
How To: Build a Newman cool motor
In this three-part video tutorial, learn how to build a "Newman Motor". From the website of Joseph Newman, this motor is an "electromagnetic motor that runs cool (unlike all conventional motors) and harnesses the


In this three-part video tutorial, learn how to build a "Newman Motor". From the website of Joseph Newman, this motor is an "electromagnetic motor that runs cool (unlike all conventional motors) and harnesses the
In this tutorial the instructor shows how to solve equations with fractions and decimals. When you have a fraction first try to simplify it by canceling out the common factors in the numerator and the denominator. If there are any decimals convert them into fractions. Now if you have a number multiplying a equation apply distributive law and simplify the equation. Now finally try to get the variables on one side and numerical terms on the other side of the equation and finally solve for the u...

Knowing how to ride a bike is a fun and useful skill that kids can use well into adulthood. This video tutorial demonstrates a safe and simple way to teach kid’s how to ride a bike. Before taking to the streets, make sure the child is wearing a correctly fitted safety helmet. Support the child while they pedal from the street or concrete into a nearby grassy area. Early on, make sure to teach them proper bike-riding safety laws and be sure to keep the mood light and avoid showing any frustrat...
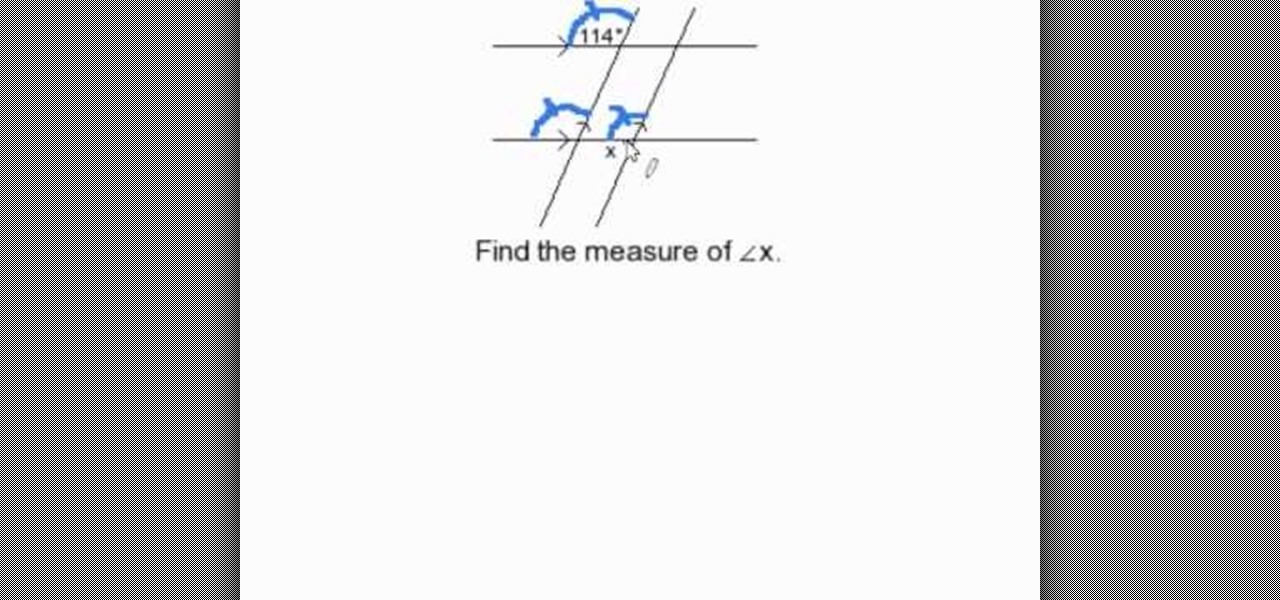
Consider two pairs of parallel lines, one pair horizontally and another is inclined from vertical position. If one of the four angles is given, then the other three angles can be easily identified. First select the angle which is down to the known angle, it will be same as first one. Then according to the law, that a straight lines consists of 180 degrees. For example if the known angle is 114 degrees, the unknown angle will be 180-114= 56 degrees.

