Welcome back, rookie hackers! We recently began an exploration of ways to hack using the Bluetooth protocol. As you know, Bluetooth is a protocol that connects near field devices such as headsets, speakers, and keyboards. Its minimum range is a 10-meter radius (~33 feet) and maximum is at 100 meters (~328 feet).

There are many hacks for increasing productivity, but so many depend on tricking your own mind or behavior. When it comes to motivation in the workplace, though, sometimes the space within which you work dictates how you behave and the work you produce. So if you want to increase your ability to get more done in a single workday while doing a better job, consider changing your surroundings in the following ways.

A while back, I wrote review of my favorite hacking movies of all time. Two of my key criteria were; (1) how realistic was the hacking, and (2) are the hackers portrayed as the "good guys." This past winter, a new hacker movie was released, appropriately named Blackhat starring Chris Hemsworth (from Thor fame) as a blackhat hacker who is released from prison to stop a notorious and destructive hacker that only he can stop. Although the movie did very poorly at the box office, I thought it was...

Welcome to the sequel to the latest post on writing 64 bit shellcode! This tutorial will assume that you are aware of everything mentioned in the last one, as I will try to make this tutorial void of formalities and straight to the point! If you have not read the last one, I suggest doing so unless you are familiar with basic assembly programming and system calls. This is by no means rocket science, so therefore I will simply repeat my TL;DR from last time before we get started, so that the a...

The gag reflex: it can interfere while in the dentist's chair, upon seeing another person throw up, or even just getting a whiff of a disgusting, stomach-twisting scent. Every time this reflex kicks in, it stops us immediately, inducing a choking, gagging, coughing fit.

Welcome back, my aspiring hackers! As I mentioned in earlier posts, the best hackers (or at least those not behind bars) have a keen understanding of digital forensics. If I am tasked to intrude upon an enemy's file server to retrieve war plans, such as in this tutorial, it is essential to my country's (and my own) well-being that it not be traced back to me. Understanding digital forensics helps us to leave without a trace and never have a trail back to us or our employer.

Welcome back, my tenderfoot hackers! Those of you who have been reading my posts here for awhile know how much I emphasize good reconnaissance. Novice hackers often jump into a hack/exploit without doing proper recon and either fail or get caught. Experienced and expert hackers know that 70-80 percent of a good and successful hack is dependent upon successful and accurate reconnaissance.

Welcome back, my aspiring hackers! Many of you have installed Kali Linux as a virtual machine (VM) using VMware or VirtualBox, while others have installed Kali (or BackTrack) in a dual-boot system. The drawback to installing these hacking systems as a VM is that it then requires an external wireless adapter (your wireless adapter is piped through the VM as a wired device, eth0), but it makes for a great place to test your hacks while honing your skills.

If you're anything like me, your day doesn't start until you've sloughed away your grogginess with a scalding hot shower. That perfectly-heated water can clear stuffed sinuses, relax the muscles, and make pretty much anyone feel squeaky clean. However, a cold shower can do even more for you if you can stand the low temperatures.

Imagine that you're the last person alive. After losing all of your loved ones, you thought you'd never see another human being in your life. Then, they arrive. The hoard of 15-year-old zombies looking for a cute British YouTuber so they may feast on his brains.

Welcome back, my hacker novitiates! In previous guides, we have used one of the most powerful hacking platforms on the planet, Metasploit, to perform numerous hacks. They ranged from exploiting Windows XP and Windows 7/8 vulnerabilities, to installing a keylogger and turning on a webcam remotely. We have even been able to save the world from nuclear annihilation, see if our girlfriend is cheating, spy on suspicious neighbors, evade antivirus detection, and more.

Welcome back, my hacker noviates! In a recent post, I introduced you to Shodan, the world's most dangerous search engine. Shodan crawls the globe from IP to IP address, attempting to pull the banners of each web-enabled device and server it finds.

Welcome back, my tenderfoot hackers! We have looked at a number of ways that we sniff traffic on the network with such tools as Wireshark, tcpdump, dnsiff, and others, but each of these tools is only capable of pulling packets off the wire.

