Whether you're new to Adobe Photoshop or a seasoned graphic arts professional after a general overview of CS5's most vital new features, you're sure to be well served by this official video tutorial from the folks at Adobe TV. In it, you'll learn how to use the new Protect Detail feature in Photoshop CS5 to prevent artifacts in your digital images when using the Sharpen tool.
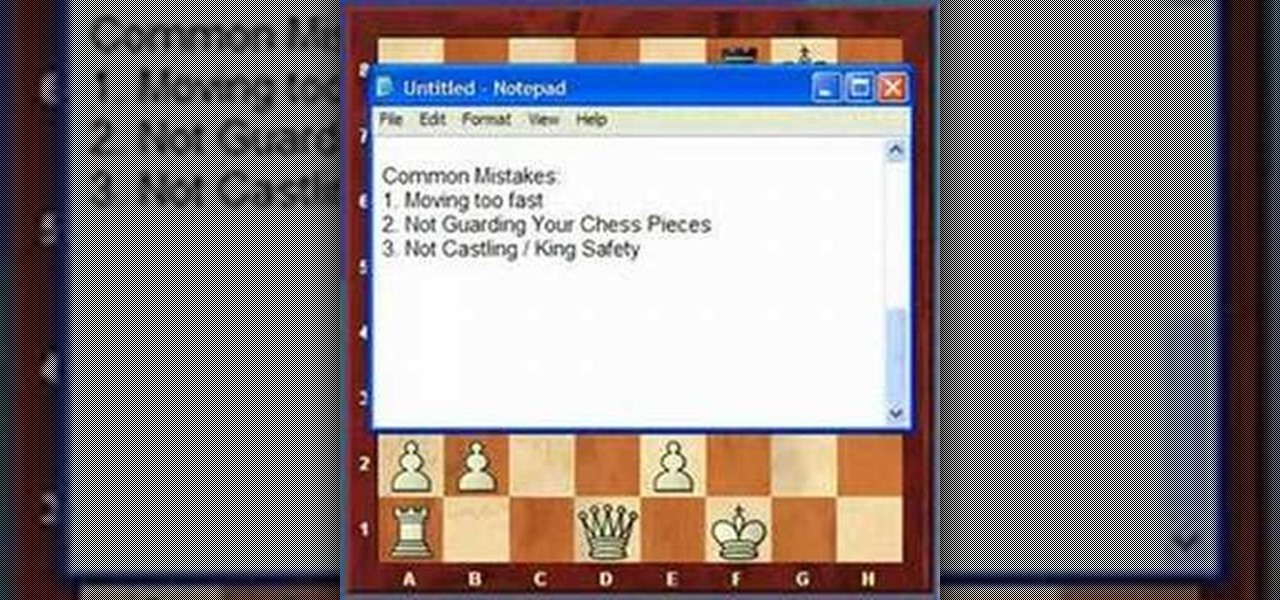
I bet you just can't win a game of chess, can you? You're probably rushing yourself, or not protecting your pieces. Well, in this video, you'll see how to avoid the common chess mistakes, such as moving too fast, giving away chess pieces for nothing (or not protecting your chess pieces), and not castling.

Aircraft equipped with ADS-B are constantly shouting their location into the radio void, along with other useful unauthenticated and unencrypted data. In this guide, we will make an ADS-B receiver using a Raspberry Pi with a software-defined radio (SDR) dongle, which we can use to track aircraft anywhere in real time.

While Android devices made by HTC, Samsung, and others have long utilized IR (infrared) blasters to offer remote control functionality, Apple has still yet to embrace it on iPhones.

After a week of teasing, ASUS unveiled its Android Wear-powered ZenWatch at IFA 2014. The ZenWatch packs style and performance with a custom ZenUI, Remote Camera, and over a 100 choices of built-in watch faces.

Lenovo didn't have as much to show off at IFA 2014 as Samsung and Sony did, but its new Android-powered Tab S8 is certainly worth a look.

Once you've patched all of the cracks and potholes in your home driveway, it's time for protecting it from further damage. Sealing your driveway will protect from further ghastly and bothersome cracks and potholes. Lowe's knows what works best— QPR's Professional Grade Driveway Sealer.

In this video, we learn how to use the reverse hyper to protect and rehab the back. First, you need to lay down on the machine correctly. Make sure your core is out and your arms are holder the levers. Now, lift your legs up on the straps and slowly lower them down. Continue to do this as you work out, this will result in a great work out in just a few reps. As you continue to do this you will be able to do heavier weights. This will help protect your back from injury and get it back into shape!

