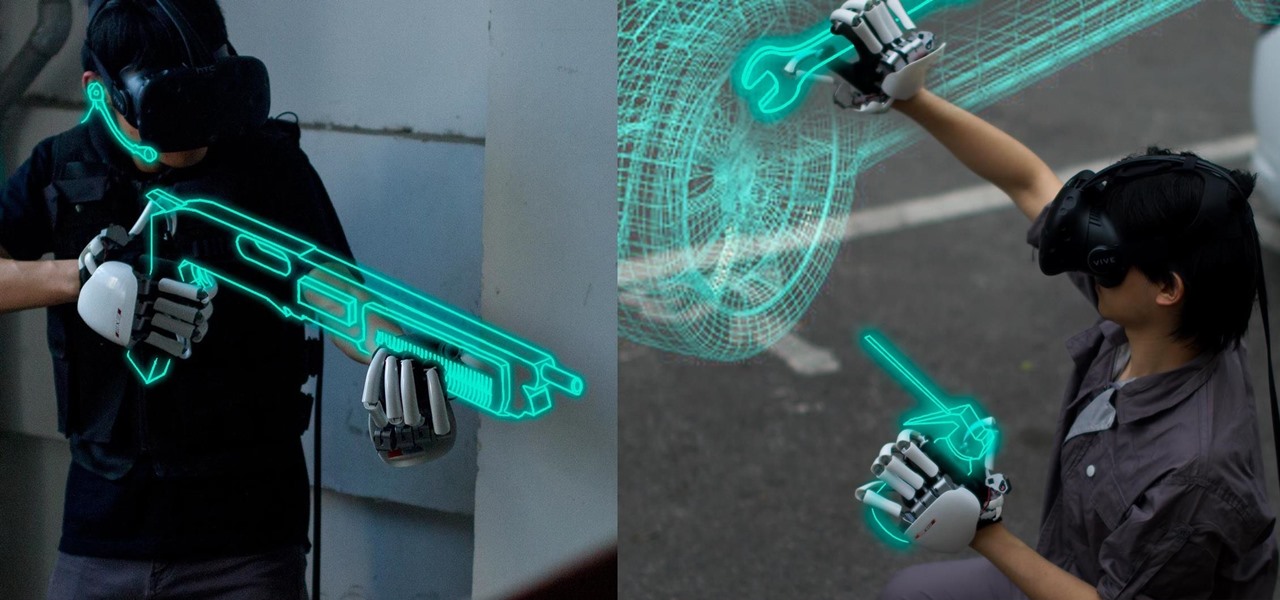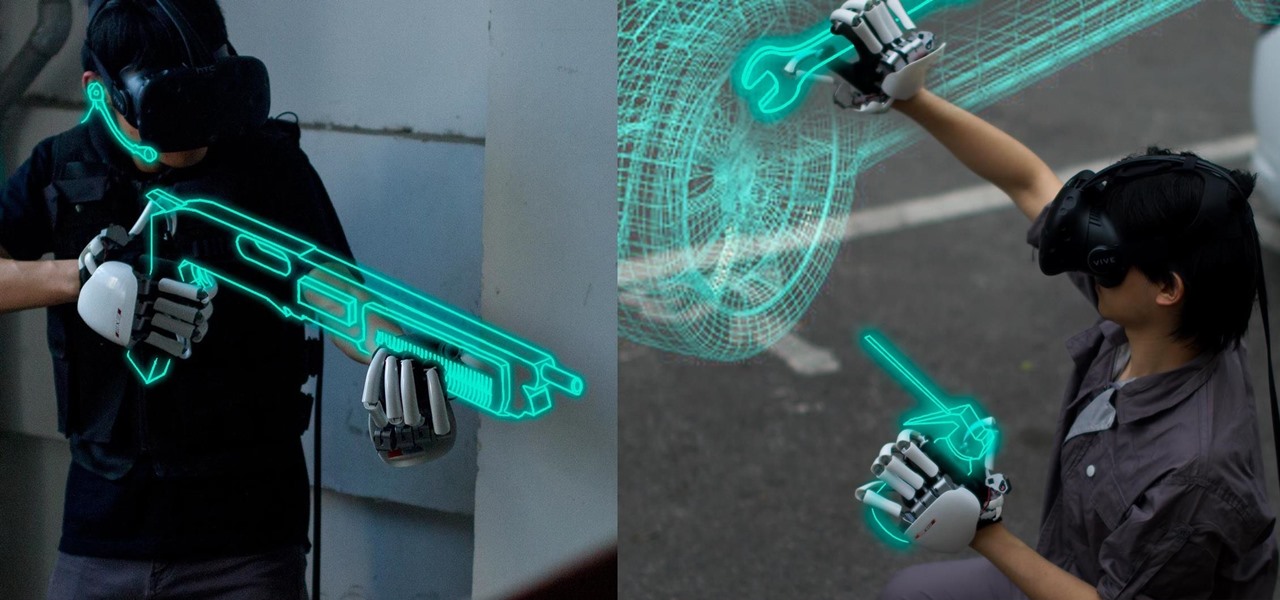
One of the disadvantages of the digital world is that you can't pick it up and touch it. While that can feel like less of a problem in virtual reality, where you're already holding controllers, mixed reality environments—like the one you'd experience in Microsoft's HoloLens—suffer from a lack of physical connection with the digital objects that appear in your real world. Dexmo aims to solve that problem with a relatively intimidating new controller that encompasses your hands.

