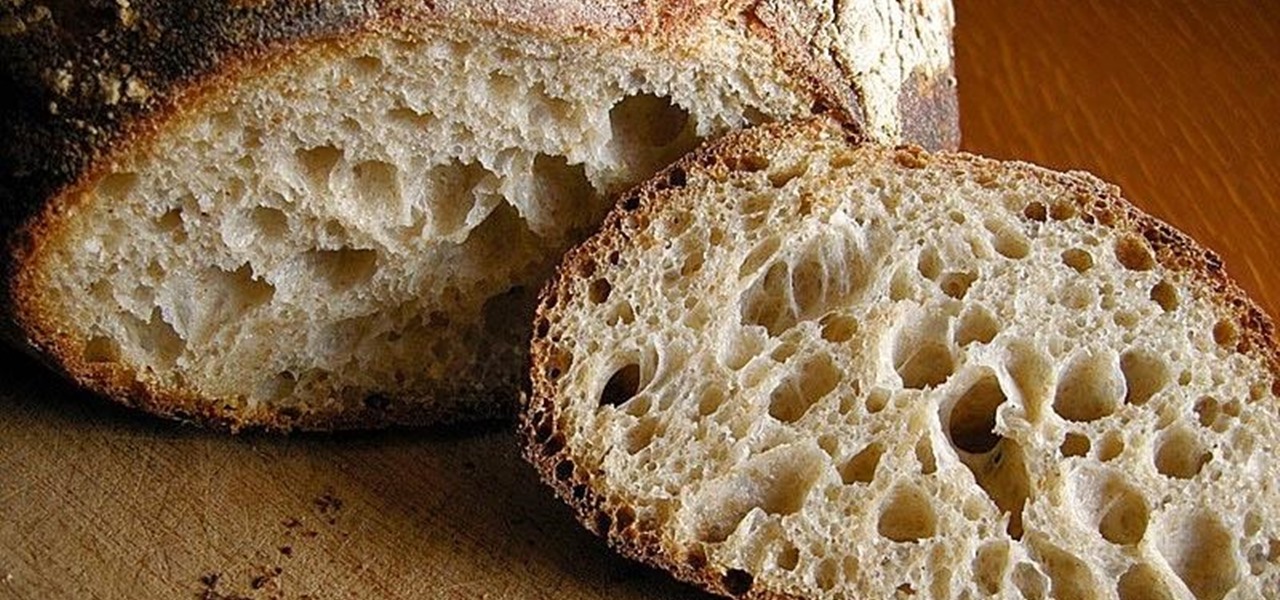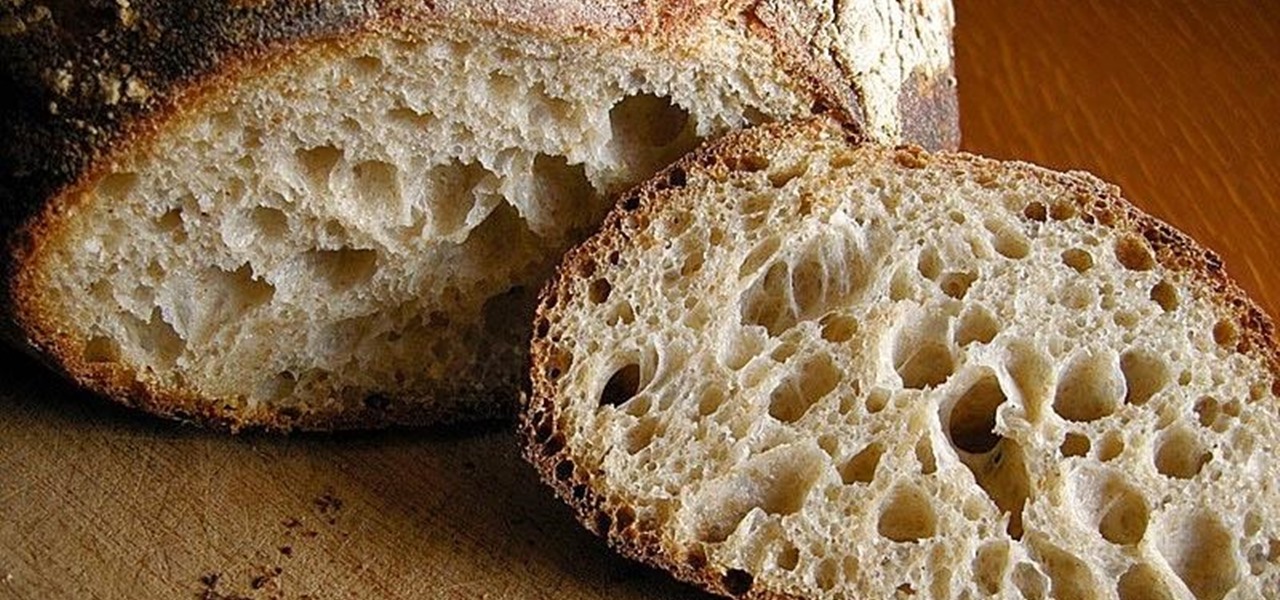
What is gluten, why do some people think it is pure culinary evil, and why are there more and more products devoted to being free of this mysterious substance? Here's what one person thinks: What Is Gluten Really?

