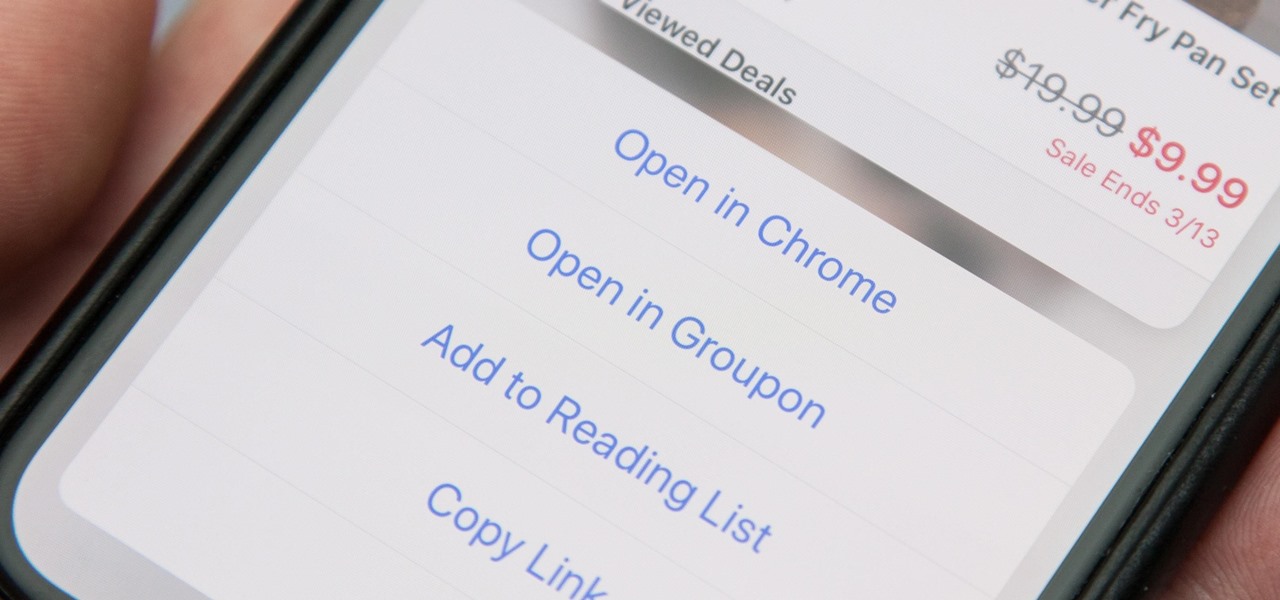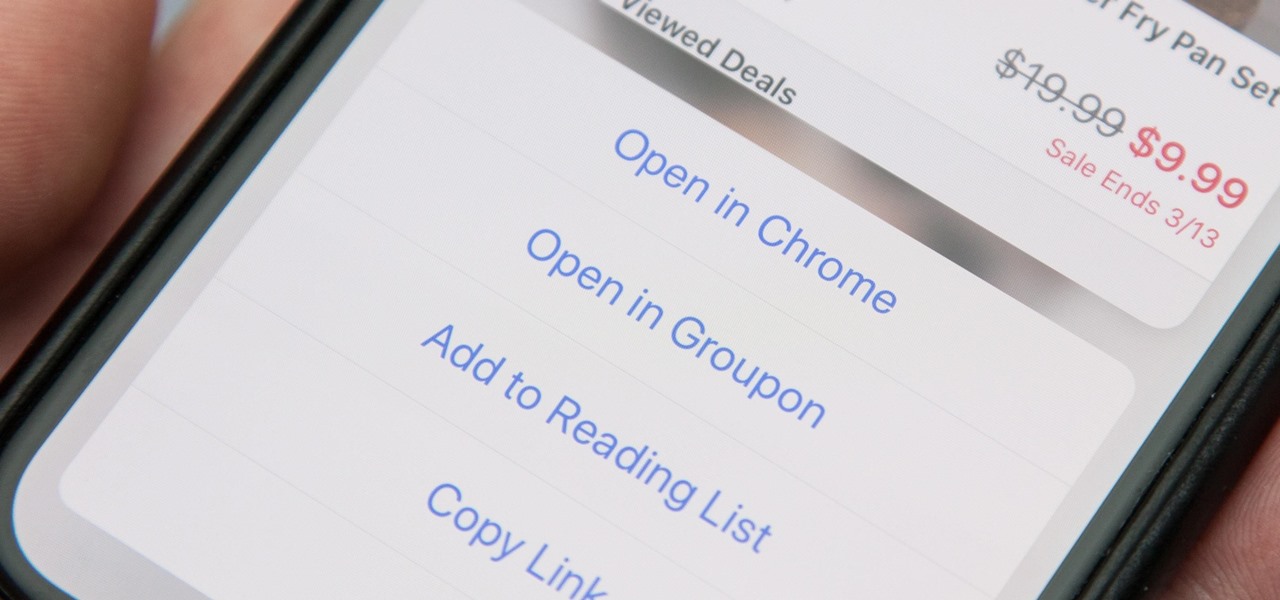
When you tap on a URL link in a text, email, or wherever, your iPhone's default reaction will be to open it up in Safari, and there's no way to change this in the settings. However, there is a way you can work around this