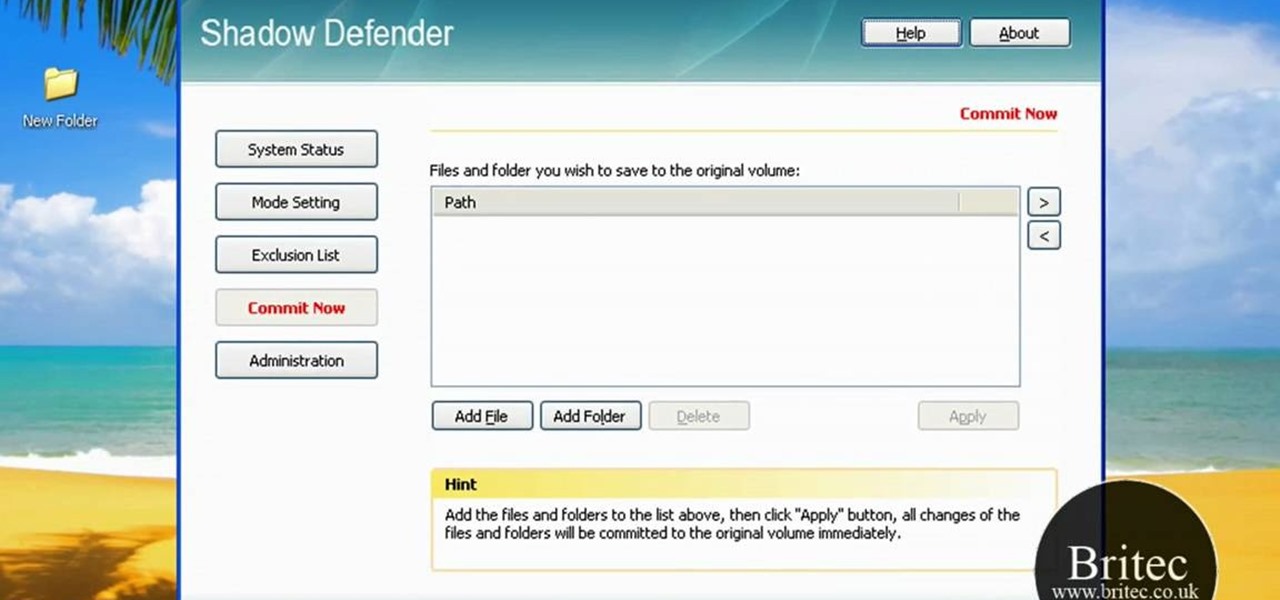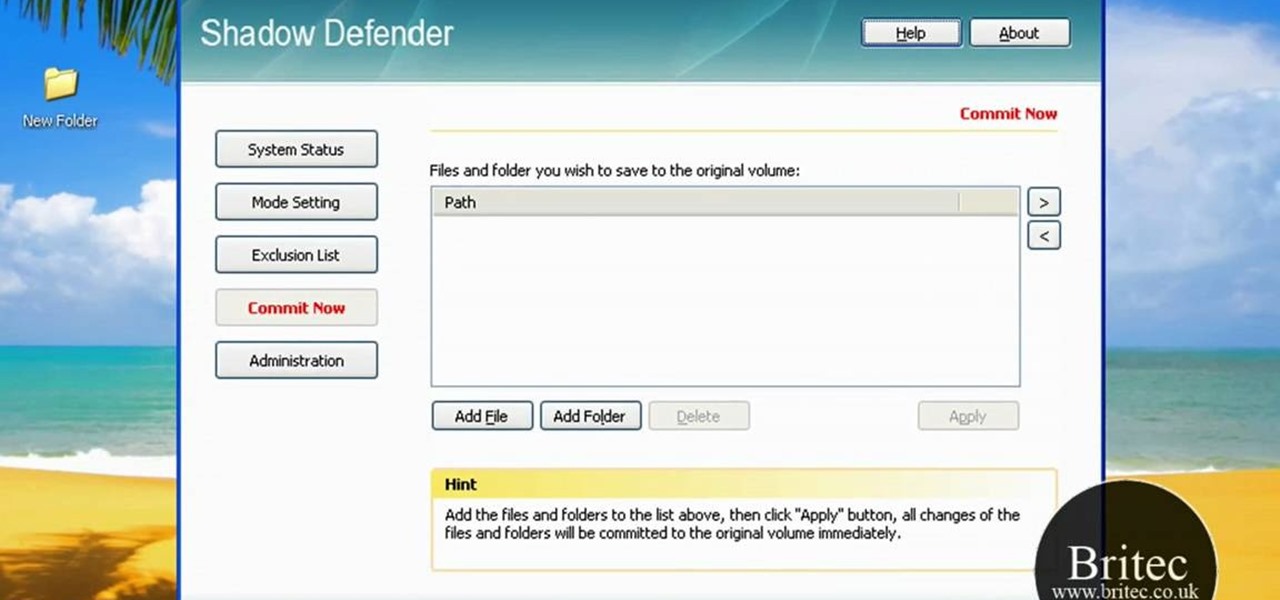
Looking for a security solution for your Microsoft Windows PC? With Shadow Defender, it's easy! So easy, in fact, that this home-computing how-to from the folks at Britec can present a complete overview of the process in just under ten minutes. For more information, including