When it comes to webcams these days, most people are using their laptops over desktops. The cameras are centered, integrated, and require no configuring. They're a cinch and usually have great resolution. So, then what do we do with all of those old wired desktop webcams that we've accrued over the years? Even if you still use an external USB one, chances are you're not using it daily, so why not come up with a better use for it?

Here's something fun for the Null Byte community to do—a coding competition! This week, I wanted to get everyone involved by offering you all a nice library of possible program types to choose from and try to code. At the end of this competition, all of the submitted programs will be reviewed by the community and myself. The coder that receives the most votes will be dubbed THE BEST.

Lost the product key for your game? If you have to reinstall the game and don't have that key anymore, you're out of luck, especially if you didn't "buy" the game. But never be in fear of losing product keys again with today's Null Byte, where we'll be practicing a little bit of mind-kung fu.

We'd like this to be one of the last HTS mission announcements, at least for now. As soon as Null Byte finds a server to play with (anyone want to donate one?), we are going to start doing root the box competitions, which is like king of the hill, except you have to hack a server and maintain access. Each server will have numerous known security holes. But for now, back to the normal flow of things...

Lock picking is defined by locksmiths as "the art of opening a lock without the key". There's many ways to accomplish this, but I'm specifically interested in using a lock pick set. Since locks vary in shapes and size, it's better to stick with just one kind of lock at first. Most locks are based on fairly similar concepts, so sharing methods across locks is possible.

I'm sure we've all heard about MSN and Yahoo! Messenger, right? They can be useful, but the setup can be quite time consuming for those who need to use it just once or twice—and the privacy statements are a real bother. For example, we must provide our real details. You could use Fake Name Generator, but if you get caught, you will have your account suspended. I don't have a law degree, but to my understanding the United States recently passed legislation that gives the authorities the power ...

Technology in computers these days are very favorable to the semi-knowledgeable hacker. We have TOR for anonymity online, we have SSDs to protect and securely delete our data—we can even boot an OS from a thumb drive or SD card. With a little tunneling and MAC spoofing, a decent hacker can easily go undetected and even make it look like someone else did the hack job.

We're aiming for this to be one of the last HTS mission announcements, at least for now. As soon as Null Byte finds a server to play with, we are going to start doing root the box competitions, which is like king of the hill, except you have to hack a server and maintain access. Each server will have numerous known security holes. But, for now, back to the normal flow of things...

The community tore up the first realistic mission last week. You've applied the techniques learned in the basic missions to a real scenario, so I'm pretty content. The realistic missions are where the learning gets intense and where we can apply real knowledge to extremely realistic situations. We will also be continuing the normal Python coding and hacking sessions. These sessions are created to bring our community together, to learn from each other, and grow together. Everyone is welcome, f...

Following the first part in this series on advanced cracking techniques, we are going to go over how we can intelligently crack passwords using the old-fashioned bruteforce method. These unique cracking techniques aren't widely used, because most crackers are Script Kiddies who have no idea what the concepts are behind cracking passwords, thus, word won't get around too quickly.

How did it happen? How did your ultra-secure WPA password on your wireless network get broken into? Well, you might have just found yourself at the mercy of a cracker.

Here's a nasty little Null Byte. An open redirect vulnerability was found in both Facebook and Google that could allow hackers to steal user credentials via phishing. This also potentially allows redirects to malicious sites that exploit other vulnerabilities in your OS or browser. This could even get your computer flooded with spam, and these holes have been known about for over a month.

I'm pretty sure that it's a universal dream for everyone in the world to retire early. Who wants to to be stuck with the rest of the country and retire when you're almost 70 years old? You heard me right, 70! Most people can't go out and do the things they love to do by the time they're 70, unless they've been practicing good health and exercise their entire life.

Community byters, it's time to get serious. We are finally moving on to the realistic missions in HackThisSite. This is where the learning gets intense and where we can apply real knowledge to extremely realistic situations. We will also be continuing the normal Python coding and hacking sessions. These sessions are created to bring our community together, to learn from each other, and grow together. Everyone is welcome, from novice programmers to aspiring hackers.

VNC is a great protocol that you can use on Windows and Linux machines to remotely control computers. This is useful if you need to control your computer when away from home, help your grandma check her email, or help a client with a disk cleanup. VNC is secure in the sense that it requires authentication in order to make the connection, but after that, the data is sent over the internet unencrypted. This means that an attacker could sniff your traffic and snoop everything that's going on. Th...

Only so much data can be passed through the network and to your computer's networking interfaces. This is limited by the amount of bandwidth you have. The more bandwidth you have, the faster your network connections will be. Not only this, but your transfers will be more parallel and distributed so that all of your speed isn't taken up by one transfer. When all of your bandwidth is sapped and unable to be used, this is called a denial of service, or a DOS.