to open up links in Chrome instead. Even if you accidentally open a link in Safari, there's a quick way to jump the tab right into Chrome.
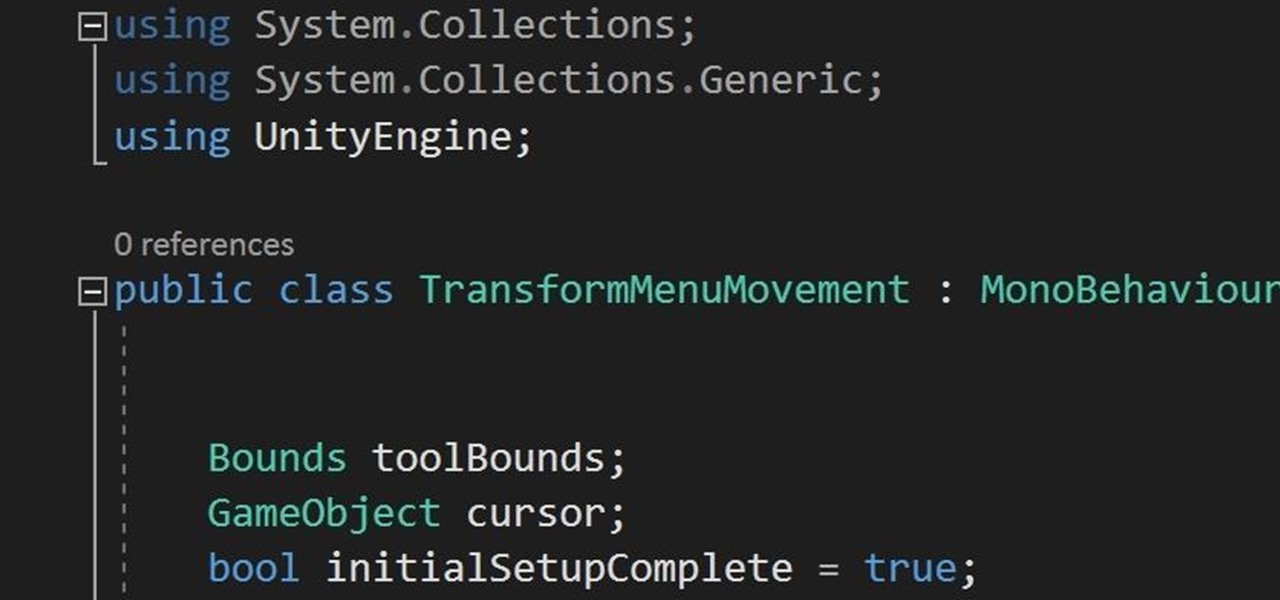
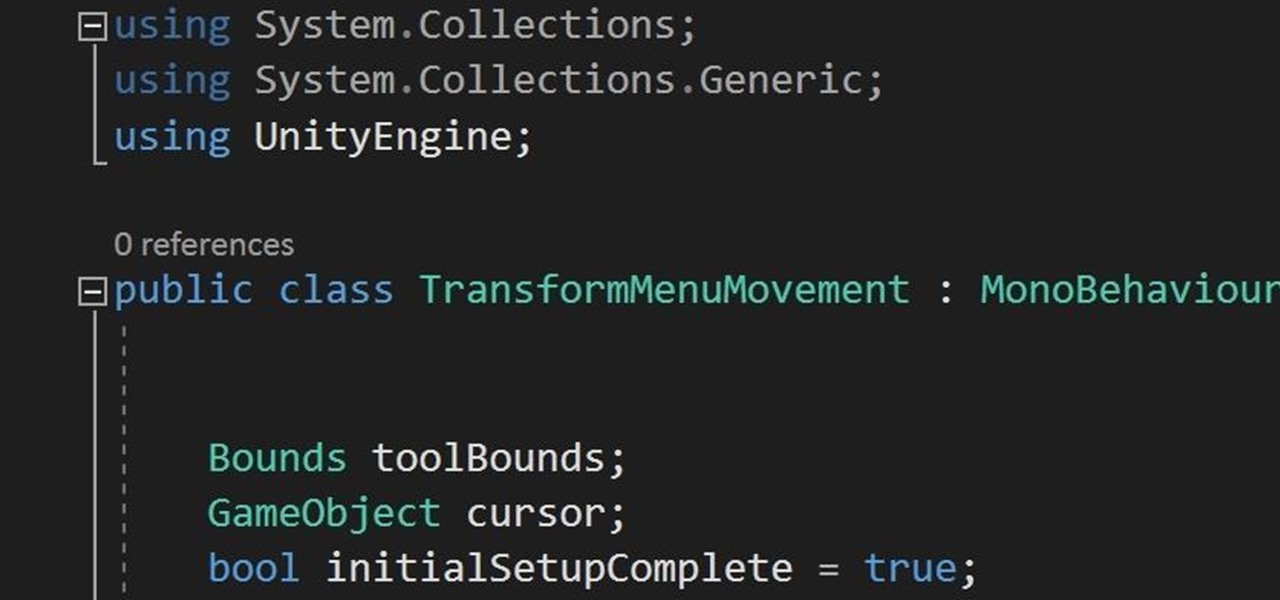
In the previous section of this series on dynamic user interfaces for HoloLens, we learned about delegates and events. At the same time we used those delegates and events to not only attach our menu system to the users gaze, but also to enable and disable the menu based on certain conditions. Now let's take that knowledge and build on it to make our menu system a bit more comfortable.