step-by-step instructions on how to get started using Shadow Defender to protect your own desktop computer or laptop, take a look.
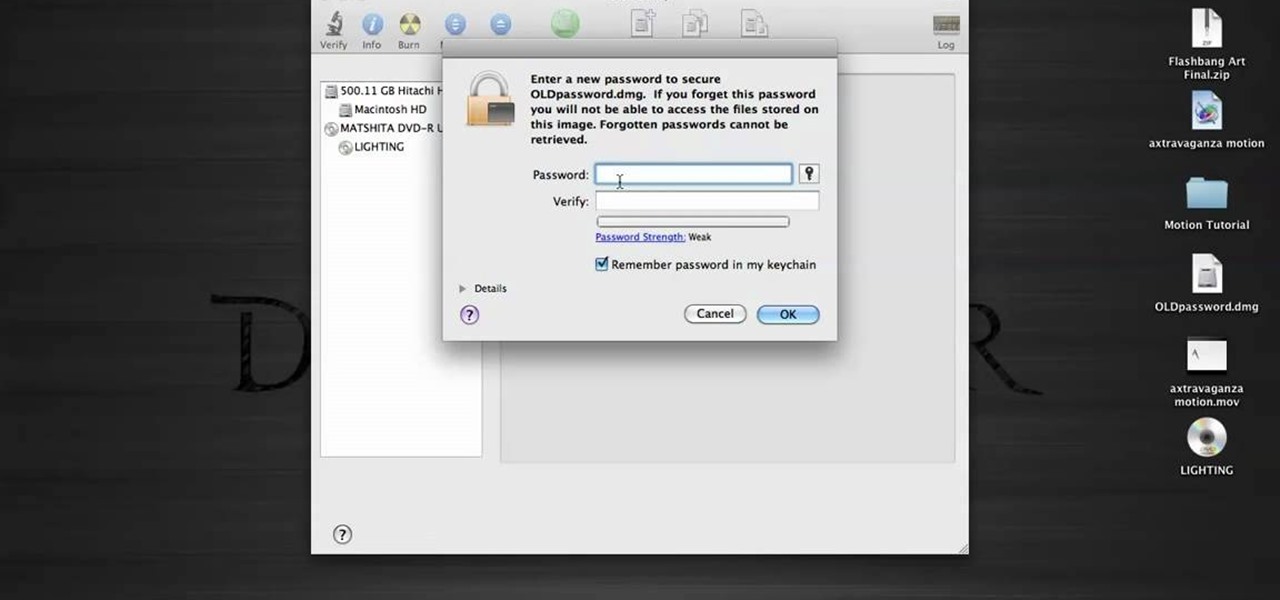
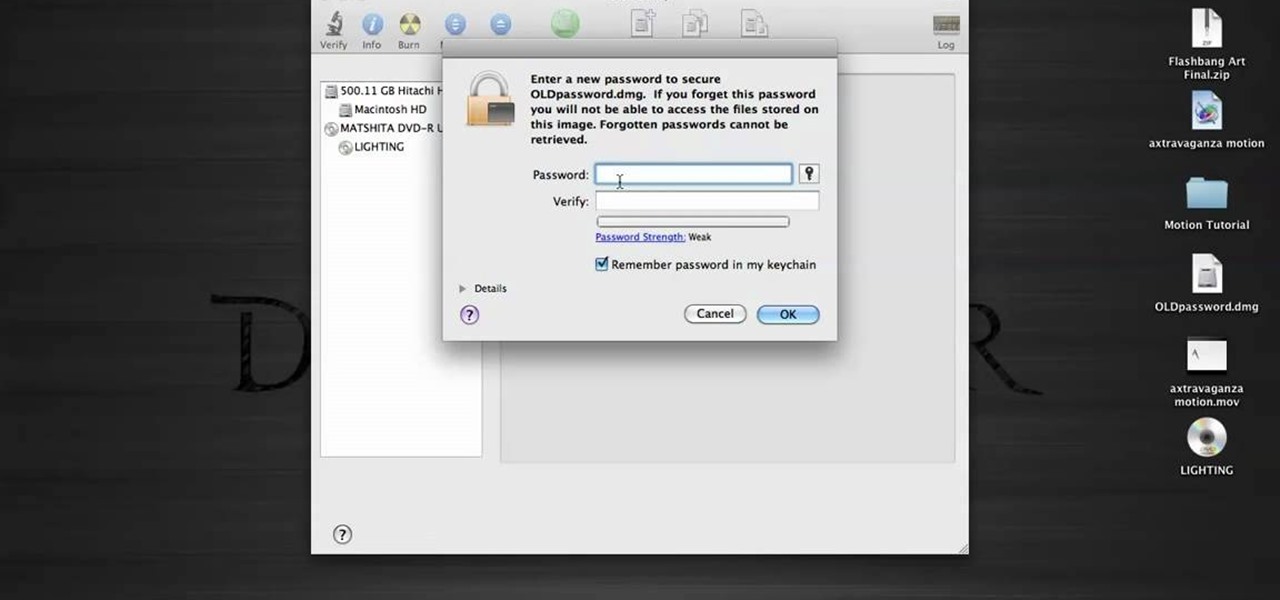
In this tutorial, we learn how to password protect a folder in Snow Leopard on your Mac. First, go to the finder and click on "utilities". Now go to "file, new, disk image from folder". Now, you can select the folder you want and then click "image". Make it a read/write folder so you still can edit the files and enable the encryption. Save this, then it will ask you for a password. Create a password and then verify it. When finished, uncheck the "remember my password", then click on "ok". Now...