If you're completely new to Android, you're in for a treat with all of the software tweaks and customization options that your smartphone or tablet offers out of the box. But if you really want to take things to the next level, the ability to mod your device expands exponentially when you're rooted.

Welcome back, my hacker novitiates! There are many ways to hack databases, and most of these techniques require SQL injection (SQLi), which is a way of sending SQL commands back to the database from a web form or other input. In this tutorial, we will use SQL injection to get access to the underlying server. So instead of getting access to the database and its data, we will use the database as an intermediary to gain access to the underlying server.

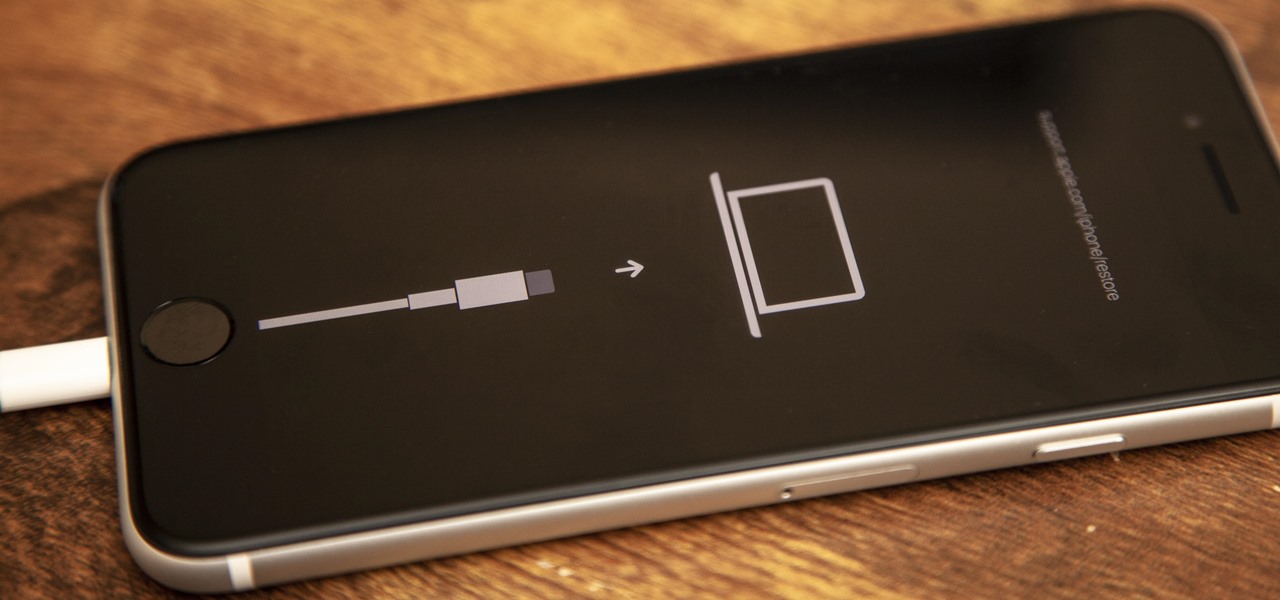
While it seemed like jailbreaking methods were always one update behind the current build, the team over at Pangu have already released a jailbreak tool for iOS 9, and it works up to iOS 9.0.2. It is not available for iOS 9.1 through 9.2 yet, but we will update this guide when they are ready.
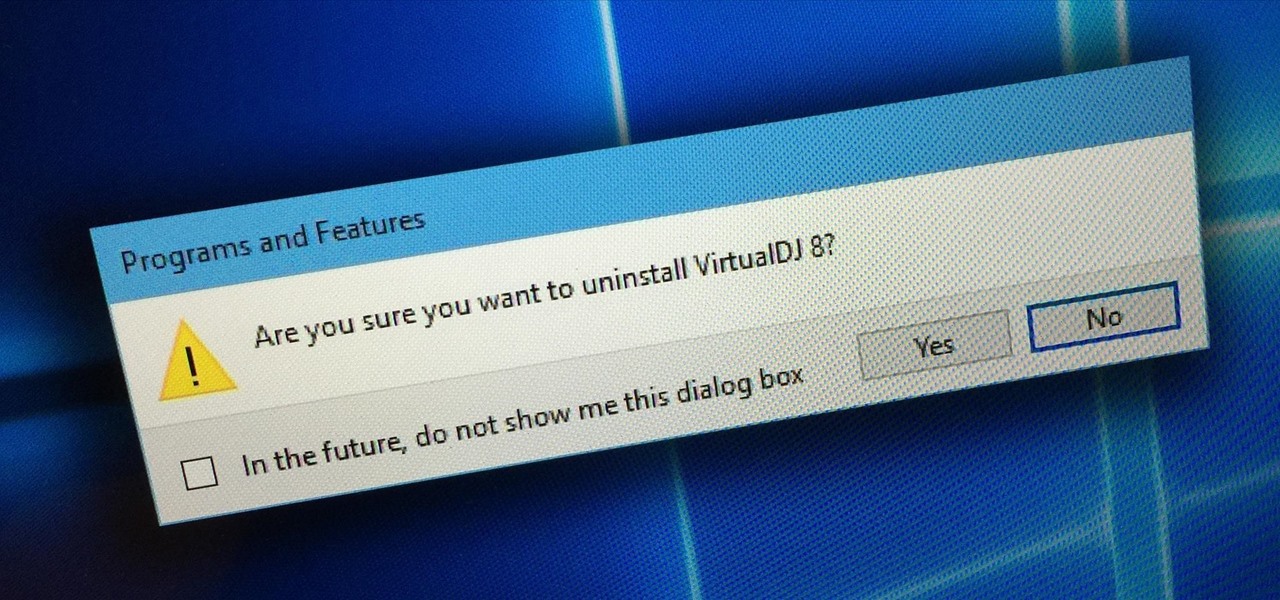
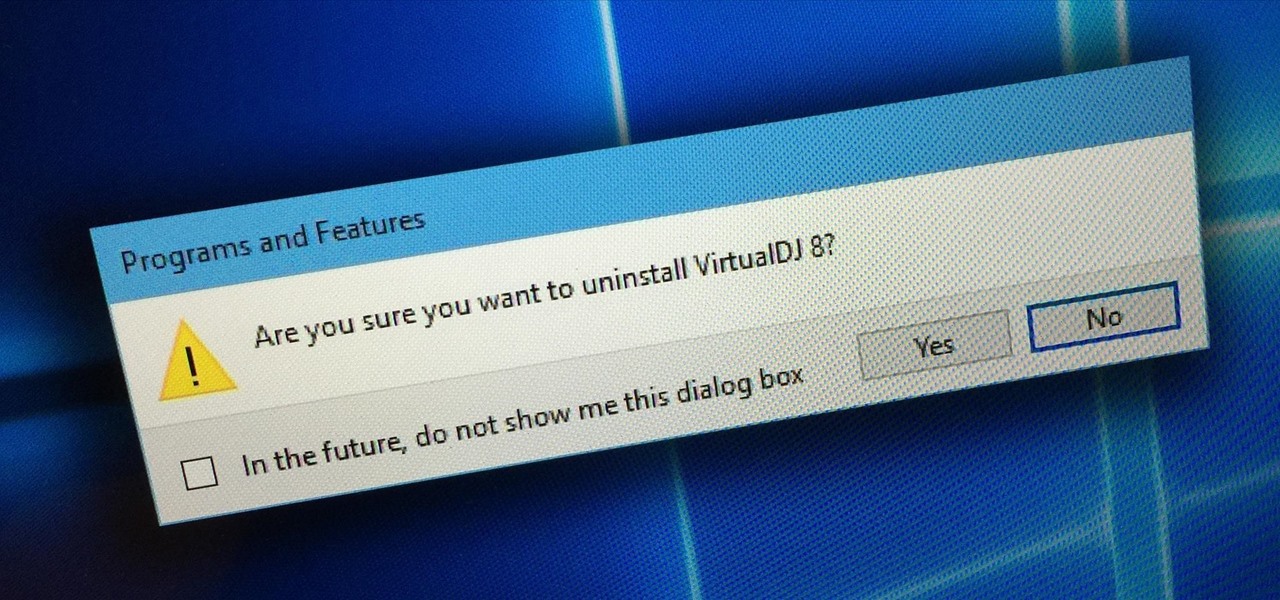
Uninstalling programs in Windows is not the nicest procedure. Some programs bundle a nice uninstaller with them which helps to ease the process. Other programs, mainly those that utilize the Windows Installer technology, begin the uninstall process right away. This can potentially be problematic for users who are trigger-happy with the mouse.