After numerous scandals like the Equifax data breach and the 2016 US election, cybersecurity has become a significant issue for Americans. Unfortunately, anytime we use our devices, we're open to a cyber attack — especially when we browse the web. However, there are ways that we can make it harder for hackers and data miners.

Puzzle games are a great way to kill time and exercise your brain in one fell swoop. They challenge you to think strategically and plan ahead, whether that's to create killer chain combinations for maximum points, or to plain old keep from getting killed.

Beginners luck is a phrase I have always hated. But really, beginners luck comes down to not letting your experience in something get in the way of the idea.

If you've been to a farmer's market during tomato season, chances are you know that heirloom tomatoes are pricier (and funnier-looking) than their hybrid counterparts.

I noticed the neon yellow sign at the new location of Pho Bar in Chinatown right away. The sweeping cursive yellow letters spell out "Crazy Rich Broth"; the same phrase printed on the back of servers' shirts. It's the kind of minimalist but colorful design feature that is especially popular on Instagram at the moment — shots of patrons in front of a glowing sign.

Ever since the announcement of the Razer Phone, a wave of gaming smartphones started to hit the market. With ASUS being such a big name in gaming, it made sense for them to throw their hat in the ring. The result is the ROG Phone. And with this first try, ASUS has topped the rest, creating a gaming phone others should try to emulate.

Conducting phishing campaigns and hosting Metasploit sessions from a trusted VPS is important to any professional security researcher, pentester, or white hat hacker. However, the options are quite limited since most providers have zero-tolerance policies for any kind of hacking, good or bad. After researching dozens of products, we came out with 5 potentials that are ideal for Null Byte readers.

Shodan calls itself "the search engine for internet-connected devices." With so many devices connected to the internet featuring varying levels of security, the special capabilities of this search engine mean it can provide a list of devices to test and attack. In this tutorial, we'll use Python to target specific software vulnerabilities and extract vulnerable target IP addresses from Shodan.

As was mentioned by the great OTW last week, TOR, aka The Onion Router, has had its integrity attacked by the NSA. In an attempt to reduce the anonymity granted by the service, the NSA has opened a great many nodes of their own. The purpose is presumably to trace the origin of a communication by compromising some entrance and exit nodes. Once both are compromised, it is much easier to correlate traffic with a particular individual.

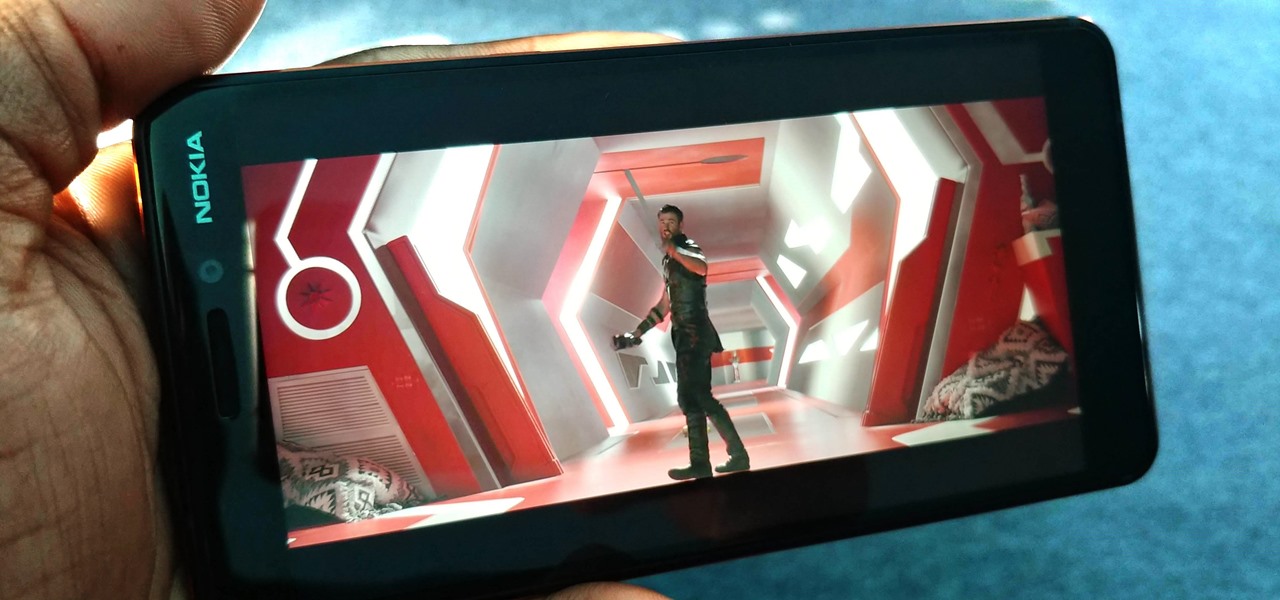
You might think you need to buy a thousand dollar phone to get a great experience while streaming movies and TV shows from services like Netflix, Hulu, and YouTube, but that's just not true anymore. While phone prices keep rising and the midrange segment now ranges from $300–$500, there are still cost-effective options that come with top-notch displays and media features.