If you're restoring an old vehicle, it's always important to make sure you take the necessary precautions for preventing any damage. In this particular video tutorial, you'll find out how to protect your door panels on a classic VW Beetle Bug without any problems. So good luck, pay attention, and enjoy!

My Blackberry TV demonstrates how to protect your Blackberry device with a password. Protecting your Blackberry with a password will help to stop people from accessing your personal information on your device. From the home screen, press the Blackberry menu key. Then, select the options choice. Next, scroll down to the password choice on the options menu. Select password and then select the set password button on the password screen. Enter your desired password and then press the enter key. V...

As any SLR or DSLR owner knows all too well, the price of lenses can often approach or even exceed the cost of your camera. As such, it's important that you take the necessary precautions to protect them. With this free photographer's guide, you'll learn about using UV (that is, ultra-violet) filters to protect your single lens-reflex camera lenses from sun damage.
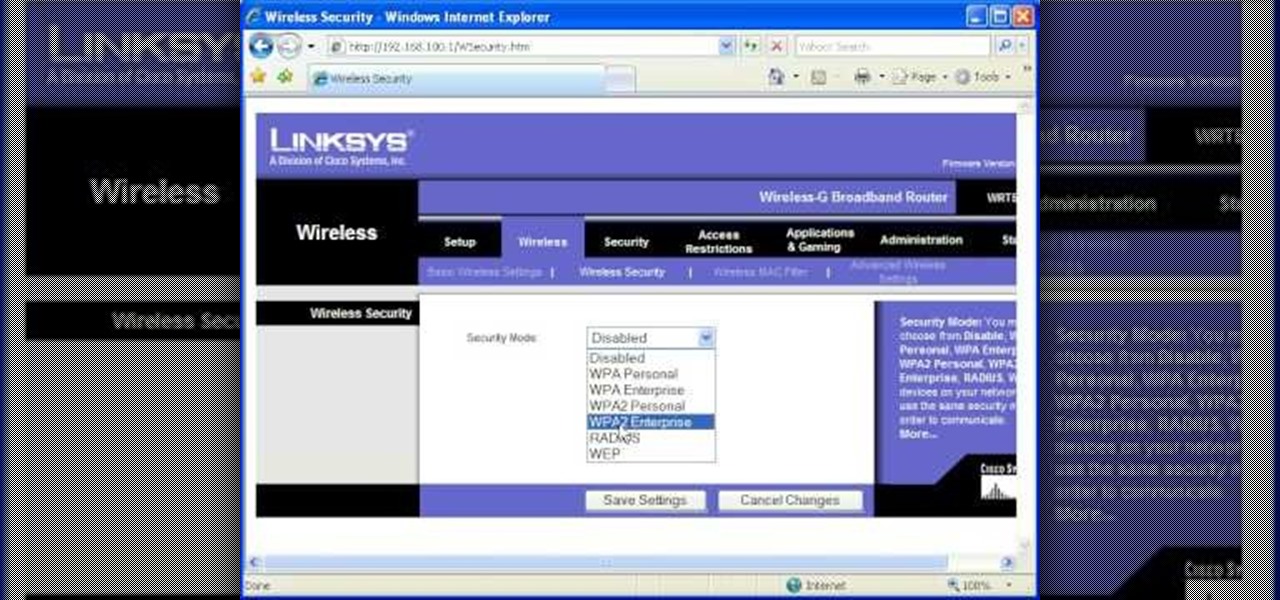
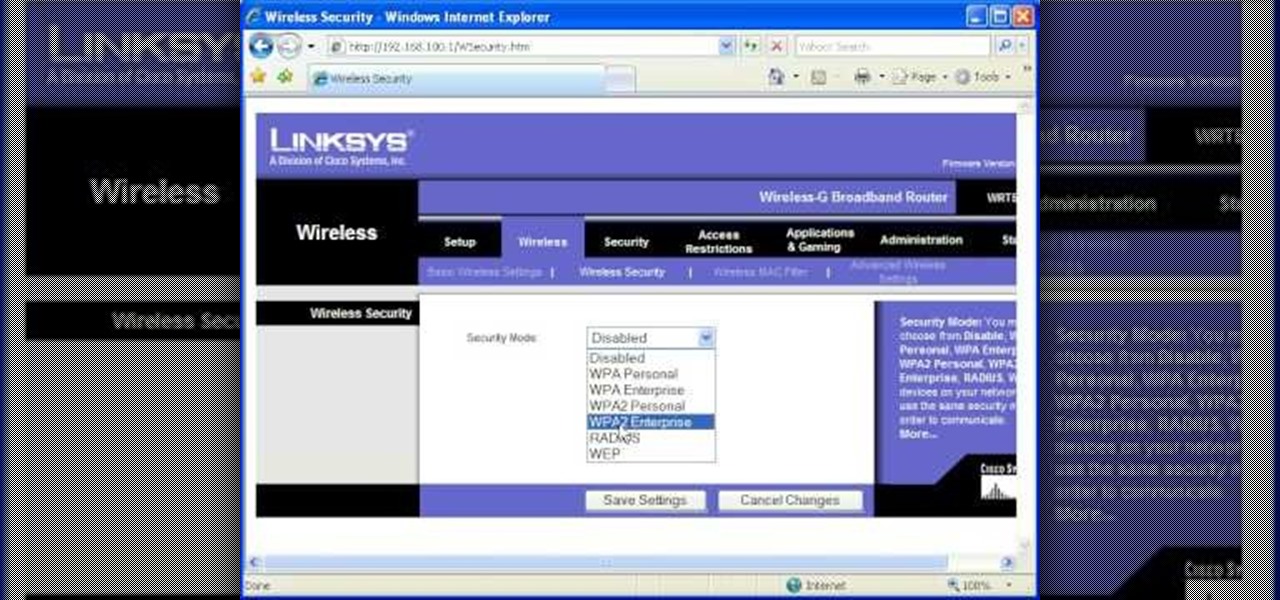
Most of the home wireless networks are not set up by professionals and hence they might lack in security features. People just set up the wireless networks by connecting the devices and powering them up and never care to apply security settings to the network. This may result in your wireless network being compromised by unwanted external entities. How ever you can do a web based configuration settings and secure your wireless network by password protecting it. This settings differ from the m...

If you live in a hurricane prone area, it is a good idea to protect your windows with security film. This video will teach you how to install hurricane security window film on your own and protect your home and assets.

