
News: How an Innocuous Bacteria Lots of Us Have Turns into Deadly Meningitis & Sepsis
How can bacteria that lives in the throat of 10%–35% of people—without causing an infection—cause life-threatening meningitis and sepsis in others?


How can bacteria that lives in the throat of 10%–35% of people—without causing an infection—cause life-threatening meningitis and sepsis in others?

Obstetric tetanus in an unvaccinated Amish woman after a home birth has emphasized the need for preventative healthcare.

A dangerous bacterial disease is infecting dogs in northern New Jersey, forcing owners to keep their pets inside.

In a world increasingly regulated by computers, bugs are like real-life cheat codes. They give you the power to break the rules and do good or bad without ever leaving your seat. And government agencies around the world are discovering and stockpiling unreported bugs as cyberweapons to use against anybody they see fit.
In the past, to see a pre-constructed state of the house that you would one day live in, you had to be able to read blueprints or hire an artist to sketch it out. Later came the ability to have a 3D rendering of that house on a screen, but you'd still have to work hard to envision it in real life.

Most people know atopic dermatitis by its common name, eczema—that dry, flaky skin that itches incessantly. Along with the scratching comes frequent skin infections, often with Staphylococcus aureus.

A young child becomes very thirsty very often and seems tired all the time. A visit to the pediatrician determines she has type 1 diabetes. The onset of type 1 diabetes may seem sudden, and it can be, but the disease may actually have been triggered by common childhood viruses years earlier.
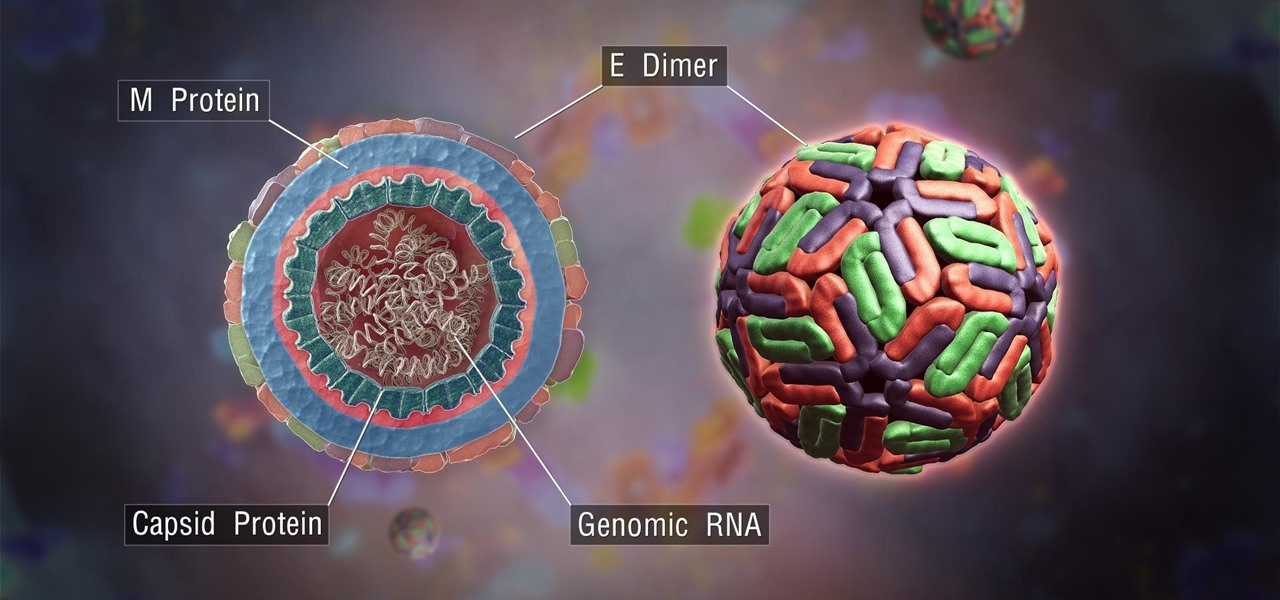
The mention of Zika can strike fear in the hearts of pregnant women. With infections increasing around the world, including in the US, researchers are fighting the clock to figure out how the virus can have such horrific effects in some people.

