from C#.

Today I will show you how to create a simple keylogger in Visual C# Sharp, which will start up hidden from view, and record anything the user types on the keybord, then save it into a text file. Great if you share a PC and want to track what someone else is writing.

Null Byte is looking for forum moderators! Welcome to the ninth Community Byte for coding in Python and completing the challenges presented to us by HackThisSite. These sessions are created to bring our community together, to learn from each other, and grow together. Everyone is welcome, from novice programmers to aspiring hackers.

Some people are what is labeled a power user. I am one of these people. No matter how fast I get my system, or how quick of programs I have, it is never good enough. There is always at least one program that I could swap out for a more advanced, text-based counterpart that increases performance just a bit. Luckily, you don't have to use text-based programs without graphical user interfaces to get blazing fast speeds on Linux. There are tons of open source alternatives to the mainstream progra...

File Transfer Protocol, or FTP, is a network protocol made for transferring files in a client and host fashion over a Transmission Control Protocol (TCP) network, such as the internet. FTP is integrated into most browsers, and you have probably used it before. It is a common way to host files and transfer them easily. To access an FTP, a login is required, unless the server is configured to use anonymous logins (like the Arch Linux mirrors).

More password cracking action from Null Byte! Today we aren't going to be cracking passwords per se, rather, we are going to learn the basics of generating rainbow tables and how to use them. First, let's go over how passwords are stored and recovered.

WENDIGO n pl. -GOS windigo 62 points (12 points without the bingo)

CARRION n pl. -S dead and putrefying flesh 59 points (9 points without the bingo)

Having a custom Linux distro can be the coolest thing ever. Most of you will probably be satisfied with any particular Linux distribution, but I know I'm not the only one out there who wants it to have custom configurations and programs preloaded while leaving the bloatware behind.

Increasingly, I'm turning to Google+ as a source of news, and it looks like I'm not the only one. On Thursday, news of a small earthquake broke on both Twitter and Google+. One curious user, +Keith Barrett, decided to try and find out which social network was faster with the news. Turns out it was a tie. As Google integrates Google+ more closely with the rest of its services, and more users post relevant stories, I think we'll start to see Google+ as a place that can create and break stories,...

Cross-Site Request Forgery (CSRF, pronounce "sea-surf") is a common web exploit. However, for unknown reasons it's not used very often. It plays on a given website's trust in a web browser by executing another website's form action, for example, sending money to another person. It's usually placed in abnormal places like HTML image tags.