As the developer behind the most popular root methods for hundreds of Android devices, Chainfire knows the ins and outs of Android root procedures. But this doesn't mean he's infallible—occasionally, some of his root utilities can cause minor bugs.

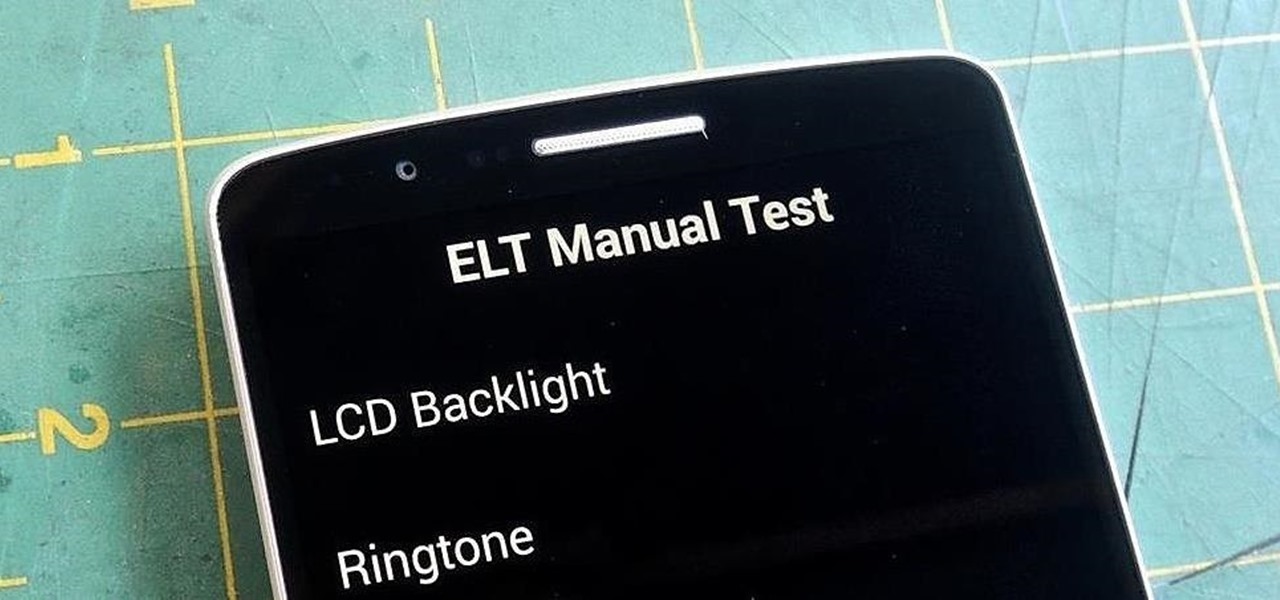
If you notice any issues with your LG G3, pinpointing the culprit can be an arduous task. It could be a hardware issue, a resource-heavy app, or a bloatware-infested operating system.

