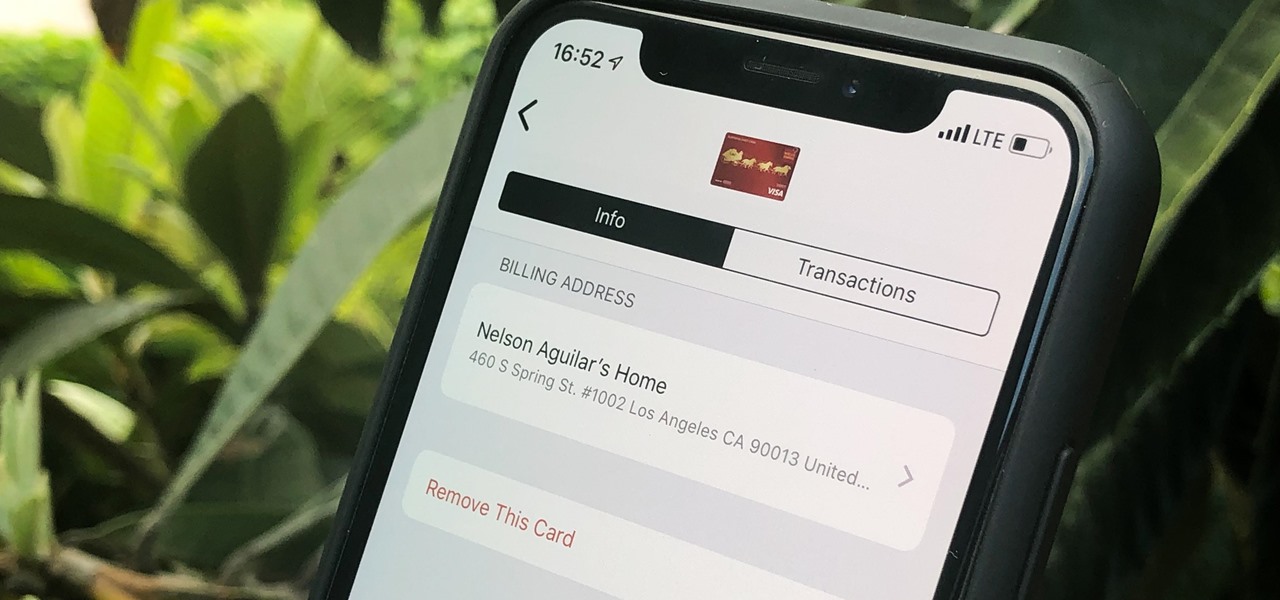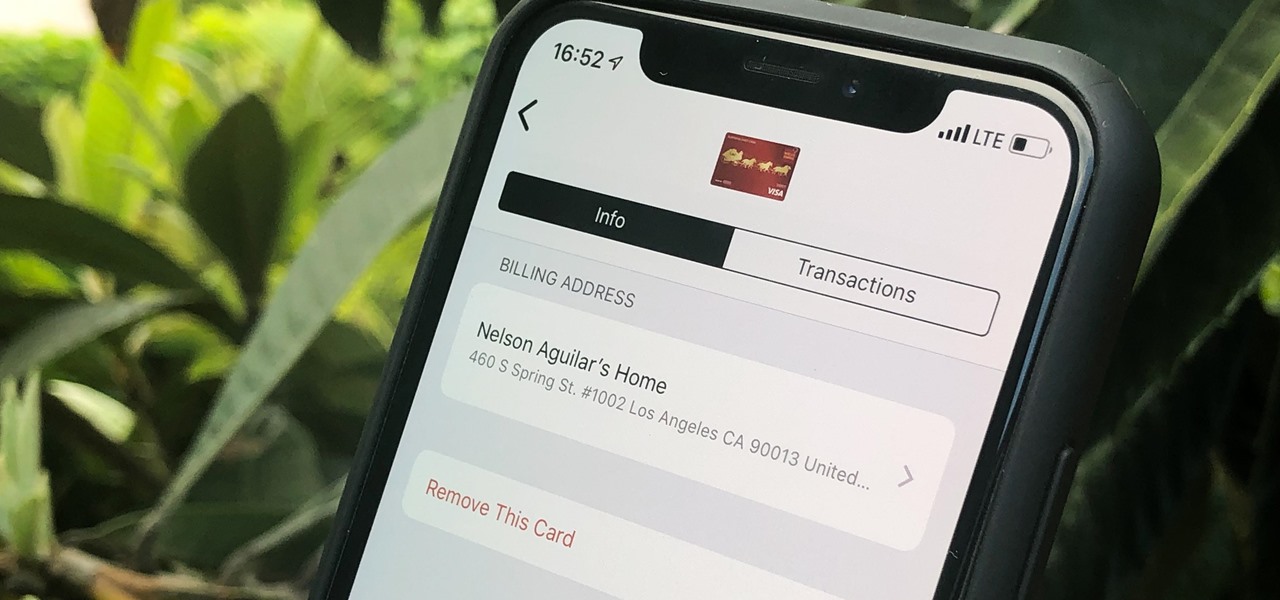
Apple Pay can be used at retail stores, restaurants, markets, and millions of other locations in the US and abroad. It's used to buy everything from clothing to groceries and vending machine snacks, so it's important to ensure that the cards in your Wallet are always up to date with the correct billing and shipping addresses.

