The Operative Framework is a powerful Python-based open-source intelligence (OSINT) tool that can be used to find domains registered by the same email address, as well as many other investigative functions. This reconnaissance tool provides insight about your target through examining relationships in the domains they own.
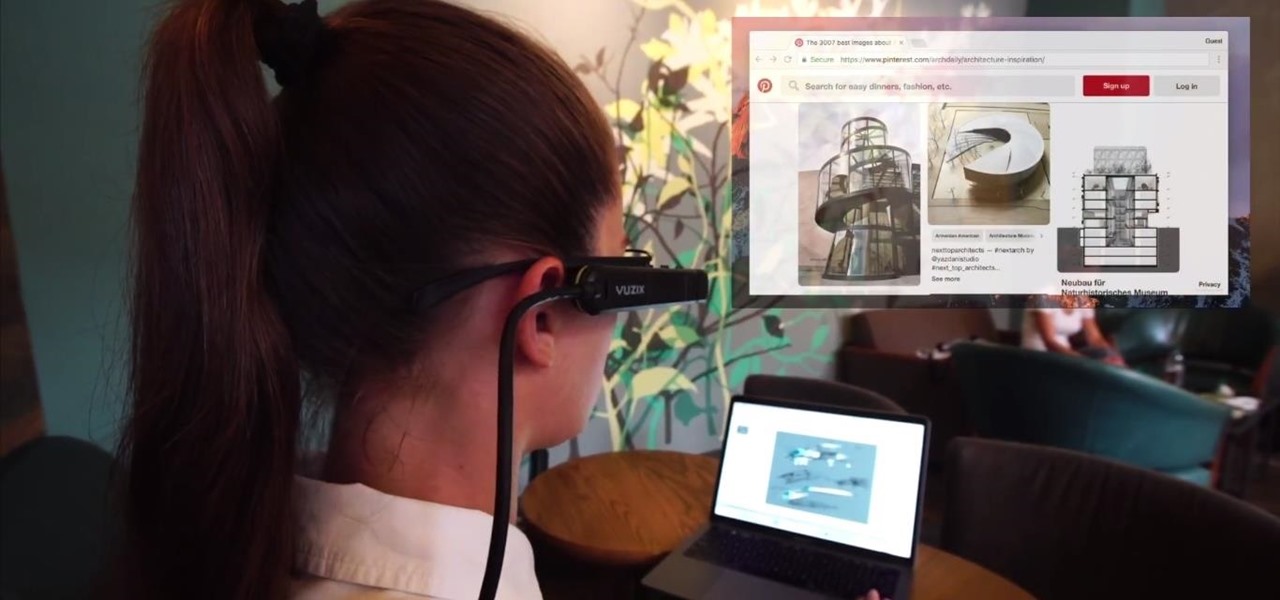
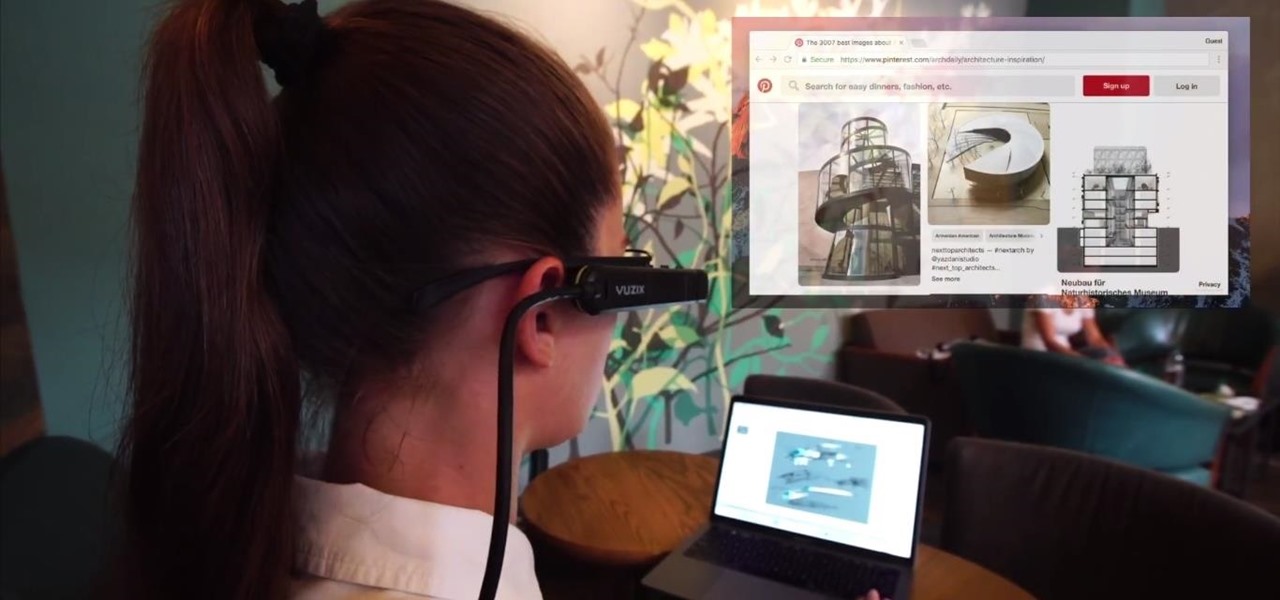
Screen mirroring app iDisplay has arrived for Vuzix M300 Smart Glasses. With the app installed on the M300 and the companion software running on a Mac or Windows computer, users can mirror or extend the computer's desktop to the headset's display, which is connected to the computer via Wi-Fi or USB cable. The app does not yet appear on Vuzix's app store.