In this video, we learn how to protect your privacy while using Twitter. Your personal information can get stolen in an instant with the internet. With Twitter, when you are doing updates showing where you are and what you are doing, someone could try to find you and potentially create harm to you. To help you avoid situations like this, you need to go to the security settings of your Twitter account. When you go here, you can change the account so that it only allows people you want to follo...

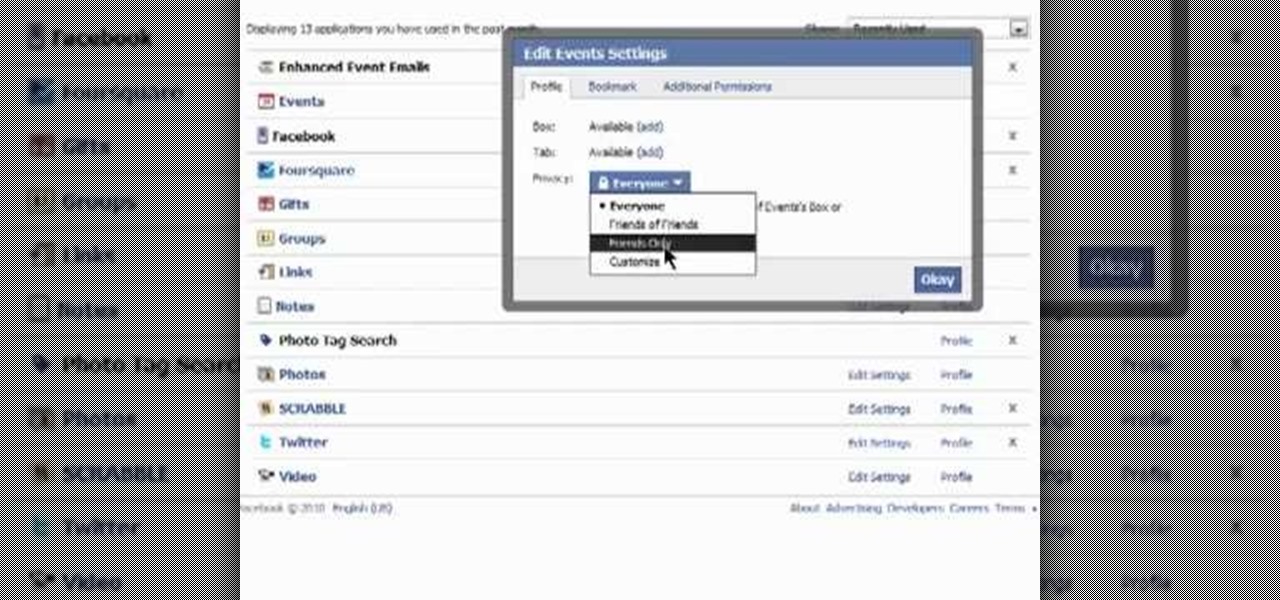
Need some help figuring out how to protect your privacy when using Facebook applications? It's easy! So easy, in fact, that this Facebook user's guide can present a complete overview of the process in about a minute's time. For more information, including detailed, step-by-step instructions, watch this guide.