Welcome back, my aspiring hackers! Domain Name System (DNS) is one of those things we seldom think about unless it doesn't work. Then, it can be very frustrating when we attempt to navigate to a website and we get that frustrating error message.

Welcome back, my novice hackers! I have tried to emphasize throughout this "Hack Like a Pro" series that good reconnaissance is critical to effective hacking. As you have seen in many of these hacks, the techniques that we use are VERY specific to the:

Welcome back, my hacker novitiates! Finding vulnerabilities in systems can be one of the most time-consuming tasks for a hacker. There will be times, though, when you'll find yourself in a position that you know that a particular port represents a vulnerable application or service.

Welcome back, my fledgling hackers! Nearly every commercial enterprise worth hacking has an intrusion detection system (IDS). These network intrusion detection systems are designed to detect any malicious activity on the network. That means you!

In my first tutorial on Linux basics, I discussed the importance of hackers using Linux and the structure of the directory system. We also looked briefly at the cd command. In this second Linux guide, I'll spend a bit more time with changing directories, listing directories, creating files and directories, and finally, getting help. Let's open up BackTrack and getting started learning more Linux for the aspiring hacker.

Welcome back, my hacker trainees! A number of you have written me regarding which operating system is best for hacking. I'll start by saying that nearly every professional and expert hacker uses Linux or Unix. Although some hacks can be done with Windows and Mac OS, nearly all of the hacking tools are developed specifically for Linux. There are some exceptions, though, including software like Cain and Abel, Havij, Zenmap, and Metasploit that are developed or ported for Windows.

Welcome back, my fledgling hackers! In one of my recent articles, I showed you how to install BackTrack as a dual boot system on a Windows computer. In this tutorial, I will walk you through BackTrack, giving you a tour of the most salient features for the hacker-to-be.

With this article, I'll be continuing the series I started with my recent plague doctor article. That is, examining tropes that may at first appear to not fit into Steampunk.

Perhaps the most important decoration of the holiday season is the Christmas tree. It's where all of the magic happens. If you're not into real Christmas trees, there's always some festive alternatives, but for those of us who can't live without a natural Christmas tree, choosing the right one for the right price can be an impossible task.

Believe it or not, water can be extremely scary for some people. Mostly, those who experience hydrophobia (an irrational fear of water), are experiencing symptoms of rabies, but you don't need to contract rabies to be afraid in Hydrophobia on the Xbox 360. This survival-adventure game is available on the Xbox Live Arcade, and this video walkthrough series will show you the complete gameplay for this water-filled action game.

Internet whores (which would be all of us by now) are quite familiar with gifs. Just like popular internet memes like LOLCats, viral gifs are short videos or slide shows sequenced together for a comical - or at least unexpected - effect.

If you're looking for a cool way to add text to your videos, like for an opening sequence to a film where the credits are displayed, embedding the text directly into the scene is the way to go, especially if you like the hit television show "Fringe", who used these kind of embedded title effects in establishing shots. Car adverts use this technique a lot, as well. "Panic Room" also use this effect in the opening title sequence.