If you've ever heard software piracy terminology being discussed, I'm sure the term KeyGens came up. KeyGens is short for key generator, which is a program that exploits algorithmic faults in software by generating software license keys that appear to be genuine. Normally used as a technique to protect the source code software and prevent piracy, a key generator exploits the key algorithm to effectively nullify the need for any software licenses. For example, we must try to find patterns in t...

If you've ever wondered how software pirates can take software and crack it time and time again, even with security in place, this small series is for you. Even with today's most advanced methods of defeating piracy in place, it is still relatively easy to crack almost any program in the world. This is mainly due to computer processes' ability to be completely manipulated by an assembly debugger. Using this, you can completely bypass the registration process by making it skip the application'...

With the purchase of my latest computer, installing Linux turned into a nightmare from Hell. The graphics drivers are probably the biggest issue that anyone with a newer computer will run into when installing Linux. AMD and NVIDIA are the dominant ones on the market, both of which have awful support.

Paying for web hosting isn't ideal in most situations. If you have your own website, hosting it yourself is very acceptable and easy to do, assuming your internet bandwidth permits. Most people want to run a personal site, nothing crazy, so hosting from home on low-bandwidth internet is actually a better solution in most cases.

Note: This shower is only visible in the Northern Hemisphere. The Quadrantid meteor shower is one of my personal favorites, mainly because of the amount of meteors it produces. You can sight more than 100 meteors per hour- that's more than 1 meter per minute. Even though that doesn't sound like much, it will make your observing experience much more exciting. The peak is short, typically lasting no more than an hour or so. It is more easily observed on the fourth, with its peak at 1:00 AM EST.

Having an SSH or Secure SHell to tunnel your traffic through is something we have talked about many times at Null Byte. As we know, it allows us to securely route and encrypt our traffic through a remote server, effectively anonymizing us and protecting our traffic from all forms of analysis—simultaneously. We have gone over how to make a home SSH tunnel. However, the question has come up, "How can I get an SSH tunnel to somewhere other than my computer?" This would be useful in a situation w...

Although most religions have inspired a variety of art, Buddhism seems to have a special relationship with the arts. Something about the endless circle of birth and rebirth seems to intrigue the minds of artists. Of course even if the art is not directly related to Buddhism, the Buddha has always been a fan of art. The Buddha has been quoted several times speaking about art, and most of his sayings are truly profound:

"Google+ is dead." How many times have you read that in the past few weeks? It seems like I can't get away from this notion that Google+, as a social network, is a total failure. Don't feel too sorry for them, though. +Bradley Horowitz isn't worried. In an interview with VentureBeat, he explains, “Six months from now, it will become increasingly apparent what we’re doing with Google+. It will be revealed less in what we say and more in the product launches we reveal week by week.” Indeed, som...

This article will teach you how to make an iPod video projector for about $6 (depending on what materials you have) that works pretty well. First off, you need to gather your materials. I had everything except the magnifying glass, which I bought for $3.

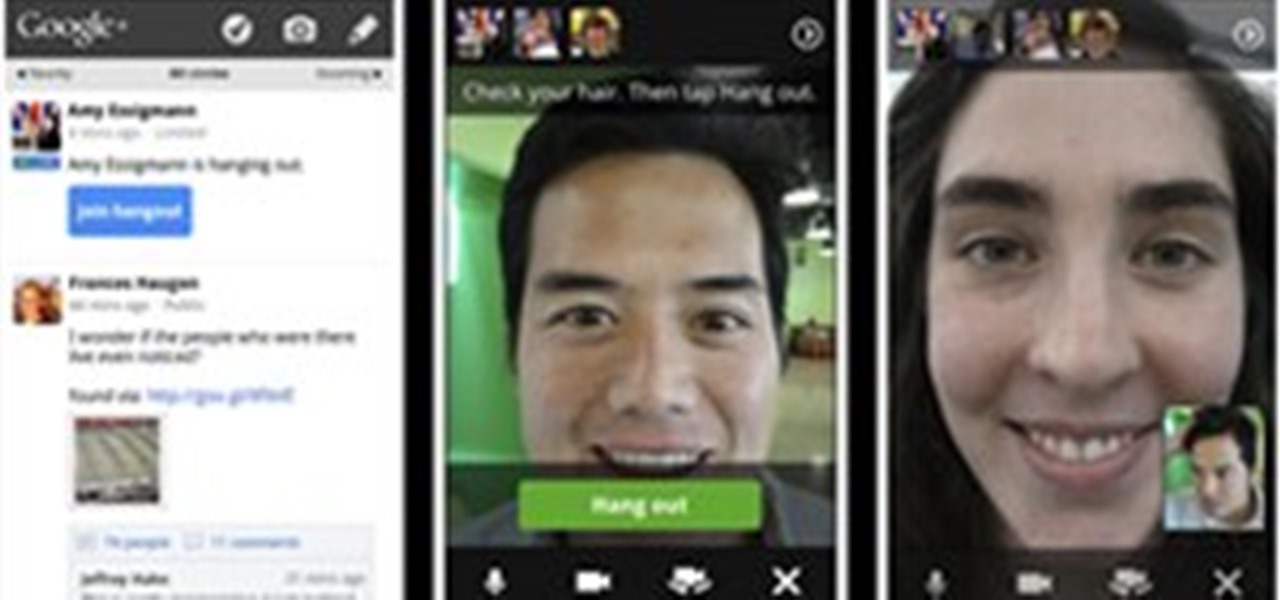
It may not seem like it, but it's been less than 90 days since Google+ was introduced to the world. Since then, we've seen many great features that have made Google+ one of the most attractive social networks around. Today, we've received even better news: major improvements and feature updates that are truly innovative.