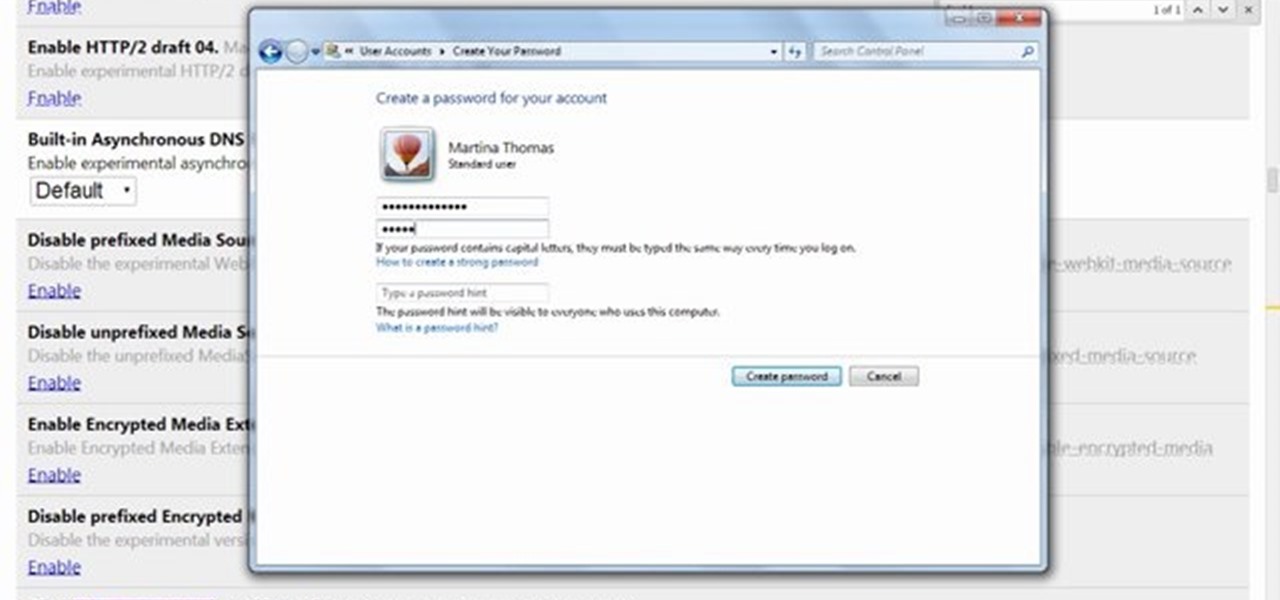
Picking a secure password is not only important for protecting your privacy, it's also very easy. Provided, that is, that you know how to go about it. This free video lesson from CNET TV will walk you through the process. For more information, and to get started creating and using high-security passwords yourself, watch this video tutorial.

Rain and snow will ruin your touchscreen device in no time. Want to protect it without spending a fortune on a bulky waterproof case? This video demonstrates a quick-and-easy expedient—a waterproof plastic bag!. For specifics, and to get started making your own plastic bag phone case, watch this handy rainy-day how-to.

Identity theft can happen anywhere, even in social networking. Why are we so careful when using our credit cards online but not when we sign on to Facebook?

Protect your email account from would-be hackers and crackers with this free video tutorial from the folks at MacMost. If you have a Gmail, HotMail, Yahoo! Mail or other web-based email account, this video is much recommended. For more information, and to secure your own online free email account, watch this helpful guide.

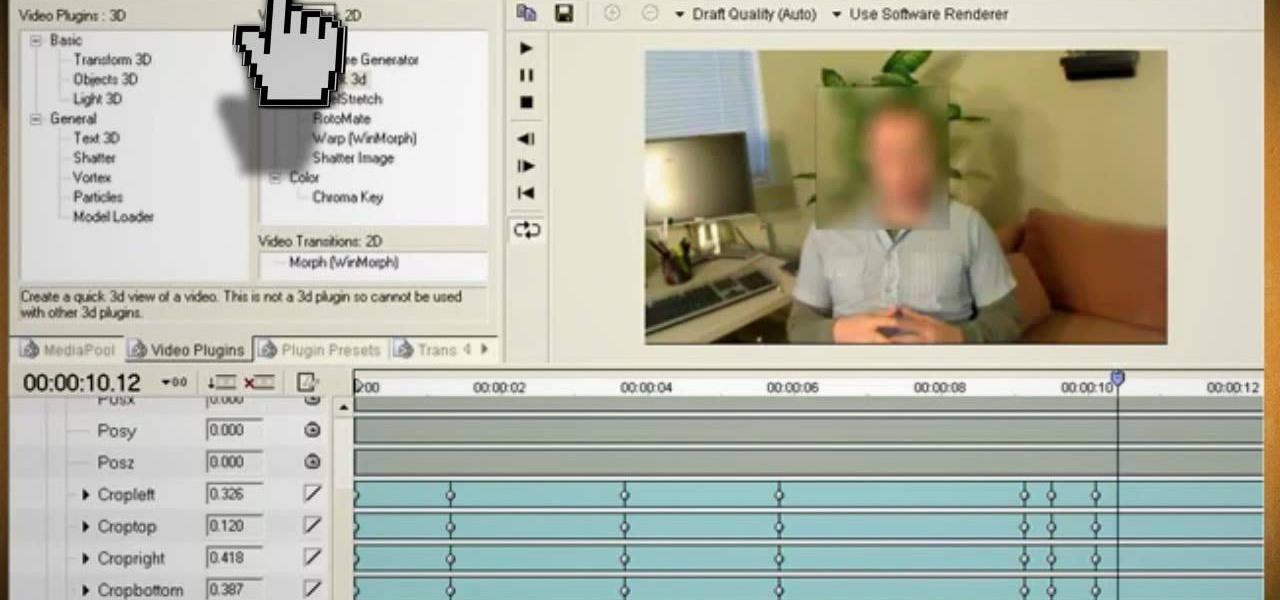
Watch this video and learn how to protect your identity on the internet. This clip will help you learn how to blur out your face and alter your voice when posting videos on the web, where your identity is an important secret. Stay anonymous while portraying your opinions. This software can also be used to avoid release issues with strangers in the backgrounds of your videos. Preventing passers by from having there picture posted with your opinions opening you up for legal action. This can als...

