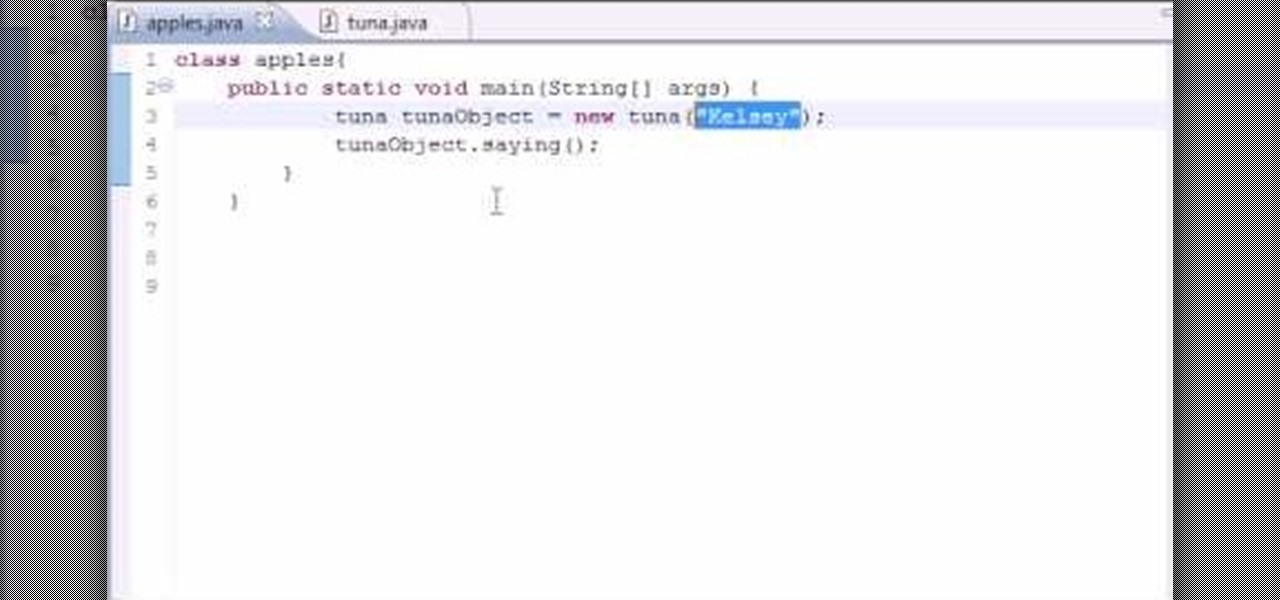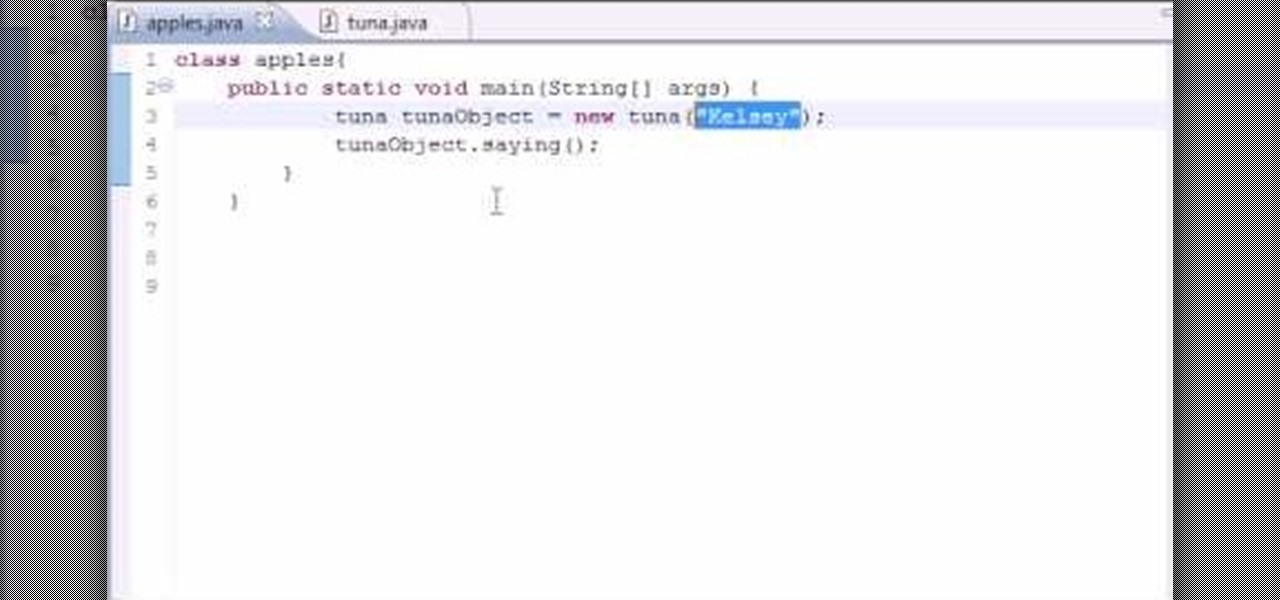
Want to program your own Java games and applications but don't know beans about object-oriented programming? Never you fear. This free video tutorial from TheNewBostonian will have you coding your own Java apps in no time flat. Specifically, this lesson discusses how to easily provide instructors to your classes when writing in Java. For more information, including detailed, step-by-step instructions, watch this helpful programmer's guide.