Okay, so you're rooted and need to return your Nexus 5 to its stock firmware. Whether it's because you need to send your phone in to the manufacturer to fix a defect or you just want to use the device's over-the-air updating feature, unrooting and returning your Nexus 5 back to its fresh-out-of-the-box state is a fairly simple process with the right tools.

The infamous Red Ring of Death plagued the Xbox 360 for years, leading people like me over to the PlayStation 3 console. Now it looks like Sony and its new PlayStation 4 are running into the same problems as Microsoft did.

How to remove and replace a door handle / door knob. How to install a door knob. This is a job that can be done quickly and easily without any special tools (a cordless drill with a Phillips bit or a hand held Phillips Head screw driver). Follow the steps outlined below for a hassle free experience.

The allure of Snapchat is that all pictures and videos sent through the app vanish a few seconds after being sent. They're completely obliterated not only from the phone, but from the Snapchat server, as well. The popularity of the application has even incited Facebook to release its own real-time picture and video messaging application, aptly titled Poke. One of the biggest criticisms (besides the wave of recent security issues) of Snapchat is that even though the messages self destruct and ...

This video shows the viewer how to take part in a ‘scramble’ golf tournament. This type of event is typically for amateurs and is essentially played as a team sport, this is unusual for golf. The general principal is that everyone plays the first drive. The team then decides which drive was the best. They then move all the balls to this point and all play as if they hit that shot. They repeat the same procedure until one of the balls has been putted. This method allows amateurs to get a reaso...

Mr. G teaches us how to make bubbles from a CD in this episode of "Do Try This at Home". You will need: a CD, screwdriver, and lighter or candle. Procedure: Use the screwdriver to scrape the aluminum coating from the CD until you get a clear plastic (polycarbonate). Heat an area underneath the CD slowly until the plastic is melted. Blow on the heated portion of the CD until you get a bubble. You may detach the bubble or leave the it on the CD. Heat and blow other portions of the CD to get new...

This video teaches us the procedure of speeding up gameplay by opening NAT on your XBox 360. Firstly, we will open NAT for XBox 360. We must access the setup page of the router in order to open the NAT for XBox 360. Open the command prompt and type 'ipconfig'. Note the default gateway and type it into the Internet Explorer. Put the username and password. The username is 'admin' without the quotes. Click on the administration tab in the resultant window. If the UPnP is set to 'Disable', set it...

The video is a demonstration of how to get your nose pierced by yourself at home. The things you are going to need for this are a sterile needle, rubbing alcohol, cotton swab, rubber gloves, a nose ring, ice cubes, eraser and of course pain tolerance. The lady also tips you to first numb your nose with ice cubes if you wish and it helps a lot. Then she asks you to put on the gloves, take the cotton swab and put some rubbing alcohol on it and then clean the inside and outside area where you ar...

This video shows how to fix an iPod which is stuck in a loop between battery warning to the apple logo. You will learn how to fix your iPod by watching this video. The procedure used in this video is to sync the iPod to the computer. Lock the iPod in disconnect mode so you can let it charge. You then wait for it to charge. You then tell I-tunes to restore the iPod to factory settings. If these steps don't work you need to replace the battery.

Okay, so this doesn't exactly teach you how to audit as a Scientologist... but I think it is the closest to an explanation we are going to get. So, listen up & try to learn.

Watch this video to learn how to make a tasty snack made from simple ingredients. Peel potatoes; should they have any sprouts remove them. Cut each potato into 2 or 3 pieces. Chop onion finely. Cut horizontally several times; repeat procedure vertically. Chop cabbage into fine, narrow pieces. Place cut potatoes into a pot full of water while adding some salt. When water starts to boil reduce heat a bit. Check potatoes for tenderness and at that stage remove water. Replace pot onto burner. Usi...