Ever have the problem of people messing with your word documents? This guy shows you the solution by telling you how to create password protected encrypted word documents. The process starts with your open file. Clicking on save as... and in the popup window clicking the tools button in the bottom left corner and clicking general options. There it shows you text entry boxes, one for setting a password to open the file, another to set a password for rights to modify the file. Enter your passwo...

Sick of damaging your hair with all the products and flat irons? Those products don't have to cause your hair damage if used correctly. In this two-part hair video tutorial, learn how to blow dry and flat iron long hair in a way that does not cause damage. Blow dry your hair and minimize the heat damage and breakage by following the tips in these two videos. Shampoos & conditioners are are also gone over, as well as how to use a flat iron minimally to get the results you want, with less damage.

Using blue tape and a dental bib during tattooing to protect a portable tattoo armrest from ink and blood. The process of protecting the armrest is simple. This process would prevent ink from being transferred to another person or even onto their clothes. Using the dental bib you place it over an armrest and use blue 3m tape to secure the dental bib. Once this is done you are ready to start tattooing. Very cost effective and efficient way to protect an armrest and others.

Duct tape is versatile and can be used for anything. But did you ever imagine that it can be used for making a book cover? Protect your books with sturdy duct tape. This tutorial shows you how to make a general book cover for a paperback using duct tape, but the process can be extended to cover any type of book. Protect all your books from damage with duct tape.

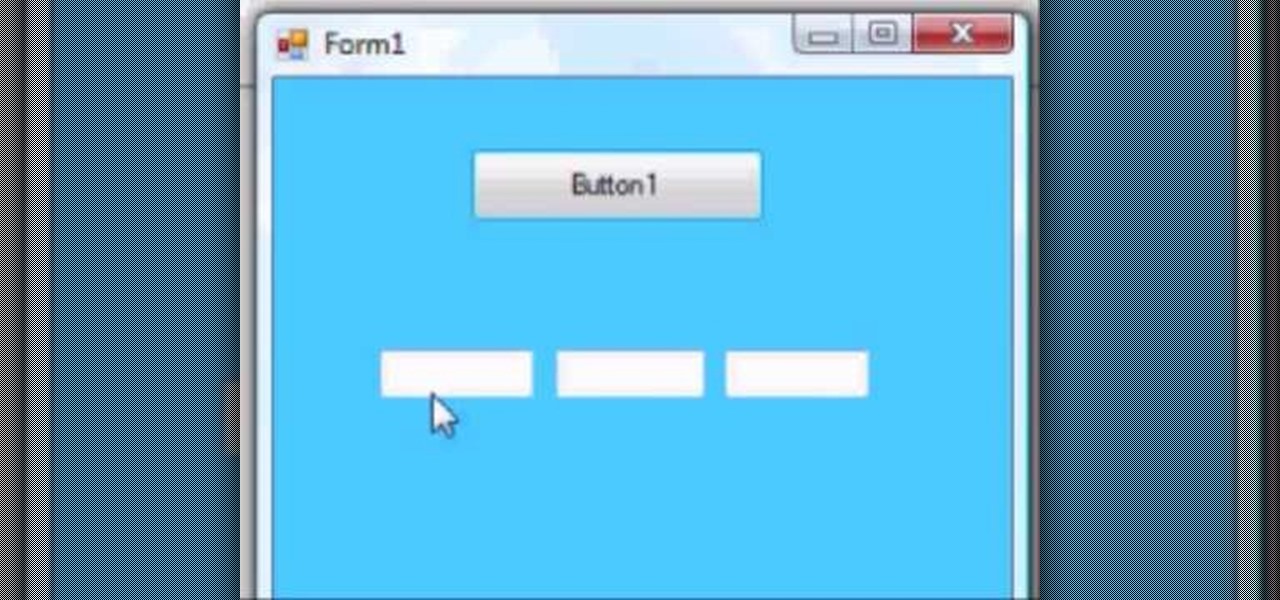
This VB.Net tutorial teaches you some tricks with duel forms and how to do create very basic password protected applications.