This is kind of scary! This video demonstrates just how easy it is to hack into an iPhone to access the data on it - including recovering deleted photos. You only think you've deleted those naughty photos you sent to your girlfriend.... Fortunately, there is a way... However, this particular process requires software available only to law enforcement. But that's never stopped a hacker - or a jilted ex - before!

Since the days of Archytas, rocket propulsion has been the Holy Grail of aeronautics. Thanks to Galileo's inertia, Newton's laws of motion, and the "father of modern rocketry," Goddard, space is not a complete mystery anymore. Rocket-powered aircrafts have evolved from the first liquid fuel rocket in 1926, to the Soviet R-7 which launched Sputnik, to NASA's Saturn V that propelled Apollo 11 to the moon. Today, even billionaire tourists can enjoy space, like Microsoft's Charles Simonyi and Cir...

Have a Cambox portable/professional DVR? Well, if you're one of the lucky few, then this video tutorial from Vofoo could help you out.

Whether you're rooting for one of the teams or just love a contest, a pool will have you cheering. You will need:

Back when we took chemistry, most of what we read and learn went in one ear and out the other. If only we had a cool experiment like this one to perk up our pubescent ADD.

Careers in law enforcement range from police officers and state troopers, to FBI agents and crime scene investigators. Get a job in law enforcement with tips from a former highway patrolman in this free video series on law enforcement careers.

Remember that scene in Tim Burton's Batman where the Joker and his goons defaced dozens of priceless works of art? A collective of digital artists have found a less criminal, more geeky way to do the same thing.

Uber's legal team may have finally sold their engineering golden boy down the river as their war with Waymo continues. Anthony Levandowski isn't your average sacrificial lamb either — given the alleged stealing and all that — but Uber seems set on distancing themselves from this whole fiasco as fast as they can.

Dutch police are using a system very similar to Pokémon GO on smartphones, but they aren't walking around trying to catch little pocket monsters. The purpose of this system is to give augmented reality help to first responders who may be less qualified to work a fresh crime scene. If successful, the idea of a contaminated crime scene could be a thing of the past.

Got some seriously sensitive information to keep safe and a spare-no-expenses attitude? Then the new Solarin from Sirin Labs is the smartphone for you and your $17,000.

The Null Byte community is all about learning white hat hacking skills. In part, this is because I believe that hacking skills will become the most valuable and important skill set of the 21st century.

Just like cash, bitcoin is used for everything from regular day-to-day business to criminal activities. However, unlike physical cash, the blockchain is permanent and immutable, which means anyone from a teen to the US government can follow every single transaction you make without you even knowing about it. However, there are ways to add layers of anonymity to your bitcoin transactions.

In the US, law enforcement officials can make you unlock your smartphone with a fingerprint, but they can't force you to input a password or PIN, which would violate your Fifth Amendment rights. To help you from ever being in a scenario where you're forced to put your finger on the Touch ID sensor, Apple has a built-in way for you to disable biometrics on your locked or unlocked iPhone in mere seconds.
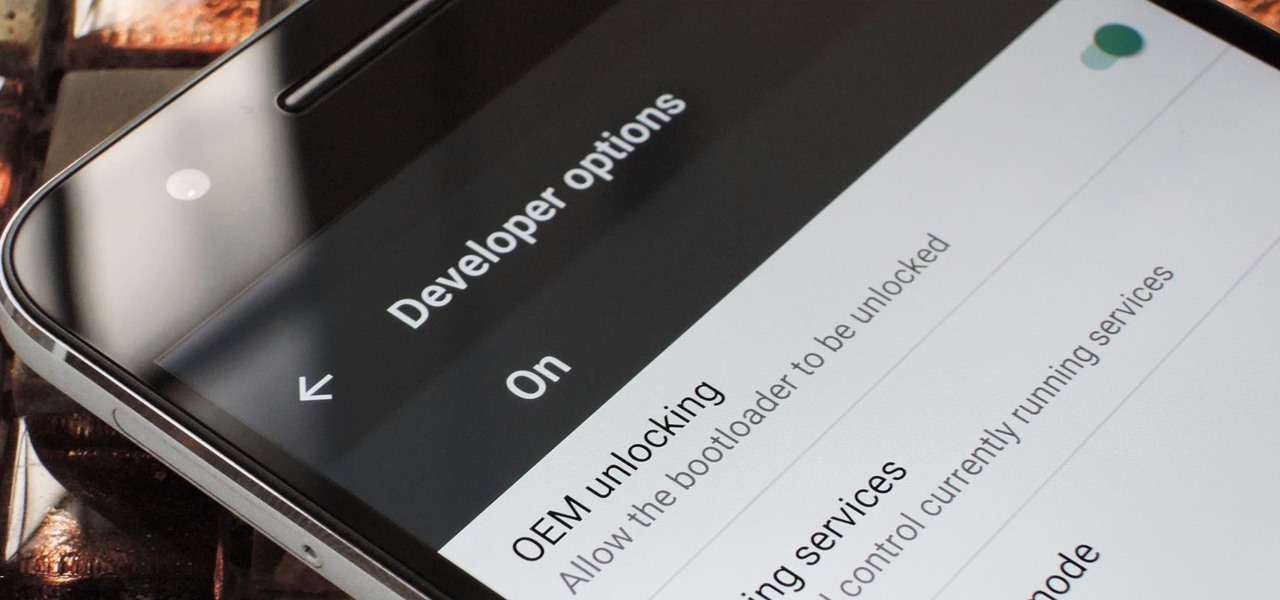
If you've ever rooted an Android device in the past or installed a custom recovery, you're surely familiar with the term "unlocked bootloader." But if all of this sounds like gibberish to you, some major changes in Android have made it to where you should definitely get familiar with the concepts.