Ever wonder how to make futomaki sushi and California rolls? Cut ingredients for filling. Remove both ends of cucumber. Make 6 cucumber sticks. Cut avocado in ½, twist, remove seed. Remove peel. Slice into thin pieces. Cut shiitake mushrooms into fine strips. Cut barbequed eel lengthwise. Using 2 eggs seasoned with salt and sugar, make egg omelet. Heat pan; add a little oil. Pour 1/3 egg mixture into the pan and when almost cooked gather on far end of the pan. Re-oil pan. Add 1/3 mixture of e...

If your new 2020 iPhone SE is frozen, unresponsive, or won't load the system, and a standard power down and up procedure didn't work, there are few more things you can try. Force-restarting the device may do the trick, recovery mode is a last-ditch option, and DFU mode is your fail-safe.

You may have recently seen a plethora of Instagram users, including celebrities and politicians, sharing a screenshot declaring that the platform will implement a new "rule" where it would own and could use your photos and videos however it wishes. The screenshots are part of an internet hoax, one that's been around in one way or another since 2012, but what can Instagram actually do with your media?

With a root bounty of over $18,000 up for the taking, developers were highly motivated to get the AT&T and Verizon Wireless variants of the Samsung Galaxy S5 rooted. Legendary hacker George Hotz, aka Geohot, has won the race and can now step up to claim his prize.

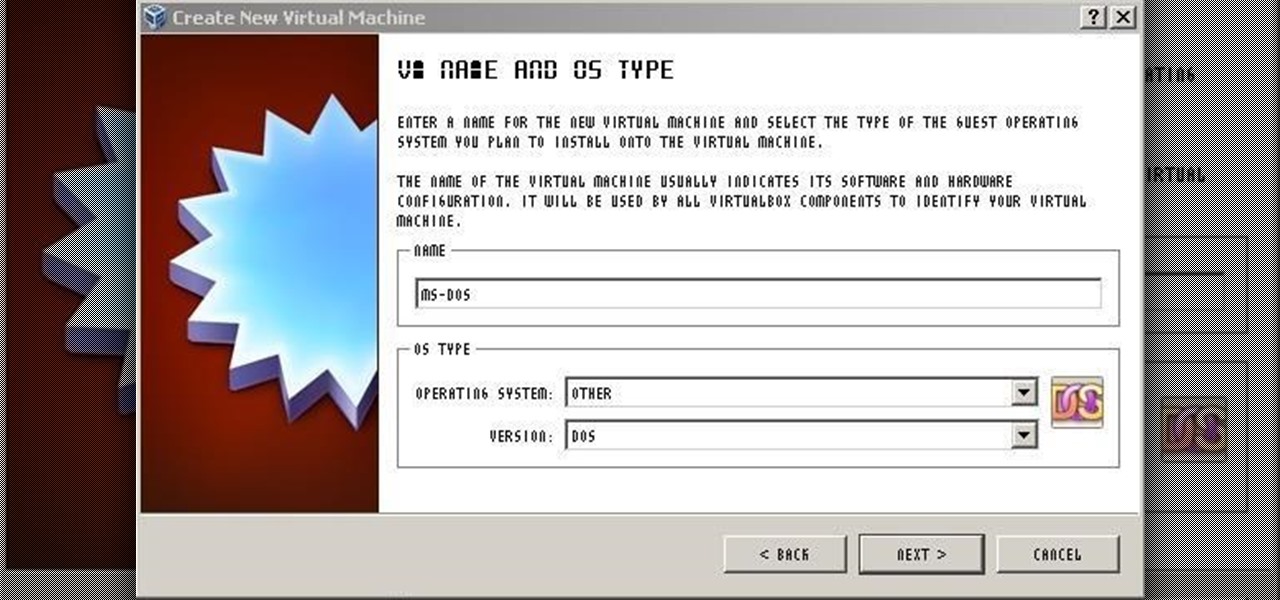
For those needing to replace old controller hardware on cutting mills, those into native retro gaming, or for those who want to see what all the fuss was about in the 1980's, or for those who just want a play with old but great technology, this tutorial shows you step-by-step processing getting the breakthrough desktop operating system running on the latest greatest hardware.

This particular video series covers what is called the natural facelift. It is essentially an intense facial that is more involved and has agents that target those trouble areas where wrinkles tend to occur more often such as around the eyes and mouth. This is a fantastic alternative to the pain and cost of surgery. Instead of weeks of recovery you have no recovery time and see effects almost immediately. It also removes the risks of a surgical procedure and is very relaxing as well. Check ou...