Frost is in the air. If you have tender plants like basil, pepper or impatients when that cold weather comes it will zap those plants. Often, if you can get through those first couple frosts, an Indian summer, that can last weeks and weeks, will follow. If you can protect your plants during this time you can have blooms for much longer. There are several ways to protect your plants. You can use a traditional device like a glass cloche. The nice thing about them is they are decorative and will...

To combat their poor coverage in rural areas, T-Mobile spent nearly $8 billion on 600 MHz spectrum in 2017, which was converted to LTE Band 71. With such a low frequency, the signal can travel further, providing LTE speeds to more Americans. But your phone also has to support this frequency, and so far, only a handful do.

Traditional media institution The New York Times continues to break new ground in its augmented reality news coverage, this time with a 3D volumetric capture of model Ashley Graham.

This video will show you how to protect others from accessing saved password on Google Chrome. Saving account passwords in browsers are useful for time saving as well as threatening for malicious activity. This is dangerous for security. So you must protect your accounts detail from others to secure your browsing. Watch the video and follow all the steps carefully.

This video will show you how to protect Google Chrome password from others. If you don't protect them from others anybody using your PC could access all your account detail. Now you can realize this is dangerous. Watch the video and employ the technique in your PC.

In this video, we learn how to protect yourself and your mattress from bed bugs. These bugs live in your bed and hide anywhere in your home and even hotels. To see if you have them, you will see blood stains on your mattress and look on your skin for any bites you may have. If you suspect you have them, you should call a professional to help take care of the problem. Check the edges and corners of your bed to see if you have been infested with bed bugs, and look at the label as well. Be caref...

There are many threats to be wary of when playing Terraria. If you'd like to be able to feel safe from a couple of them, watch this video and learn how to protect your house during Red Moon events and Goblin Invasions.

As you may know, your iPhone stores data on your location from time to time. If you'd rather that information be kept private, watch this video for some helpful instruction on how to protect your location information. Encrypt the information being gathered by iPhone tracker.

Even if there's a giant block of obsidian, you can figure out a way to exploit a glitch that will let you easily break into it. You're also shown a way to easily break into protected chests on shared servers in Minecraft.

Learn how to password protect your Motorola Droid Google Android smartphone. Whether you're the proud owner of a Froyo Motorola Droid or are just considering picking one up, you're sure to be well served by this video guide. For more information and detailed step-by-step instructions, watch this phone hacker's how-to.

If you have a big beautiful lawn and live somewhere with cold winters, you probably already know about how to winterize your lawn and how doing so can protect your lawn in the winter and make it grow better in the spring. If you don't, watch this video.

If you live somewhere with harsh winters, you know that they can be hell on your garden and the flower pots therein. Watch this video for tips on protecting different kinds of flower pots from the elements during the winter.

During the winter and freak weather events in spring and fall your garden can take a beating from frost and excess cold. Watch this video to learn how you can protect your plants and flowers during the cold so they are healthy and ready to grow when the weather improves.