Welcome back, my aspiring hackers and those who want to catch my aspiring hackers! As most of you know, this series on digital forensics is inspired by the motivation to keep all of you all out of custody. The more you know about the techniques used by law enforcement and forensic investigators, the better you can evade them.
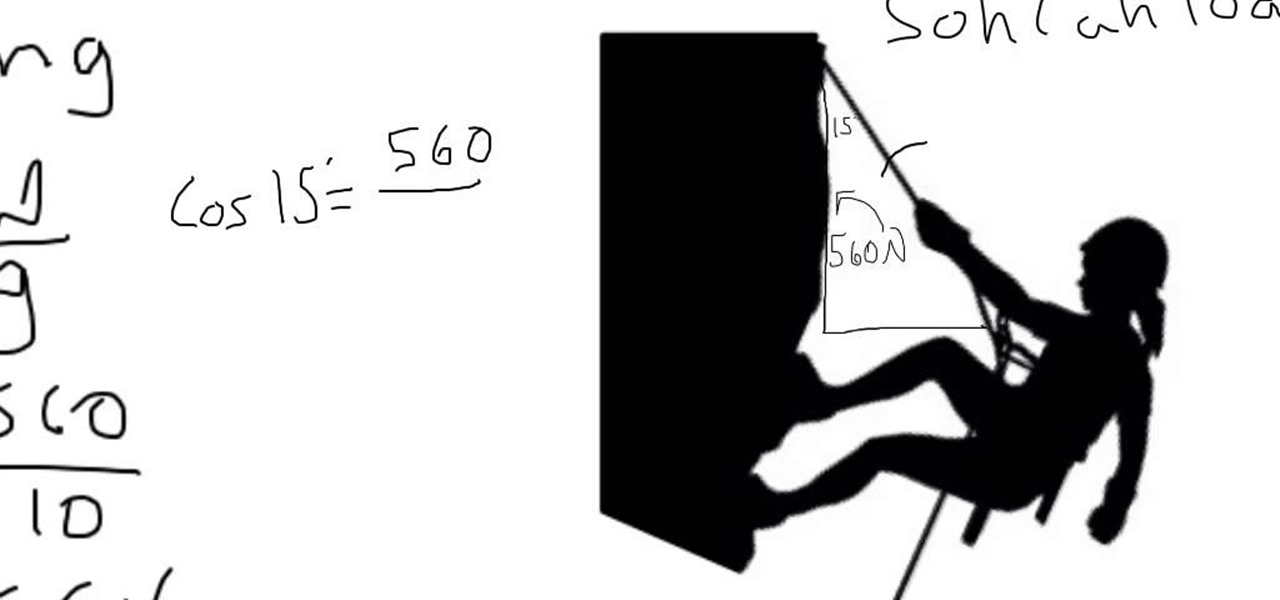
In this video tutorial I will be explaining how to work a tension problem. Usually these problems are found during a Newtons laws unit in physics. I am currently in physics and I thought I might share my strategy and work to help you guys succeed in the problems. Thank You. The video was made with Explain Everything. Also, please check out my youtube channel. It is new and I pasted a link for you guys to check out. Like comment and subscribe!
Here's a very informative video for those of you learning to drive in the Nottingham and surrounding areas. We look at what to do when you get to the end of a road and you can't see what's coming from the sides. Keep slow so you can look, assess, decide and act upon what you see. You have to wait at a give way line and definitely stop at the stop sign. It's the law.