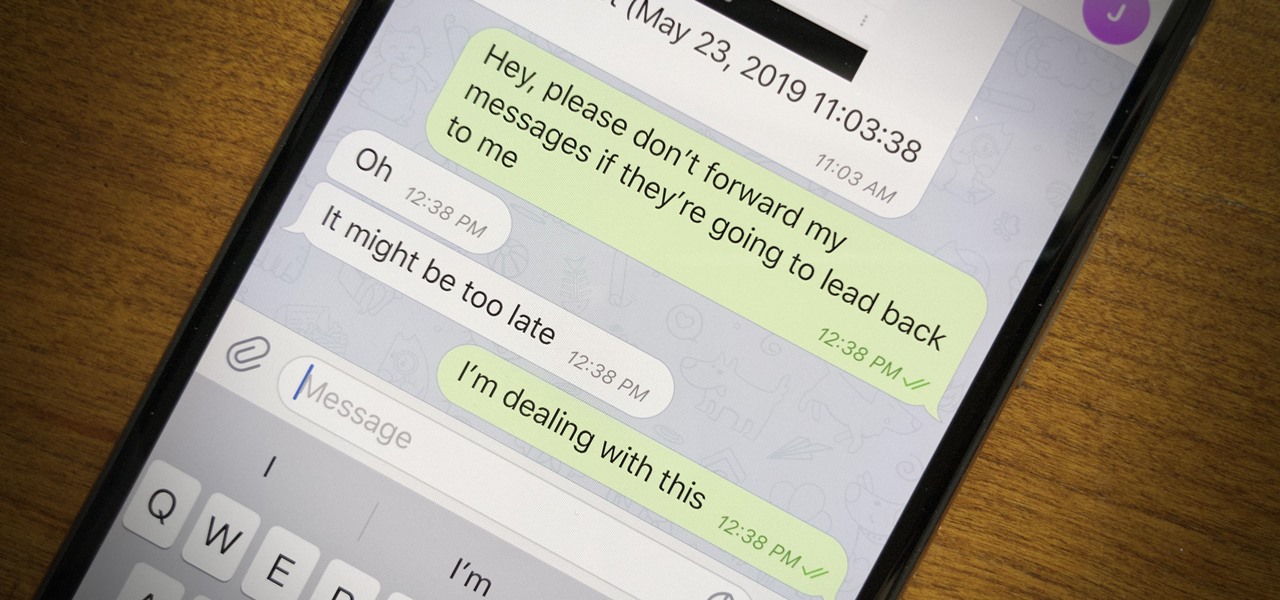
Forwarding messages is a helpful Telegram feature that makes it easy to share funny and entertaining content with other contacts. However, for the privacy-centric, forwarding poses an issue, as messages of yours that are delivered elsewhere carry a tag back to your account. Luckily, you can make your messages anonymous, so anyone receiving messages of yours that are forwarded won't be able to see you originally sent the message.

OnePlus pulled out almost all the stops with their latest flagship, but there are a few areas where the phone falls just short of perfect. The single bottom-firing speaker leaves a lot to be desired, for instance, but thanks to the awesome development community for the OnePlus 6, you can already give your phone true stereo speakers with a software mod.

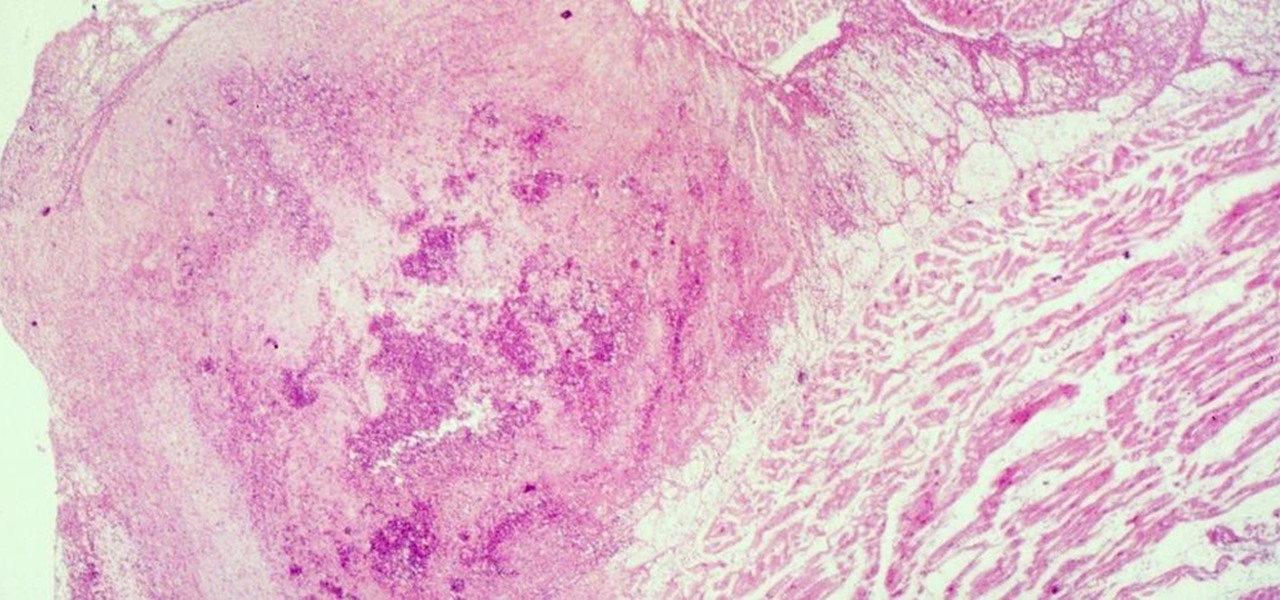
Four million Americans misused prescription opioid painkillers in 2014. Those who do are 40 times more likely to inject heroin or other drugs than other people. Now, the Centers for Disease Control and Prevention (CDC) are blaming that misuse for a 12-fold increase in endocarditis, an infection of the heart valves.

Marketing and healthcare, two of the leading industries in the adoption of augmented reality, continue to demonstrate applications for the technology in their businesses. Meanwhile, improvements to augmented reality devices are just around the corner with new developments from two display makers.