Ron Hazelton explains how to protect your foundation or basement wall from being affected by water that is discharged from your downspout. He explains how downspout extenders can be used to carry the water away from the foundation. Ron will show you three variations of downspouts that you can use. You'll learn how to install each kind of downspout so you can decide which is right for you. If you follow the advice given in this video, you're sure to further protect a very important part of you...

In this video a professional boxer demonstrate the basics of boxing so that you can protect yourself. First of all, you should stand in such a manner that your left foot is in front and the right foot is in back (if you are right-handed). Make a fist, put both hands in front of your face. The distance between both the hands should not be much so that in any case, you can cover and protect your face. Your left hand should always turn up and pull back. For punching, take your right hand fist ne...

Watch this video for a helpful tip on how to use secret folder application and protect folders in your MAC PC by hiding it. you could download secret folder application from version tracker.com for free go to the Website and click download button to download the application on your Mac PC open the secret folder application. click on the required password button, put your desired password and re enter to confirm. to access your file, click the plus button at the lower left. choose the desired ...

Need to unlock your music? Want to save Rhapsody or Napster files on more than your own computer? This is how to unlock, remove drm and convert protected wma files from napster and rhapsody to mp3 without having to pay for them. Also how to put napster and rhapsody files in iTunes and on your iPod.

The Microsoft Office Access 2007 relational database manager enables information workers to quickly track and report information with ease thanks to its interactive design capabilities that do not require deep database knowledge. In this Microsoft Access video tutorial, you'll learn about protecting your VBA code from snoopy little trolls. For more information on keeping your VBA code secure, watch this MS Access how-to.

Sadly, into each life at least one mean, nasty, low-down, no-good boss must fall. When it's your turn, you'll want these survival tips. Trying to remain calm and protecting yourself are important strategies to protect your career. Watch this video job skills tutorial and learn how to cope with an unfair boss.

In this video Bob Schmidt shows you how to protect yourself when working with fiberglass insulation when insulating or doing removals during your home improvement projects.

Watch this video to learn how to make a password protected video.

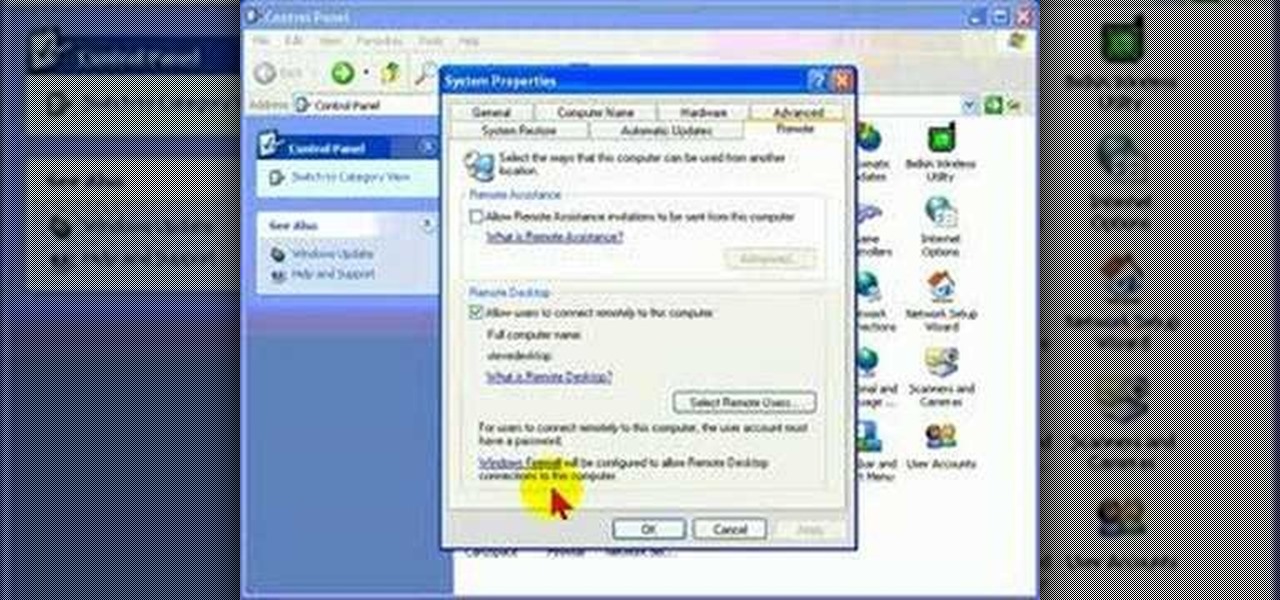
Remote Desktop is a feature of Microsoft Windows, that allows you to access your PC from anywhere in the world, and use it as if you were sat right in front of it.

