The sheer variety of Android devices on the market is staggering—one report suggests there are well over 24,000 distinct phones and tablets floating around out there. When you consider that each manufacturer adds a few tweaks to the Android code base here and there, that makes for a lot of software variations, which in turn means there needs to be many different root methods to match this variety.

This year, Google released two Nexus phones to glowing reviews, and as we've grown to expect, the Android community wasted no time in coming up with a root method for both. In fact, legendary root developer Chainfire even devised an entirely new "systemless" method for rooting that should make updating a bit less complicated, along with a few other benefits.
Let's say that you've got the look down, and you have your Steampunk props all ready to go. Congratulations! You're a Steampunk!

Whether you miss the good old days of Telnet or you want to know what hacking was like when security was nothing but an afterthought, Telehack is the game for you. The text-based hacking game is a simulation of a stylized combination of ARPANET and Usenet, circa 1985 to 1990, with a full multi-user universe and player interactions, including 26,600 hosts.

If you're on the hunt for a profitable side-gig, or even a completely new way to to make money, you'll want to take a look at Upwork, a leading freelancing platform that connects skilled freelancers with clients from all over the world.

Virtual private networks, or VPNs, are popular for helping you stay anonymous online by changing your IP address, encrypting traffic, and hiding your location. However, common IoT devices, media players, and smart TVs are hard to connect to a VPN, but we have a solution: Turn a Raspberry Pi into a router running through PIA VPN, which will ensure every connected device gets the VPN treatment.
Have you ever used an open wifi, which after you connect displays a website to enter your credentials to get internet? That website is called captive portal and widely used in airports, hotels, universities etc. Have you ever wondered what would happen if someone would set up an open wifi with the same name displaying a very similar web page asking for credentials? Usually if there are multiple wifi networks with the same name and encryption, devices only display the one with the highest sign...

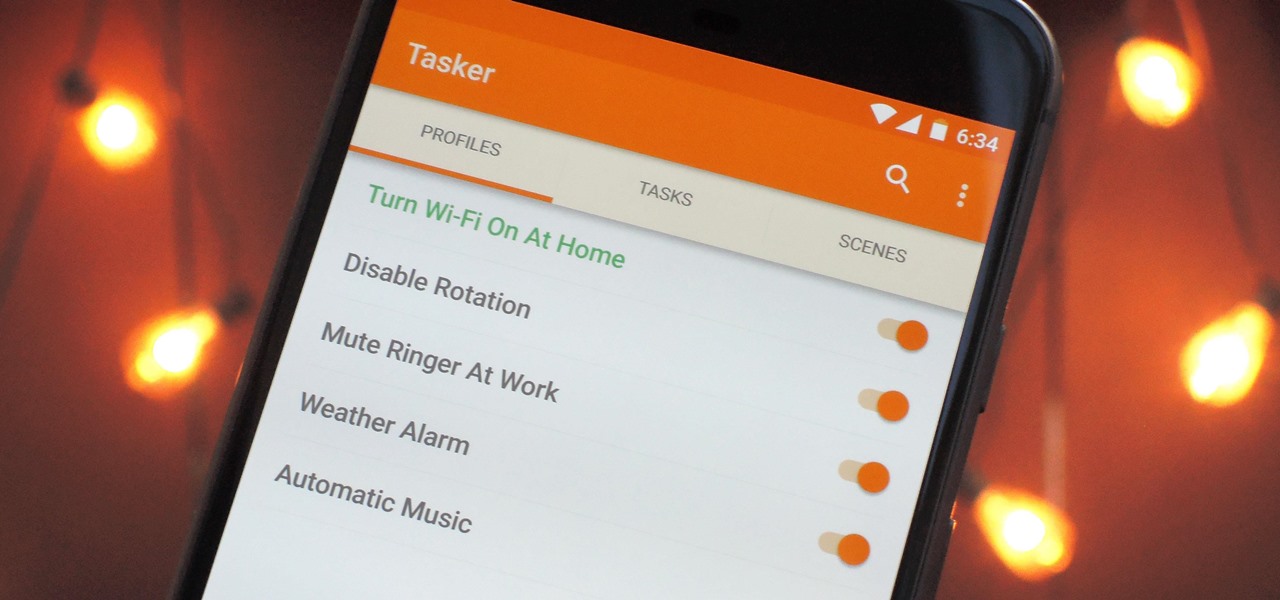
When it comes to automation apps on Android, Tasker is still the king of the hill. For a price of $2.99 on the Google Play Store, it's a great buy for any would-be tinkerer that would like to get into automating actions on their Android device. Then, when you consider that there's a free 7-day trial version available, there's almost no reason that you shouldn't at least test the waters with Tasker.