Think back to when you last wanted to transfer some music or videos to your friend's smartphone and how difficult and slow it was. As powerful as our phones are, the default file sharing options are limited. There are, fortunately, some better options which make moving files easy, secure, and painless.

The gig economy is thriving, and if you aren't already making money with your phone, you could be missing out on easy residual income. Some people just want extra cash, and some even manage to completely ditch the 9–5, enabling them to work at their own pace and set their own hours.

Clumsiness is the great equalizer when it comes to smartphones — it makes no distinction between the most expensive flagship handset and cheaper mid-range models. A hard drop onto pavement will usually result in a shattered screen, regardless of how pricey your device is. And with a smartphone breaking every two seconds, we're truly our own handset's ultimate nemesis.

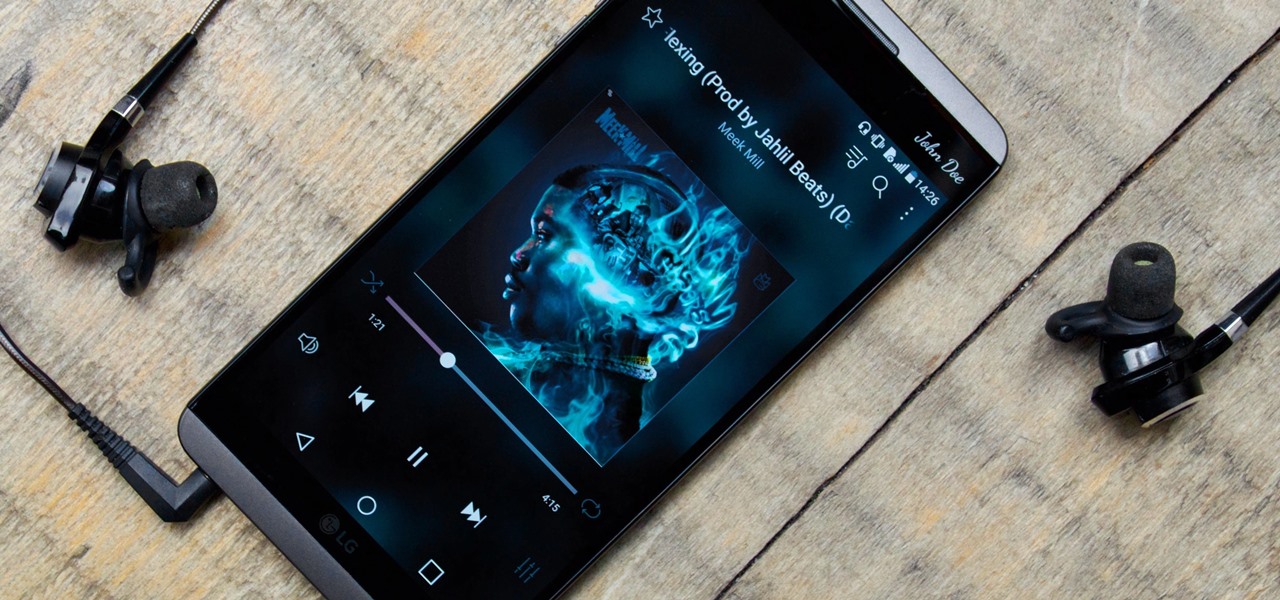
While music may not technically be a "universe language," it is the one language listened to by all. There are over 1,500 music genres today—rap, classical, rock, jazz, trap, hip-hop, house, new wave, vaperwave, charred death, nintendocore... and the list goes on. And if you're like most people, you now probably listen to the majority of your music on your phone.
Welcome back Hackers\Newbies!

Automation has been a buzz word for quite some time now, but the principles behind it are as strong as ever. For a hacker or pentester, Bash scripting is one form of automation that cannot be ignored. Virtually any command that can be run from the terminal can be scripted — and should be, in many cases — to save valuable time and effort. And a Bash script just happens to be great for recon.