This week has been pretty exciting for both Facebook and Google. Facebook announced a slew of features that seem on the surface to copy Google+. For Google+ users, a lot of improvements, updates and features were implemented, and they're seeing a lot more overall integration with their Google account.

In a previous article where I suggested 104 photographers to follow on Google+, I received a lot of criticism because over 90% of the listed photographers were men. While women are currently not a majority on Google+, they are a definite presence, and they are active. Today, I highlight the best female photographers I've found on Google+ so far. This time I'm taking a slightly different approach. Since the best way to get to know photographers is through their work, I've included one photo fo...

It's been an eventful week for Google+. Facebook decided to up its game and start rolling out several major updates intended to address privacy concerns. We got a glimpse into the future of Google+ via an insightful discussion between +Bradley Horowitz and +Tim O'Reilly. And Google decided to integrate the +1 button more fully with Google+ by allowing users to share directly from the +1 button. That's not all, though—scroll down for more news & updates that occurred in the past week.

+Tom Anderson of MySpace has been very active on Google+ over the first week, and he's not shy with his thoughts on the evolution of the industry he once owned. Here's his take on this morning's Facebook announcement and Mark Zuckerberg's response when asked about Google+.

Do you ever really know someone? I mean really really? Super really? Sometimes we can talk and be with people normally for years and then bam: five people dead, house on fire, dog missing. All the while people shake their heads and regret that if they had just put the little clues together all of this could have been averted.

Gears of War fans around the world are excited (possibly drooling) over the upcoming release of the third installment in the series, Gears of War 3. There's a lot of hype about the game and its new features, which includes a 4-player co-op mode and a slew of new female characters. But there's one problem—it doesn't come out until September 20th. But for a lucky circle of gamers, the Multiplayer Beta just opened up today.

Welcome back to the two-part series of Ten foods to eat for clear, acne-free skin. Check out part 1 here.

Today Farmville updated some of the user interfaces for crafting and farmers market! Changes

Good news. Facebook has finally listened. After severe criticism for ignoring the world's privacy norms, Facebook will finally release simplistic, user-friendly privacy settings soon.

Get a little perspective on FarmVille hysteria, via FarmVille World, written by tenebrism: Did you know it only took five weeks to make FarmVille? That it currently has over 80,000,000 users? That FarmVille farmers outnumber real farmers in the United States by a ration of 80 to 1?

Did you know it only took five weeks to make FarmVille? That it currently has over 80,000,000 users? That FarmVille farmers outnumber real farmers in the United States by a ration of 80 to 1?

Ever typed out a long message on your phone only to find several errors after you hit send? Proofreading would fix this, but anyone who's spent time trying to edit on a smartphone knows how difficult it is. Thankfully, Gboard makes this task easier.

To use a circular embroidery guide on a sewing machine, loosen screw at back of the presser foot ankle just enough to insert a circular embroidery guide from left. The radius of the circle is determined by placement of the guide in the holder. Secure the guide with a screw. Place the stabilizer under fabric. Mark the center point on fabric with marking pen. Align the center of the fabric with the rubber point of the circular embroidery guide. Put a flat tack under the fabric and up through th...

Outside the realm of politics, where opposing sides are quite passionate and quite disagreeable, there are few areas in our society quite as divisive as Twitter. People who like Twitter love Twitter and are relentless in trying to co-opt the people they know into joining (this is both altruistic and an unsubtle attempt to boost followers).