I don't know how many of you had this experience in your youth, but when I was a kid, I used to actively think about what would happen if I suddenly woke up in a fantasy land, or were to pass through a portal into another space and time. I knew it wouldn't really happen, but when you're a kid, these can be important issues to you. So I slept with my glasses on every night, just in case. Photo from George Pal's The Time Machine.

In the first part of this two-part guide, I covered cutting, grooving, beveling, making holes, and stamping/tooling. I hope you enjoyed that part, because we're pushing the accelerator to the floor and moving ahead at full speed!

Your iPhone's Mail app has a lot of fantastic productivity features, such as unsending emails, follow-up reminders, opening drafts from almost any view, the snooze option, bulk-selecting messages, and the formatting toolbar, but one of the most helpful ones might just be the one you're not using.

The Pi-hole project is a popular DNS-level ad blocker, but it can be much more than that. Its DNS-level filtering can also be used as a firewall of sorts to prevent malicious websites from resolving, as well as to keep privacy-killing trackers such as Google Analytics from ever loading in the browser. Let's take a look at setting a Pi-hole up and customizing a blacklist to suit your needs.

During our last adventure into the realm of format string exploitation, we learned how we can manipulate format specifiers to rewrite a program's memory with an arbitrary value. While that's all well and good, arbitrary values are boring. We want to gain full control over the values we write, and today we are going to learn how to do just that.

So, your grandmother finally wants to ditch her flip phone for a shiny new smartphone? Congratulations. But helping her get used to her new device, even when it's an iPhone, is no small task. Grandma mastered checking her email in late-2012 and just recently learned there's a thing called "Facebook." But we love grandma, and thanks to this guide, we can definitely make this happen for her.

I obviously do a lot of Steampunk projects, but there are a ton of things out there that I haven't tried yet. So, in an effort to broaden my horizons, I recently taught myself how to use Arduinos, which I plan to incorporate into some of my future Steampunk builds.

At launch, Chromecast with Google TV is fairly limited in the number of compatible apps. Many of the usual suspects are there, but there are some interesting omissions, like Google Stadia (though support is coming). However, at its core, the device runs on Android 10, which means you can sideload apps, including those that don't officially support Chromecast with Google TV.

While our time with the Protostar VM from Exploit Exercises was lovely, we must move on to bigger things and harder challenges. Exploit Exercises' Fusion VM offers some more challenging binary exploitation levels for us to tackle. The biggest change is that these levels are all network services, which means we'll write our first remote exploits.

After a long hiatus, we shall once again emerge from the shadowy depths of the internet to build an exploit. This time, we'll be looking at how to defeat a non-executable stack by using the ret2libc technique — a lean, mean, and brilliant way of exploiting a stack overflow vulnerability.

While iOS offers a plentiful mix of excellent and exclusive features, what you see is what you get. Apple doesn't leave much room for customizability, meaning most people's iPhones look relatively the same. You can make yours stand out, however, by giving your apps unique and personal icons.

Things just got a lot better in your iPhone's Messages app, and the most significant change lets you text Android users with iMessage-like features such as typing indicators, read receipts, large file sharing, high-quality photos and videos, and even emoji reactions.

Welcome to the first annual Next Reality 30, our list of people who've made the biggest impact on the augmented reality space in the last 12 months — and what a 12-month roller-coaster ride it's been. Apple introduced ARKit-powered apps last fall, Google launched ARCore for Android soon after, Snapchat began monetizing AR, and the Magic Leap One headset finally came out. These are historic times.

