
News: Verizon's Envrmnt Team Opens Early Access to AR Design Easy App Creation Tool
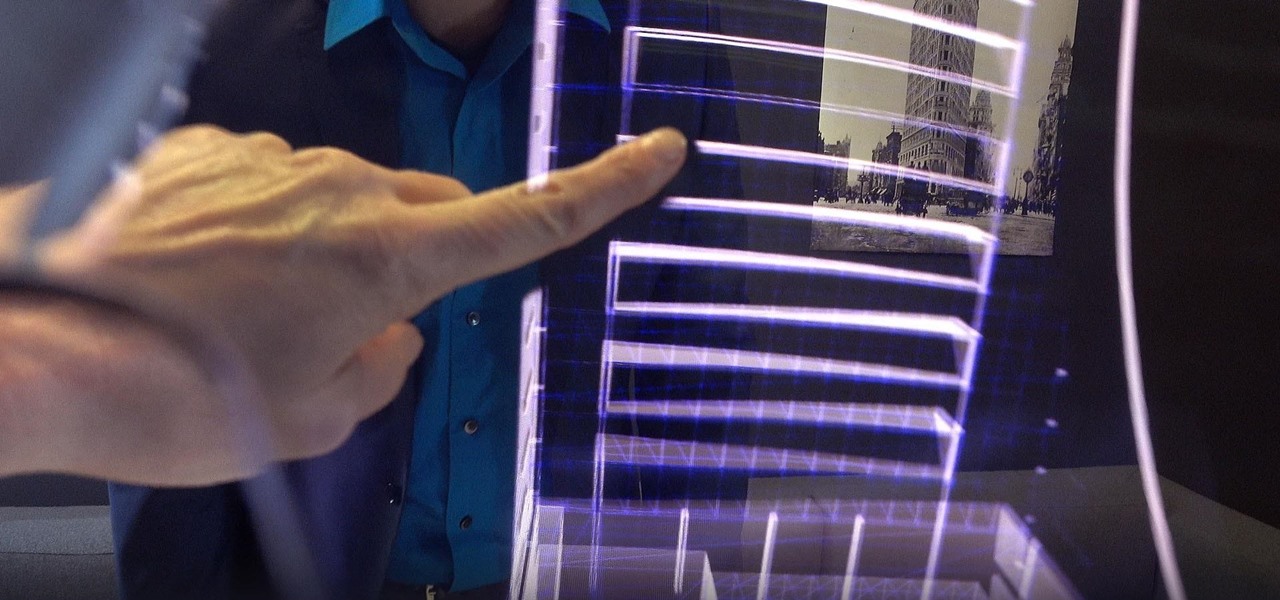
The augmented reality and VR arm of Verizon, Envrmnt, wants to make it really easy for anyone to create AR apps.


The augmented reality and VR arm of Verizon, Envrmnt, wants to make it really easy for anyone to create AR apps.

It's always a pleasure when your activity syncs across all of your devices. Herein lies another reason to use Samsung Internet — the app natively syncs with your open tabs on desktop Firefox. Anything you do on your computer can be easily accessible from your smartphone.

Netflix currently lets parents block content based on maturity rating, but it isn't a perfect system. Not all titles rated PG-13 are equal, for instance. That's why it's good news that Netflix is adding more controls for parents, by allowing account holders to bar individual movies and TV shows they deem inappropriate.

Eventually, even the most private company has to file its patents and unveil its tightly-held secrets, and Magic Leap is no exception.
Oreo, the latest and greatest Android OS, lets you enjoy a ton of new features such as app shortcuts and an improved keyboard. But thanks to a feature that's required of all phones that ship with Android Oreo out of the box, your S9 may be the first Galaxy phone to finally receive timely software updates.

The day has finally arrived — Samsung has unveiled the Galaxy S9 and S9+. Apart from minor upgrades, the two might not appear to be much different from last year's S8 and S8+, but that's not necessarily a bad thing. One feature that hasn't changed is the Galaxy's IP68 water-resistance rating. That's a great score, but it begs the question — what does that number really mean?

If you're an Android user, you're very likely jealous of your iPhone friends who have access to the wide, wonderful world of augmented reality thanks to ARKit.