Video: . HOPEWELL, Va. (WTVR) -- A Hopewell circuit court judge has ordered that a Marine veteran detained over anti-government Facebook posts be released from a psychiatric hospital.

There's more to recording calls than just protecting yourself against liability or an angry ex — oftentimes, this feature is the perfect tool to save momentous calls like breaking news of your recent engagement to loved ones. And with the prevalence of video calls, you can even capture memorable video chats such as your mom's first glimpse of your newborn on your mobile, courtesy of Skype.

| Update: ZTE's issues with the US government have finally been resolved. Check out the details below.

New statements from Apple make it clear that they do not believe a hacker, or group of hackers, breached any of their systems. This comes after a recent report from Motherboard that a hacker gang called the "Turkish Crime Family" is threatening to remotely wipe up to 559 million iPhones by April 7.
I'll admit it: I ignore expiration dates. No matter if it's a sell-by date, "best if used before" date, or even a use-by date, I don't care. I just check for signs of food decay and keep on eating.

Welcome back, my fledgling hackers! In this series, I am trying to develop your knowledge of digital forensics, which is valuable whether you're choosing a career in it or just want to know how your hacker activity can be traced. Few professional digital forensic investigators have a hacking background, but the best ones do.

Welcome back, my tenderfoot hackers! So many readers in the Null Byte community have been asking me questions about evading detection and hacking undetected that I decided to start a new series on digital forensics.

This short video clip shows seven demonstrations of Isaac Newton’s first law of motion– the law of inertia. Newton’s law of inertia states that objects moving at constant velocity will continue moving at constant velocity, unless acted upon by an outside unbalanced force. Six of these demonstrations (excluding number six) are from Tik Liem’s book Invitations to Science Inquiry.
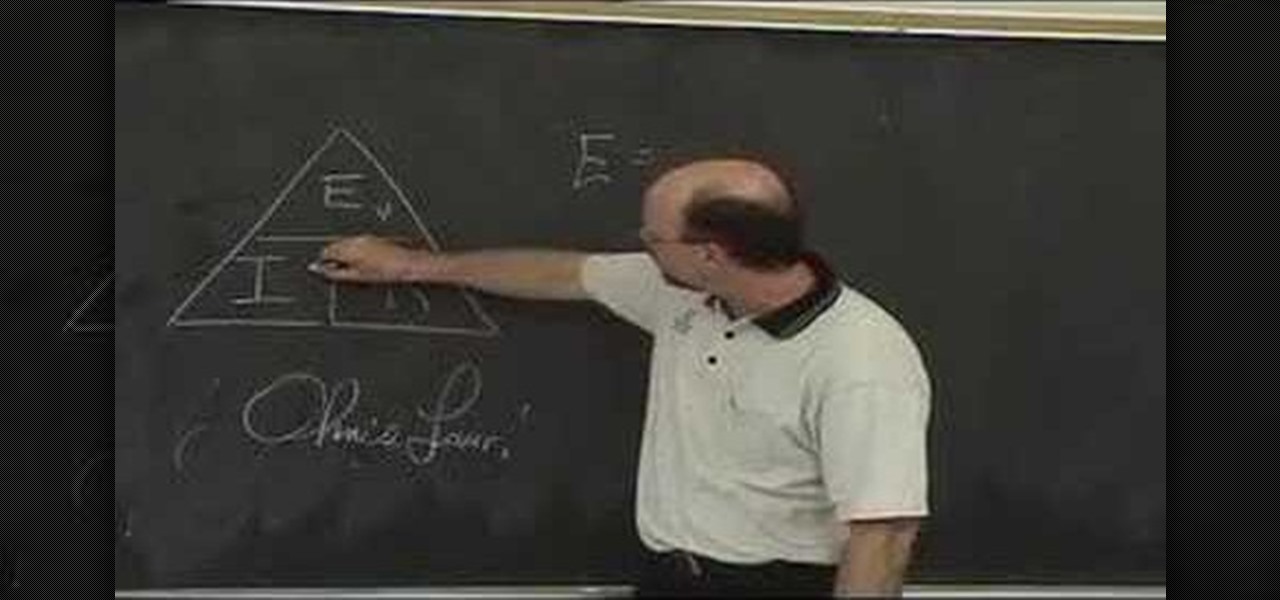
Watch this educational how to video to review Ohm's Law. This math and physics concept is derived from electric motive forces, intensity of current flow and resistance values of conductor. Watch and learn more about Ohm's Law.