For companies wary of the temperature, PTC just made it easier for them to dip their toes in the waters of augmented reality.

Any parent with a rambunctious child who may have at one point racked up a hefty bill on their Kindle or Android device can now breathe a sigh of relief. One, Jack Black has had it happen to him too, and two, Amazon will be refunding up to $70 million of in-app purchases made by children after downloading apps from the Amazon AppStore.

It's the bane of many a tech geek's existence that the customizability of Android software cannot be combined with the sleek design of the iPhone. A new Kickstarter project titled Eye, however, is looking to change that with a new iPhone case that allows you to combine the two.
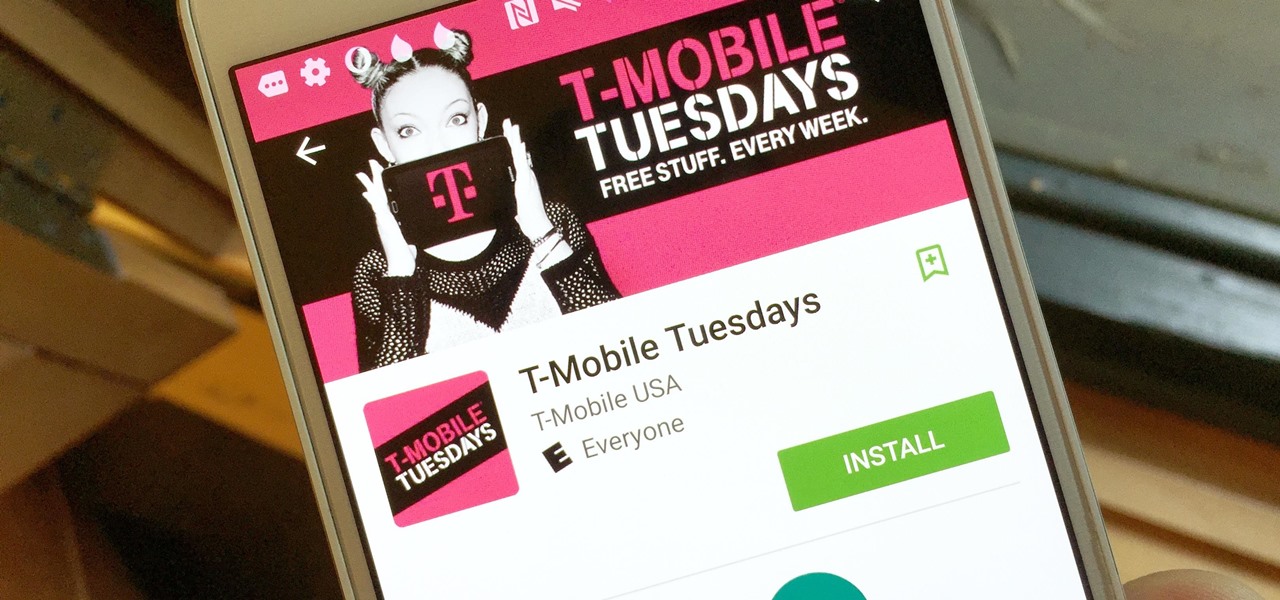
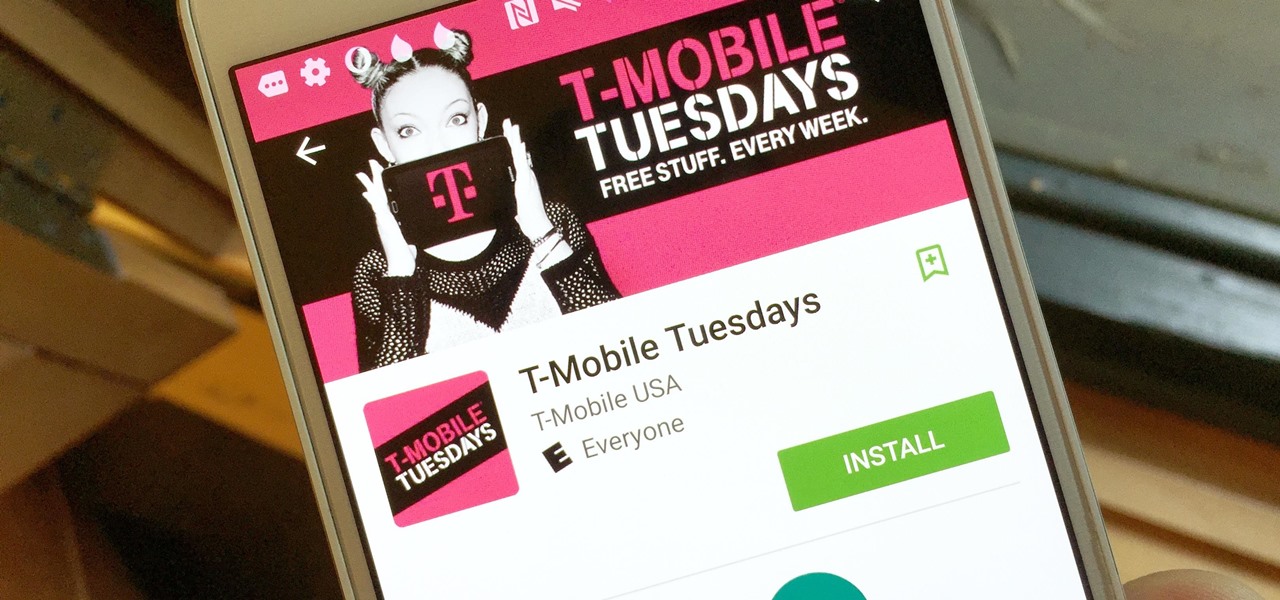
T-Mobile is going for broke. The carrier recently announced it will be giving away free stuff to its customers every Tuesday through a new app called T-Mobile Tuesdays for Android and iOS, and that's in addition to one share of stock and free in-flight Wi-Fi. The app will give out "food, movie tickets, gift cards, subscriptions, ridesharing, and more," the announcement said. You just have to be the primary account holder and you're good to go. One person will win a huge prize every Tuesday, l...

Since I first announced the new Null Byte recognition for excellence a few weeks ago, several of you have written me asking, "How can I study for this certification exam, and what material will be covered on the exam?" Now I have an answer for you. The White Hat Hacker Associate (CWA) will cover 14 domains or areas. Everything you need to know is here on Null Byte. There will be no questions that are not covered here on this site, guaranteed.