Coinhive, a JavaScript cryptocurrency miner, was reportedly discovered on the BlackBerry Mobile website. It was placed there by hackers who exploited a vulnerability in the site's e-commerce software that allowed them to anonymously mine cryptocurrency every time the website was viewed. There's no doubt Coinhive, an innovative mining method, is being abused and exploited by hackers in the wild.

Gboard is one of the best third-party keyboards available for iPhones, but you probably don't know everything you need to know about it to become a real Gboard pro and stop using Apple's stock keyboard for good.
By default, images embedded using external links will not automatically load in any emails that you get with ProtonMail. This is a security mechanism that can prevent malicious code from being executed on your system, but it can also be fairly annoying to have to manually load images in email after email.

OnePlus is on track to deliver Android 8.0 Oreo to its flagship users by Q1 2018. Open Beta 1 was released for the 5T in late December, and we just received Open Beta 2. But this update isn't just tweaks and bug fixes, OnePlus has included a few new features to enhance the Android experience.

One of the most overlooked components of talking about augmented reality and virtual reality is getting people to actually use the hardware and software associated with these platforms.

Many guides on Null Byte require using the Secure Shell (SSH) to connect to a remote server. Unfortunately for beginners, learning to use SSH can become a confusing mix of third-party programs and native OS support. For Chrome OS users, using SSH is even more difficult. We'll fix this by using the Chrome Secure Shell to establish an SSH connection from any device that can run a Chrome browser.
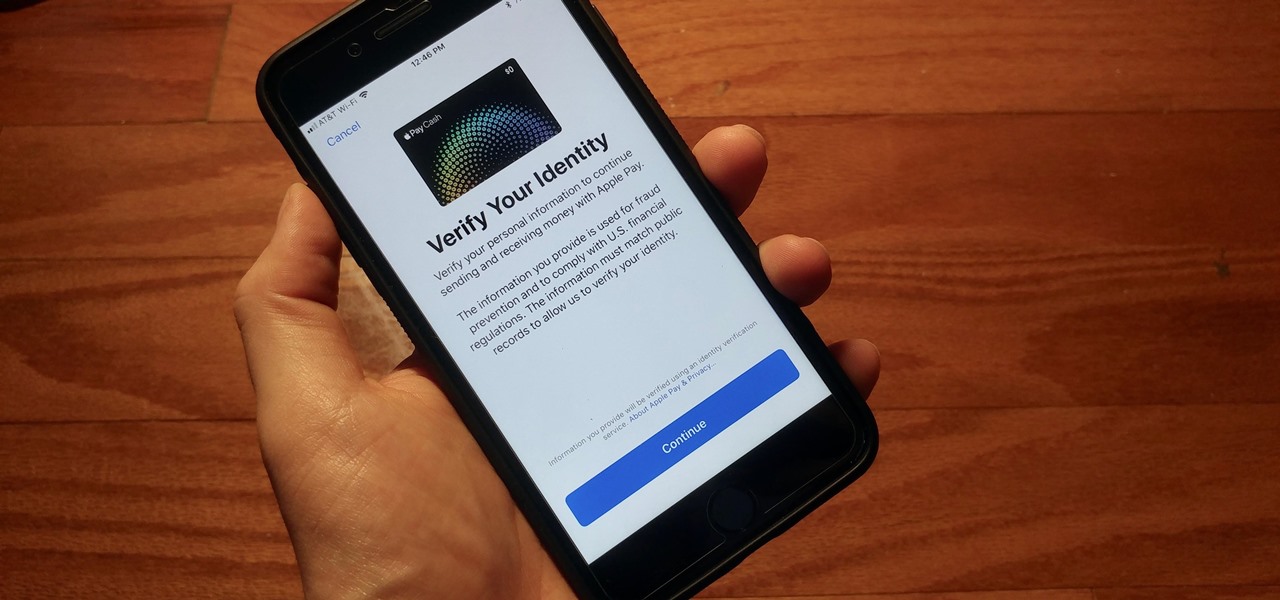
With iOS 11.2's introduction of Apple Pay Cash, you can send and receive money to others directly through iMessage, using the convenience and security Apple Pay is known for. However, if you want to make sure your efforts go uninterrupted, you'll want to make sure you verify your identity with Apple.

