If you save scraps of yarn, and have a dog, this is an easy project for you. The Mobius scarf has the advantage of not having any ends to come untied, or dangle down for your dog to trip over, or get tangled in branches and stuff. I made this one for Pepper, my 16lb rat terrier. Step 1: Choose Your Yarn: I had very little yarn to work with. I had one more ball, but it had just a little more on it than the largest shown here.

Welcome back , my fledgling hackers! Lately, I've been focusing more on client-side hacks. While web servers, database servers, and file servers have garnered increased protection, the client-side remains extremely vulnerable, and there is much to teach. This time, we'll look at inserting a listener (rootkit) inside a PDF file, exploiting a vulnerability in Adobe's Reader.

While there are countless ways to welcome in the new year, many of them involve imbibing copious amounts of delightfully spirited libations. If you're anything like me, I know you're fearing the monster hangover on New Year's Day.

Despite the security concerns that have plagued Facebook for years, most people are sticking around and new members keep on joining. This has led Facebook to break records numbers with over 1.94 billion monthly active users, as of March 2017 — and around 1.28 billion daily active users.

Will the predicted apocalyptic date—December 21st, 2012—really be the end of the world? In this ongoing five-part series, we examine what would happen if zombies, nuclear weapons, cyber wars, earthquakes, or aliens actually destroyed our planet—and how you might survive.
The concept and structure of Christmas hasn't changed much since its inception. In its infancy, Christians recruited Roman pagans by associating Christmas with the Saturnalia, an ancient Roman festival in honor of the deity Saturn (also held in December). The pagans had long worshiped trees (as did other historical cultures) and would bring them into their homes and decorate them, something that influenced our modern holiday decorations. While certain things such as gifts and ornaments have b...

Thanksgiving is pretty much the only day out of the year when you can be a complete fatass. It's totally expected, if not encouraged. In fact, if you aren't stuffing your face with a bunch of delicious and unhealthy food, people start to look at you funny.

Stand out from the high street fashion clones with stuff you’ve fashioned yourself. It’s easy to take old pieces of electronic junk and transform them into all sorts of fun ‘n’ funky geeky accessories. Like a totally useful tote bag, a what-on-earth-is-that wallet and a bedazzling belt. It’s terribly geeky but chicy too. Here’s how…

When it comes to milk, my family consumes anywhere between two and four gallons every two weeks. That's about four to eight gallons every month. That's a lot of milk—and a lot of empty milk jugs! Instead of simply tossing them in the recycling bin, why not get creative and make something useful out of them yourself?

WonderHowTo is a how-to website made up of niche communities called Worlds, with topics ranging from Minecraft to science experiments to Scrabble and everything in-between. Check in every Wednesday evening for a roundup of user-run activities and how-to projects from the communities. But don't wait—start submitting your own projects to the most appropriate World now!

It's already Halloween and the night is fast approaching. You swore to yourself last year that you wouldn't wait until the last minute again for a Halloween costume, yet here you are on Samhain without a costume… again. All of the costume shops are sure to be crammed with last-minute shoppers, and you don't feel like spending a lot of dough anyway, so what are your options?

This tasty treat might stop your heart but it'll seem worth it. There's nothing much better than your favorite candy bar, but trust me there is and favorite candy bar fried. No longer reserved for fairs and carnivals this artery buster can be made right at home.

One app is continuing to make a name for itself as the go-to platform for celebrity art that transcends canvas and paint and moves in augmented reality.

Riding your bike with and incorrect seat height will make it more difficult to peddle and can be hard on your knees. Ensure a more enjoyable bike ride by taking a couple of minutes and making sure your seat is the correct height.

It’s easy to gain a little extra weight in college but there are ways to defy this weight gain trend. It won’t work without will power but you can limit your unhealthy food intake and sneak in some unconventional exercise routines.

Before attempting to play this video game, try out the first DeathSpank (Orphans of Justice), then move onto this sequel to the storyline, DeathSpank: Thongs of Virtue. This walkthrough series has every single minute of gameplay stuffed into 58 parts. Okay, that may seem like a lot, but for a hefty role-playing game like this, you try and do better. Watch the last couple videos for the multiple endings and the Hothead Mountain easter egg.

The remake of the Warner Bros. classic animation meets live-action movie Space Jam, this time starring LeBron James instead of Michael Jordan, hits theaters today.

In the dark, even the lowest brightness option on the iPhone can still feel a thousand burning suns. No matter whether you're in bed or at the movie theater, you don't want to create a distraction with your smartphone. That's why you might want a brightness that isn't readily available on your device — but luckily, there may be a way to go lower than the lowest brightness.

If you thought Snap's Spectacles were limited to a couple of demos, you haven't been paying attention.

Ever since Facebook announced its partnership with Luxxotica brand Ray-Ban to produce smartglasses, the augmented reality space has been on high alert awaiting more details.