The holidays are here. From the week of Thanksgiving until the end of the year, retailers will be offering massive discounts on your favorite items. So if you're looking for smartphone accessories, this is the time to buy. From Walmart to Best Buy, there are deals everywhere on a host of items.

The fifth annual Amazon Prime Day is upon us. Starting July 15, Amazon will offer thousands of deals on products across its site, kicking off at 3 a.m. EDT. This year, it will only run for 48 hours, so you have even less time to act. To save you some of that time, we made a list of the best deals for smartphone accessories.
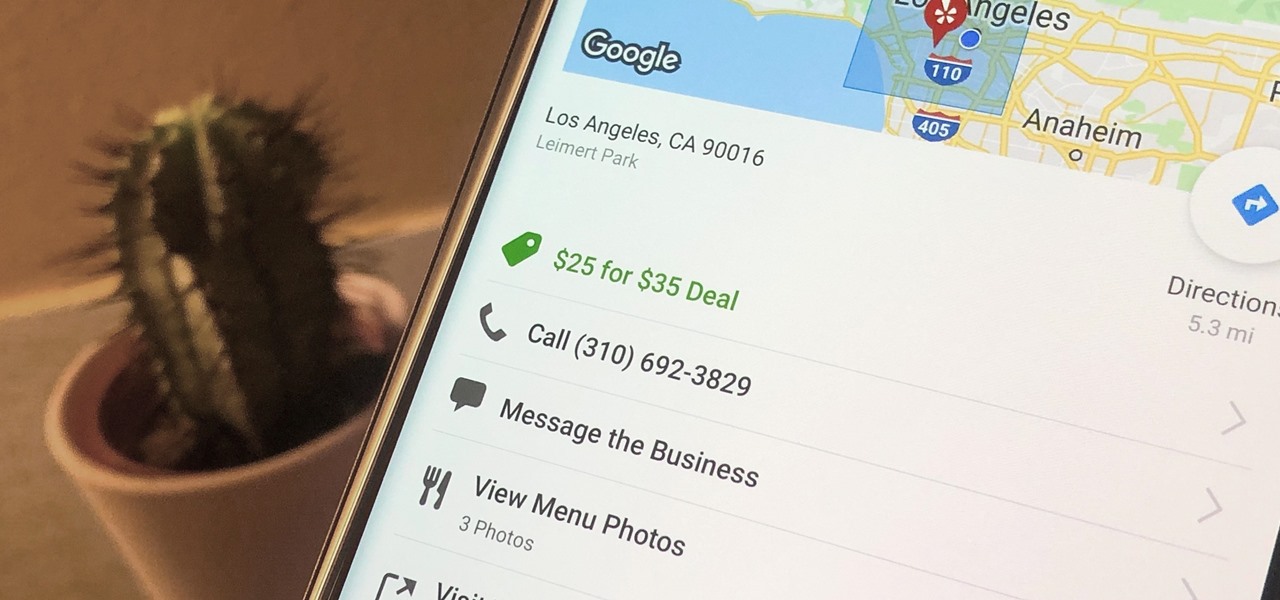
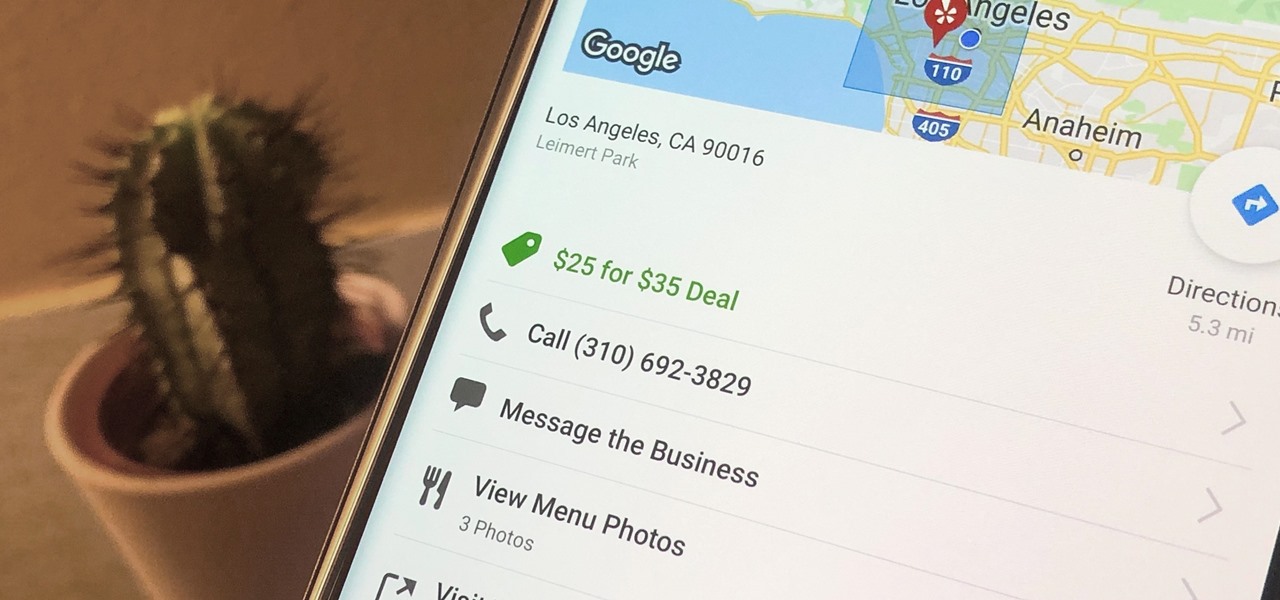