OpenBSD implements security in its development in a way that no other operating system on the planet does. Learning to use the Unix-like operating system can help a hacker understand secure development, create better servers, and improve their understanding of the BSD operating system. Using VirtualBox, the OS can be installed within a host to create a full-featured test environment.

There was a time when building a website required coding knowledge. Eventually, software came along that made the process easier, and then services like Squarespace made it dead simple for even a technical novice to design a website.

A mention of the deep web can bring to mind images of drugs, hackers, and other criminal activity. Despite the presence of these elements, the Tor network is a valuable tool for preserving privacy and anonymity. And browsing the deep web and any hidden services can be as simple as downloading the Tor Browser.
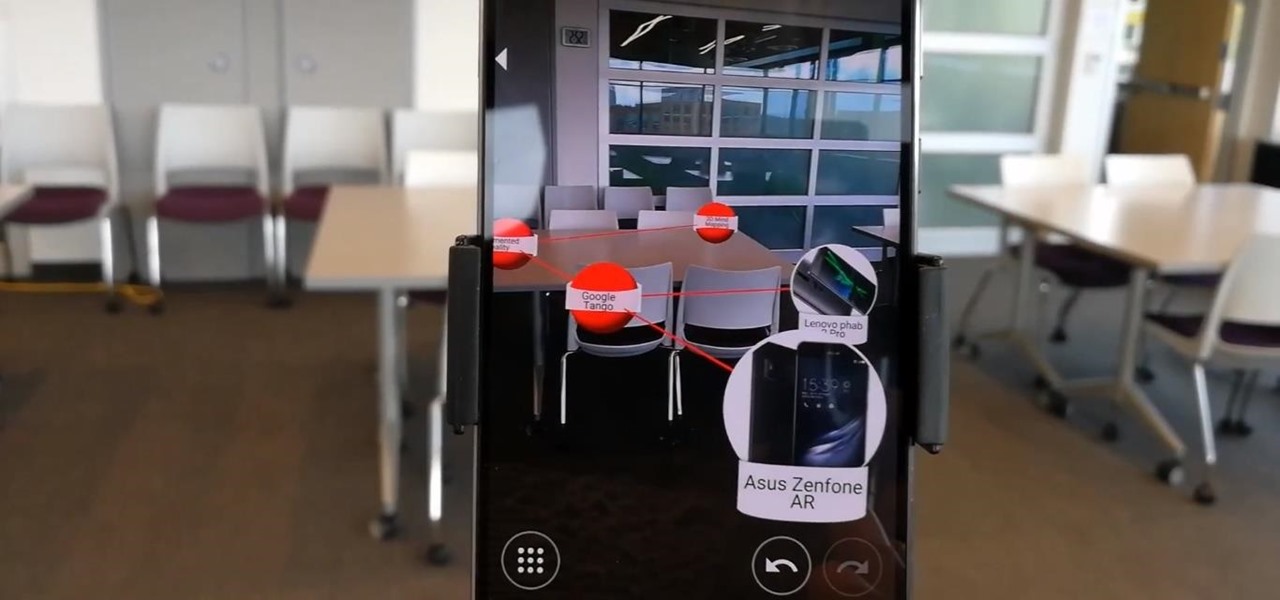
When Google announced its ARCore augmented reality toolkit for Android as its answer to Apple's ARKit for iPhones and iPads, the question from many observers was, "What about Tango?"

When we are building programs that communicate over a network, how can we keep our data private? The last thing we want is some other lousy hacker sniffing our packets, so how do we stop them? The easy answer: encryption. However, this is a very wide-ranging answer. Today we're going to look specifically at how to encrypt data in Python with dynamically generated encryption keys using what is known as the Diffie-Hellman key exchange.