One method you can use to protect yourself, is to ensure you clear your private data, such as your search history, and in this screencast tutorial, we show you how to do just that in Mozilla Firefox.

Gary Rosenzweig from MacMost looks at one method to protect a set of files with a password on a Mac. It involves using Disk Utility to create an encrypted disk image.

Veronica Belmont imparts her wisdom on how to be safe within social networks. Learn how to adjust the settings on your Facebook, MySpace, and/or LinkedIn profile to help protect your privacy.

This video segment will show you how to protect your LCD or DLP TV which is susceptible to irreparable damage. We can build you a custom screen for far less cost that a TV repair.

Andrew Burke from Videomaker magazine gives some advice for protecting your equipment while shooting in the rain.

Want to make your fingers look like they have flames shooting out of them? Learn how to protect your fingers while they are ablaze and make your friends think you are impervious to pain. Use easy to find material to protect your fingers while you light each one on fire.

On Monday, the world watched in horror as the historic Notre Dame Cathedral went up in flames in Paris.

If you have yet to receive your invitation to next weekend's royal wedding in the UK, then you can still experience part of the pomp and circumstance in augmented reality courtesy of ABC News.

Augmented reality device maker Vuzix has filed a defamation lawsuit asking for $80 million in punitive damages, money damages, and interest against a short seller who has publicly claimed that the Amazon Alexa functionality of the company's Blade smartglasses is fraudulent.

Because of the way Google Play works, Android has a "bad app" problem. Google allows any developer to upload an app to the Play Store, regardless of if it works, how it looks, or whether or not it can harm users. Malware scanning happens primarily after apps are uploaded, and though Google has recently taken steps to safeguard users with its Play Protect program, you don't have to depend on them.

Comic-Con International: San Diego, better known to you and I as "San Diego Comic-Con", is coming very soon; and if you're like me and live far, far away from San Diego (sigh), Twitter is now offering a helpful alternative to keep you in the loop at this year's event.

Virgin Wireless, perhaps best known for Sir Richard Branson and all of his antics, is an affordable cellular option here in the US. Virgin customers can enjoy — if that's the right word for it — Sprint's cellular service, at a discounted rate, however, there are usually some compromises for that. Now, there will be yet another compromise for Virgin customers who don't like iPhones — Virgin will now only carry Apple's phone on their network.

Texas has become the 18th state to pass a bill into law regarding autonomous vehicles, the third this month to do so.

We don't know exactly what form 5G cellular technology will take, but it intends to bring faster Wi-Fi-like performance to mobile devices. While that'll provide major advantages to lots of connected technology, PC Magazine notes that it could be what augmented and mixed reality needs to become widely adopted.

Systm is the Do-It-Yourself show designed for the common geek who wants to quickly and easily learn how to dive into the latest and hottest tech projects. They will help you avoid pitfalls and get your project up and running fast. In this DIY episode, see how to build a firewall from a junk PC to protect networks.