Want to program your own Java games and applications but don't know beans about object-oriented programming? Never you fear. This free video tutorial from TheNewBostonian will have you coding your own Java apps in no time flat. Specifically, this lesson discusses how to generate random numbers in a Java application. For more information, including detailed, step-by-step instructions, watch this helpful programmer's guide.
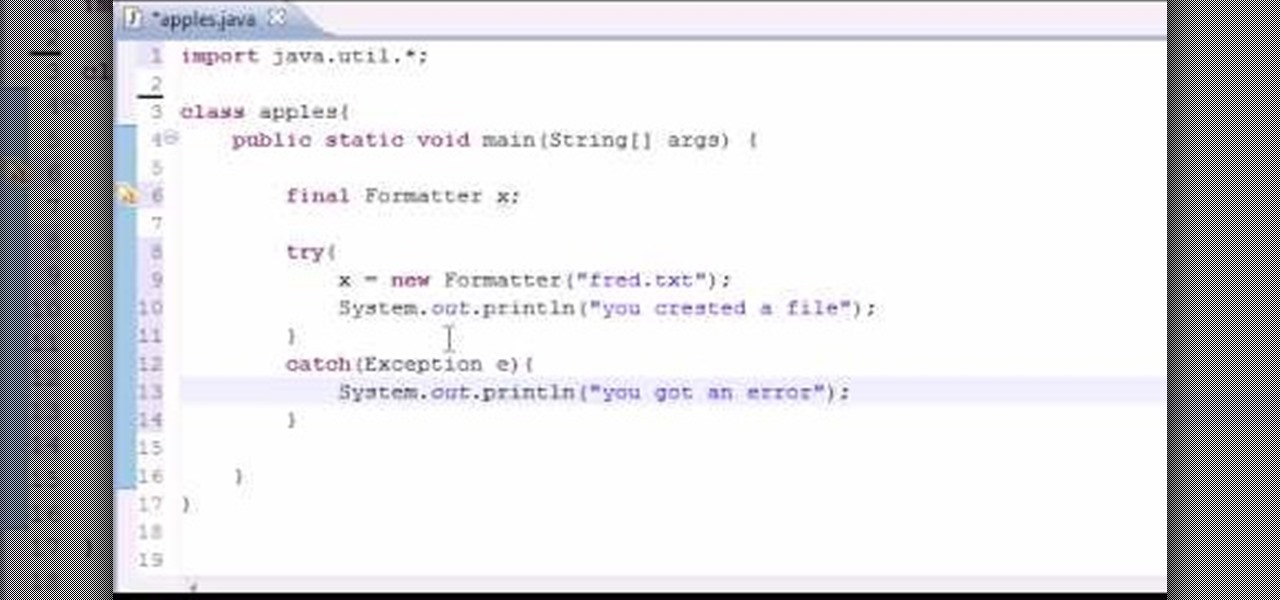
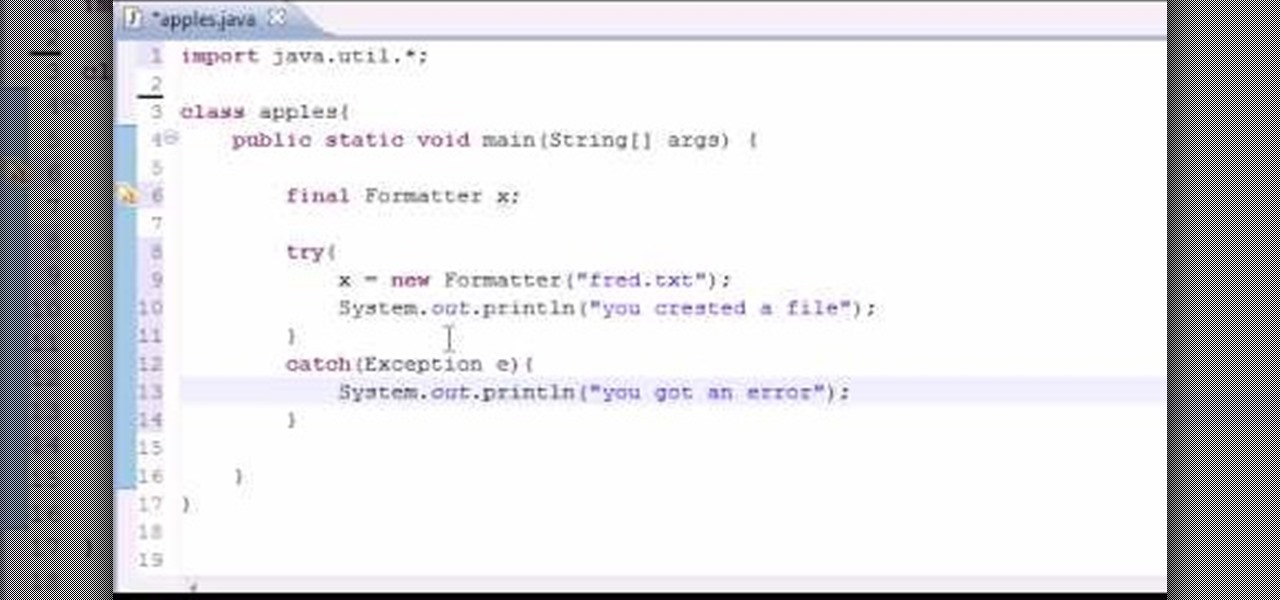
Want to program your own Java games and applications but don't know beans about object-oriented programming? Never you fear. This free video tutorial