Armis Labs has revealed eight vulnerabilities, called "BlueBorne", which put 5.3 billion Android, iOS, Windows, and Linux devices that use Bluetooth at risk. With it, hackers can control devices, access data, and spread malware to other vulnerable devices through networks. In this post, we will learn about the vulnerabilities, then look at how to find devices that have them.
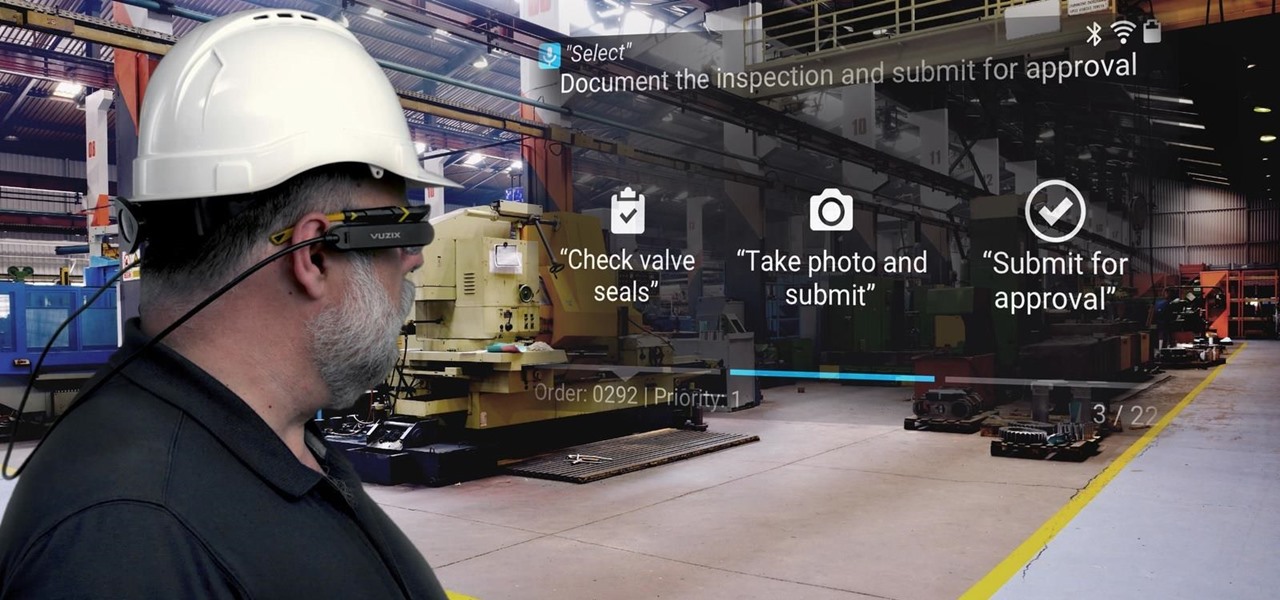
Augmented reality software maker Upskill has released the latest version of their Skylight platform, adding a number of new tools to ease implementation and improve functionality for enterprises, including a new application builder.

Avegant Corporation has begun shipping display development kits based on its light field technology that other companies can use in their augmented and mixed reality devices.
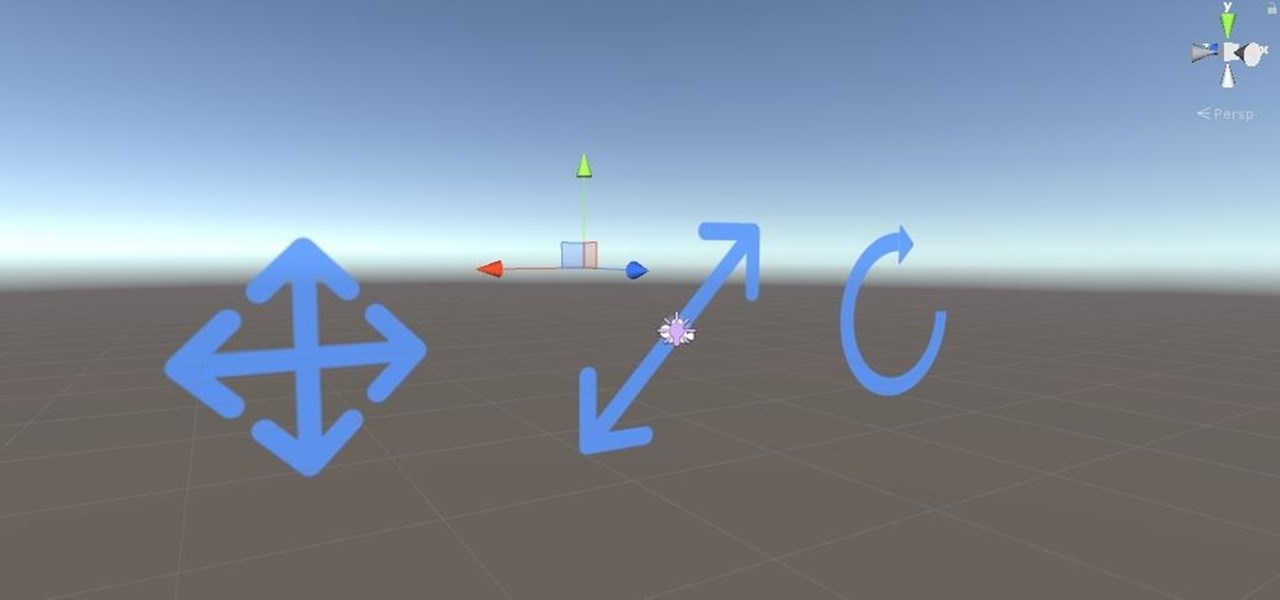
Alright, calm down and take a breath! I know the object creation chapter was a lot of code. I will give you all a slight reprieve; this section should be a nice and simple, at least in comparison.