Video: . This video will show you how to secure your kayak to a J bar roof rack carrier.

Many people who use braided line complain that it gets wind knots which may have to be cut off and expensive line discarded. Almost all "wind knots" have nothing to do with the wind and are caused by user error. This video explains how to avoid those knots and start taking advantage of braided fishing line.

Hello ladies and gentlemen, PySec here coming at you with another informative(hopefully) article for you all. In the last tutorial, we finally finished our discussion about IP Addressing and I intentionally didn't mention a really important concept with which IP Addressing wouldn't be feasible without it. What I'm talking about is how our network device gets the IP Address in order to communicate with other devices on the network/Internet. There are many different ways for that to be accompli...

Greetings aspiring hackers. I have observed an increasing number of questions, both here on Null-Byte and on other forums, regarding the decision of which USB wireless network adapter to pick from when performing Wi-Fi hacks. So in today's guide I will be tackling this dilemma. First I will explain the ideal requirements, then I will cover chipsets, and lastly I will talk about examples of wireless cards and my personal recommendations. Without further ado, let's cut to the chase.

You want to become anonymous, and dont want your IP to be logged on websites? Well read along here. Continuing This Series:

Recently, I've been experimenting with BeEF (Browser Exploitation Framework), and to say the least, I'm hooked. When using BeEF, you must "hook" the victims browser. This means that you must run the script provided by BeEF, which is titled "hook.js", in the victims browser. Once you've done that, you can run commands against the victims browser and cause all kinds of mayhem. Among these commands, there is an option to use the victims webcam. This is what we'll be doing here today, so, let's g...

Hello! I'm newbie at Null Byte and I want tho share some of my thoughts with you guys, hope you like it. I've been inspired by 3 facts for making this: 1- The post 'How to write better code', 2- A few illegible comments at some posts, 3- I myself have never written such a long text in English, this will be my first one!

These days, that pocket-sized computer we call a smartphone is home to your entire digital life. But with the onset of mobile payments and online banking, the line between your virtual world and the physical realm is becoming increasingly blurred.

Welcome back, my rookie hackers! So many readers come to Null Byte to learn how to hack Wi-Fi networks (this is the most popular hacking area on Null Byte) that I thought I should write a "how-to" on selecting a good Wi-Fi hacking strategy.

Beautiful Macrame Bracelet. This video tutorial is intended for people who know a little bit about macrame :)

Hi there again, aspiring hackers (and veterans as well)! I'm going to explain how to perform a dictionary attack on a WPA/WPA2 protected network with Wifite. Please note that this doesn't work with WPA Enterprise For that end, you'd have to use an Evil Twin to get the "Enterprise" auth attempt, and then crack it.

These instructions are applicable to both bObsweep models. Follow the video or text descriptions to replace the disinfecting UV lamp on your automatic vacuum.

Hi again! :) Many people have been asking me to do a lesson about what to say when you visit the doctor in Lebanon, so here's that lesson. So if you're sick, I hope you get well, and I hope you enjoy this lesson and find it useful.

How to make a Macrame Lagoon Earrings. A good accessory to wear everyday and for any occasion. (This video tutorial is intended for people who know a little bit about macrame)..

If you're still looking for that perfect prank to pull off on people on April 1st, here are 5 simple yet funny practical jokes you can get your friends and family with. Most require household items which you should already have, so you won't need to go out and purchase any additional stuff. Check out the video tutorial to start pranking right away!

Inspiration for tutorial: Foxtrot's "How to Trap a Tracker"

This is just a heads up that thieves are now using GPS fitness apps to target people. Thieves are using popular GPS fitness apps such as Strava to find out where you live where they will then come and steal your bikes.