from TheNewBostonian will have you coding your own Java apps in no time flat. Specifically, this lesson discusses how to easily generate a text (txt) file from within a Java application. For more information, including detailed, step-by-step instructions, watch this helpful programmer's guide.
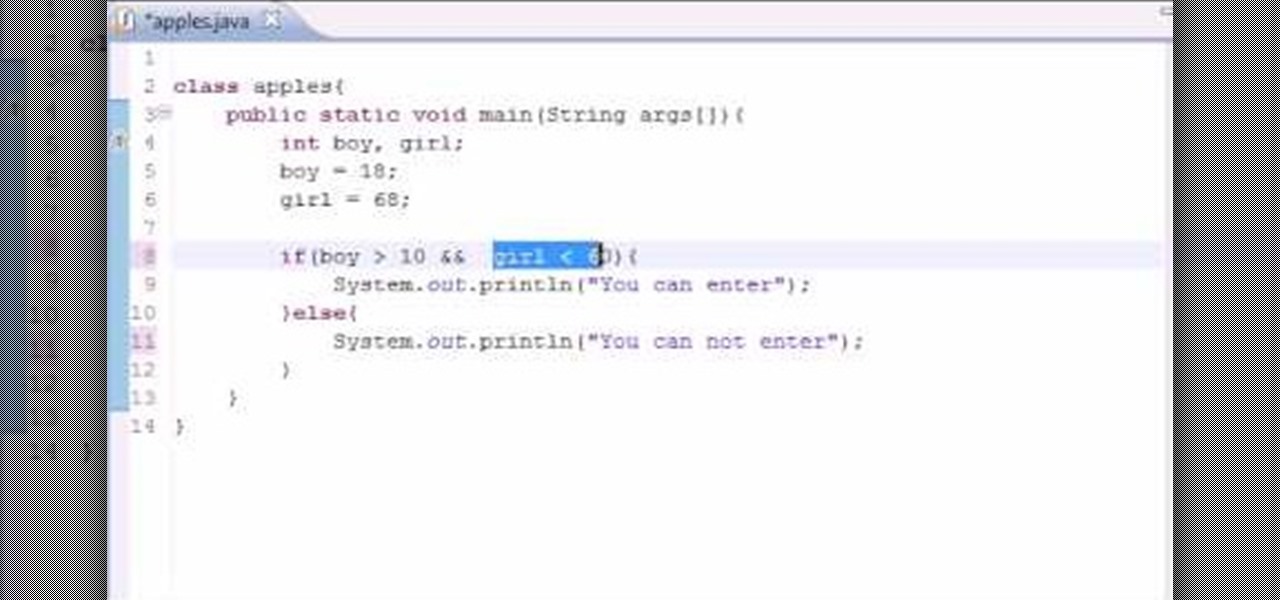
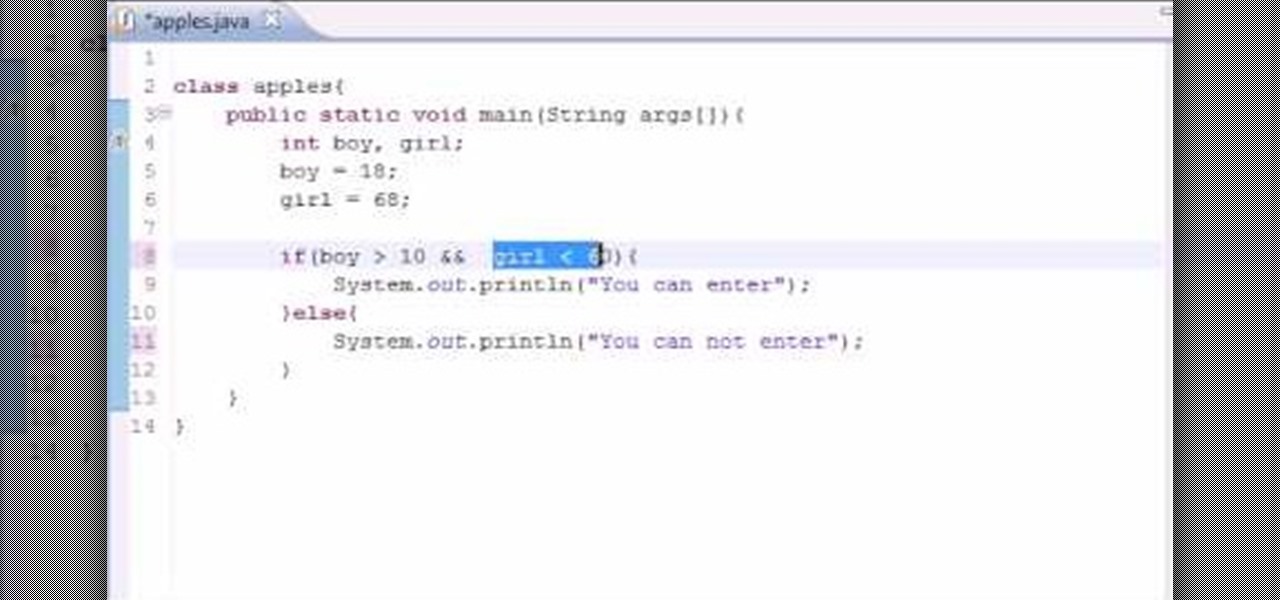
Want to program your own Java games and applications but don't know beans about object-oriented programming? Never you fear. This free video tutorial from TheNewBostonian will have you coding your own Java apps in no time flat. Specifically, this lesson discusses how to work