Since its launch two years ago, the HoloLens 2 has been the best AR headset available, and nothing has come close to touching it since.

IT is a competitive field, and finding success requires more than knowledge of a couple of coding languages or knowing how to google really well. To stand out among your peers and competitors, you should learn everything you can and get as much diverse experience as is available.

Like the layers of an onion, 2021 continues to peel back new hints of Apple's kinda-secretive augmented reality device development.

It's been said time and time again: reconnaissance is perhaps the most critical phase of an attack. It's especially important when preparing an attack against a database since one wrong move can destroy every last bit of data, which usually isn't the desired outcome. Metasploit contains a variety of modules that can be used to enumerate MySQL databases, making it easy to gather valuable information.

This week's Magic Leap Lumin OS update contained a number of goodies, including iris authentication, and a way to stream to Twitch from the device.

Phishing is the easiest way to get your password stolen, as it only takes one mistake to log in to the wrong website. A convincing phishing site is key to a successful attempt, and tools to create them have become intuitive and more sophisticated. SocialFish allows a hacker to create a persuasive phishing page for nearly any website, offering a web interface with an Android app for remote control.

A hacker with privileged access to a Windows 10 computer can configure it to act as a web proxy, which allows the attacker to target devices and services on the network through the compromised computer. The probes and attacks appear to originate from the Windows 10 computer, making it difficult to detect the attacker's actual location.

Information gathering is one of the most important steps in pentesting or hacking, and it can often be more rewarding to run things on the target itself as opposed to just running scripts against it remotely. With an SQL injection, a hacker can compromise a server and, ultimately, upload and run the "unix-privesc-check" script locally in order to further identify possible attack vectors.

Apple's aiming to take over the TV world, and it shows in iOS 12.3. Nothing is going on yet with Apple TV+, Apple's video streaming platform with original content, which isn't supposed to come out until the fall. But there are some goodies in the new Apple TV app for iPhone that you should get to know.

While Microsoft dominated the augmented reality news at this year's Mobile World Congress, a small AR startup we've covered in the past arrived in Barcelona, Spain, to unveil the next phase of its mission.

With the number of web applications out there today, it comes as no surprise that there are just as many vulnerabilities waiting for hackers to discover. Finding those vulnerabilities can be a difficult task, but there are plenty of tools available to make the process easier. While it won't help find any zero-days, web scanners such as Uniscan will detect common vulnerabilities.

The year 2018 was a rough one for Snap, the company behind the Snapchat app and the Spectacles wearable camera device. From executive departures to reports of slowed user growth, the company that once spurned Facebook's multibillion-dollar advances is now facing a moment of truth as it stares down its uncertain future.

In 2018, augmented reality went from the vague promise of interesting things in the near future to tangible developments in software and hardware, proving that immersive computing is indeed the future.

You're minding your business when your Apple Watch taps you. To your surprise, the watch claims your heart rate dipped abnormally low. The news might come as a shock — especially if you have no history of a heart condition — but before you panic, you should take the time to fully understand what this alert is really saying and what you can and should do about it.

Mystery is a tricky thing. Used correctly, it can give onlookers the impression that wondrous and perhaps valuable things are afoot. However, once the veil of suspension of disbelief is removed in any significant way, that same mystery can quickly turn into not just skepticism, but outright anger at what may have seemed like an attempt to dupe trusting onlookers.

On Tuesday, the smartglasses startup known as North finally took the wraps off its Focals product, but in a very unique way: The team simply opened a couple of stores and invited the public in.