In recent weeks, major bank websites around the world have experienced outages after being have been hit with Distributed Denial of Service (DDoS) attacks. Although few, if any, of these banks have been totally knocked offline, these DoS attacks have dramatically slowed the response time of their websites to legitimate customers. The most recent victim was the Royal Bank of Scotland. Due to this attack, RBS customers were unable to access their accounts for about an hour last week.
So, you wan't to become a Xbox Community Ambassador? Wan't to give support to other Xbox Customers and Earn loot doing it? Want to be different from a "normal" Xbox Customer? Want to share your knowledge to others who want it? Come on over here, friend! In this How-To, I will tell you how to become a Xbox Community Ambassador in the most correct way possible! In 3 Easy Steps! Here is the Link to the Website : http://ambassadors.xbox.com/

For $100 each year (unless you used Faisal's workaround to save yourself twenty bucks), Amazon Prime membership gives you access to all the best that Amazon has to offer. From free 2-day shipping to Prime Instant Video, there's a lot to like about the service.

This video demonstrates how to calculate shipping costs with UPS. UPS provides an easy-to-use online calculator to help customers accurately estimate shipping costs. By following a few simple steps, this tool can help customers control their shipping costs and avoid confusion during the billing process.

A couple of months ago at the Black Hat security conference, hacker Cody Brocious gave the hotel industry a nasty surprise when he figured out how to hack the locks made by Onity that are used in millions of hotels worldwide.

It's easy to lose oneself when playing Minecraft and easier still to get plum lost. That's why it's always good to have a compass on hand. No compass? No problem. There are, in fact, no fewer than seven methods at your disposal for finding true north in a Minecraft world. Better still, a lot of them are accessible to you from the very moment you start playing the game.

Step 1: Score! Watch for the referee signaling a touchdown, field goal, extra point, or successful try by raising their arms straight up over their head. Raising their hands above their head with palms together signals a safety.

It's slime time! Get ready to make some sticky, gooey, slippery slime with the A-TV science sleuths.

Who said you can't play with your food? Join the A-TV science squad and learn how to make a rubbery bouncing ball out of pudding!

Soap suds aren't just for dishwashing! Blow away your family and friends with this cool science experiment.

While conducting an OSINT investigation, it's important to be able to pull in information based on any clue you uncover. In particular, license plate information can turn up everywhere, from photos to live data to on your own street. You could use that data to find the VIN, see if a Tinder date has hit anyone, find out who's blocking your driveway, and so on. Skiptracer can help get the ball rolling.

Since its release back in 1988, Microsoft Office has been the top client and server software suite for businesses around the world. Office's domination is thanks to both Microsoft's extraordinary foresight and their continual updates and innovations to ensure that companies always get what they need.

Alongside its official unveiling of the lower-cost Pixel 3a smartphone at Google I/O, Google took the opportunity to extend its early preview of AR walking navigation in Google Maps to all Pixel devices.

New images reveal that Microsoft is already well underway in fulfilling its $480 million contract to provide augmented reality headsets to the US Army.

When it comes to attacking devices on a network, you can't hit what you can't see. Nmap gives you the ability to explore any devices connected to a network, finding information like the operating system a device is running and which applications are listening on open ports. This information lets a hacker design an attack that perfectly suits the target environment.