with logical operators in Java. For more information, including detailed, step-by-step instructions, watch this helpful programmer's guide.
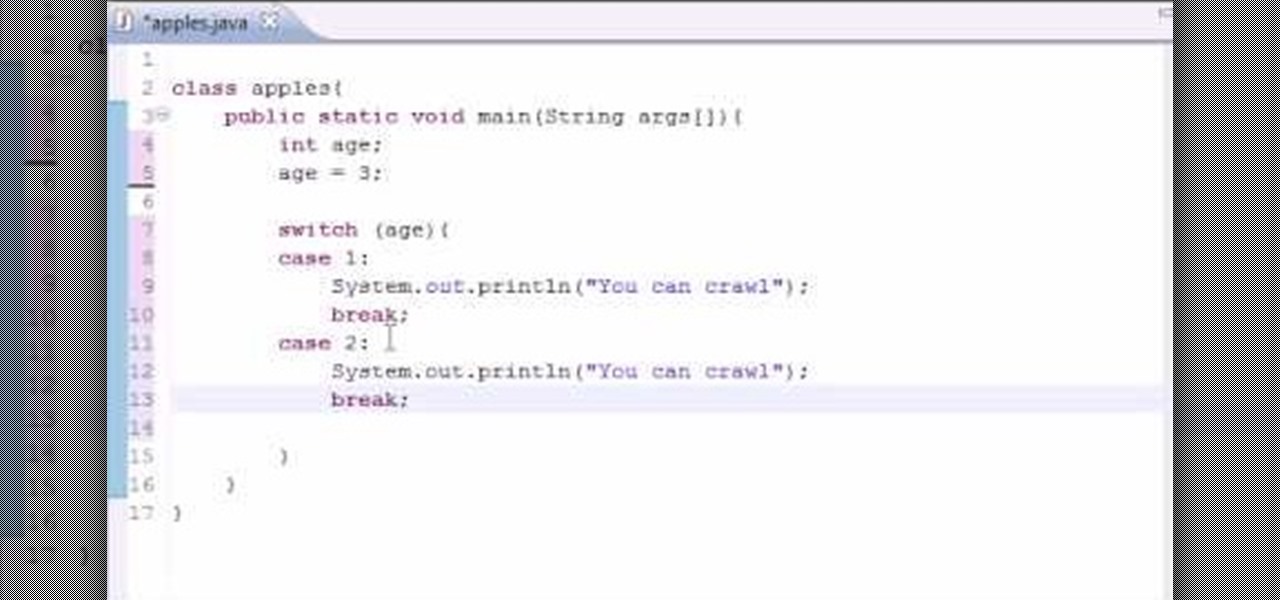
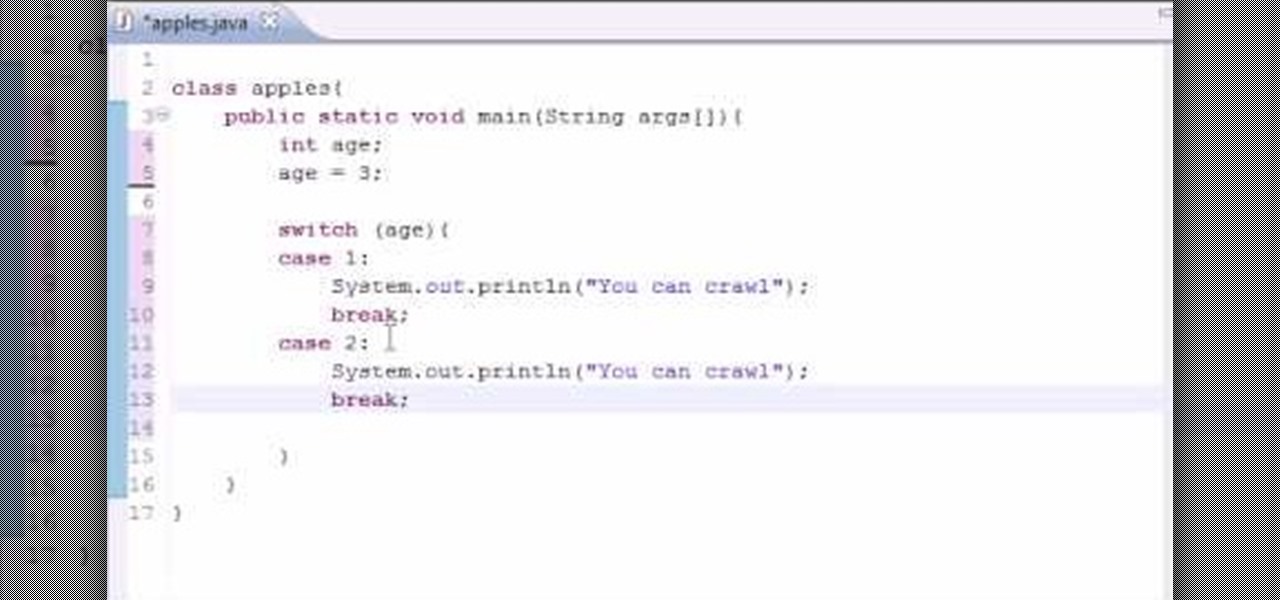
Want to program your own Java games and applications but don't know beans about object-oriented programming? Never you fear. This free video tutorial from TheNewBostonian will have you coding your own Java apps in no time flat. Specifically, this intermediate-level lesson will discusses how to work with switch statements. For more information, including detailed, step-by-step instructions, watch this helpful programmer's guide.

