Have you ever been locked out of a room in your own home? Well Barbara K is going to show us exactly how to open a locked door in this video. This will let you get your bedroom door open when you have locked yourself out!

When you buy a computer, you aren't just paying for the machine's constituent parts but the cost of putting all of those parts together. Building your own computer, then, can be a great way to save a little money for the technically savvy. And if you're not savvy, get savvy with this clip.

If you don't have room for a full-scale compost heap, you can always employ the services of some worms. In this handy vermiculture how-to, you'll learn how to build your very own wormery.

Systm is the Do It Yourself show designed for the common geek who wants to quickly and easily learn how to dive into the latest and hottest tech projects. We will help you avoid pitfalls and get your project up and running fast.

You love your iPhone and you can't live without it, but it's lacked the basic ability to cut, copy, and paste across multiple apps. With Apple's OS 3.0 upgrade, you can do it all with just a few taps. Watch this Howcast guide to learn how to cut, copy, and paste on your iPhone.
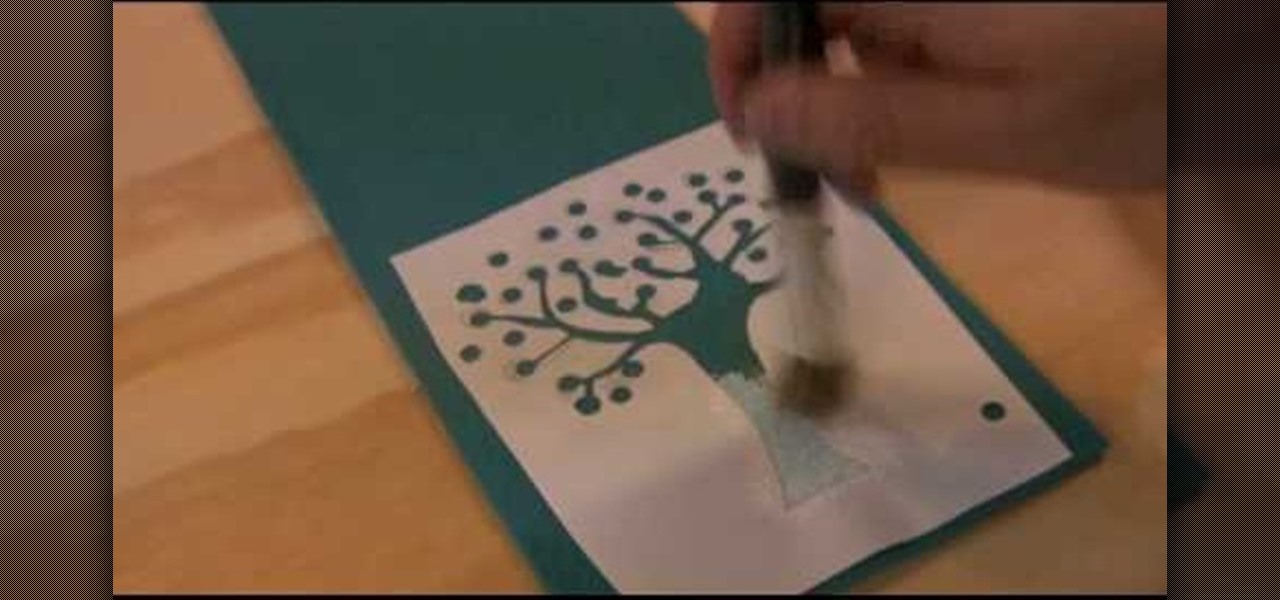
Check out this DIY video tutorial from Curbly, the best place to share pictures of your home, find design ideas, and get expert home-improvement advice.

Mike Callahan from Butterscotch describes how to manage the passwords on your iPhone by using the 1Password app. The application costs $5.99 for the Pro version. First, you enter an Unlock Code to give you access to the app. The icons across the bottom of the screen correspond to different features of the app. The Logins icon stores your login information. The Wallet icon stores information about your credit and bank cards. The Passwords icon holds all your passwords. The Add icon allows you ...

This is a great way to turn your treadmill into a walk station quickly and cost effectively. You only need a few things for this project: a tape measure, four shelf mounting brackets, screws, a drill, and a shelf.

Check air pressure in car’s tires

This video shows you how to make Great Depression-era baked apples. This is healthy for you. You will enjoy it. This is a really old recipe.

Eagle Lake Woodworking, hosted by John Nixon, offers great do-it-yourself guides for building your own furniture, especially in the American Arts and Crafts style, and turning your garage into an amateur woodshop. Search Eagle Lake on WonderHowTo for more carpentry tutorial videos. From Eagle Lake Woodworking on this specific lesson:

Whether you’re a professional DJ or simply a vinyl enthusiast, knowing how to install a fresh needle will help protect your music.