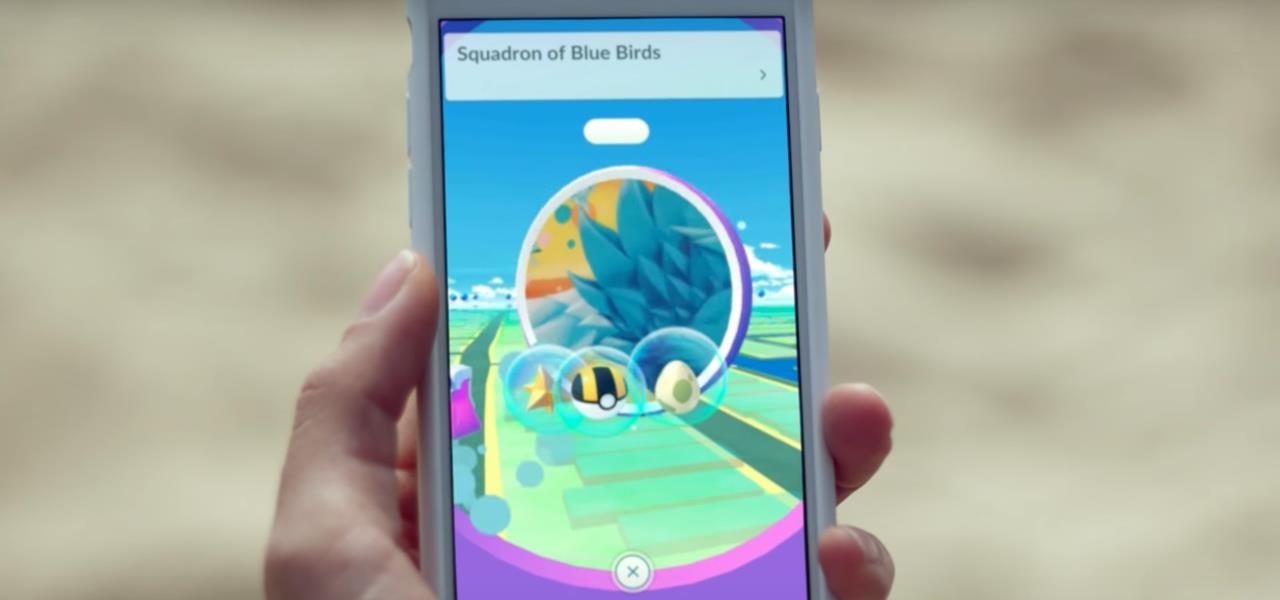
Augmented reality gaming developer Niantic has decided to give its players the opportunity to make their mark on Pokémon GO with a PokéStop nomination system.

Smartglasses maker Epson remains the top gun in the drone market with its Moverio line of wearables, and the company is further elevating its offerings with its new Drone SoAR app for DJI drones.

After years of rumors, we got our Apple Watch, and we have our anniversary iPhone, so now everyone has moved on to a new Apple rumor obsession: Apple smartglasses. And, in keeping with Apple rumor tradition, we're getting some pretty imaginative ideas of what the next big Apple product might look like.

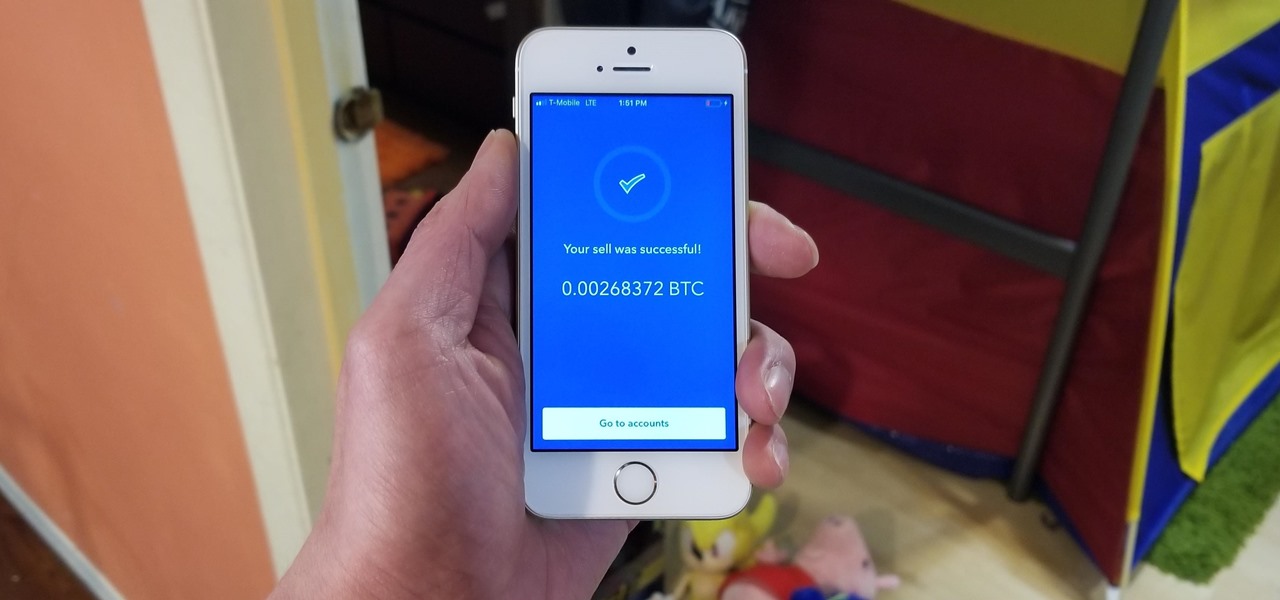
Coinbase has become the most popular mobile wallet app due in large part to its user-friendliness. The app takes the hassle out of buying and selling Bitcoin (BTC), Bitcoin Cash (BCH), Ethereum (ETH), and Litecoin (LTC), letting Android and iPhone users alike trade their favorite cryptocurrency in a few easy steps.