Whether you're new to Adobe's Creative Suite or a seasoned graphic design professional after a general overview of CS5's most vital new features, you're sure to be well served by this official video tutorial from the folks at Adobe TV. In it, Terry White discusses his five favorite features of the newest addition to Adobe's CS, Flash Catalyst, an application which allows you to create dynamic web pages without coding. Learn how to create dynamic scrolling content and functional Flash buttons ...

This video will show you a few techniques for removing stuck pixels from an LCD screen. This is not a guaranteed fix. Please only use these as a last resort, as some of them can cause more damage to the LCD. Only attempt these if you are experienced and know what you are doing.

Understand how binary numbers work, including how to read binary numbers, and create your own. This mathematics or computer programming tutorial is a zip to get through. It covers practical and theoretical use and need for binary code understanding. Binary means zeroes and ones in a series. This is paramount to digital transmission versus analog that transmits in a sinusodial wave form.

Watch this ASP.Net video tutorial to learn how to create culture-aware and locale-specific web content with no additional code. Use the Resource Editor to create page-level and application-level resources.

As a mechanic, you can't get paid until you fix it, and you can't fix it until you diagnose it, which means a quick diagnosis means a quick fix which means a quick payout. If life was always this easy! This automotive video will show you how to troubleshoot and diagnose a 1999 Mercury Village, 3.3L, with 150,000 miles on it. The chief complaint is the CEL (check engine light) comes on and it runs like it has a misfire. It feels like a steady consistent misfire, which is code P0304 (Cylinder #...

In order to build a Spark Carousel in Adobe, you can get the source code first, which is available here.

YouTube videos can be embedded in other websites like MySpace. Go to the YouTube page of the video that you want to display on other websites. In the right had side of the page there are details of the video like the URL to it and below it is the Embed link. This link can be used to embed this video in other websites. To do this first copy the embed code and go to your MySpace edit page. Copy the code over there. Now delete everything that is there between the embed tags. Now in the code afte...

In a recent poll taken by an online recruiting company revealed that 37 percent of all hiring managers do not hire someone based just on the way they dress, more than half said they'd hold it against a candidate if they hadn't worn a jacket and seventy percent said that they wouldn't hire anyone wearing jeans, a leather jacket or a polo shirt to the interview. The rules for office dress code have changed, more and more companies offer their employees a business-casual dress code which makes i...