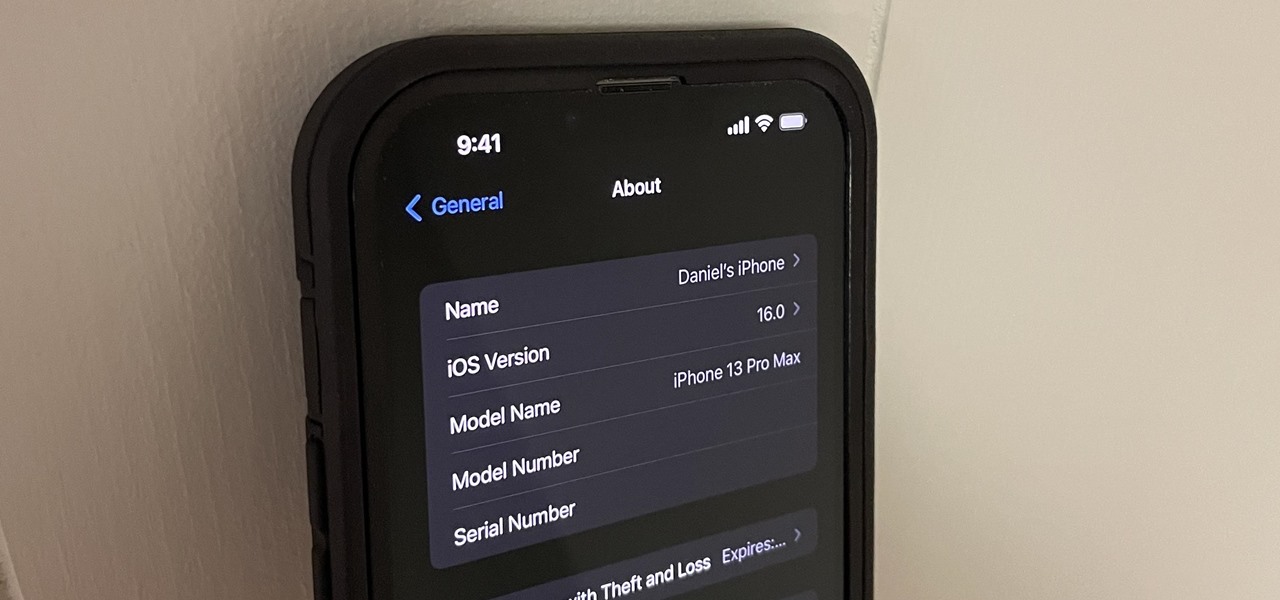
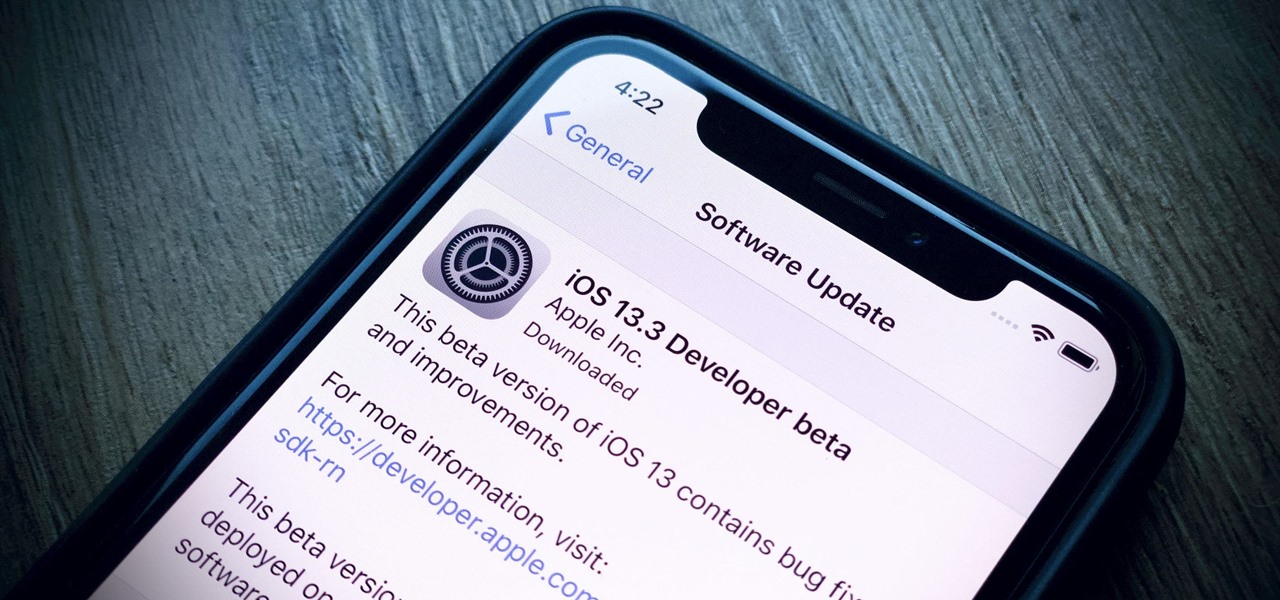
Beta software can be exciting because you get to experience cool new features before most other people. But it can have unwanted consequences such as bugs, UI glitches, and horrible battery life that'll make you wish you never installed it. If that sounds like you with iOS 16 beta or iPadOS 16 beta, you can downgrade to iOS 15.5 or iPadOS 15.5 for a more stable user experience.