If you're like me, you take more than just a few screenshots throughout the day, and they add up fast on your iPhone. When you snap that many images of the screen, your Photos app's "Screenshots" folder can swell beyond triple digits if you don't manage it, and your "Recents" folder will become a cluttered mess. But there is a trick to keeping screenshots in check, and you can have total control over it.

Overall, iOS is more impressive than ever with its stability enhancements, security tools, suite of apps and services, and intuitive user interface. With each passing update, things just get better and better for iPhone users. But don't think for a second that this is all because of Apple's genius — many of these features were at least partly inspired by tweaks made by the jailbreak community.

Trying to figure out which music streaming service to subscribe to can be a difficult task when the playing field is so crowded. Each has its benefits, as well as downsides, so finding the right one for your needs and wants can take a lot of overwhelming research. But we've done all the research for you to help you find the best music subscription your money can buy.

The last iOS software update was a modest one, but iOS 17.4 has a lot more for your iPhone, including changes to emoji, Podcasts, security, Safari, widgets, Apple Cash, CarPlay, and more.

Apple's new iOS 16 software update is finally here, and there are over 350 new features and changes for you to enjoy on your iPhone. There are major lock screen and home screen improvements, a pleasant surprise for the Contacts app, and tons of new upgrades to Safari, Mail, Messages, and more.

Check out this video of corporate/industrial photographer David Tejada's small location lighting kit and what criteria he used to compile it. Get tips from this how-to video.

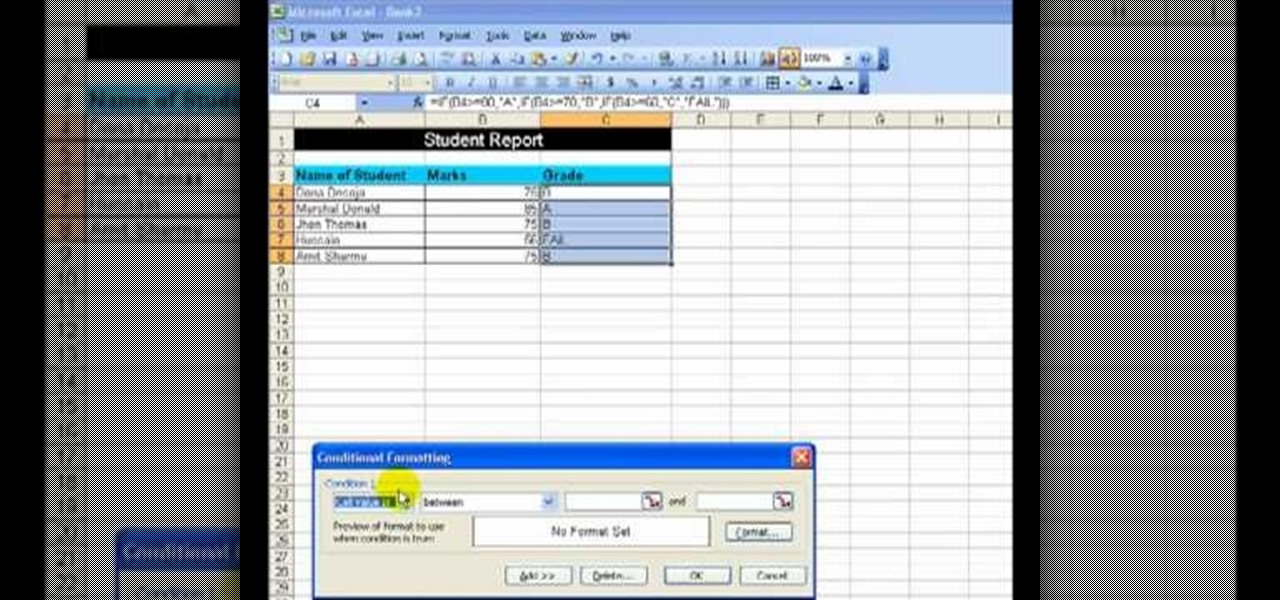
If you're looking for a way to create a student report, Microsoft Excel makes it easy to create a wonderful spreadsheet with tons of information. This video shows an example of a student report being created, which has three simple items in the columns of the sheet, which are the names of the students, the marks obtained and the grades.

