Although +Google Chrome has been getting many deserved kudos for its innovations and speed, many people still prefer to use +Mozilla Firefox as their primary browser. If you’re a dedicated Google+ user, you know that there are many Google+ Chrome browser extensions available to modify your Google+ experience. What you may not know is that there are also Firefox extensions you can use for Google+.
Since the invention of the printing press, books have been a dominant and iconic paradigm in our culture and throughout the world. During my years in elementary and high school, the digital world was on the rise sparking the conversation: Are Books Obsolete. Over the last year (or 2 at the most) that the term "Book" has started to make the shift from a physical object to the concept of a written work.

+Nik Cubrilovic discovered last week that Facebook could track your web activities even after you logged out of your Facebook account. After some blatant denials from Facebook spokespeople, Facebook decided to fix the logout issue, but not before +Michael Arrington, on his new Uncrunched blog, made a concise post revealing Facebook's dishonesty: Facebook submitted a patent application for "tracking information about the activities of users of a social networking system while on another domain...
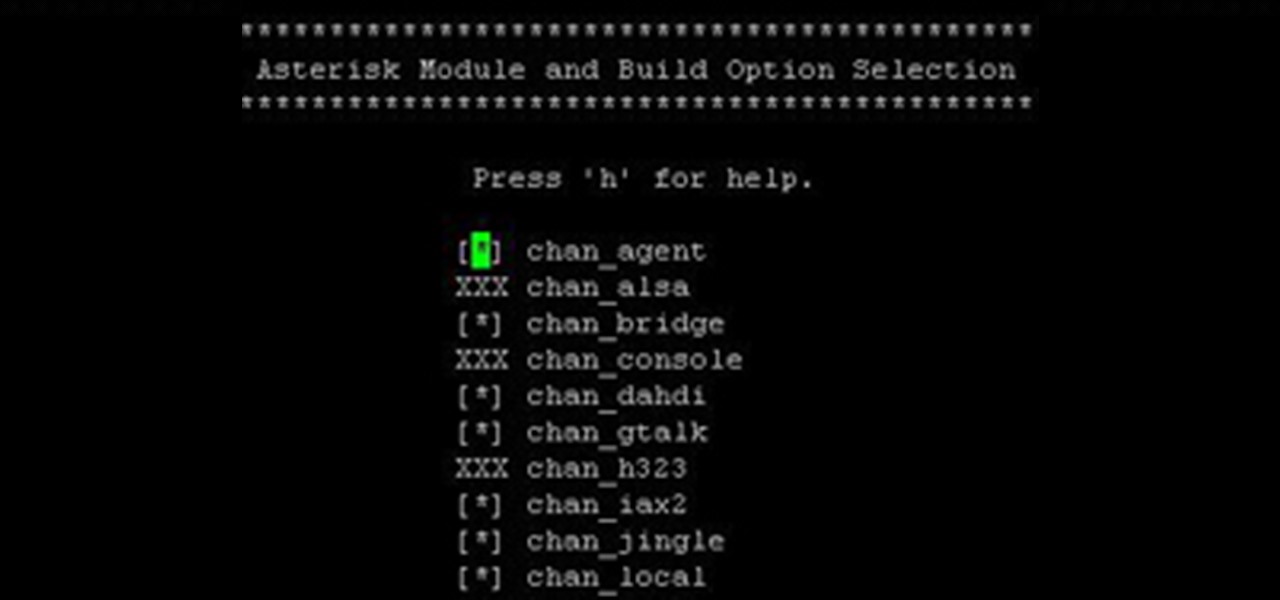
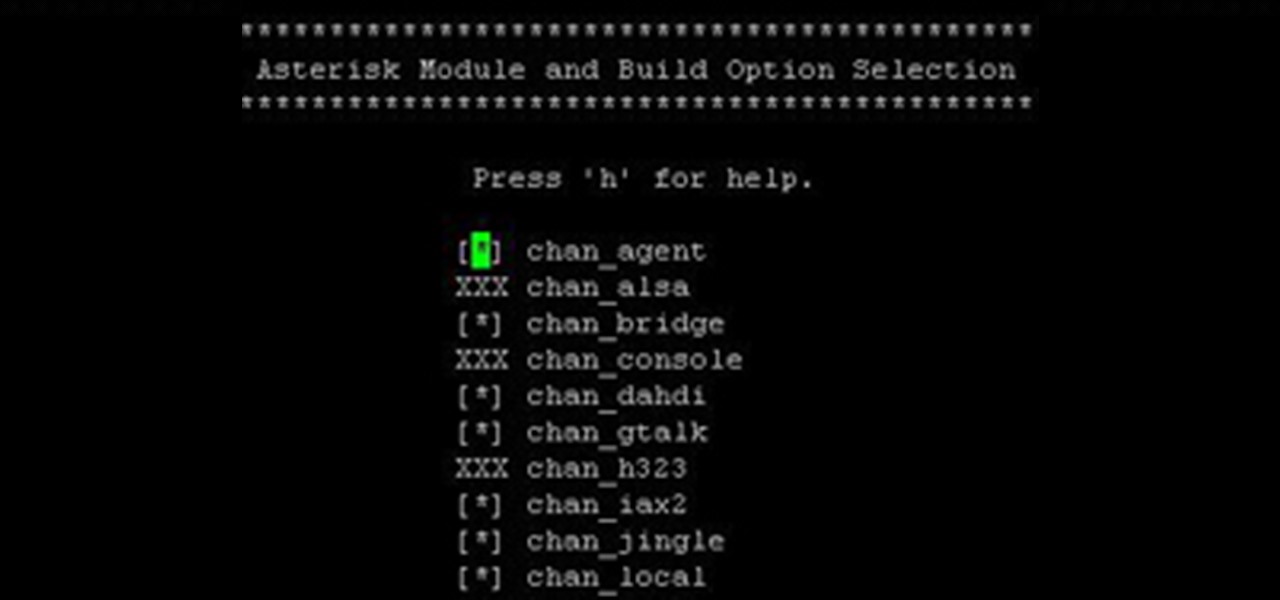
Over the years, I have enjoyed playing with Asterisk. I have found Asterisk to be extremely powerful and fun to play with. There are several books and many scattered how to articles out there, but most are outdated and the information required to build Asterisk from beginning to end can be a bit daunting. I wanted to combine all the steps into a single article and share my experience with everyone. If I have left out any steps please let me know.

Wireless networks. Nowadays, everyone uses 'em, but most don't secure 'em. On average, I can drive up and down any block in my city and find at least one or two open or semi-open networks on any given day. With some changed MAC addresses for good measure, an attacker can use your network as a spring board for who knows what. When the police come a few days after, they are coming to your door—and not to talk about how nice your lawn is. Don't be that guy.