Is the augmented reality magic fading down in Plantation, Florida? That's the first question some may be asking following a casual revelation over the weekend that Magic Leap, the maker of the Magic Leap One, has assigned much of its patent portfolio over to JP Morgan Chase as collateral.

Just as the NCAA men's basketball tournament is set to start later this month, USA Today has decided to trot out an augmented reality mini-basketball game to promote its bracket competition.

In response to Apple's implementation of LiDAR sensors in iPad Pro and iPhone 12 Pro models, Google is looking to leverage the dual-camera setups in recent flagship devices as depth-sensing components.

The PlayStation 4 has been around since 2013 and has brought with it countless game releases since then. One thing that hasn't changed, though, is the strict device restrictions on the PS4 Remote Play feature for streaming your games. The capability has always been there, but you still had to have an iPhone or Sony smartphone to get the best experience possible — until now.

Web application vulnerabilities are one of the most crucial points of consideration in any penetration test or security evaluation. While some security areas require a home network or computer for testing, creating a test website to learn web app security requires a slightly different approach. For a safe environment to learn about web app hacking, the OWASP Juice Shop can help.

Bluetooth Low Energy (BLE) is the de facto wireless protocol choice by many wearables developers, and much of the emerging internet of things (IoT) market. Thanks to it's near ubiquity in modern smartphones, tablets, and computers, BLE represents a large and frequently insecure attack surface. This surface can now be mapped with the use of Blue Hydra.

Social engineering makes headlines because human behavior is often the weakest link of even well-defended targets. Automated social engineering tools can help reclusive hackers touch these techniques, but the study of how to hack human interactions in person is often ignored. Today, we will examine how to use subtle, hard to detect persuasion techniques to compromise a human target.

In a world increasingly regulated by computers, bugs are like real-life cheat codes. They give you the power to break the rules and do good or bad without ever leaving your seat. And government agencies around the world are discovering and stockpiling unreported bugs as cyberweapons to use against anybody they see fit.

Food labeling is a tricky beast. For instance, when I read the words "cage-free" on an egg carton, I think it means that happy chickens frolic in a sunlit meadow all the livelong day until they're gently herded into a clean, sweet-smelling coop to lay a few dozen eggs—which I can purchase for a reasonable price, of course.

Unless you're vegan or lactose intolerant, butter is an indispensible ingredient. However, butter is no one-trick pony. It can take many forms that make it even more versatile and useful in the kitchen. Clarified butter has many advantages over regular butter—but there are certain cases where you shouldn't use it. More on that later.

Chances are that you've been using your microwave just to nuke leftovers, but they can do so much more than heat up last night's dinner—microwaves can help you peel garlic more quickly, get more juice out of lemons, disinfect your kitchen, dry out herbs, give beauty products new life, cause exciting explosions, and even arc weld.

April Fool's Day, aka National Screw with Your Friends Day, is finally here. You can always pull a conventional prank, like strategically placing a whoopee cushion on your mom's chair, but that joke has been exhausted generations before smartphones were around. We live in a day and age where smack cam is the new level of pranking, so it's time to step your game up, novices.

Use this safe and easy technique next time you need to replace a shattered light bulb. You Will Need

"Unfortunately, no one can be told what the matrix is, you have to see it for yourself." That's the line just before Morpheus gives Thomas Anderson (aka Neo) the red pill, finally opening his eyes to the tapestry of code that has veiled his eyes for his entire life.

Smartphone videos get better and better each year. Seven or eight years ago, who would have thought iPhone and Android phones could support 4K video recording. Some phones can even shoot slow-motion at 960 fps. But no matter the resolution or frame rate, a phone's rolling shutter can make quick movements in front of the camera appear wobbly, distorted, or with artifacts.

Coinhive, a JavaScript cryptocurrency miner, was reportedly discovered on the BlackBerry Mobile website. It was placed there by hackers who exploited a vulnerability in the site's e-commerce software that allowed them to anonymously mine cryptocurrency every time the website was viewed. There's no doubt Coinhive, an innovative mining method, is being abused and exploited by hackers in the wild.

Apple has a sterling reputation when it comes to managing its supply chain; it's where CEO Tim Cook proved his mettle to succeed Steve Jobs. Now, the company has made a strategic investment with a supplier that will be crucial to its future plans for AR wearables.

There have been concerns with how much personal information Google tracks and all the things they know about us. Of course, that's what makes Google services so useful, they can use that information to cater to each of us individually. So yes, it serves a purpose, but it's not great for personal data security.

The rise and fall of Meta, the Silicon Valley-based augmented reality startup that looked to challenge the likes of Microsoft's HoloLens, and others, took just six years.