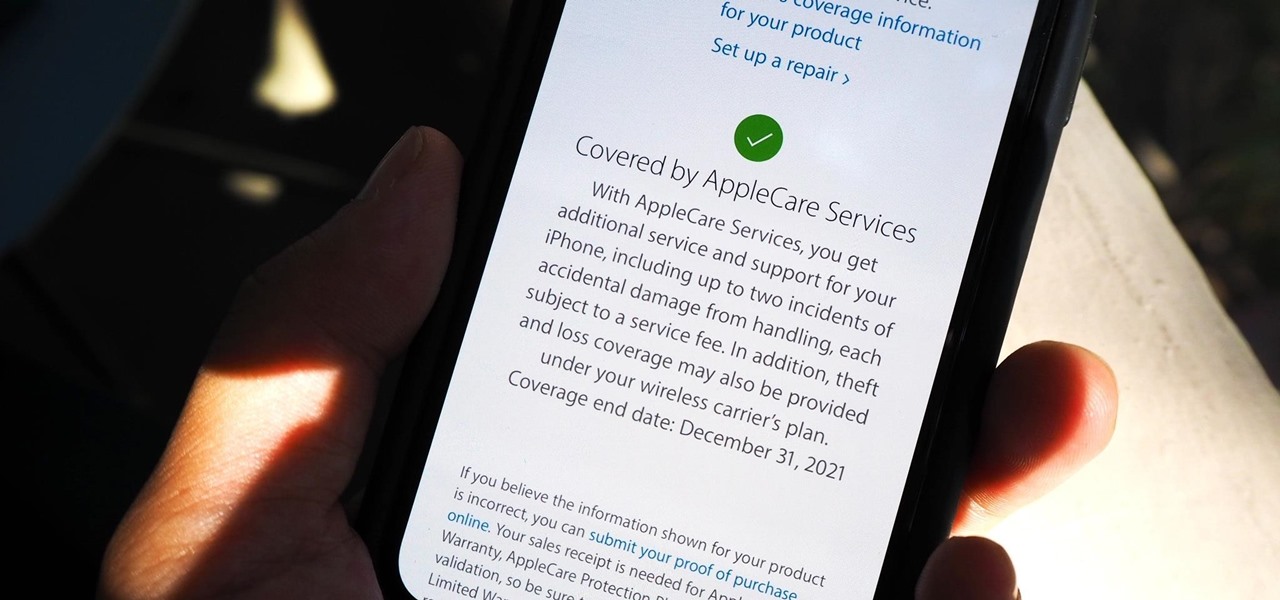
Let's say that the screen on your iPhone is showing signs of discoloration, which makes the display annoying to use. You'll need a replacement display or a new iPhone as soon as possible. If you have one of the newer iPhone models, the cost to fix it might be more than your wallet can handle, but a warranty may still cover it, and there are ways to check quickly.

With the whirlwind of noise surrounding the COVID-19 virus sweeping the nation, it's not hard to default to panic mode. One of the best ways to avoid panicking, however, is to follow trusted sources of information and avoid all of the opinions and trolls that don't reflect reality.

There's definitely some malware-ridden apps on the Play Store. When it comes to the third-party apps you've connected to your Google Fit account, some have a crazy amount of permissions they have no business accessing. For example, you probably don't want a heart monitor app having access to your personal location data.

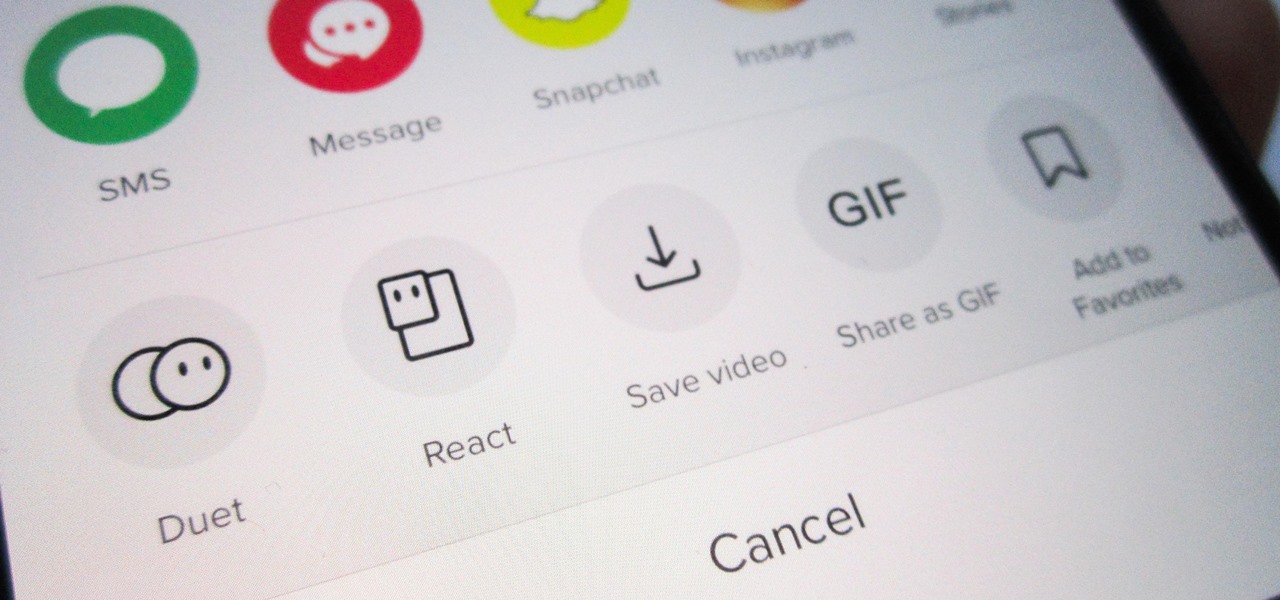
Unless you want to make your TikTok account totally private, anyone that uses the app — with or without an account — can view your profile and all the videos of you performing new dance moves, singing along to popular songs, and recreating your favorite TV show scenes. Even worse — they can download those videos.