With the game Crush the Castle, it is now possible to hack the game and get a high score. By following a few simple steps shown in the video, it is entirely possible to achieve a gold medal in the game quite easily. As simple as entering a sequence of number codes into a line will make it possible to do one shot and still win gold, as well as completely crush the castle. Just by putting in the code, you are able to start the game, and, with one shot from the catapult, you are able to complete...

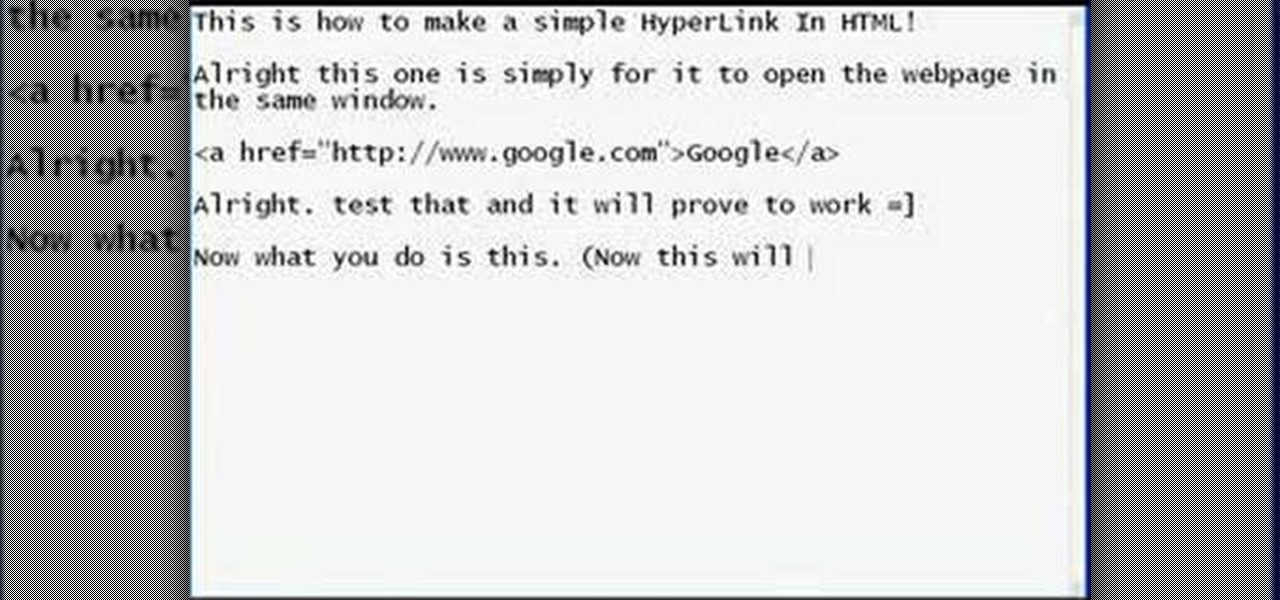
This how to video shows how to put an HTML hyperlink on a web page. It starts with the basic code to simply insert the link and have that link open in the same window. The code appears as follows: <a href="http://www.website.com">Text that will show up on the page </a>. The example used is Google, so it would be, <a href="http://www.google.com">Google</a>. The video then explains how to create a hyperlink that shows up in a new window. Sticking with the Google reference it would read <a href=...

The Visual Prototyper is a wireframe design solution that allows you to design a fully functional application wireframe and simulate it.

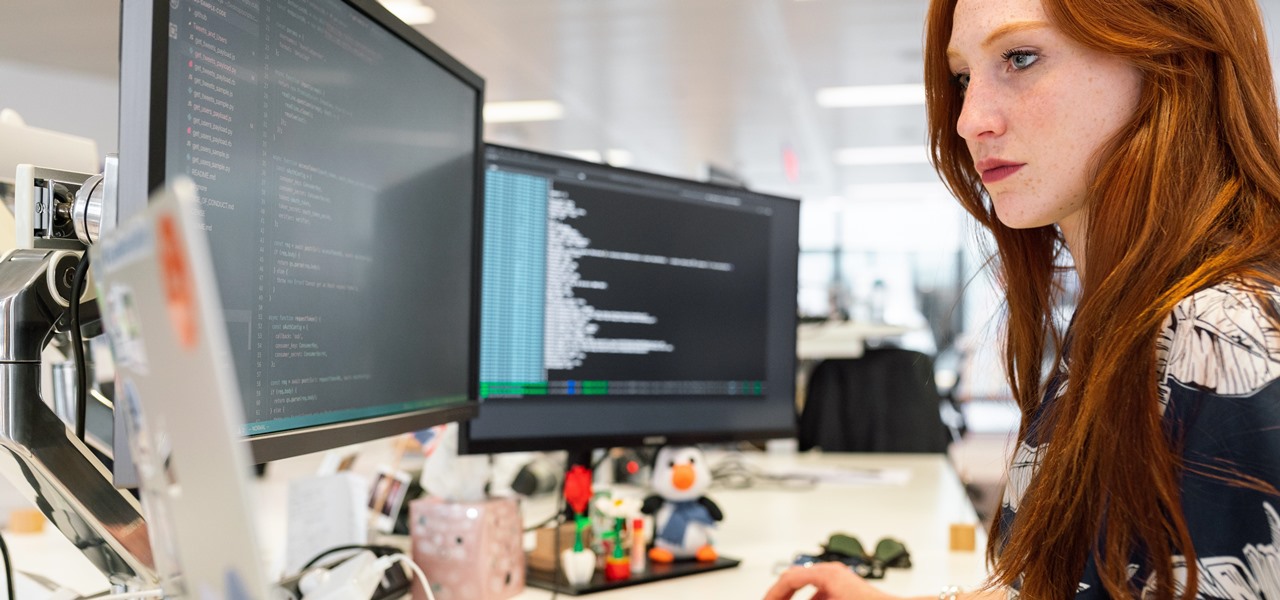
In 2020, we had to learn that it's up to us to make ourselves stand out in our jobs or to future employers. Coding is a skill that won't just make you stand out — it'll make you indispensable. Due to the mass move to working online, there is more demand for strong, intuitive web design, and learning to code means you can be the person who makes that.