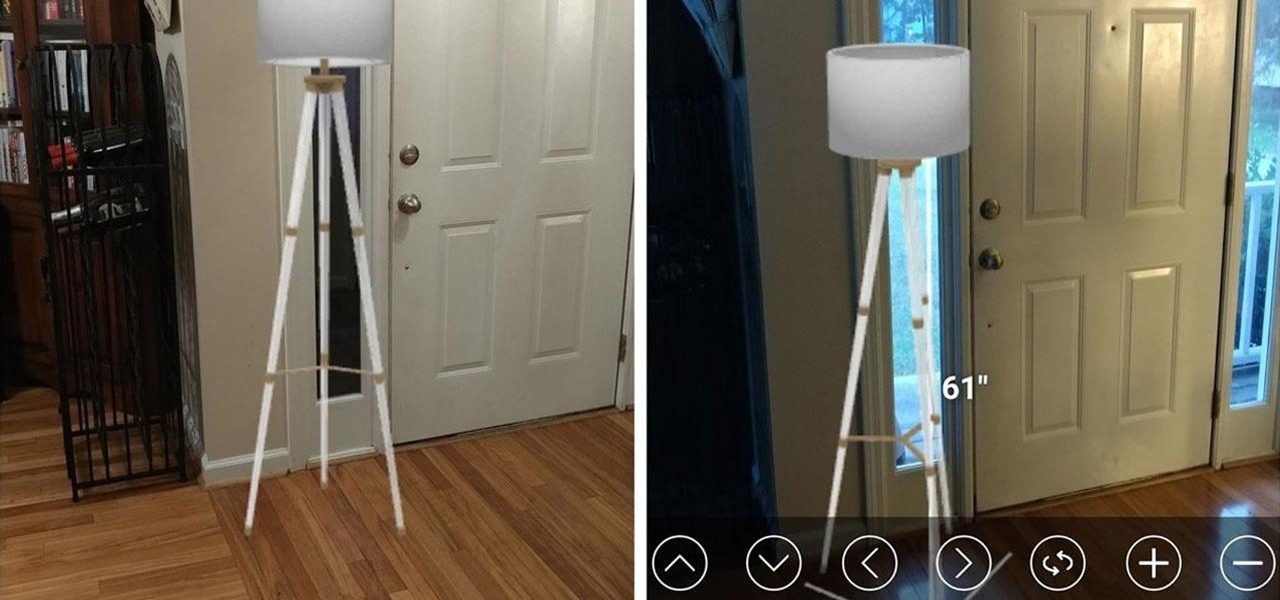
While some companies like IKEA and Lowe's zig towards ARKit to entice shoppers, Target has opted to zag to broader appeal with an augmented reality see-before-you-buy tool for its mobile website.

Augmented reality developer Blippar has created a new visual positioning service based on computer vision that is two times more accurate than GPS in urban locales.