You will hear a million speeches and presentations in your life. It is helpful to know criteria for evaluating them beyond whether or not you liked it. Learn how to evaluate speeches from a professional speaker and communications instructor in this free public speaking video series.

It has often been said that the only constant is change. IT's ability to manage change is an important business success criteria in today's competitive markets. Change can either be planned or unplanned. This presentation will help you understand the effects of change, and how to manage change properly. It will help Oracle database administrators better prepare to implement changes and measure the positive (or negative) affects those changes produce on the system.

Super Mario Brothers! No, wait... Super Meat Boy! Yep, that's right. Meat. As in "cube" steak. As in a square piece of beef with eyes and a shitty grin, who just happens to be in love with a band-aid. I have no idea why. And no matter how shocked you are to see your dinner on your screen, it doesn't change the fact that this platform game is AWESOME!

Papaya trees are very vulnerable to transplantation shock. Seedlings tend to recover slowly and poorly after replanting in a new location under a sunny sky. Many internet articles advise that papaya trees should be transplanted without injury to their root systems. Keeping the root systems intact is next to impossible if the papaya seedlings are too close to each other. However, you would be surprised to learn how a papaya tree with serverely broken root systems can survive a transplantation ...

Tracey Cox talks about the five key areas of compatibility (chemistry, compatibility, common goals, speed, and timing) that lead to long term relationships. If your relationship meets enough of these criteria then it will likely stand the test of time. Know if you've found "the one".
(This is a manifesto I wrote 2 years ago. I have never published it. It was a reaction to the ignorance I faced in graduate school from the modernist sculpture

Google announced the creation of "Life In A Day," a film project that solicits video submissions from YouTube users around the world--the criteria is that they must capture some kind of moment filmed on July 24.

Another example of outstanding resourcefulness and ingenuity in the medical community (see earlier this week: Blood Sucking Plunger Could Heal Millions).

One of the biggest video games events of the year is about to happen in Japan tomorrow, when the Tokyo Game Show (TGS) kicks off. If you've never heard of it, just think of it as the E3 of the East—a video game extravaganza open to both businesses (Thursday and Friday) and the public (Saturday and Sunday). And even though it hasn't officially started, TGS has already released some grand announcements, specifically about Nintendo's future lineup and a precipitous drop in their share prices.

Video games are the newest major expressive media. As such, their role in society is still being defined continuously. A monumentally important example of this took place yesterday at the US Supreme Court. After a long deliberation, the highest court in the land handed down a decision invalidating a California law banning the sale of violent video games to minors on the grounds that video games are protected speech under the First Amendment, like movies and books.

As you all know, the first Null Byte Technical Excellence Tutorial Contest ends this coming Monday, Feb. 15, 2016. If you are working on another great article or your first article, try to complete it and submit it before midnight Pacific Standard Time (PST) to be considered in this contest. The winner of this contest will not only receive a certificate verifying the technical excellence of their tutorial, but they will also receive a free copy of the Professional version of the Exploit Pack ...

What is Google Dorking? Well, simply put, "Google Dorking" is just an efficient way to utilise keywords in order to perform very specific searches on a given subject. In this case, one would look for websites/servers that are vulnerable to attacks or are configured improperly by using specific search criteria that should yeild results, should it find matches to known mistakes/errors in a website or webserver.

It may not seem like it, but it's been less than 90 days since Google+ was introduced to the world. Since then, we've seen many great features that have made Google+ one of the most attractive social networks around. Today, we've received even better news: major improvements and feature updates that are truly innovative.

You've had a hard day at work and need to get out of the house, have a few drinks, but you don't want to go just anywhere—you want the right crowd and the right bar. For those nights, barhopping just isn't the answer, it's SceneTap.