You're on your computer a lot, so it only makes sense that you download the best apps and software for it. The Official Cyber Monday Mac Bundle Ft. Parallels Pro & Luminar 4 is available for only three weeks at an additional 40% off the sale price of $69.99. Just use the promo code CMSAVE40 at checkout.

You may be familiar with image-based or audio-based steganography, the art of hiding messages or code inside of pictures, but that's not the only way to conceal secret communications. With zero-width characters, we can use text-based steganography to stash hidden information inside of plain text, and we can even figure out who's leaking documents online.

Wi-Fi networks come in two flavors: the more common 2.4 GHz used by most routers and IoT devices, and the 5 GHz one offered as an alternative by newer routers. While it can be frustrating to attack a device that moves out of reach to a 5 GHz Wi-Fi network, we can use an Alfa dual-band adapter to hack Wi-Fi devices on either type of network.

The Digispark is a low-cost USB development board that's programmable in Arduino and capable of posing as a keyboard, allowing it to deliver a number of payloads. For only a few dollars, we can use the Digispark to deliver a payload to a macOS computer that will track the Mac every 60 seconds, even bypassing security like a VPN.

Microsoft Office files can be password-protected in order to prevent tampering and ensure data integrity. But password-protected documents from earlier versions of Office are susceptible to having their hashes extracted with a simple program called office2john. Those extracted hashes can then be cracked using John the Ripper and Hashcat.

A relay is an electrical component that works like a light switch, where it's turned on or off with an electrical signal. By connecting a relay to a Wi-Fi connected microcontroller like an ESP8266, you can build a connected switch that can be controlled from the web browser of any device connected to the same Wi-Fi network — all for just a couple of dollars.

Kali Linux is probably the most well-known hacking distribution among penetration testers. However, there are alternative distros which offer versatility and advanced package management systems that are absolutely worth considering.

Net neutrality is dead and your internet service providers can collect all the data they want. While VPNs are a great way to protect some of that privacy, they're not perfect. There is another option, though, called Noisy, which was created by Itay Hury. It floods your ISP with so much random HTTP/DNS noise that your data is useless to anyone even if they do get it.

The misconception that macOS is more secure than the Windows operating system is far from the truth. With just one small command, a hacker can completely take over a MacBook and control it remotely.

Google, Amazon, and Facebook are always listening. But what's worse? Hackers are listening, too. Windows PCs are particularly vulnerable, but with a few simple commands, a remote attacker can even take over the microphone on someone's Mac computer, streaming audio and listening to private conversations in real time without the victim's knowledge, abusing an overlooked security consideration.

For SQL injection, the next step after performing reconnaissance and gathering information about a database is launching an attack. But something seems off .. in the real world, it's usually not quite as simple as passing in a few fragments of SQL code to an input field and seeing all that glorious data displayed right in the browser. This is when more advanced techniques are needed.

As cryptocurrencies gain mainstream acceptance, it's not far-fetched to think that we'll one day be able to buy alt coins like Ripple (XRP) and Stellar (XLM) using debit cards and bank accounts. Until then, we'll have to rely on using bitcoins and ethereum to buy digital coins. Thankfully, depositing and withdrawing cryptocurrencies with Binance is relatively hassle-free.

Barrow's article on Pupy made me wish for a RAT that could target an OS frequently used by gatekeepers at startups, tech companies, and creative firms: macOS. Once run, a RAT can do severe damage by dumping a user's stored credentials for many accounts. The best loot lives in the Chrome Password cache, and EvilOSX, an OS X RAT, infiltrates macOS and dumps these credentials.