With mobile developers near and far primed to implement augmented reality into their iOS apps with Apple's ARKit, uSens offers them a new tool for markerless location tracking.

More bad news for patients who have undergone heart surgery in the past five years. A new study suggests about one-third of heater-cooler units used in cardiac procedures remain contaminated with a slow-growing, potentially fatal bacteria.

Citrus greening disease — caused by a bacteria spread by psyllid insects — is threatening to wipe out Florida's citrus crop. Researchers have identified a small protein found in a second bacteria living in the insects that helps bacteria causing citrus greening disease survive and spread. They believe the discovery could result in a spray that could potentially help save the trees from the bacterial invasion.

Blizzard's Hearthstone was a rousing success with more than 10 million downloads on the Google Play Store. Not taking things lying down, Bethesda, the creator of The Elder Scrolls, has come up with a card game based off its popular fantasy franchise. The Elder Scrolls: Legends is now out in the wild, though, officially only available for select Android tablets. But with a little creativity, there's a way to game the system and play Legends on any Android device. The Elder Scrolls: Legends is ...

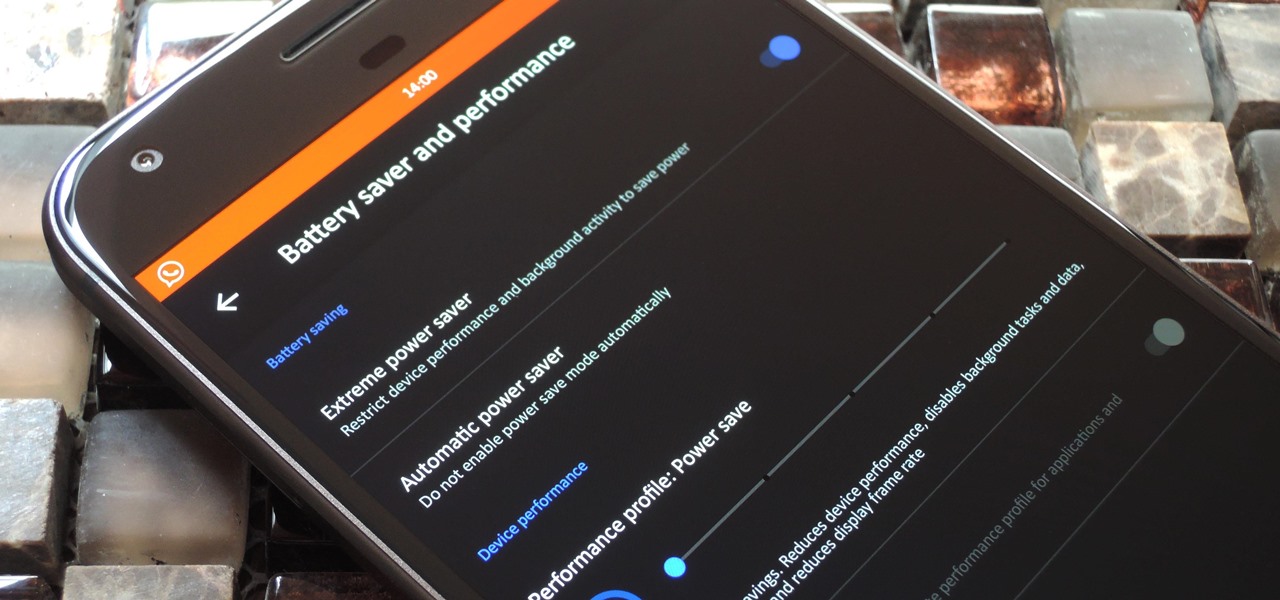
LineageOS, the successor to the wildly popular CyanogenMod custom ROM, is adding an interesting new feature that could potentially save lots of juice when your battery is running low. When enabling "Extreme power saver" mode, which can be set to kick in automatically at 15%, you'll soon have the option of changing your kernel's performance profile as well.