If we were to assign a theme for the 2019 edition of the Next Reality 30 (NR30), it might be something along the lines of, "What have you done for me lately?"

Apple's already gone through iOS 13.0, 13.1, 13.2, 13.3, 13.4, and 13.5 betas, and now it's time for iOS 13.6. If you want to try out new features on your iPhone before the masses, install either the developer or public beta.

Apple officially unveiled iOS 14 on June 22 at its first all-virtual WWDC. After months of beta testing, iOS 14 hit iPhones on Sept. 16, but that doesn't mean that Apple is done beta testing iOS 14. There will be new features to try out right up until iOS 15 comes out next year.

The easiest way to change your mouse pointers using Deviant Art artwork is explained in this informative and easy-to-follow video.

This video will walk you through the process of updating a psp to the 5.50gen-a. This is information you may want if you are an avid psp user and would like to hide your Mac address. This video is a little hard to see but he will talk you through the main points.

If you were paying attention to the Rio Ad in the 4th quarter of the 2011 Super Bowl between the Green Bay Packers and the Pittsburgh Steelers, you might have noticed the secret Angry Birds code behind the monkey on the wooden fence.

Want to stick it to your mobile carrier by porting your cell number to Google Voice? Now you can! On Wednesday, January 19th, Google Voice began allowing select users to transfer their personal numbers to Google Voice for a one-time fee of $20. Though the feature is still in limited release, Google has stated that they intend to make the feature available to all Google Voice users "in the near future." Terrific, right? Not entirely!

Did you know that you can use Gmail to make free phone calls to anywhere in North America? We're not talking computer to computer, but actual free phone calls to cell phones and home phones. All you need is a Gmail account, a microphone, and speakers plugged into your computer.

Eating fire is a guaranteed method of not only impressing an entire room, but also instantly settling any questions as to whether or not you're a complete and total stone cold BAD ASS. When you can casually whip this trick out in a bar, you're not only going to get your drinks bought for you for the rest of the night, but at least three phone numbers scrawled on the backs of napkins.

Some of the most popular cellular devices on the market today are the iPhone 4 and 4S models. Seeing as they are made of glass, it's not uncommon for the back panel to break.

Getting your own blog is easier than what you can imagine. Thanks to WordPress. One need not be a techie to follow the steps mentioned below (though certain stages might require third-party advice).

Introduction Halo: Reach is Bungie's latest and final addition to the franchise. Microsoft has claimed the title and from now on 343 Industries will be working on the Halo franchise. In my opinion, Bungie's last game is the best out of all of them. These are some tactics and bits of advice that I've picked up.

Learn how to tie the snell fishing knot. 1. Run line through the eye and down the shank of the hook. Form a loop behind the eye with the line against the hook shank. 2. Pass tag end around line and shank and through loop four plus times. Keep turns in a neat row and pull tag end to tighten turns around the shank. 3. Work coil or turns down the shank to the eye by pulling on standing line. Pull alternately on tag end and standing line until snug. Congratulations! You just learned how to tie th...

Learn how to tie the dropper loop fishing knot with this instructional video. The dropper loop fishing knot forms a loop anywhere on a line. Hooks or other tackle can then be attached to the loop. 1. Form a loop in the line at the desired location. Pull line from one side of loop down and pass it through and around that side of loop. Make 5+ wraps around the loop, keeping a thumb or forefinger in the new opening which is formed. 2. Push bottom of original loop up through new opening and hold ...

Watch this knot tying instructional video and learn how to tie the improved clinch knot for fishing. The improved clinch knot has become one one of the most popular fishing knots for tying terminal tackle connections. It is quick and easy to tie and is strong and reliable. The improved clinch knot can be difficult to tie in lines in excess of 30 lb test. Five+ turns around the standing line is generally recommended, four can be used in heavy line. This fishing knot is not recommended with bra...

WonderHowTo is a great place to find advice and learn things that you want to know, but can't find anywhere else. On this website, there are tons of people who make articles and videos to show you how to do stuff. In this tutorial, you will learn how to make your own WonderHowTo account and join this amazing place.

Wall studs are both critical for maintaining the structure of your home and supporting items of weight and function on the interior walls (e.g. cabinets, shelves, plasma TVs, etc.). With wall studs playing such a critical role, consistently being able to find them is important. The problem with finding them is that drywall and wallboard isn't exactly see-through.