Newer businesses, or older businesses looking for more traffic and sales, often offer enticing deals to attract customers. On Yelp, any business has the option to provide a deal to users, which is essentially a Groupon-like coupon. But how do you find these deals in the Yelp app for Android or iOS?
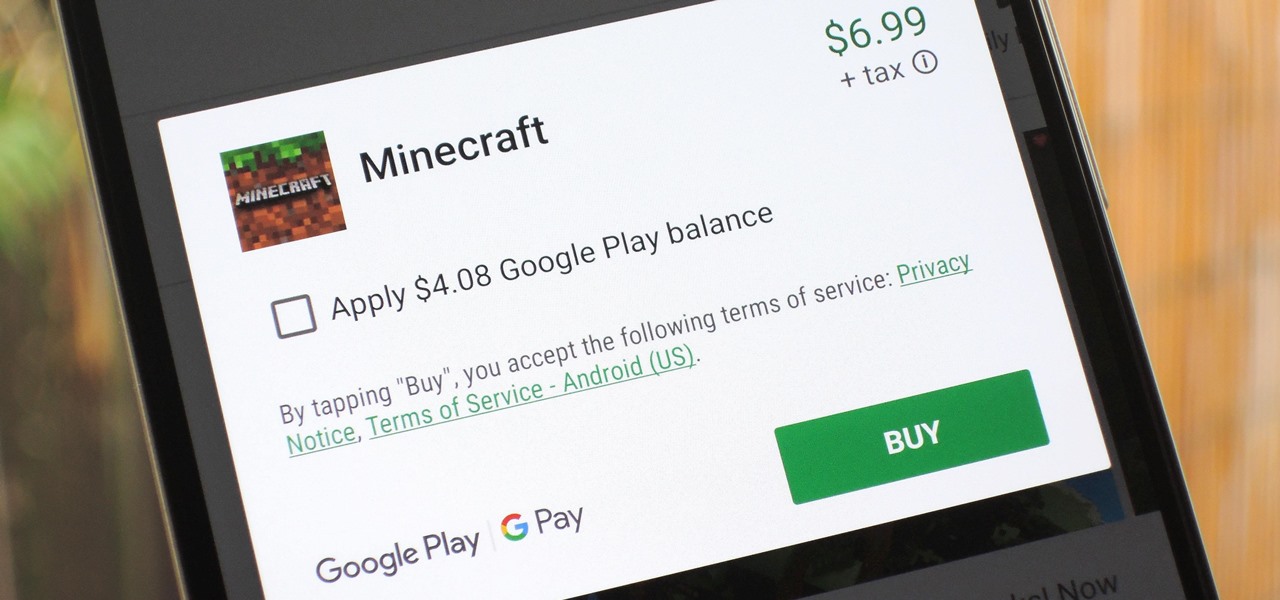
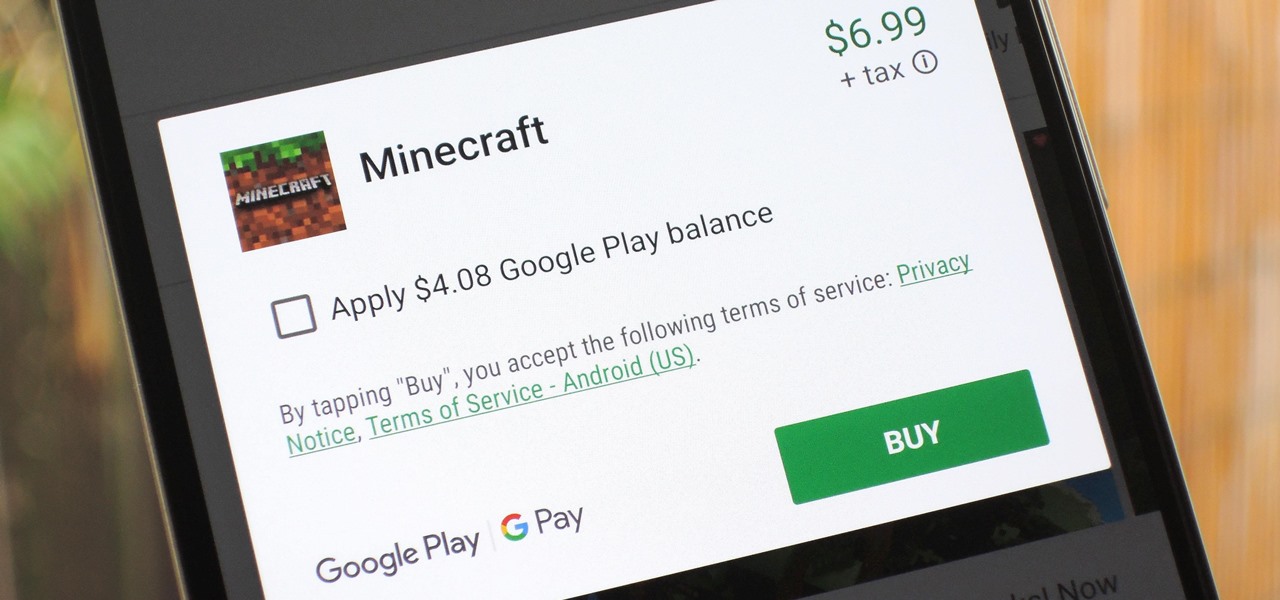
The iTunes App Store makes it easy to buy an app or game on someone else's behalf, and it's a great way to send an iPhone user a thoughtful gift. The Google Play Store doesn't have such functionality, but there are still a few workarounds to accomplish the same goal: gifting an app to an Android user.