Systm presents this detailed tutorial on how to make a custom Star Wars style light saber. Luke, Darth and Obi-Wan's Lightsabers were pieced out of junk piles. David shows you how to build exact replicas and an original design from The Custom Saber Shop. Then he picks a fight with Patrick.

Sure, you can go online and send the first flowers you see, but a little thought and planning will go a long way toward impressing her. Sure, you can go online and send the first flowers you see, but a little thought and planning will go a long way toward impressing her. You will need a friend or relative of the recipient. Send her favorite. If she’s ever mentioned a favorite flower, buy that. You’ll get bonus points for listening to her. If you have no clue, ask a friend or relative of hers ...

Getting bored, or need some sort of car that costs practically nothing? This three-part video tutorial will show you how to create a life-sized foam and clay automobile model. You'll learn how to build an automotive clay model. Why would you want to build an automotive clay model? Well, for the fun of it, or because you're an automotive designers or modeler and you need to design and build a prototype of a new vehicle.

Since Motorola engineer Bill Smith invented Six Sigma in 1986, corporations around the world have employed it to eliminate costs and process cycle time while increasing profits and customer satisfaction. These techniques and tools for process improvement were invaluable to famed CEO Jack Welch, who used them to redefine General Electric's business strategy in 1995.

Invented by Motorola engineer Bill Smith in 1986, Six Sigma's methodology defines a series of steps with specific value targets. These targets can be used, for example, to eliminate costs and process cycle time while increasing profits and customer satisfaction.

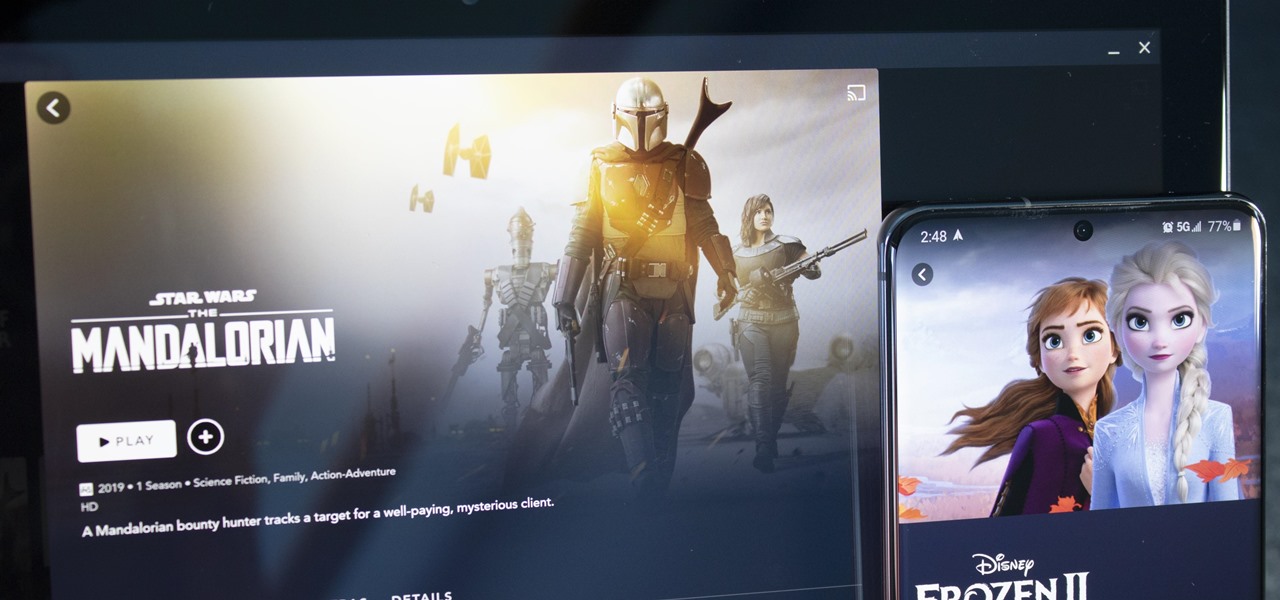
With shows like "The Mandalorian" and movies like "Frozen 2," Disney+ has quickly become a must-have streaming service. However, with Netflix, Amazon Prime Video, and Hulu, adding another subscription-based service can become expensive — but there are ways to trim down the cost.

Edison Mail's big Assistant update means more features and functions for you in a convenient, efficient package. One of the most significant changes to come with the 1.17.0 (iOS) and 1.12.0 (Android) updates is calendar functionality for all connected email accounts. Other apps, like Spark, have had this for some time, but we're excited that Edison has finally jumped aboard the bandwagon, too.

While North has yet to add third-party app support to its Focals smartglasses, the company has been diligent as of late in its efforts to add more functionality to the bare-bones AR device.

Update February 25: The new Sony Xperia flagship has been announced, and it has a new name: The Sony Xperia 1. You can read all of the official specs and details at our full article on Sony's new model.