Our canine best friends could spread our bacterial worst nightmare, according to a recent study. The problem with drug-resistant bacteria is well known. Overused, poorly used, and naturally adaptive bacteria clearly have us outnumbered. As science drives hard to find alternative drugs, therapies, and options to treat increasingly resistant infections, humans are treading water, hoping our drugs of last resort work until we figure out better strategies.

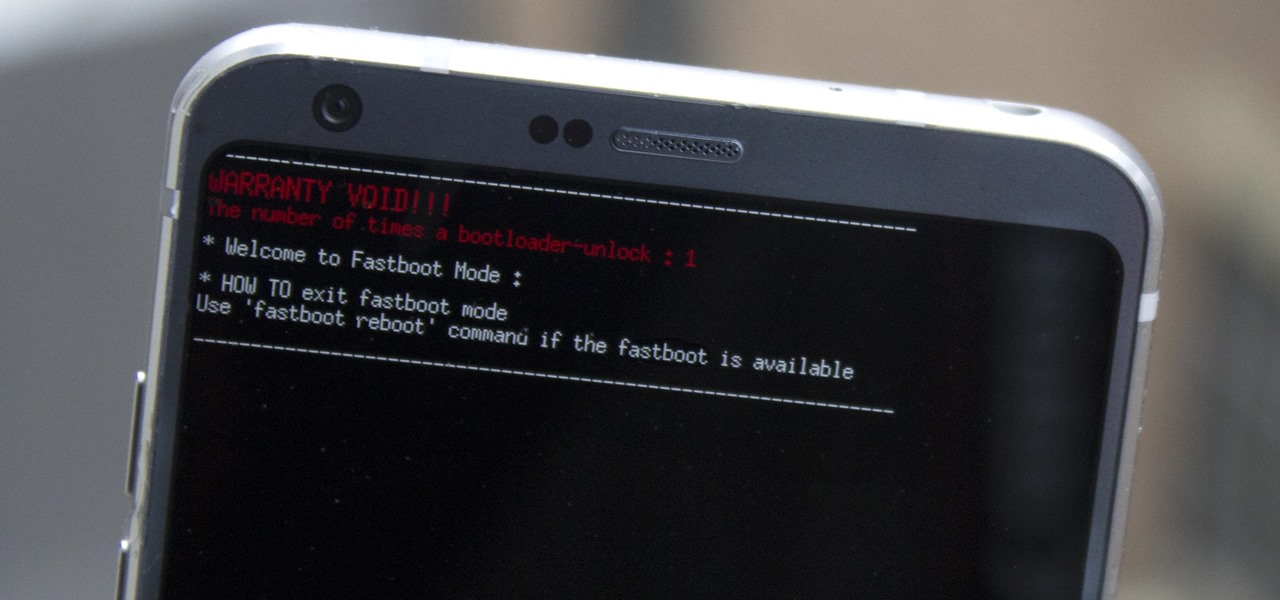
Preorders for the LG G6 have all been fulfilled, and the phone has been up for grabs at local cell phone providers for three weeks now. However, not every LG G6 was created and released equally. The T-Mobile variant of the LG G6 features an unlockable bootloader, while most other North American variants come with a tightly locked down bootloader, which effectively limits the full potential of your brand new fairly expensive phone.

In this Tuesday's Brief Reality report, there's a trio of stories from the healthcare world where augmented reality is helping out with surgical microscopes, asthma treatment, and other diagnostic and treatment tools. There's also something for all of you AR/VR storytellers out there.

US blood banks have assured the American public that they have the tools to prevent a Zika contamination, despite the rapid spread of the disease.

Obstetric tetanus in an unvaccinated Amish woman after a home birth has emphasized the need for preventative healthcare.

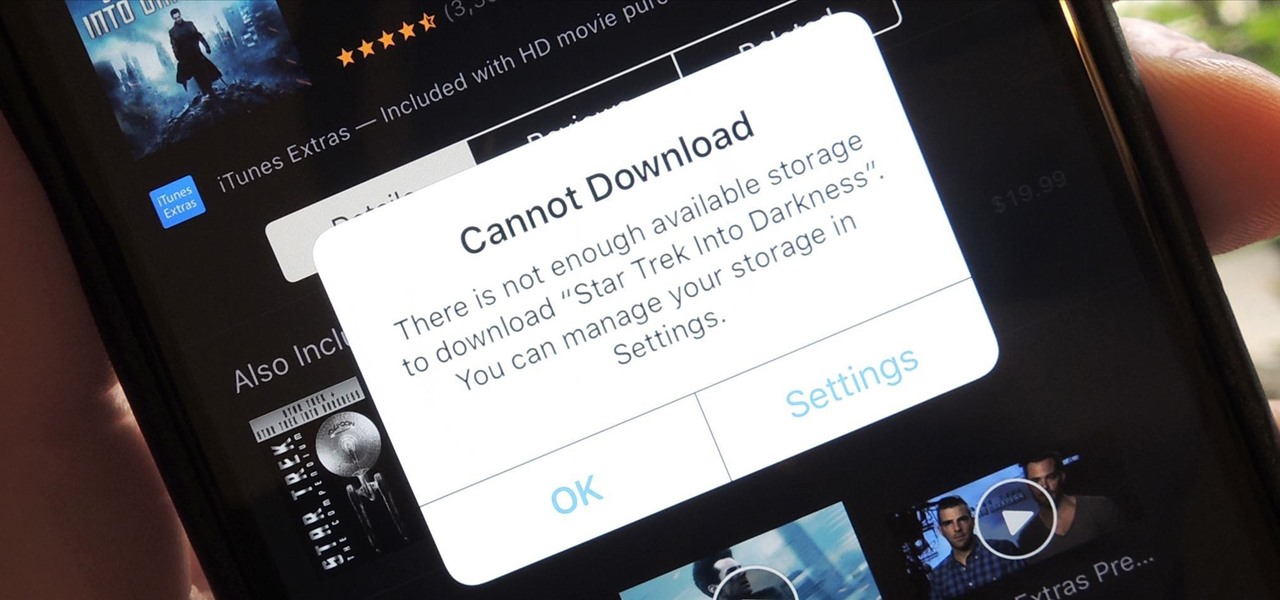
Clearing storage space is a constant concern for people with iPhones, especially since they don't come with expandable storage, limit the amount of free iCloud storage, and still, unfathomably, produce units with only 16 GB of space. Thankfully, Reddit user eavesdroppingyou shared this quick and easy tip you can use to wipe unnecessary files from your phone and potentially free up gigabytes worth of storage.