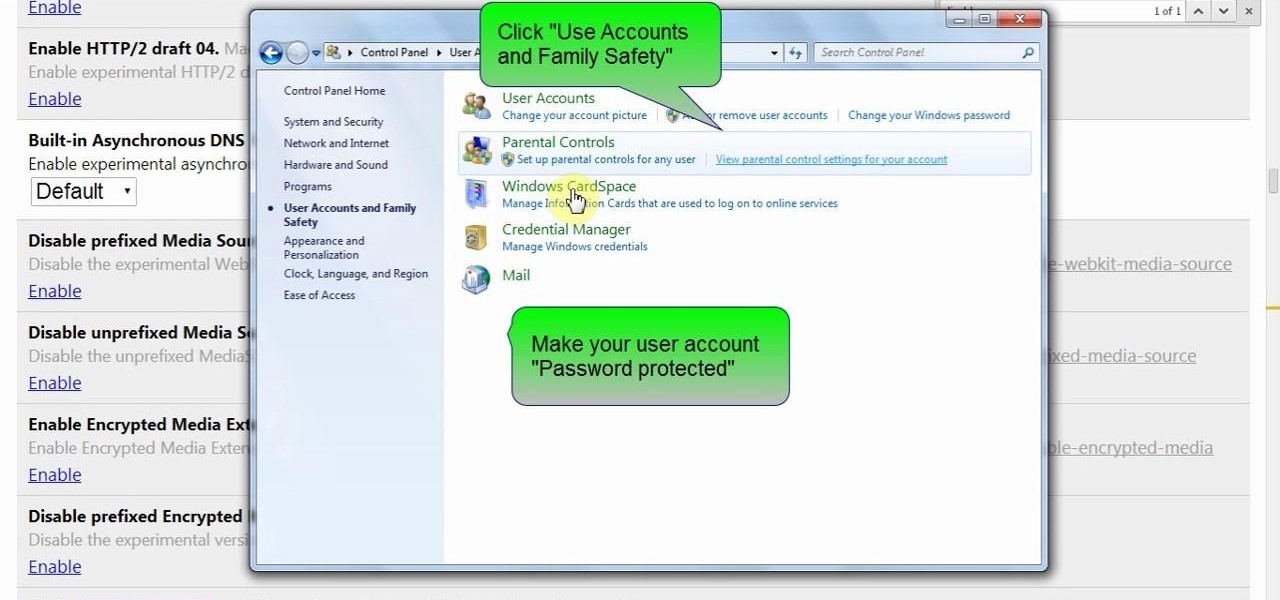
In this clip, you'll learn how to secure a new Microsoft Windows desktop or laptop computer. For more information, including a complete demonstration, and detailed, step-by-step instructions, as well as to get started protecting your own new Microsoft Windows PC, take a look.

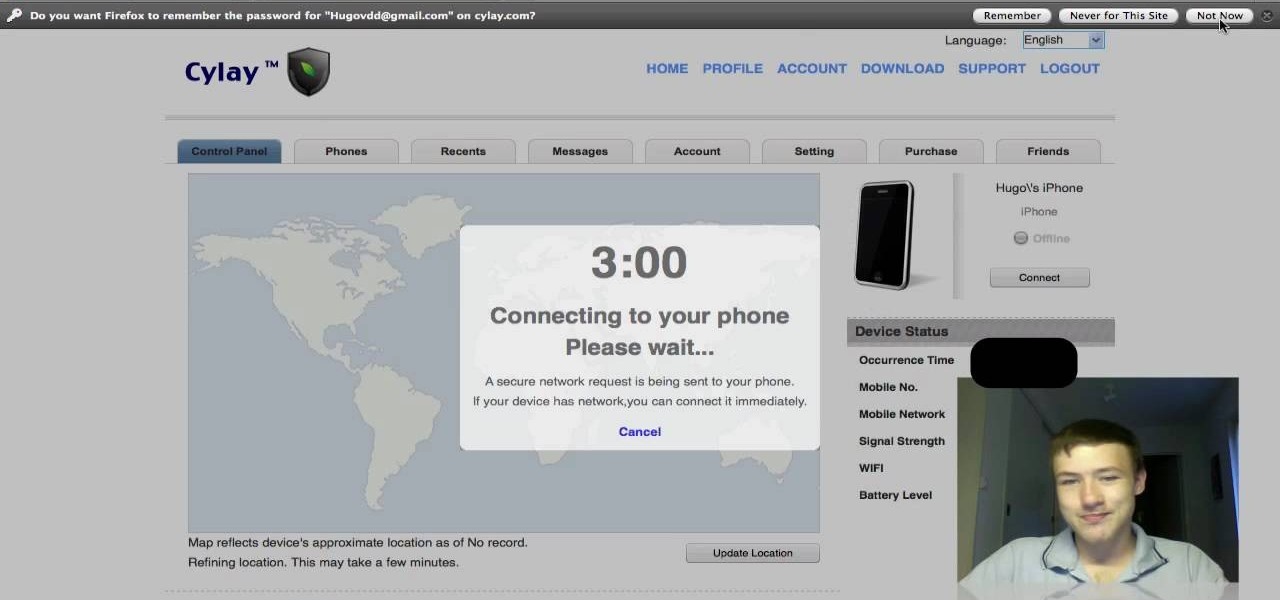
This app will only work on Apple devices that have already been jailbroken. Once you have, you can set up an account with Cylay. And once you have an account with Cylay, you can protect your phone or mp3 player against theft.