The fourth and final beta version of Android O just made its debut, and the biggest change is what appears to be a new code name. When you access Android 8.0's version number Easter egg, you'll be greeted by ... a cartoon octopus.

The Raspberry Pi is a credit card-sized computer that can crack Wi-Fi, clone key cards, break into laptops, and even clone an existing Wi-Fi network to trick users into connecting to the Pi instead. It can jam Wi-Fi for blocks, track cell phones, listen in on police scanners, broadcast an FM radio signal, and apparently even fly a goddamn missile into a helicopter.

With tools such as Reaver becoming less viable options for pen-testers as ISPs replace vulnerable routers, there become fewer certainties about which tools will work against a particular target. If you don't have time to crack the WPA password or it's unusually strong, it can be hard to figure out your next step. Luckily, nearly all systems have one common vulnerability you can count on — users!

After enabling disk encryption, creating encrypted disk images, installing KeePassX and iTerm2, and using Git with local repositories, the next step to getting your Mac computer ready for hacking is setting up a package manager that can install and update open-source hacking tools. There are multiple options to choose from, but Homebrew has a slight advantage.

In this how-to we will be sending an email with an image we get from a php script after running some fishy code. What you'll need

Step 1: What Exploit Development Is and Why Should I Be Interested on About This Topic

OK, In my last Tutorial we made a Server for sending Instructions to a Client. This time we will build the Client. Fire up your favourite Python environment and get the Code here.

As many of you know, processor's clock frequency improvement got stuck in about 2003, causing the origin of multicore CPU (and other technologies). In this article I'll introduce you on how to run code simultaneously in various processors (I suppose that all of you have a multicore CPU). When you write code without any parallel directive, it only executes in one CPU at the same time (see it below). OpenMP make simple to work with various cores (if not with all of them) , without so much heada...

Recently, I've been learning Ruby as a second scripting language. But one topic I never covered with the many lessons online were sockets. So I did some research and came up with a very simple client/server connection that sends a string over the socket.

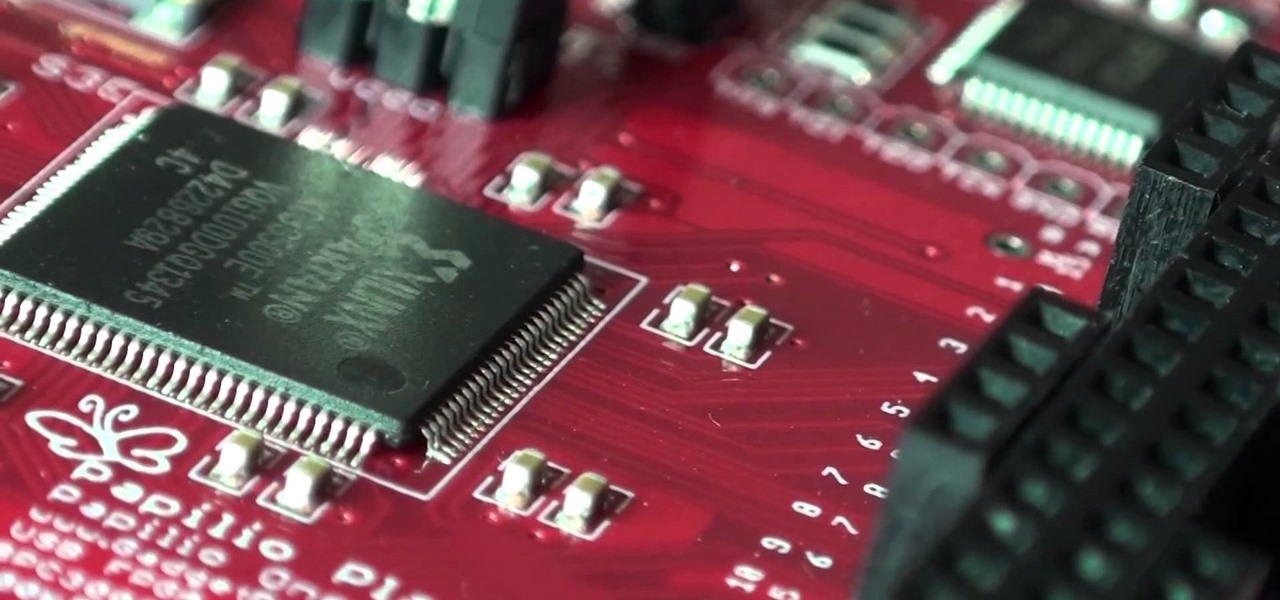
A FGPA is chip that is programmable with the computer to create circuit. It is a totally different type of programmable board compared to an Arduino for example. The Arduino will follow lines of codes to generate the necessary outputs. A FPGA won't however read lines of code, but it is a circuit itself. When the chip is programmed, a series of AND-ports, OR-ports and many others ports are linked together. The FGPA will increase the speed and the possibilities of your designs! I assume that by...