Before you go out to protest, understand what you are facing. Sometimes these demonstrations become infected with looters and rioters, which could mean interaction with law enforcement and potentially arrest. And if your phone is on you, it can be used as a tool against you.

In recent years, Google's Arts & Culture project has been leading the way in terms of innovating the practice of using technology to preserve landmarks and great works of art via digital 3D copies. Increasingly, these efforts are also giving history buffs the chance to experience classic works and spaces with unparalleled intimacy through the wonders of augmented reality.
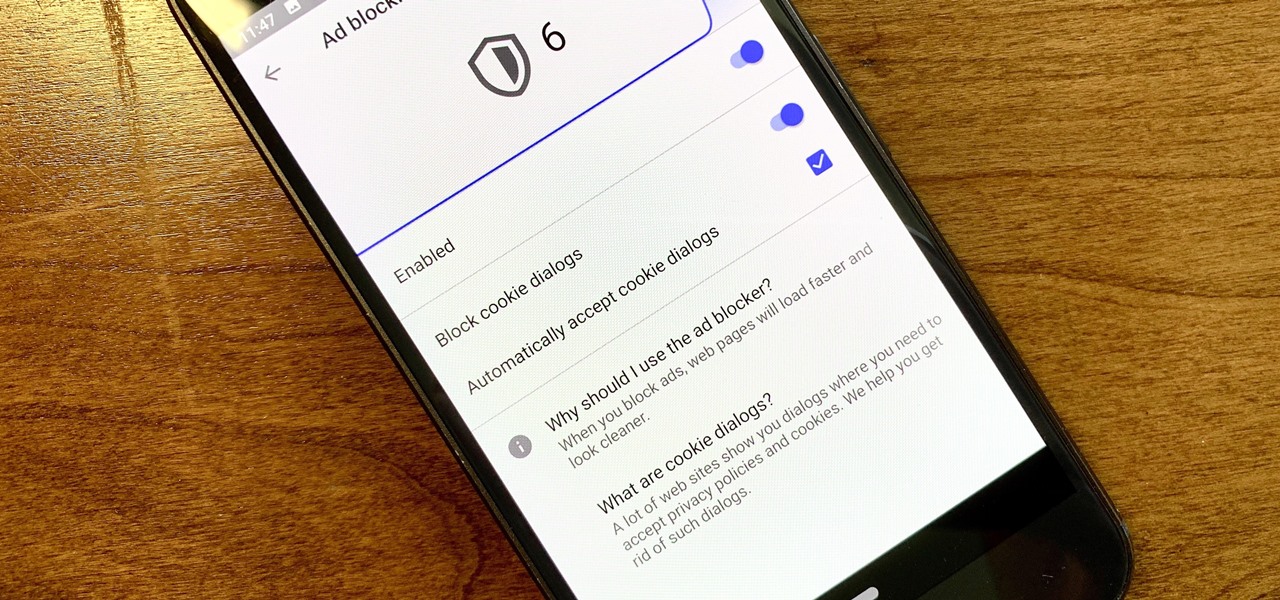
Ever since the GDPR was implemented, it seems every website on the internet needs to inform you of how its privacy policies have changed. If your web browsing experience has been marred by a constant barrage of these cookie pop-ups and privacy dialogs, you should know there's an easy way to block these web annoyances so you never have to tap another checkbox or accept button again.