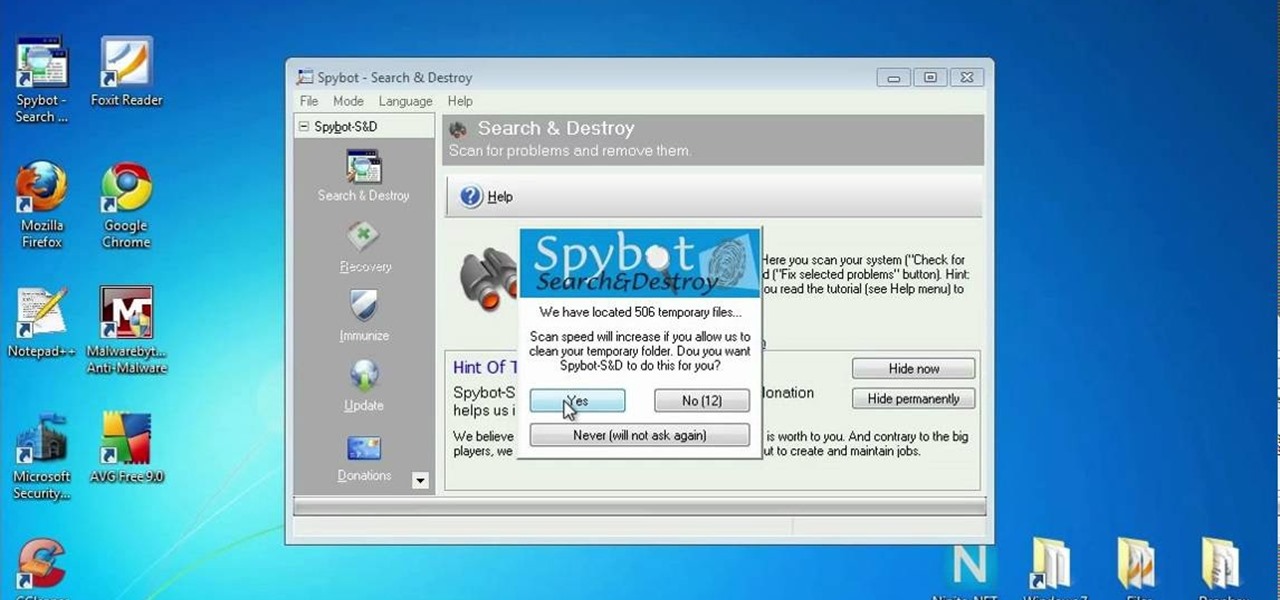
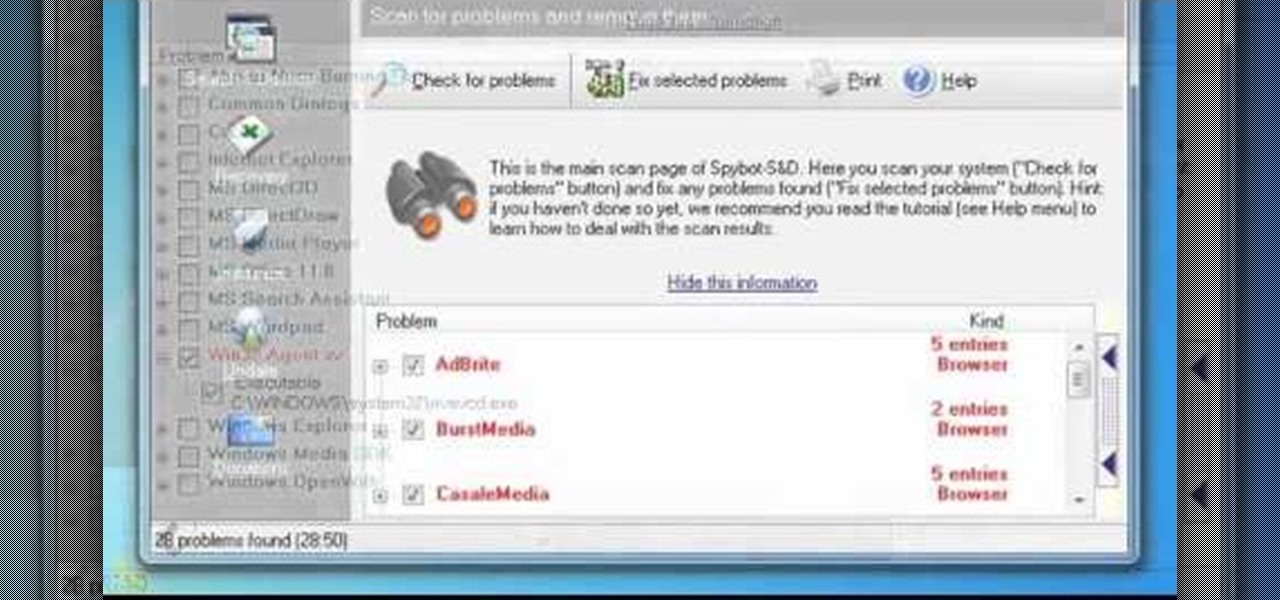
In this clip, you'll learn how to use the free Spybot Search & Destroy tool to protect against and remove malware on a Microsoft Windows PC. For more information, including detailed, step-by-step instructions, and to get started using Spybot on your own Win PC, take a look.