Thanks to its intuitive interface that makes sending and receiving money a breeze, Venmo has become the go-to app for millions in the US. In fact, you've probably heard the term "Venmo you" being tossed around between friends. But before you take the plunge and sign up, it's always a good idea to read the fine print and know what you're getting into. Money is involved, after all.

As the level of data being generated grows exponentially, past the Information Age and into the coming Hyper-Information Age of immersive computing — as resistant as many of us are to the idea — personal data security is becoming a necessary consideration in our everyday lives. Recognizing this, Mastercard, Qualcomm, and Osterhout Design Group have teamed up to show what secure shopping could look like in the very near future with iris authentication.

It's March once again, and while that might signify the beginning of spring for some, basketball fans have this month marked on their calendars for one good reason: NCAA March Madness. Though the tournament is already underway, the Sweet Sixteen leg begins Thursday, March 23, 2017. If you fear you may miss the upcoming games, worry not, as free apps for smartphones and tablets are available to help you watch all the action.

Google's new Pixel and Pixel XL flagships are some very powerful smartphones, but as with any high-tech gadget, they're only as capable as the user allows them to be. So if you're a proud new Pixel owner, it's time to bone up on a few new features to help get the most out of your device.

Throwaway phones aren't just for seedy criminals and spies—they can be useful for many everyday situations.

Using a technology we like to call "Hive Computing," several Android apps allow you to contribute idle processing power to help further scientific research. This basically means that when you're not using your phone or tablet, it can join forces with other idle devices to form a supercomputer that scientists can use to potentially make a world-changing breakthrough.

Welcome back, my greenhorn hackers! In previous Wi-Fi hacking tutorials, I have shown you ways to create an Evil Twin, to DoS a wireless AP, and to crack WEP and WPA2 passwords, but in this tutorial, I will show you something a little bit different.

Welcome back, my greenhorn hackers! In a previous tutorial on hacking databases, I showed you how to find online databases and then how to enumerate the databases, tables, and columns. In this guide, we'll now exfiltrate, extract, remove—whatever term you prefer—the data from an online database.

You saw our post on the 18 coolest new features of iOS 7, but now that you've had a chance to play around with your updated iPhone, it's time to lock it down.