If you've ever been on the receiving end of a threatening phone call, you'll immediately know the value in being able to record phone conversations on your iPhone. Beyond that extreme example, however, recording calls is still an extremely useful feature to have for important conversations like business meetings and verbal agreements, and it's totally doable with a third-party app.

You don't need an obsessive ex stalking you to benefit from the ability to record calls on your iPhone in a pinch. Besides protecting yourself from nefarious intent, recording important conversations like verbal contracts and agreements can help you cover all your bases and ensure you're insulated from any potential liabilities that may appear down the road.
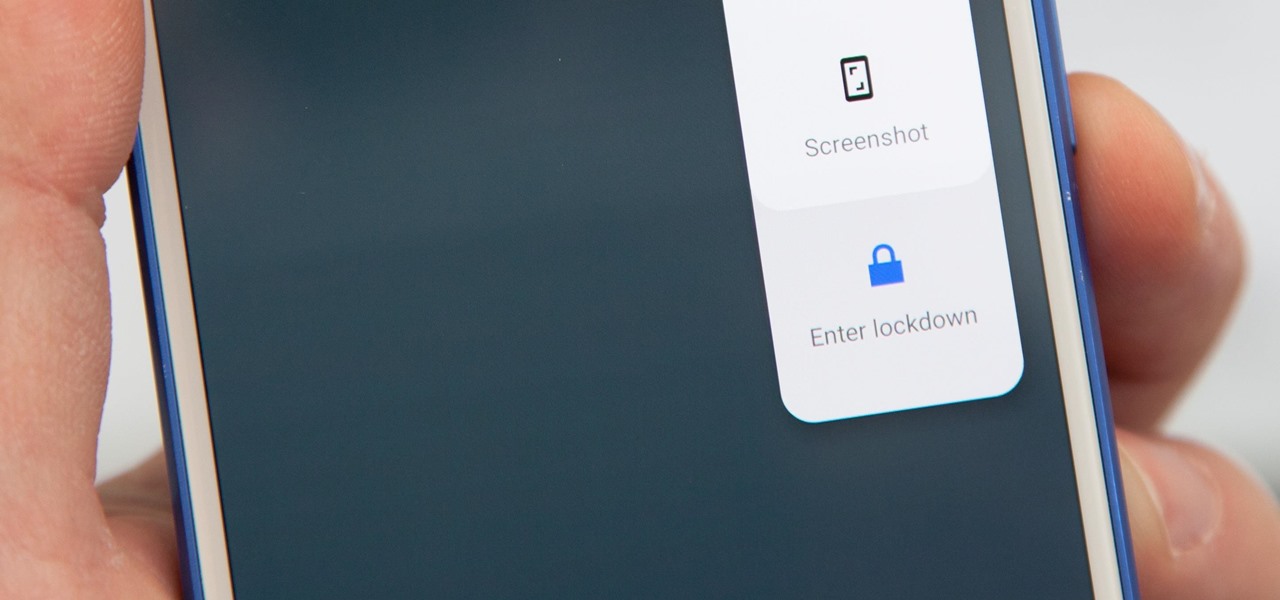
Following in iOS 11's footsteps, Android 9.0 Pie will include a security feature that lets you immediately disable the fingerprint scanner as well as extended Smart Lock features. After initiating the feature, you will be required to insert your PIN, pattern, or password before any other unlock methods will work again.

Patent holder Genedics, LLC has filed a legal complaint alleging that hand-tracking startup Leap Motion is infringing on its intellectual property.

Accused of violating whistleblower and age discrimination laws by its security director, Magic Leap has taken an internal situation to the US District Court to clear its name of the allegations.

The AFL-CIO's Transportation Trades Division, which represents 32 unions in the US, has successfully lobbied for the removal of 10,000-lb. and heavier commercial trucks from provisions in bills expected to pass that could allow for millions of driverless vehicles on public roads and streets, Bloomberg News reported.

A router is the core of anyone's internet experience, but most people don't spend much time setting up this critical piece of hardware. Old firmware, default passwords, and other configuration issues continue to haunt many organizations. Exploiting the poor, neglected computer inside these routers has become so popular and easy that automated tools have been created to make the process a breeze.