As we have seen previously with the likes of SethBling's Mar I/O videos and other examples, video games seem to be a great source for training AI neural networks. Augmented reality and machine learning are part of a collection of technologies that seem to be growing toward a point of maturity, and that will likely cause them to be intertwined for the foreseeable future. As developers, machine learning will definitely change the way we create software in the coming future. Instead of going lin...

Every time you make a call or send a text, you're giving the recipient your phone number. This can be quite the security vulnerability, opening yourself up to scammers, spammers, and the feds. In this how-to, we'll look at what a burner phone is, why you might want one, and how to get started using a free second phone number on your regular smartphone.
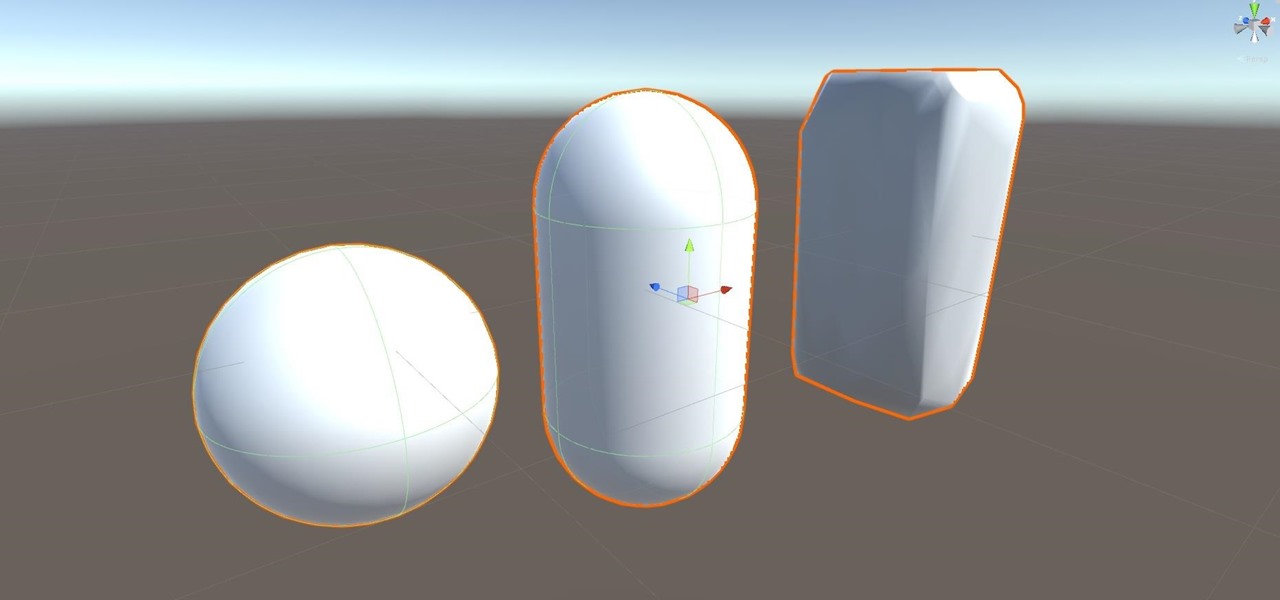
Alright, let's dig into this and get the simple stuff out of the way. We have a journey ahead of us. A rather long journey at that. We will learn topics ranging from creating object filtering systems to help us tell when a new object has come into a scene to building and texturing objects from code.
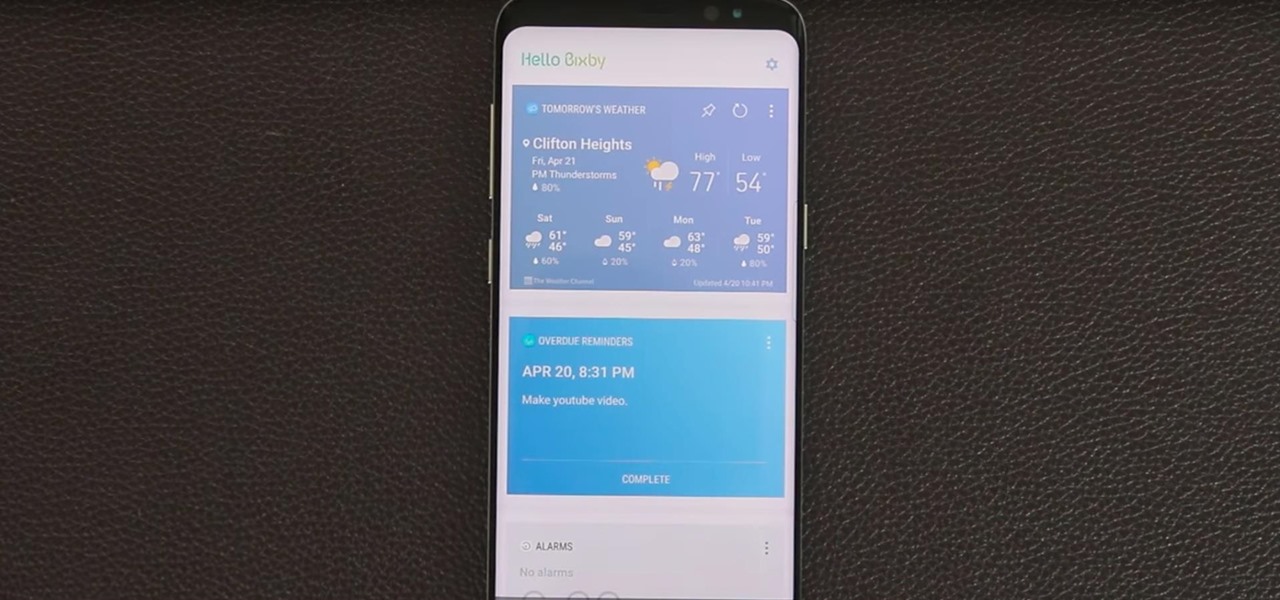
Bixby — Samsung's voice-activated digital assistant — has been delayed again because the software still can't recognize English. Although Samsung claims Bixby can execute 15,000 tasks, it appears it's inability to master English is a major obstacle that's preventing its full release in the United States.

A new cross-licensing patent deal signed by Nokia and Chinese smartphone maker Xiaomi will bring increased collaboration between the two companies. One area of focus in which both Nokia and Xiaomi have already agreed to work together is augmented reality.

Your favorite music-streaming app is taking artists from its popular RapCaviar playlist on tour to five major US cities. That's right, put down your smartphones and pick up your credit card because these tickets are going to sell fast.

The Galaxy S8 and S8+ come equipped with all of the hardware needed to access live FM radio, but this feature was never really advertised or even spoken about. Thankfully, though, all you need is an app to enable it.
While two augmented reality companies were recently recognized for their innovative technologies, other companies have turned to augmented reality to innovate in their respective fields. Over the past week, use cases have ranged from selling snacks and video games to raising awareness for public health issues.

Pokémon GO has been making the news since it was released last summer. But throughout the past year, the core gameplay has remained mostly the same. We're learning today that is about to change, as Niantic is gearing up to release a major update for the popular AR game.