Okay, Mr. Thrifty, you reserved the least expensive hotel room that you could. But your inner Donald Trump doesn’t want to settle for low-frills. Go ahead, it never hurts to ask. Watch this video to learn how to get a hotel upgrade.

Watch this video tutorial to learn how to calculate your carbon footprint. A carbon footprint is an equation that estimates just how much you, personally, are contributing to global warming—and all you have to do is plug some info into an online calculator. Figuring out how to make your footprint smaller, of course, is another matter.

IMVU is a 3D avatar chat, instant messenger, and dress up game. Get help with all of your IMVU avatar needs with these IMVU tips and tricks! Watch this video tutorial to learn how to earn credits easily on IMVU (09/28/09).

Spoofed phone calls originate from one source that's disguising its phone number as a different one, and you probably get these calls all the time. Maybe they're numbers from your local area code or for prominent businesses, but the callers are just hijacking those digits to fool you into picking up. Turns out, making a spoofed call is something anybody can do — even you.

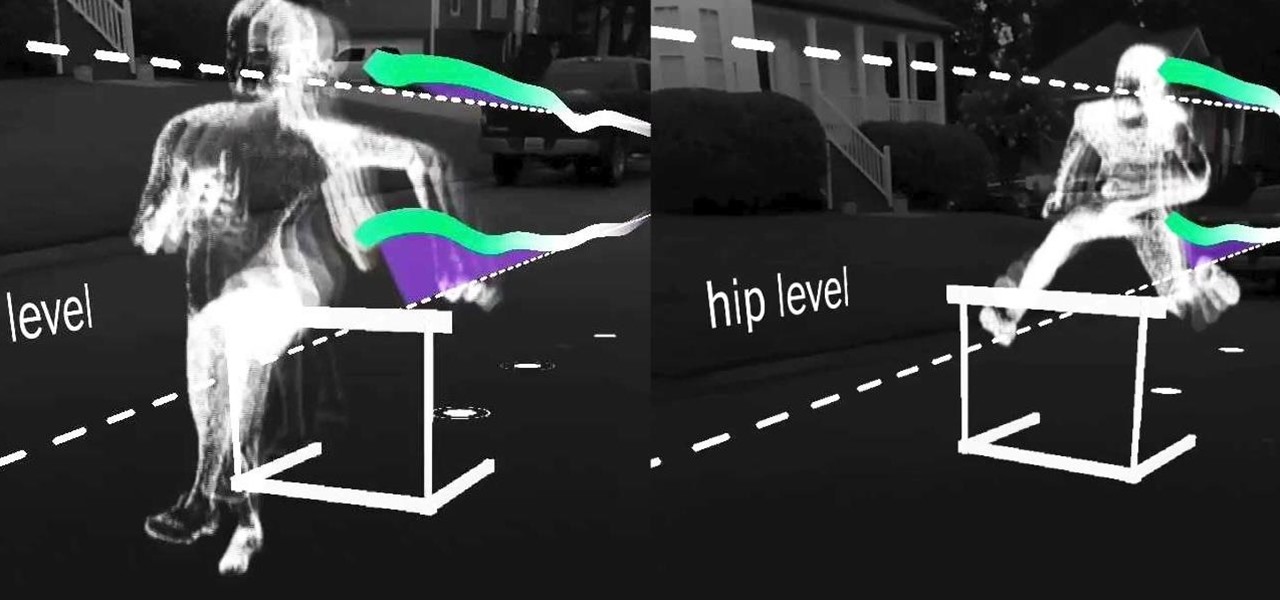
Old school media stalwart The New York Times launched its augmented reality news content in 2018 with a feature on the athletes of the Winter Olympics.

The realm of science fiction isn't all lasers and cute green toddlers, sometimes alternate science history is sci-fi, too, as exampled by the Apple TV Plus series For All Mankind.

It is well documented that what you say and do online is tracked. Yes, private organizations do their best to protect your data from hackers, but those protections don't extend to themselves, advertisers, and law enforcement.