How to Make a Easy Macrame Criss-Cross Bracelet with Beads. It's simple to make and looks really cool and fun :) Even people who just found out about macrame can make this bracelet!
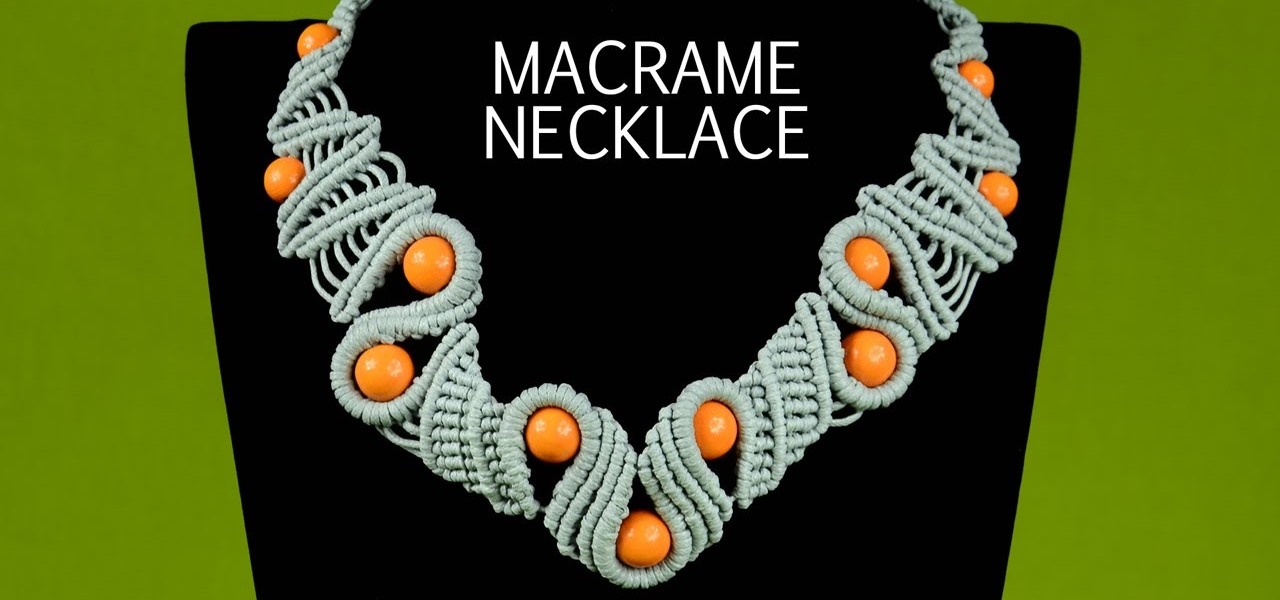
How to make a wavy macrame snake necklace with beads. This necklace looks very interesting and not hard to make, perfect to wear everyday and for any occasion :) This video tutorial is intended for people who know a little bit about macrame.

Looking for an April Fools idea for a prank, Well here's one you can easily pull off. Works best in the mornings which is when most people usually eat cereal. Check out the instructional video for further details.

Sun in the Sea waves - Macrame bracelet tutorial. This bracelet has some macrame design elements - waves, chevron etc, and this is my design. This video tutorial is intended for people who know a little bit about macrame :)

Maybe it is inspiration for some people around here. I have done this in AE and want to share it. Feel Free to download and use or customize it however you want. Download the template here (music not included).

How to make a Macrame Bracelet with a big bead (eye) in the middle. This video tutorial is intended for people who already know how to macrame..

This video will show you an easy way to draw one of the most popular people on YouTube at the moment - Zoella! From drawing out a rough first sketch, all the way through to creating a complete, coloured-in illustration, this video will show you how it's all done. Hope you like it!

For Halloween, most people want to go all out when it comes to decorating their homes with spooky, scary decorations. I myself decided that for this year I would go ahead and try something more realistic, which is why I went to my local thrift store and purchased a stuffed dog. I made sure it looked as realistic as possible for this project.
This method can be used on any kind of scroll saw pattern. Animals, people, inanimate objects, etc. Done on paper and scanned onto my computer only to clean them up and color them in to display. Three part series.