Hey guys I am starting this Series because I thought there was a lack of post about Hacking from Android.

Hello again, folks! I'm back with another (final) guide on runtime crypters which is an extension on my previous runtime crypter guide. If you have not read it yet, I highly recommend that you do since the fundamental theory of the PE format. Again, this will be a Windows-specific guide, so I'll repeat this: If you're a hater and cringe at the slightest sound of Microsoft's grotesque baby, feel free to close this tab, delete your history, exit your browser, pour some oil onto your machine and...

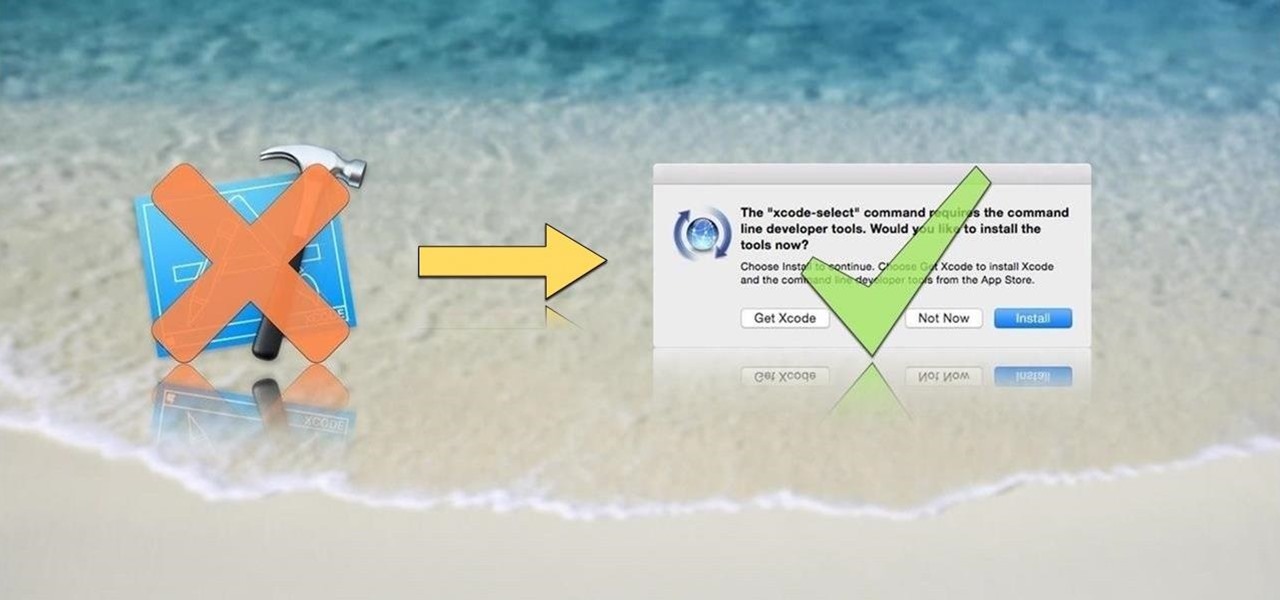
OS X is built upon a UNIX foundation, which grants you access to the benefits that UNIX offers, including the standard toolkit (make, gcc, clang, git, perl, svn, size, strings, id, and a lot more) via the command line developer tools, which are an essential if you're a developer. Aside from developers, the command line tools can offer benefits to normal users as well, like the ability to purge RAM for better performance.

Hello readers, in this tutorial, we will be discussing how to perform file operations such as reading and writing.

Hearthstone is a collectible card game by world-class developer Blizzard Entertainment. It has taken an entire generation of casual and professional gamers alike by storm. So many people play it, chances are you've already sunk some money into it. So, if you're going to pay a little anyway, you may as well get a discount.

This is a collection of various guides and tools available on the internet. Instead of searching for 1 you can easily find whaht your looking for here.