Apple CEO Tim Cook's June 5 announcement that the company is developing autonomous software should have some companies rattled. At least, Morgan Stanley thinks Tesla should be.
Android O doesn't have an official code name yet, but it's certainly got plenty of cool new features. The OS won't officially debut until Q3 2017, but we've gotten our hands on some of the updated stock apps thanks to the Android beta program.

Waymo's transfer of its driverless car know-how to commercial trucks will likely pose few challenges for the self-driving unit of Alphabet, which owns Google.

The Augmented World Expo (AWE) is upon us, and that means it's time to get excited about all the awesome next reality things to come.

Firefox Focus has been out for iOS for a while now, so it's about time Mozilla began porting the app over to Android. It's an amazingly private browser that protects you from trackers and ads when you're surfing the web. It blocks a wide range of online trackers, erases your browsing history, hides passwords, and deletes cookies. This essentially means ads won't be able to follow you around, in the sense that you won't see ads related to your last ten searches on Google.

Google loves to play games. That's just what they did when they went ahead and teased us with a few Android O hints after Reddit user Zitroney unlocked an Easter egg in a Google Creative Lab developer's app ShortStories.

The hunt for the mixed reality use-case that wins over consumers' hearts and creates a critical mass is a problem every developer would love to solve. Not only would they find themselves rich and famous seemingly overnight, but they would also end up making one of the various possible hardware solutions a viable place for other developers to put their time and energy.
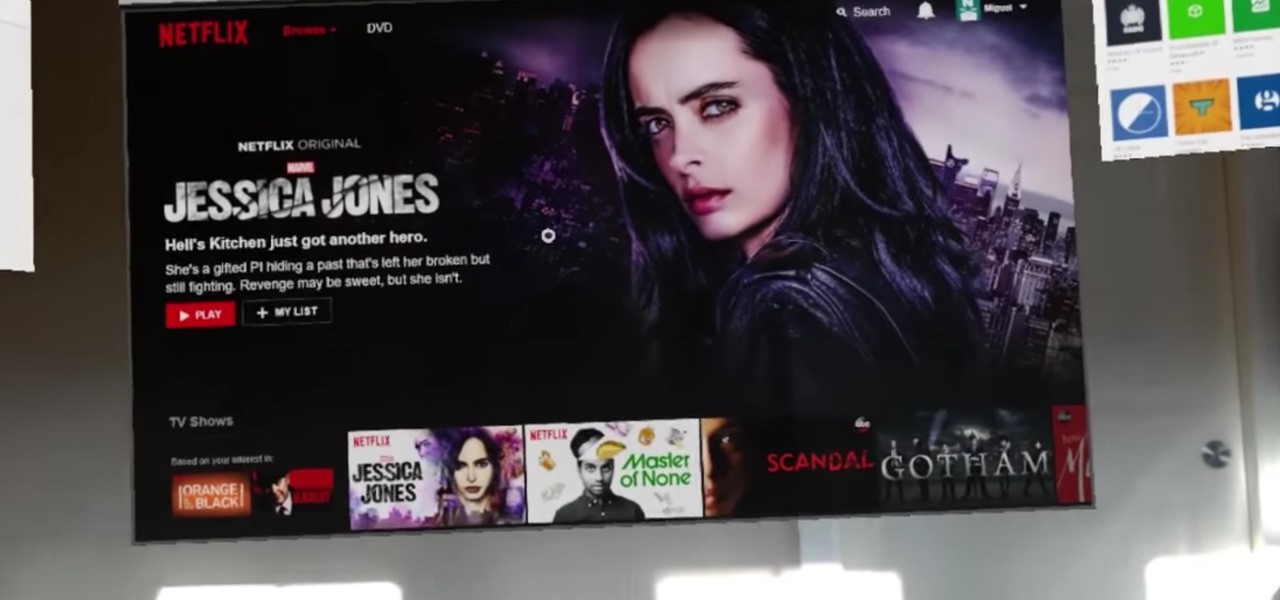
Alright, fellow HoloLens code wranglers, load up your word processor because it's time to spruce up your résumés. According to a report by Variety, Netflix is looking to hire a new Senior Software Engineer — and Windows and HoloLens were mentioned as an end point.