For this prank, you'll be messing with people while they eat. You'll need a fake zombie finger and a bag of their favorite snack. Preferably chips. This one is perfect as a Halloween prank.

Probably SSH is not as clean and fast as other useful tools like netcat, but it has some features which are very useful, and when you'll need them, here's how to behave with that huge amount of computers all over your house.

Welcome back, my hacker novitiates! Every so often, a MAJOR vulnerability appears that makes millions of systems vulnerable to attack. The most recent, named Shellshock, basically leaves every Mac OS X, Linux, and UNIX system on the planet vulnerable. As nearly two-thirds of all web servers on planet Earth run one of these operating systems (primarily Linux), that's a whole lot of systems out there waiting to be harvested.
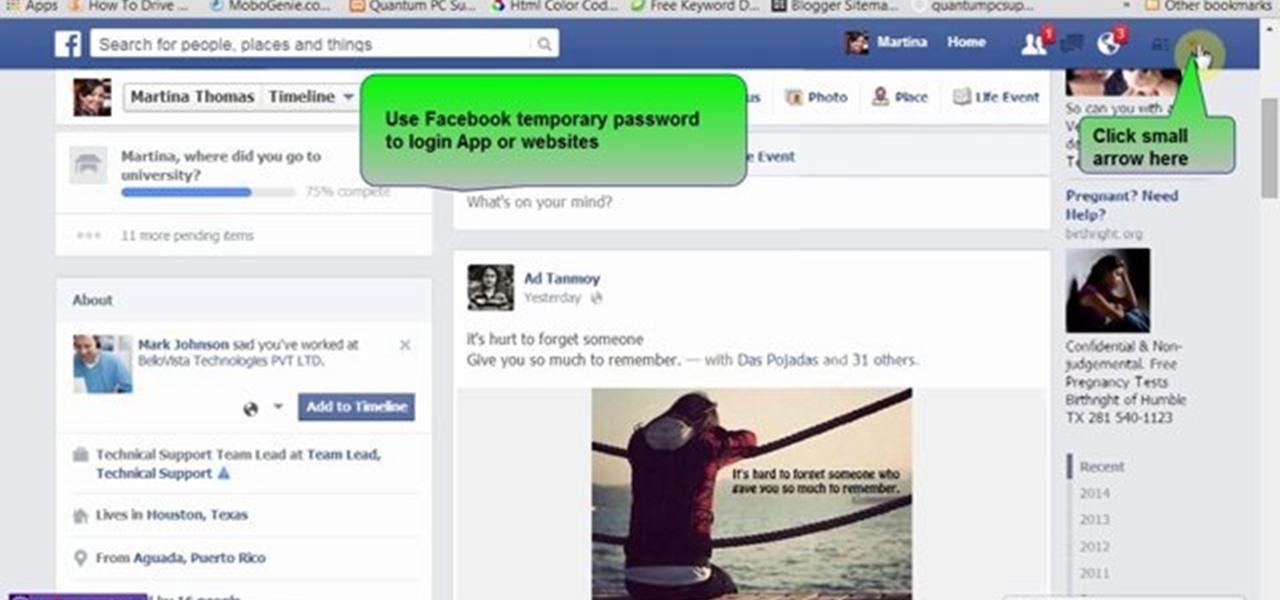
Many people use Facebook login detail to enter different apps or websites. This is somehow dangerous because unethical websites or apps may use your Facebook detail. So to avoid this warning Facebook is generating a temporary password for you. Now you could use this detail to login app or websites. You don't have to use your Facebook original login detail.

This video will show you how to stop spammy notification from apps on Facebook. It is often seen that people unintentionally install many unnecessary apps. Not only from those apps but from few useful app also they get spammy notification. This is irritating and frustrating. So if you want to stop notification from those apps then you must watch this video.

This is a tutorial I made in order to help people have a little more control over their pc and a little more options to change settings.