Andre was enjoying the carefree life of a 12-year-old with his friends, riding his bike and playing sports, like all kids that age. Schoolwork wasn't hard for him, and his grades showed that.

Equifax reported on Sept. 7 that it discovered a breach on July 29 which affects roughly half of Americans, many of whom don't realize they have dealings with the company. Hackers got away with social security numbers, addresses, and driver's license numbers, foreshadowing a "nuclear explosion of identity theft." Let's explore what really happened and what you and those around you can do to protect yourselves.

If you buy an Android phone from any of the big US carriers, it will come with several extra apps in addition to any apps the manufacturer preinstalled. It's all in the name of profit, of course. Some of these apps are from companies that paid the carriers to distribute their software, and some are from the carriers themselves, usually aimed at upselling you or perhaps collecting a little data.

For those of us without rice cookers, conventional wisdom tells us that the stove is our only real option (unless, of course, you dabble in microwavable rice). However, if you're only using the stove for cooking rice start-to-finish, you're missing out on the easiest way to make perfect rice every time.

Rooting. As an Android user, I'm sure you've heard the word once or twice. According to Kaspersky, 7.6% of all Android users root — but for the 92.4% who don't, we wanted to talk to you.

Ports allow network and internet-connected devices to interact using specified channels. While servers with dedicated IP addresses can connect directly to the internet and make ports publicly available, a system behind a router on a local network may not be open to the rest of the web. To overcome the issue, port forwarding can be used to make these devices publicly accessible.

A mention of the deep web can bring to mind images of drugs, hackers, and other criminal activity. Despite the presence of these elements, the Tor network is a valuable tool for preserving privacy and anonymity. And browsing the deep web and any hidden services can be as simple as downloading the Tor Browser.

The year 2020 was a pivotal span of time during which the word "virtual" took on a brand new meaning. Instead of referring to VR or augmented reality, the term was hijacked to describe meeting across long distances through a variety of software tools, most often through video.

Tony Buzan is a leading expert on the brain and learning, and inventor of the revolutionary Mind-Mapping technique, which he believes is more efficient than conventional methods of writing notes and ideas. In this film Tony talks about how he developed Mind Mapping and how it can be applied in everyday life. Develop mind mapping with Tony Buzan.

Are you a conventional male in a conventional relationship with a conventional female? The majority of the population aged 25+ would likely answer "yes". According to stereotype, many males seem to "genetically" struggle with what many females seem to "genetically" value: the acknowledgment and appropriate appreciation of relationship milestones. If you've answered in the affirmative, worry no more, because there's an app-to-the-rescue for the helpless male: If you include yourself among the ...

New trailer for "The King's Speech", directed by Tom Hooper (John Adams,The Damned United) and shot by Danny Cohen (John Adams,Pirate Radio). Really interesting use of framing (shortsided and headroom) and lenses. Among other things, it's refreshing to see the filmmakers choose to shoot a CU with a 24mm that's a foot below the eyeline instead of the conventional 180mm CU that feels like you're in another county.

Want to bug a room on the cheap? This video how-to demonstrates how to make a simple eavesdropping device using a cell phone with auto-answer support and conventional plug-in type headset. For detailed advice on setting up this expedient spy bugging device, consult this friendly how-to. Eavesdrop with a cell phone.

Revitalize your computer experience with something new and eccentric, possibly even more comfortable—a felt computer mouse.

A team of Japanese researchers have developed an airbag system for the exterior of the car, rather than the interior, with the purpose of protecting pedestrians.

I'm no skateboarding pro, so I'm curious. In the case of the 14-wheeled skateboard, does the saying "less is more" apply? Flowlab's unconventional skateboard has been around since the early '90's, and has yet to replace the conventional 4-wheeled model. It boasts that it can "carve to 45 degree angles with no resistance and fluid transitions edge-to-edge", but how does it handle an ollie? Those in the know, please comment below.

Every summer, I pick one or two films I can't wait to see. Some of them are conventional blockbuster choices (Transformers, Star Trek) and others are guaranteed to deliver (Dark Knight, etc.). The obvious choice for this summer is Chris Nolan's new epic "Inception". But if you're interested in an indie-epic all its own, check out "Animal Kingdom", directed by David Michod. The early Scorsese-esque fan favorite at Sundance (and Dramatic winner) has some of the best looking stuff I've seen in a...

CMU’s Biorobotics Laboratory modular snake robot slithers in all sorts of different ways. Check out the three videos in the gallery below.

Commonly associated with cleaning and disinfecting items around the home, bleach can also be used as a water sterilization method in an emergency situation when you do not have access to clean, running water. Simply add 6 drops of bleach to a gallon of water and wait for 30 minutes before drinking.

Capstone's CMT-380 stealth looking prototype can hit 150mph, compared to Tesla's 125. Tesla better step it up.

Heatherwick Studio's London based rolling bridge is an engineering marvel. Lots of fun, and immensely satisfying to watch (via YouTube, assuming you can't see it in person).