Looking for an easy way to protect your privacy when using Google Search? With the right habits, it's easy. So easy, in fact, that this home-computing how-to from the folks at CNET can present a complete overview of the process in just over a minute. For more information, including detailed, step-by-step instructions, take a look.

In this clip, you'll learn how to use the Backtrack 3 Linux distro and Aircrack-ng WiFi security app to crack the password to a WEP-protected wireless network. The process is simple. For more information, including step-by-step instructions, and to get started testing the security of your own WiFi networks, watch this hacker's how-to.

Interested in finding out just how secure your WEP-protected wireless network is? Let this video be your guide. It's a simple process and this home-networking how-to will teach you everything you'll need to know. For specifics, including detailed, step-by-step instructions, and to get started cracking WEP networks with BackTrack yourself, watch this helpful video guide.

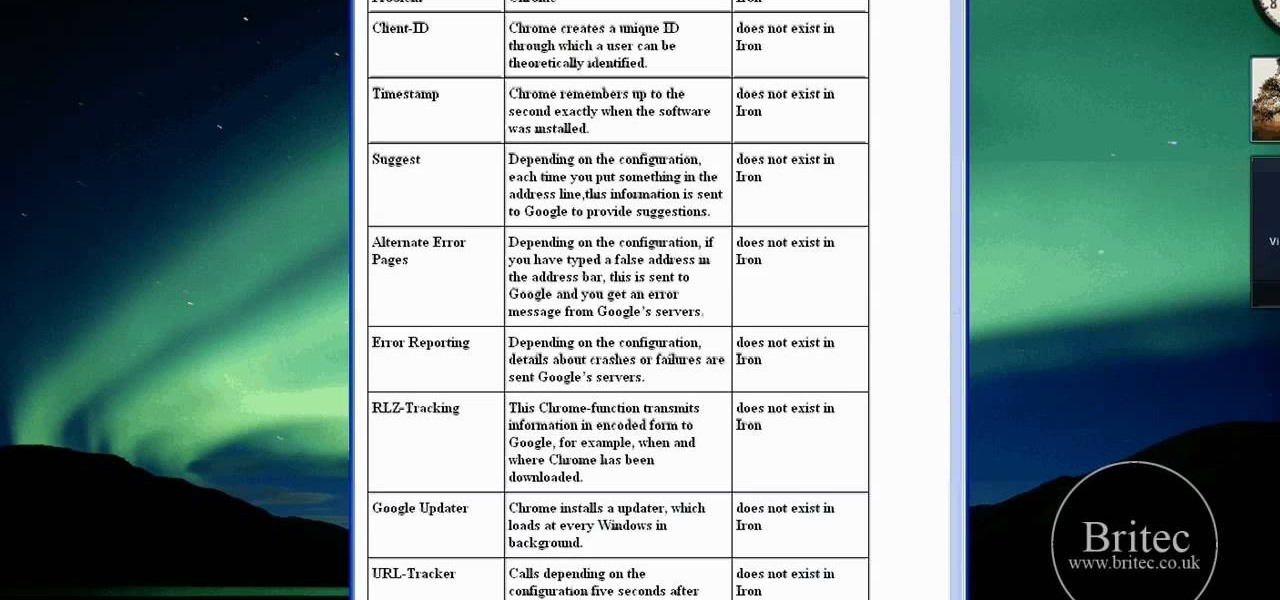
Interested in using Google Chrome but concerned about protecting your privacy while surfing the web? Meet Iron Browser, a secure but otherwise identical clone of the Google Chrome web browser. This clip from Britec will teach you where to find it, how to install it and how to get started using it.