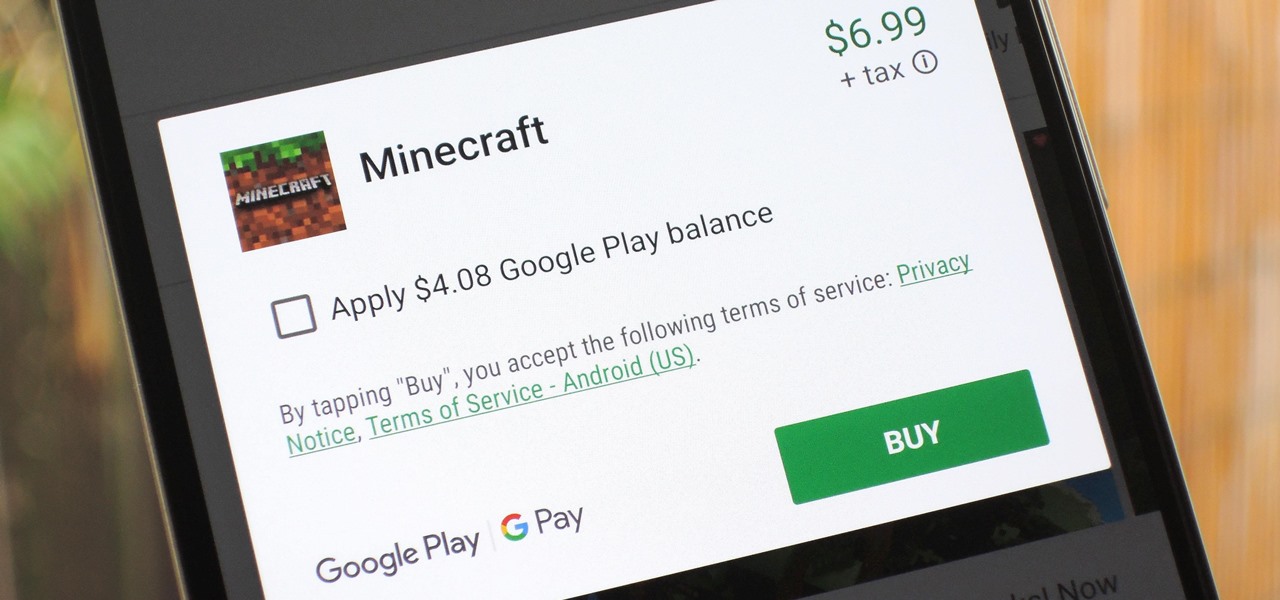
The iTunes App Store makes it easy to buy an app or game on someone else's behalf, and it's a great way to send an iPhone user a thoughtful gift. The Google Play Store doesn't have such functionality, but there are still a few workarounds to accomplish the same goal: gifting an app to an Android user.

The battle between the Pixels and the iPhones has been heating up over the last few years, and this year's bout is the best one yet, with Google's Pixel 3 taking on Apple's iPhone XS.

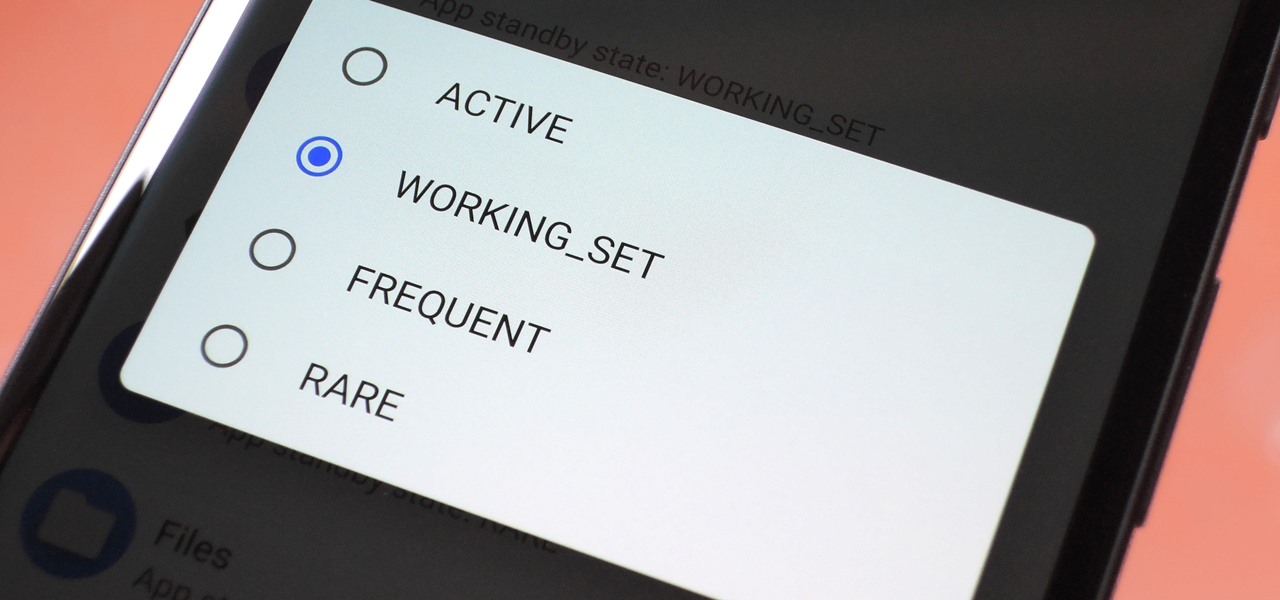
Battery drain is a major pain point for Android users, though that promises to change thanks to Android Pie's new Adaptive Battery feature. But Google hasn't said much about the inner workings of this feature, only publicly stating that it uses AI to boost battery life. So we dug in to find out what's really going on under the hood.

After gaining access to a root account, the next order of business is using that power to do something more significant. If the user passwords on the system can be obtained and cracked, an attacker can use them to pivot to other machines if the login is the same across systems. There are two tried-and-true password cracking tools that can accomplish this: John the Ripper and Hashcat.