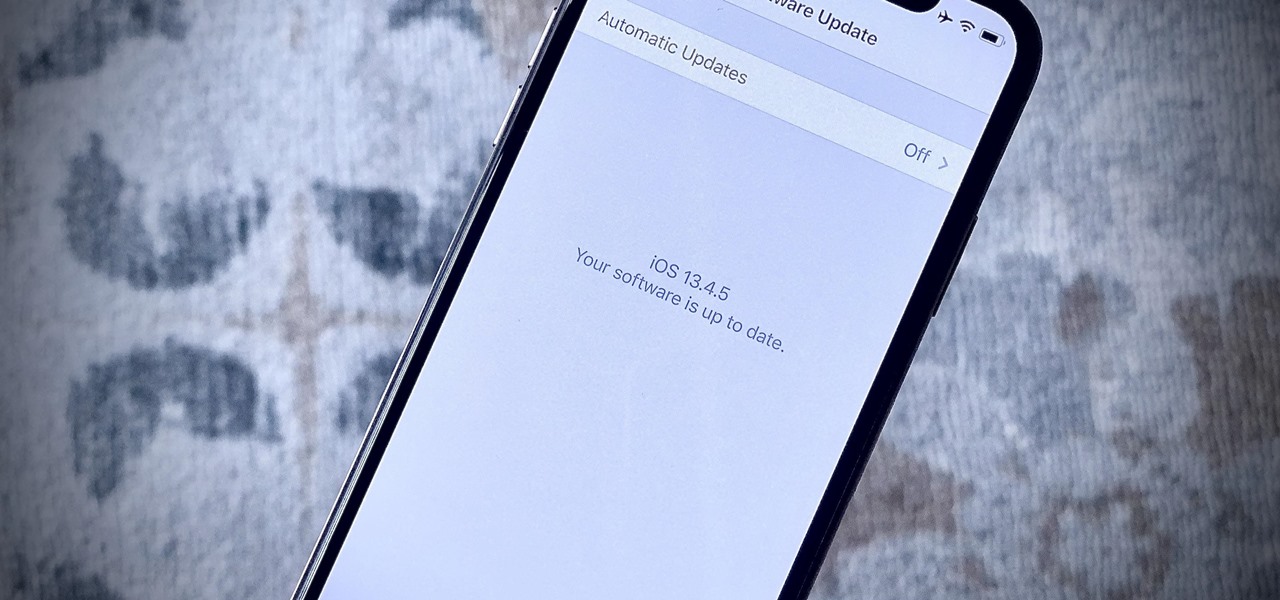
Apple just released the first public beta for iOS 13.4.5 today, Thursday, April 16. This update comes one day after Apple released 13.4.5 developer beta 2, which itself arrived just over two weeks after 13.4.5 dev beta 1.

Snapchat parent company Snap credits its popular augmented reality experiences and its flourishing Lens Studio creator community to its user growth throughout the year.

Reconnaissance is one of the most important and often the most time consuming, part of planning an attack against a target.

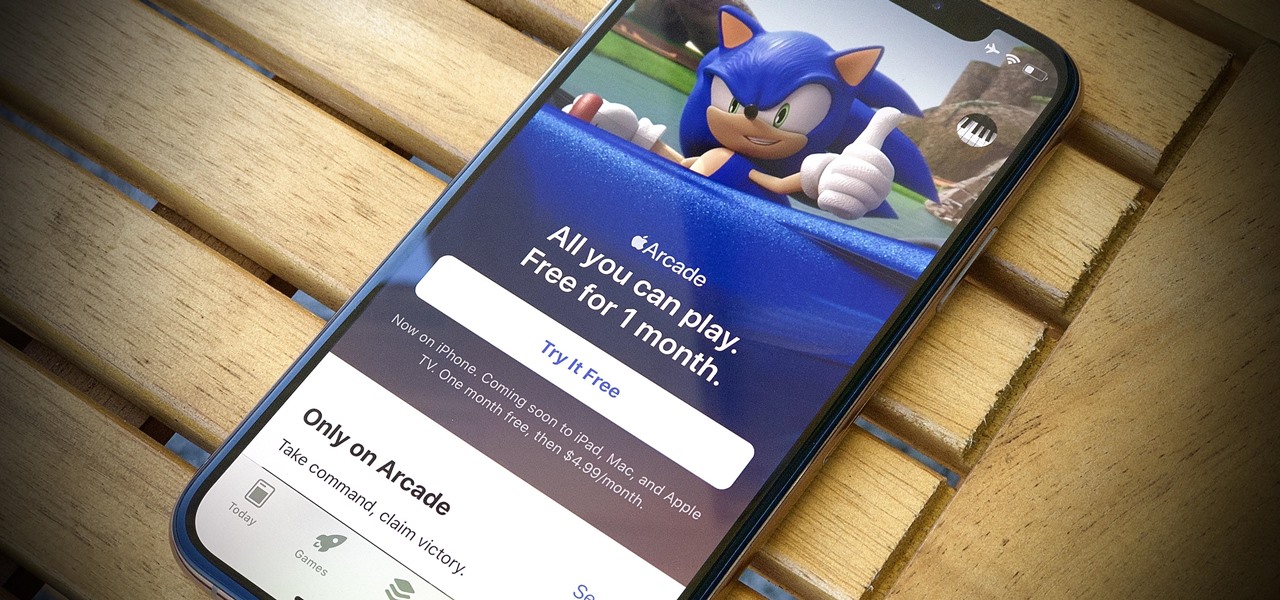
Apple Arcade actually looks like a refreshing change of pace for subscription services. The platform costs just $4.99 a month and includes access to over 100 unique and exclusive games. That's not to mention the one-month free trial each new user can claim. But know this: you shouldn't cancel that free trial until you're ready to give up Apple Arcade.