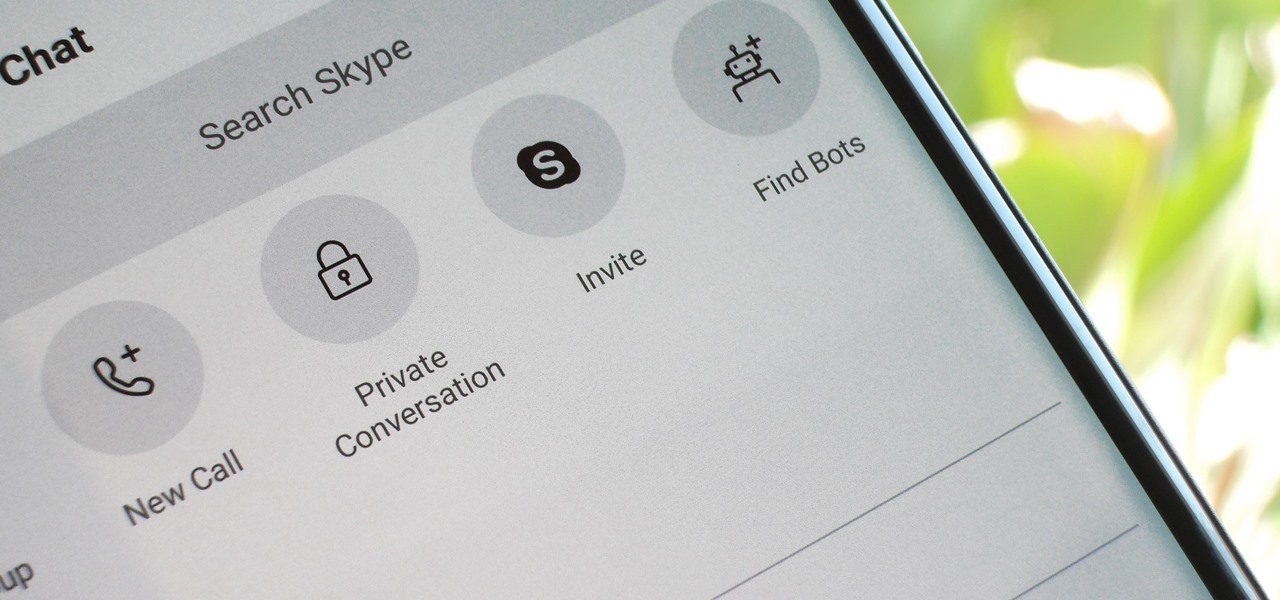
For years, Skype has been synonymous with video calling and messaging. However, as the industry moved toward encryption and privacy, Skype usage was discouraged by experts due to its murky encryption. To combat this, Skype has introduced true end-to-end encryption.

Getting a good night's sleep is critical to maintain good health, a better mood, and clear your mind for whatever the day has planned for you. But in practice, whether you're tired or not, the world has a way of preventing it, either through your partner's snoring, your neighbor's music, or the road construction going on right by your bedroom window. It can get rough.

A shemagh, or a keffiyeh, is a traditiona Arab headdress that's worn by Arab men. Made from a square scarf, it protects their heads and face from desert wind and sun. It's also multifunctional - warm at night and lightweight during the day. These scarves have even become adopted by the U.S. Cavalry to protect themselves during long treks outdoors.

If you're really into Yu-Gi-Oh! or any other collectible trading card game, you know that protecting your valuable cards is important. This video will teach you how you can circumvent having to buy a deck box to protect your cards by building your own out of cardboard.

In this video tutorial, viewers learn how to protect their privacy online. Some information that is exposed every time you visit a website are your I.P. address, operating system and browser. To view what information that you are revealing to a website, visit the site provided in the video. This site will give you all the information that you are exposing in a website. This video will benefit those viewers who visit a lot of websites, and would like to learn how to view the their exposed info...