The latest preview build for Microsoft HoloLens is packed with new sharing features, including support for the Miracast protocol.

When it comes to the sub-$250 price range, the new Nokia 5.1 might be the perfect phone. Of all the new models announced at Nokia's event in Moscow, the Nokia 5.1 offers the most with the least compromises. For a third of the cost of a flagship, you get a phone with a premium build, solid specs, and good battery life.

There's always been a clear divide between flagship and midrange phones. Flagships will run you at least $700, while midrange typically falls between $250 and $550. The main difference is the processor, with midrange phones sporting a 600-series Snapdragon and flagships rocking the 800-series. Now, Qualcomm may have just created another smartphone tier with their newly-unveiled 700-series chip.

While our time with the Protostar VM from Exploit Exercises was lovely, we must move on to bigger things and harder challenges. Exploit Exercises' Fusion VM offers some more challenging binary exploitation levels for us to tackle. The biggest change is that these levels are all network services, which means we'll write our first remote exploits.

Ever since Google CEO Sundar Pichai took the helms of the world's most valuable brand, he has made it his mission to bring smartphones to lower-income communities. Born in India, Mr. Pichai has created several programs to address the needs of the Indian market, particularly the lower income families.

Apple officially unveiled the long-awaited iPhone X, its tenth-anniversary edition iPhone, on September 12. With preorder and release dates just around the corner, you'll want to brush up on all things iPhone X to make sure you get your hands on one as soon as possible. After all, preorders start Friday, October 27.

German groups ZF Friedrichshafen AG and HELLA are collaborating to add to their autonomous portfolios with camera and radar development.

The technology driving the automated vehicle revolution relies on the car's ability to see and understand the world around it.

The Moto X and Moto Z have a set of features that let you launch common shortcuts by shaking your phone in one direction or another. For instance, there's a chop gesture that turns on the LED flashlight, and a wrist-twist gesture that instantly opens the camera app.

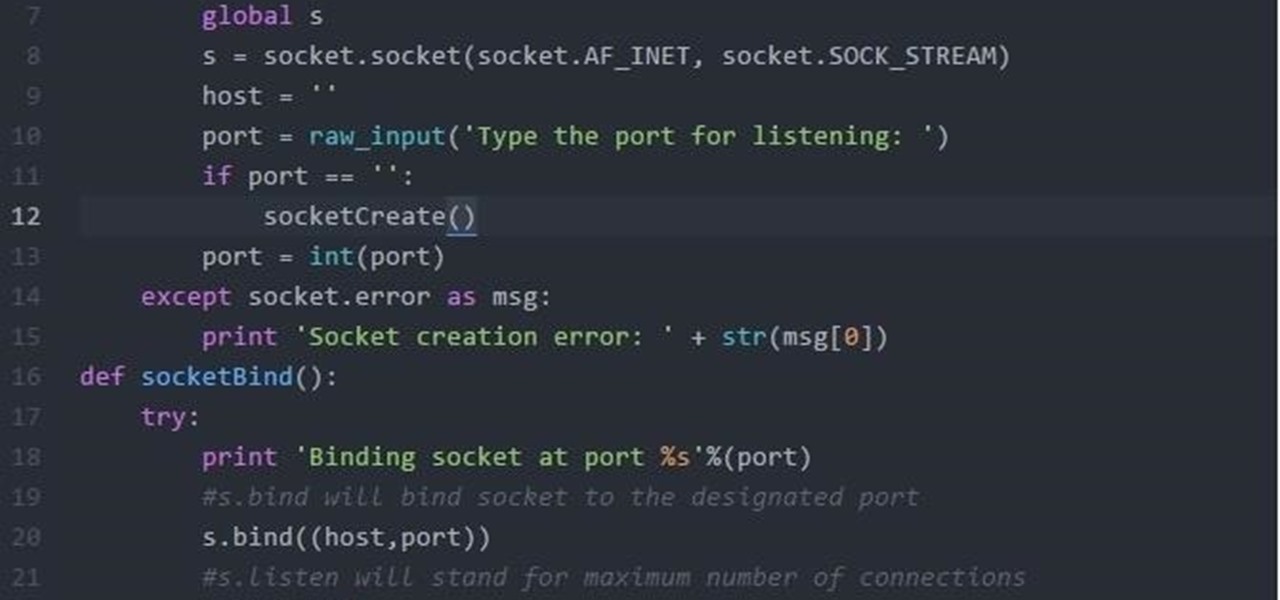
Welcome back, everybody. In the previous article, we covered the ideas and concepts of well-known ports and trust exploitation in order to evade a firewall. Today, we'll be building the shell, the part that receives commands, executes them, and sends the output back to the attacker.