Apple's upcoming iOS 12.4 isn't the company's most exciting release on its surface, given iOS 13's impending fall unveiling. However, anyone interested in Apple's in-the-works credit card, Apple Card, will need iOS 12.4 on their iPhone to use the card, and that day seems to be getting closer. The sixth beta for iOS 12.4 was just released today, July 9, for both developers and public software testers.

Firewall solutions for macOS aren't impervious to attacks. By taking advantage of web browser dependencies already whitelisted by the firewall, an attacker can exfiltrate data or remotely control a MacBook, iMac, Mac mini, or another computer running macOS (previously known as Mac OS X).

While iOS 13 is not ready for public beta testers just yet, Apple is still testing iOS 12.4 out, and you can install that right now on your iPhone. The latest version, iOS 12.4 public beta 4, was released June 12, a day after its developer version.

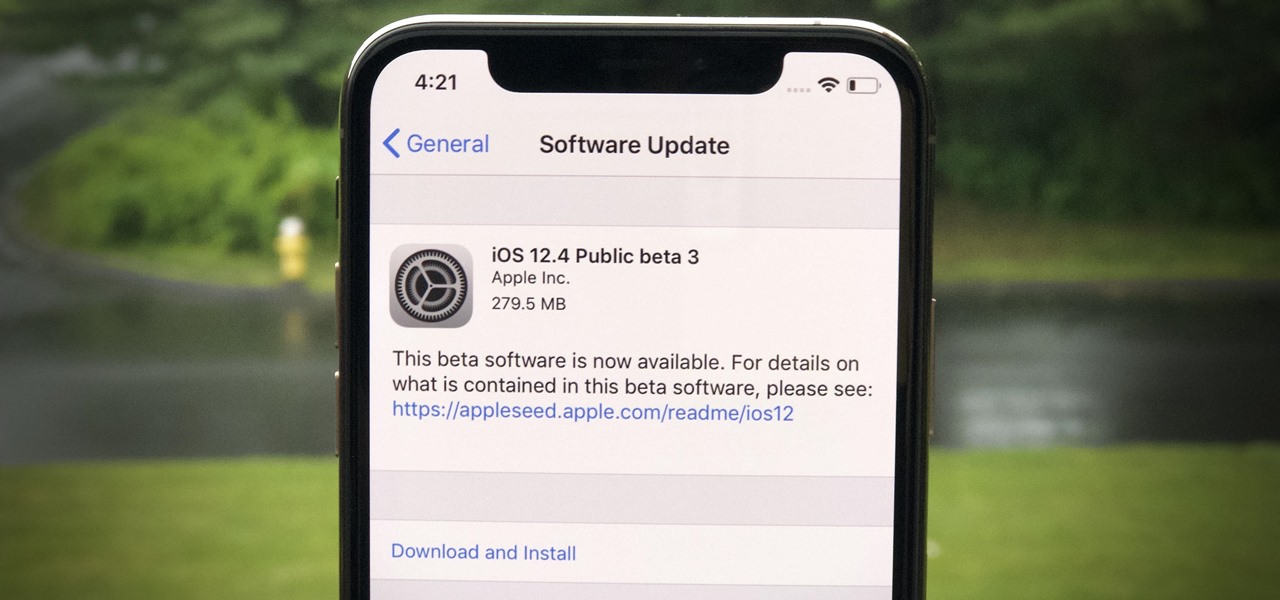
With iOS 13's developer beta in full swing, it can be easy to forget that there's an entirely separate iOS beta cycle still running right now. Yes, iOS 12.4 is still in beta, and unlike iOS 13, it's available to the public for testing.

KeePassX, 1Password, and LastPass are effective against keyloggers, phishing, and database breaches, but passwords managers rely on the operating system's clipboard to securely move credentials from the password vault to the web browser. It's within these few seconds that an attacker can dump the clipboard contents and exfiltrate passwords.

Apple released the third public beta for iOS 12.4 on the afternoon of May 28. The update arrives roughly three hours after Apple published 12.4's third developer beta, and eight days after 12.4 public beta 2. At this time, it seems beta 3 is a minor update for 12.4, which itself is a small upgrade to iOS 12 as a whole. We expect iOS 12.4's shining feature to be Apple Card support.