When it comes to a perfect summertime dessert, lemon meringue pie is the ideal contender with its rich lemon filling and light-as-air meringue topping. In my humble opinion, the meringue is the true star of the dessert, instantly elevating what is simply a lemon pie to something more elegant and certainly more decadent.

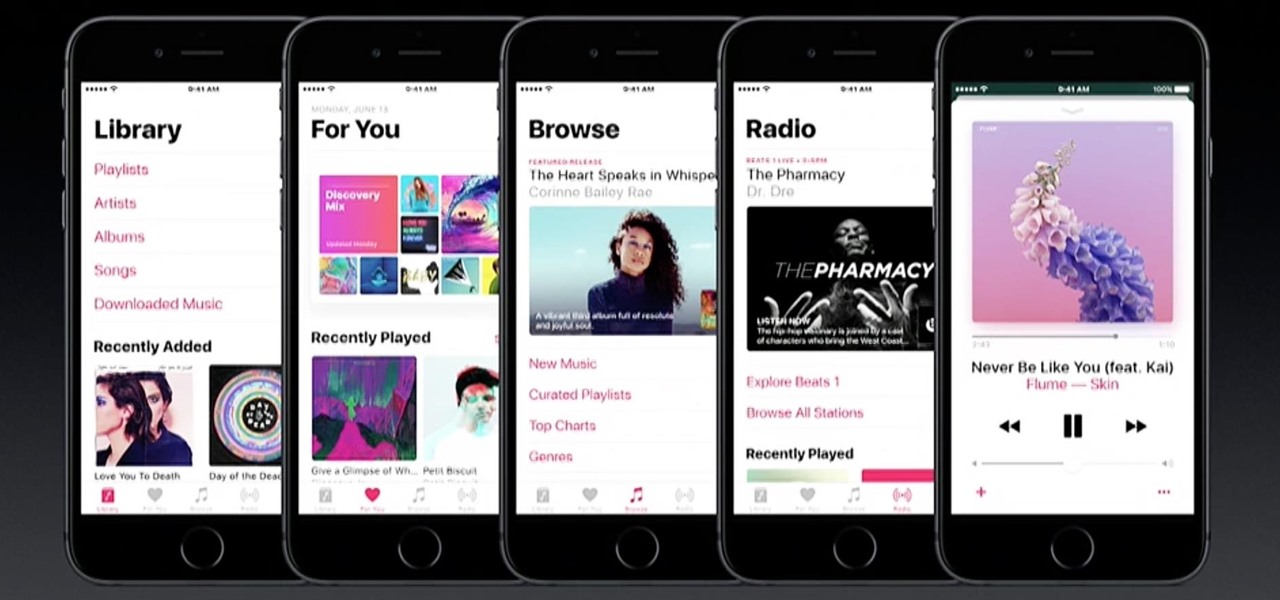
iPhone and iPad users are getting a huge update with iOS 10, and one of the biggest (and most sought after) redesigns is to the Music app, as shown at Apple's WWDC '16. The redesign essentially makes the user interface easier to navigate, which was something that was fairly clunky starting in iOS 8.4 when Apple Music was first released.

If you're in the market for a new tattoo, the biggest hurdle to clear is imagining exactly how it's going to look. It's going to be part of your identity for the rest of your life, so you have to make sure it looks just right—or as your mom probably told you, "Think of what it's going to look like when you're 60."

What's up, peeps? In this quick tutorial, we will be looking at structs, a special kind of data type.

Before we begin learning about another vulnerability, we are going to explore printf in a bit more detail. This will be quick little tutorial.

In many programs on Linux, you'll come across programs which allow you to specify additional arguments instead of just simply running the program by itself. If you've used the Kali distribution, I'm more than certain you'll have come across these with the command line tools, else if you have been following these tutorials, we have already come across three tools which also use the same technique, i.e. gcc, gdb and wc. How do we do this with C? Let's find out.

Hey readers! This tutorial will be the entry point for the introduction of buffer overflows. Something like requesting user input is a very common place for vulnerabilities to pop up and we will definitely have fun while trying to make programs crash. But for now, let's start with how we can get input from a user.