Welcome to the final tutorial of the series on standard C. This article will cover the linked list abstract data type (ADT). There will be a lot of abstraction to try to deliver the understanding in the most basic way for easiest interpretation of what they are and how they work, then we will get into the guts of it and learn the technical code underneath. For those who have yet to grasp the concept of pointers, it's advisable that you do that first before approaching this. Having learned thi...

Welcome finally, to a tutorial on buffer overflows! At last we have reached an exciting part of this series where I will dedicate the entire article on explaining and exploiting the notorious vulnerability. Grab some popcorn, sit back and enjoy the show.

In the recent hit movie Furious 7, the storyline revolves around the acquisition of a hacking system known as "God's Eye" that is capable of finding and tracking anyone in real time. Both the U.S. spy agencies and an adversarial spy agency (it's not clear who the adversary is, but the location is "beyond the Caucasus mountains," which could imply Russia?) desperately want their hands on this system.

If you haven't read the last article, feel free to stop by and give it a read, but abstaining from reading it will not, for the most part, be detrimental to your understanding.

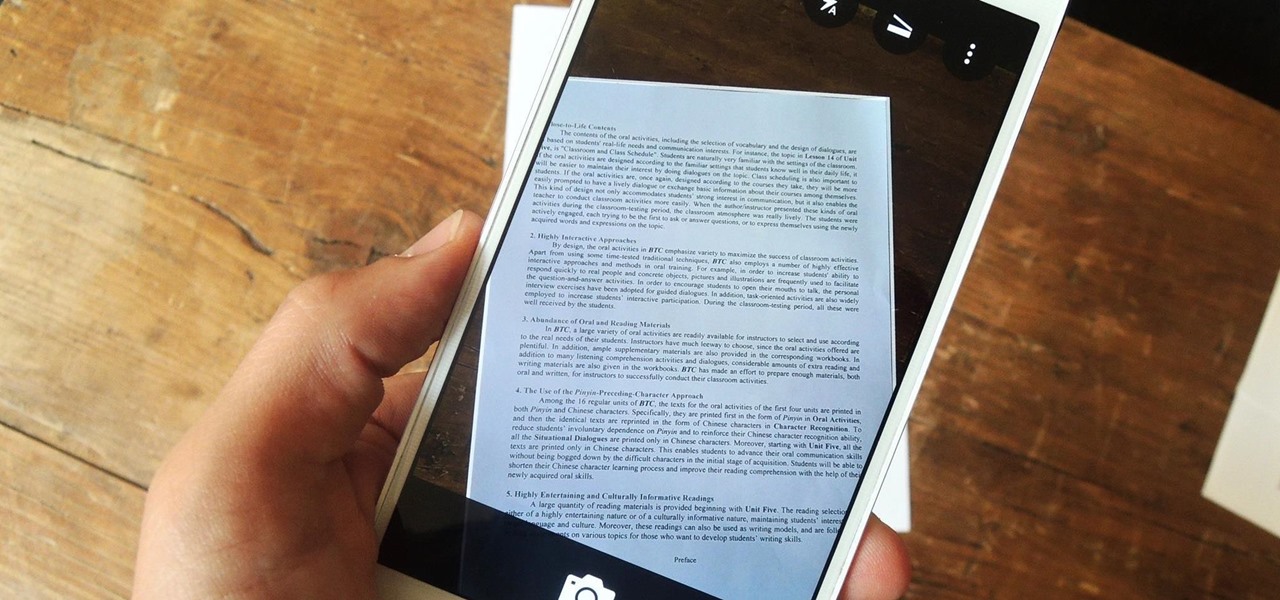
Scanners are much too cumbersome to fit in a pocket, but with the use of just one application, you can replace all that bulky hardware with your Android smartphone and take it with you wherever you go. All you need to do is find the scanning app that fulfills your needs. Here are our five favorites that are good for business pros and average joes alike.

As we're all aware, recon is vital to a successful hack. We need to know everything we can about the target in order to perform the best possible attack. Port scanning is a basic recon concept that is introduced very early in learning proper reconnoissance. The issue with port scanning is that is makes a lot of noise. Every connection to every port will be logged. This is where stealth scanning comes in. Also known as SYN or half-open scanning, stealth port scanning is a bit quieter, and is l...

Hi Folks. This is my first post. I will teach how to create a server and client python reverse shell using sockets and python language. The script i'll post here is going to be very simple, and from here you'll have the possibility to adapt to your own purpose. For example, my original script can download files, upload files, make changes to registry, create user accounts and more. I'm sure you could do it on your own too.

As Android's de facto virtual assistant, Google Now lets us speak directly to our phones in plain English to answer our questions and perform many basic tasks. With the app open, just say "Okay Google," then wait for the beep, and ask almost any question.

NOTICE: Ciuffy will be answering questions related to my articles on my behalf as I am very busy. Hope You Have Fun !!!