With the iOS 13 beta right around the corner, Apple is churning out the betas for iOS 12.4 with developer beta 3 out today, May 28. It's the third beta in just 14 days and just eight days after developer beta 2 and public beta 2. The third beta may only house improvements overall, as iOS 12.4 is pretty bare bones as is, despite some hints at Apple Card support.

Apple just released the second iOS 12.4 developer beta today, May 20, five days after the release of the first developer beta for iOS 12.4 and one week after the public release of iOS 12.3. In general, the iOS 12.4 update will support Apple Card, Apple's upcoming credit card due out this summer.

Much of the excitement around the HoloLens 2 has moved on to many wondering when we'll finally be able to get our hands on what is now the best augmented reality device on the market.

At its F8 developer's conference in 2016, Facebook went on record with a roadmap that called for augmented reality integration into Oculus within 10 years. Now, it appears as though Facebook is accelerating those plans.

The year in augmented reality 2019 started with the kind of doom and gloom that usually signals the end of something. Driven in large part by the story we broke in January about the fall of Meta, along with similar flameouts by ODG and Blippar, the virtual shrapnel of AR ventures that took a wrong turn has already marred the landscape of 2019.

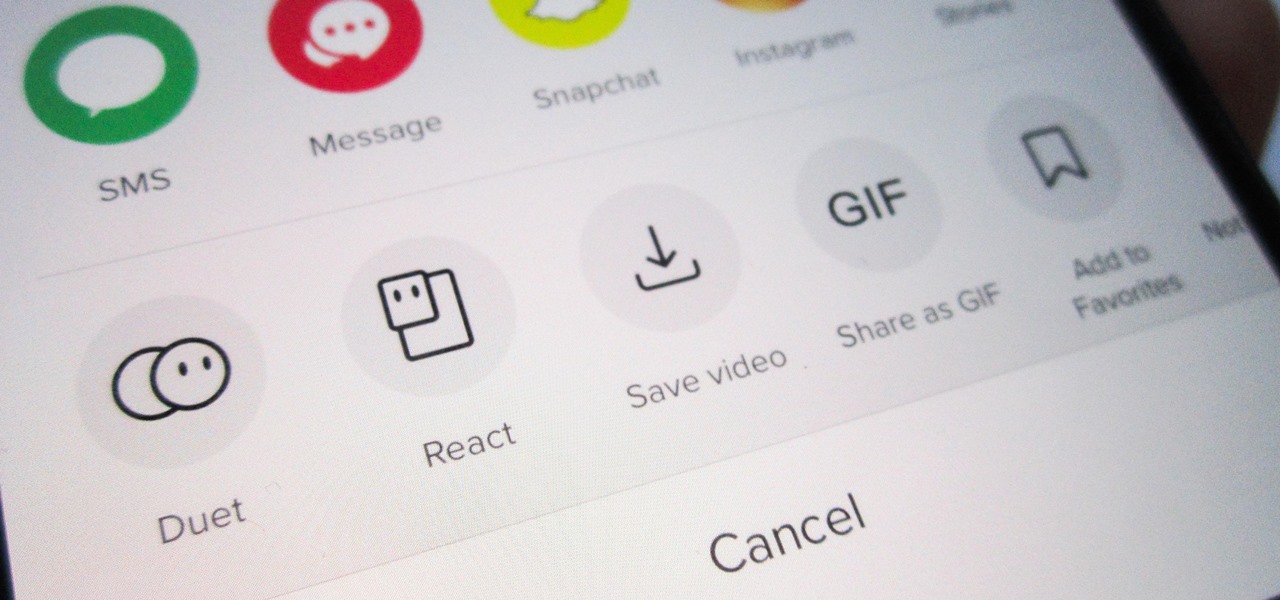
Unless you want to make your TikTok account totally private, anyone that uses the app — with or without an account — can view your profile and all the videos of you performing new dance moves, singing along to popular songs, and recreating your favorite TV show scenes. Even worse — they can download those videos.

It's the icing on top of your cake (or whipped cream on top of your Android Pie) of despair. You may have not had the easiest time rooting your device, but you feel like you overcame all of the obstacles. Only now to discover that those very apps and mods you were rooting for still won't work — and the signs point to a lack of root access. Don't lose hope, because we have some tricks up our sleeve.

It's important to know who you're dealing with after hacking your target's MacBook. Getting remote access is simple, but covertly gathering information about the user and their system can be a challenge.

One of the primary marketing tactics used by Magic Leap in promoting the Magic Leap One was selling early adopters on the "magic" contained within the device. On Thursday, some of that magic was uncovered as the Magic Leap One was completely disassembled by repair engineers, revealing the delicate innards of the device and detailing how it delivers its augmented reality experiences.