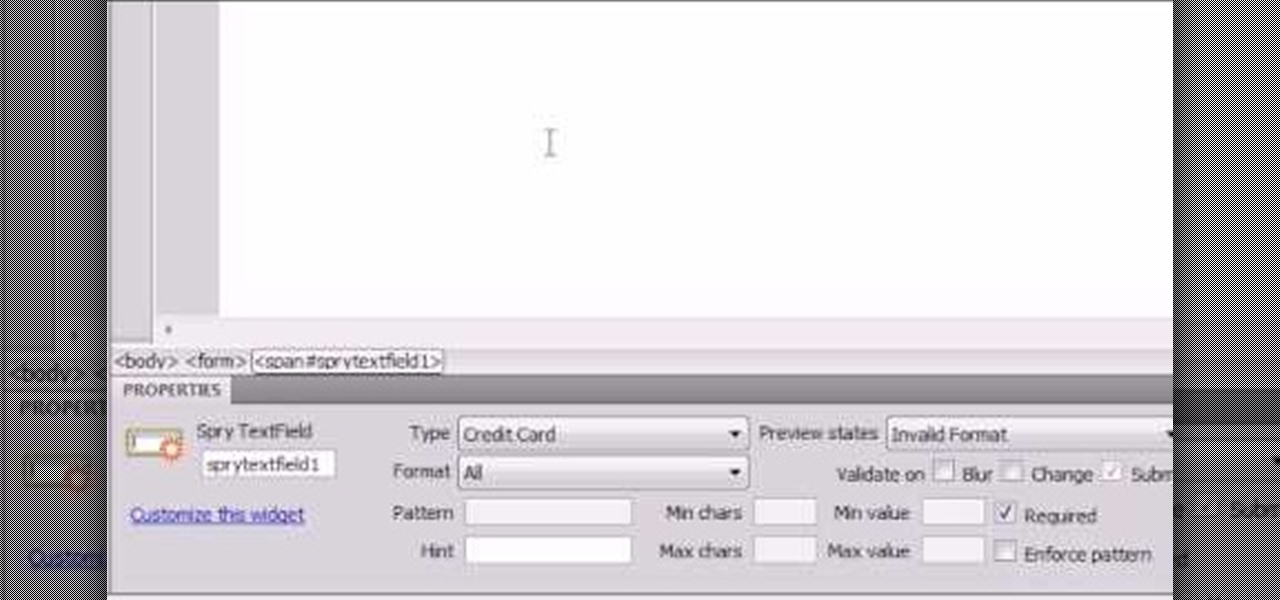
Here the New Boston shows you some tips about using the Spry Validation Text Field. To begin you will go to the Spry Validation Text Field, on Dreamweaver CS4. Looking at the bottom of the page notice the various options that are available for Properties. You find drop-down boxes for Type, Pattern, Minimum or Maximum values, Required, Enforce pattern, Format, Validate on, Blur or Change and Preview States. You can see the types of text available for validating by left mouse clicking the Type ...

Glintzy shows viewers how to sanitize all of their makeup products. To do this you will need, a spritz bottle with rubbing alcohol in it and some paper towel. You should always wipe down wherever you put your makeup on with a germ killing spray. Also, always clean the outside of your makeup to make sure this is clean because you are always touching the makeup. Also, don't forget to clean the handles of your brushes. Foundation you cannot sanitize if it does not have a pump so you have to be r...

Your friends want you to marry them! Before you can officiate their big day, you'll need to jump through some legal hoops. Learn how to officiate at a wedding.

Compulsive gambling is a recognized addiction, just like alcoholism or chemical dependency. Follow these steps to see if you might fit the profile. Recognize the signs of compulsive gambling with this guide from Howcast.

Go thrifty! Go vintage! Go second hand. With the right approach and an open mind, a trip to your local thrift store can yield some fashionable bargains. Buying used is a smart solution to this economy, and gives you a smart sense of fashion.

LEGO and Harry Potter unite in this extensive video game called LEGO Harry Potter: Years 1-4. Each year corresponds to the years in J. K. Rowling's wizardry series, so this is like four games in one! This 80-part series will take you through the complete gameplay of LEGO Harry Potter for the Xbox 360, but it's also available for the Nintendo Wii, PlayStation 3, Nintendo DS, PSP and Windows. For more information on this walkthrough, visit Mahalo.

In Grant City, crimes has taken over, and there's only one man who can help: Jack Slate. With the help of his trusty sidekick canine, Shadow, maverick cop Jack Slate will help restore Grant City to its previous renowned existence as of one of the world's greatest cultural and financial centers, one criminal at a time. While ridding the city of its filth in Dead to Rights: Retribution, Jack and Shadow uncover a conspiracy that threatens their whole existence. And it's up to you to stop it.

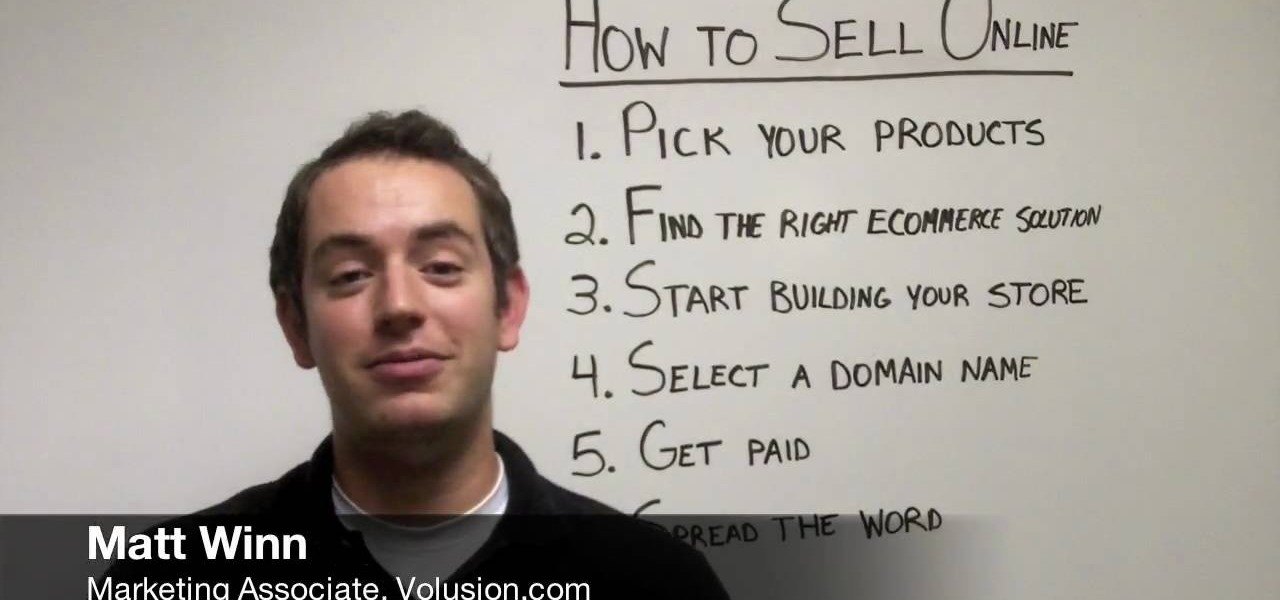
Selling isn't easy. And it isn't any easier online, at least, until you get set up. It sure beats the streets. But how do you get ready to sell online?

This video discusses the basic steps necessary to start an online business. The first thing you need is a name for your business. Keep it simple, easy to spell and remember. Once you have your name, register it with the government. Next, find a good hosting company for your website. He recommends Godaddy.com. Also a good web designer is a necessity. They will meet with you to discuss your ideas, and your website should be ready in about a week.

It's summer again and it's time to get out of the house and there's no better way than with a fun game like some improvised baseball. You don't need a whole team of people all you need is a bat, a ball and another person to play with.

Keeping the books in order is one of the great challenges every business owner faces. Having a great product or service is one thing, but managing the minutia of invoicing can trip up a lot of small- and medium-sized businesses.

Tax season is always stressful, especially for entrepreneurs and small business owners. Rather than wait until March to get your finances in order every year, learning how to keep track of your expenses is a valuable skill that saves you and your business time, money, and plenty of anxiety.

If your phone has an A/B partition layout, there are two virtual hard drives that each contain a copy of Android. After every restart, it picks a partition to boot from, then the other lays idle. The idle partition can be overwritten with a new copy of the OS and it won't affect the active one. So the next time you reboot, it just switches partitions and it's as if you updated instantly.

When you place your iPhone over a card reader for Apple Pay, it'll always pull up your default card. That might work fine for you, but perhaps that isn't the card you want to use. The problem is, you don't have time to switch cards before the payment goes through. That might result in using your rewardless debit card to buy groceries when you could've snagged 2% back by using your Apple Card.

Phones these days are expensive. The iPhone 11 Pro is presumed to start at $999, following the iPhone XS and iPhone X's leads. One way to bring down that cost is to trade in your old iPhone, but there isn't one clear-cut way to do that. You could trade your iPhone into a participating website or put yourself out there and sell the iPhone on your own. It's all about what's best for you.